What is a Hot Wallet?
Learn what a hot wallet is, how it works, why it enables fast crypto activity, and why online signing authority creates major security tradeoffs.
Introduction
Hot wallet is the term for a wallet whose signing capability is available from an internet-connected environment. That sounds like a small implementation detail, but it is the whole point of the category: a hot wallet exists so you can act now rather than after a manual offline process. If you want to connect to a dapp, sign a message in a browser, move funds from an exchange, rebalance treasury assets quickly, or automate operational flows through an API, you need some form of keys or signing authority that is reachable enough to respond.
That same reachability is what makes the idea dangerous. In crypto, control is not mostly about account passwords or database permissions. It is about the ability to authorize transactions with private keys or equivalent signing mechanisms. When that authority lives in an online system, the attack surface expands from physical access and deliberate recovery workflows to browsers, mobile operating systems, malware, phishing, compromised websites, bad permissions, misconfigured infrastructure, and operational mistakes. A hot wallet is therefore not just a convenience tool. It is a trade: speed and interoperability in exchange for more exposure.
The easiest way to understand hot wallets is to stop thinking of them as “places coins are stored.” The assets remain on the blockchain. What the wallet controls is the ability to produce valid signatures, expose accounts to applications, and submit authorized transactions to the network. Once that clicks, the distinction between hot and cold wallets becomes clearer. The question is not where the coins sit. The question is where the power to sign sits, and under what conditions it can be used.
How does online signing authority define a hot wallet?
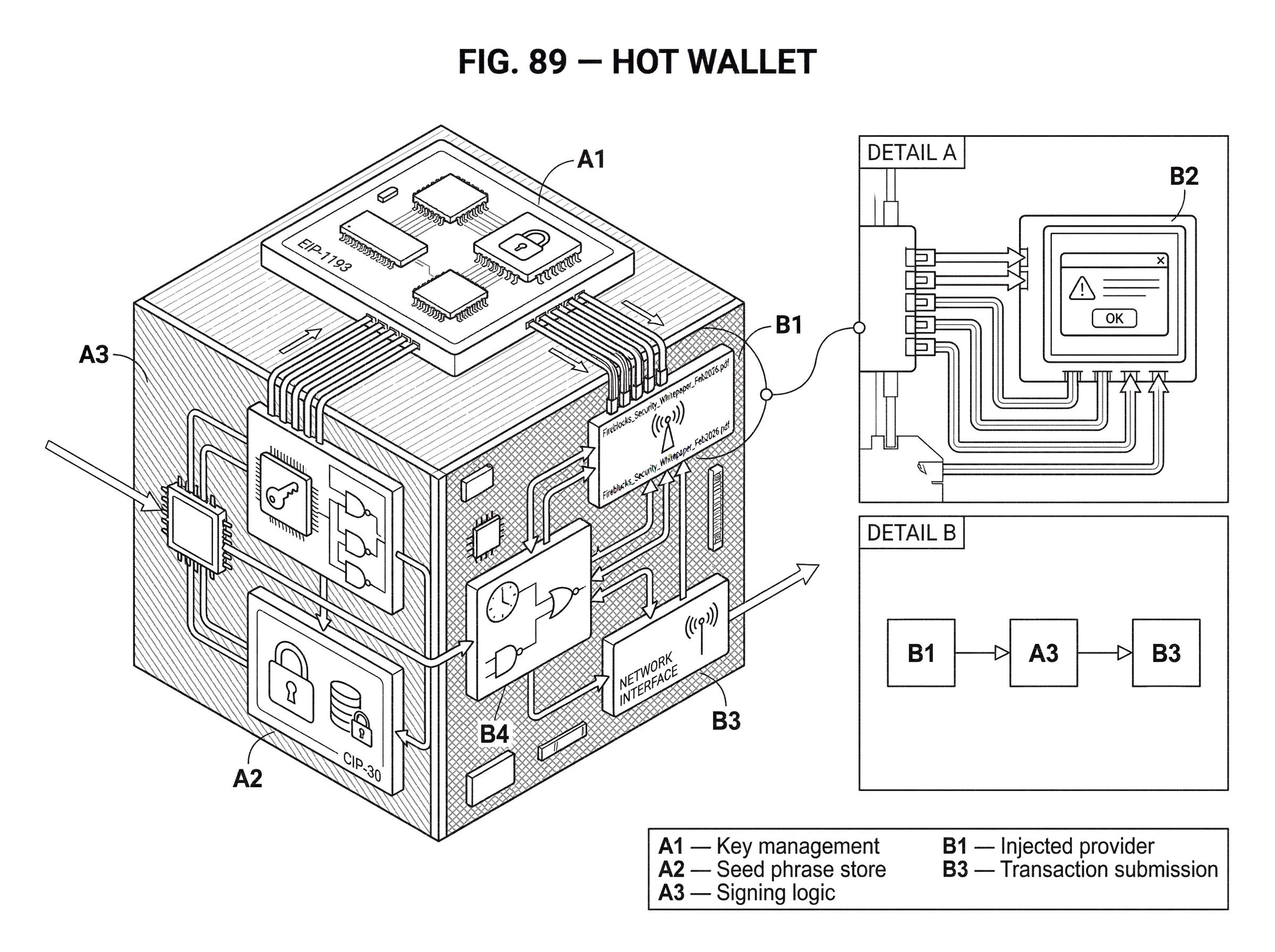
A hot wallet is usually described as a wallet connected to the internet. That is directionally right, but the more precise idea is that its signing authority is available from an online environment. Sometimes that means a seed phrase was generated on a phone or laptop and the wallet stores encrypted key material there. Sometimes it means a browser extension can prompt you to sign. Sometimes it means an exchange or institution uses servers, policy engines, and multiple online components to approve transfers. Sometimes it means a web app talks to wallet software through an injected provider or bridge. The surface details differ, but the invariant is the same: a transaction or signature can be produced without first moving to a deliberately offline device and offline ceremony.
This is why hot wallets are the default wallet form for everyday crypto activity. They make interaction friction low enough to support real usage. A browser wallet can expose an interface to a web page so a dapp can request accounts, ask for a signature, learn when the user changes chains, and submit transactions. On Ethereum, EIP-1193 standardizes this provider pattern: the wallet exposes a JavaScript provider object, dapps send requests through request(...), and the provider emits events such as account or chain changes. On Cardano, CIP-30 defines a similar browser bridge in which a wallet injects a shared cardano object and the dapp calls methods like enable(), signTx, signData, and submitTx. Different chains, same underlying reality: a hot wallet is how the user’s signing authority becomes available to an online application workflow.
That availability is not accidental plumbing. It solves a real problem. Blockchains are interactive systems. Users do not just hold assets; they connect to exchanges, lending markets, NFT marketplaces, bridges, games, governance systems, and staking interfaces. If every action required a fully offline device handoff and manual transaction shuttling, many of these activities would become too slow or cumbersome for ordinary use. A hot wallet exists because blockchains are live systems, and users need a live interface to them.
What roles does a hot wallet perform (keys, signing, and interfaces)?
| Role | Where keys live | User interaction | Common defenses |
|---|---|---|---|
| Key management | Device or distributed shares | Seed generation & backup | Encryption, secure backup |
| Signing logic | Device process or MPC node | Per-transaction approval | Hardware signer, MPC |
| Application interface | Wallet process or provider | Grant accounts & permissions | Provider isolation, consent |
| Submission & policy | Wallet or backend nodes | Automatic or gated submit | Whitelists, velocity limits |
Mechanically, a hot wallet combines a few roles that people often blur together.
At the bottom, there is key management: generating, importing, deriving, storing, or splitting the cryptographic material used to authorize actions. In a simple self-custody mobile or browser wallet, that may mean a seed phrase generated in software and stored, usually encrypted, on the device. Ledger’s explainer makes the key distinction starkly: a hot wallet generates the seed phrase in an online environment and stores private keys on an internet-connected device. That is exactly what creates both the convenience and the risk.
Above that, there is signing logic: the code that takes a transaction or message and produces a valid signature. In some designs, the private key is directly used on the device. In others, the key is never held whole by any one machine. Institutional systems may use multi-signature or MPC-style architectures so that authorization requires multiple keys or multiple distributed key shares. Fireblocks describes an MPC model where private keys are split into shares and never exist whole at any point, while BitGo describes a self-custody hot wallet design where the client and backup keys are held by the customer and the platform key is held separately, with countersigning gated by policy. These are still hot-wallet systems when the signing process remains reachable for online operations; they just try to reduce the danger of a single compromised component.
Then there is the application interface. A wallet must expose some way for software to ask for accounts, request permissions, trigger signing, and detect state changes. This is why provider and wallet-adapter standards matter. EIP-1193 explicitly separates the JavaScript provider from the wallet middleware behind it: the provider passes messages and emits events, while the wallet is responsible for key management, signing, and account exposure. That separation is useful because it shows where security decisions really live. The object visible to the web page is not the secret. The wallet behind it is the sensitive component.
Finally, there is transaction submission and policy. After signing, the wallet or connected application may broadcast the transaction to a node or RPC endpoint. In institutional settings, there may also be whitelists, velocity controls, role-based approvals, device separation, simulation, or transaction scanning before anything is allowed through. Those controls are not cosmetic. They exist because online signing is dangerous enough that cryptography alone is not sufficient.
How does signing through a browser wallet work in practice?
Imagine you visit a decentralized exchange in your browser and press “Connect Wallet.” What happens next reveals the essence of a hot wallet.
The website does not get your private key. Instead, it looks for a wallet interface the browser wallet has injected into the page. In Ethereum-style integrations, that might be a provider implementing EIP-1193. The site asks for account access using a request method. The wallet shows you a consent prompt because account exposure is a privacy and authorization decision, not something a page should receive automatically. If you approve, the dapp learns which account or accounts the wallet is willing to expose.
Now you decide to swap tokens. The website prepares a transaction payload and sends a signing request to the wallet. The wallet parses that request, decides whether it is structurally valid, and displays something for you to approve. If the wallet is well designed, it does more than show raw hexadecimal data. It tries to decode intent: what contract will be called, what tokens may move, what approvals are being granted, and whether the action looks suspicious. Fireblocks emphasizes this kind of pre-execution simulation and human-readable decoding as a defense against blind signing. That matters because the attack is often not “steal the key directly.” The attack is “trick the holder into producing a valid signature for a malicious action.”
When you approve, the wallet uses the online signing authority it controls to produce a valid signature. The signed transaction is then submitted to the network. The dapp updates its interface when it sees the pending transaction, and later the confirmed result.
The entire flow is fast because the wallet is hot. The browser, the wallet software, the user prompt, and the network request all happen in one online loop. If the same assets were controlled only by an offline signer with no online path, the interaction model would be fundamentally different.
Why are hot wallets widely used despite the risks?
Hot wallets are common because they solve the latency problem of real blockchain use. A user who moves small amounts frequently, signs into web3 apps, mints NFTs, votes in governance, claims rewards, trades on short notice, or interacts with DeFi protocols values responsiveness. For institutions, the same logic appears in a different form: operating capital must move, treasury workflows must execute, APIs must initiate payments, validators and market-making systems may need timely authorization, and customer withdrawals cannot all wait for deep manual review.
This is why providers market hot wallets as the layer for operating liquidity, not long-term vault storage. BitGo explicitly frames self-custody hot wallets as useful for transfers, staking, and DeFi, while recommending a broader setup that combines hot and colder forms of storage. That is a sensible pattern because the design pressure is real: some funds must be liquid if the operation itself is live.
Even newer authentication models fit this same pattern. WebAuthn, for example, allows authenticators to exist in software on general-purpose devices, not only in dedicated hardware. It also distinguishes between single-device and backup-eligible multi-device credentials. That does not automatically make a WebAuthn credential a blockchain wallet key, but it matters conceptually: modern digital identity systems are also grappling with the same tradeoff between portability, recoverability, and online usability on the one hand, and narrower attack surface on the other. As wallet designs evolve, the boundary between “wallet,” “authenticator,” and “signer” becomes more architectural and less purely physical.
What are the main risks associated with hot wallets?
| Attack vector | How it works | What it risks | Typical sign | Key mitigation |
|---|---|---|---|---|
| Phishing | Credential or access theft | Signer credentials | Unexpected approval prompts | Training, MFA, delays |
| Malware | Memory or key exfiltration | Private keys, seed phrases | Unknown outgoing txs | Device hygiene, hardware signer |
| Malicious dApp | Blind or deceptive requests | Authorized malicious txs | Opaque calldata shown | Intent decoding, consent |
| Compromised extension | Tampered provider object | Provider APIs exposed | Unexpected account exposure | Isolate providers, limit extensions |
| Operational exceptions | Legacy allowlists/backdoors | Validator or RPC access | Large unexplained outflows | Revoke access, monitoring |
The hot-wallet risk is not mysterious. It follows directly from the system being online.
If key material is generated or stored on a phone, laptop, browser extension context, or server environment, then compromise of that environment may compromise the wallet. Malware can inspect memory, modify transaction details, capture recovery phrases, or intercept approvals. A malicious website can ask for dangerous signatures. A phishing page can mimic a real dapp closely enough to fool a careful user. A compromised dependency or browser extension can tamper with what the wallet sees. The injected provider object itself must be treated carefully: EIP-1193 warns that because the provider is a JavaScript object exposed to page code, consumers should treat it as potentially adversarial and not rely on it for secrecy.
Notice what that warning means. The danger is not only “someone steals the key file.” The danger is also that the communication boundary between webpage and wallet is itself part of the threat model. A web page can read, overwrite, or manipulate objects in its own execution environment. So a wallet must assume the page may be malicious and keep sensitive logic isolated.
Operational systems face the same issue at a larger scale. The Ronin breach is a vivid example of what happens when online signing infrastructure is compromised. Attackers gained control of validator private keys through spear-phishing and then abused an allowlisted RPC path that had not been revoked. The core lesson is not just that phishing is bad. It is that network-reachable signing authority plus weak operational boundaries can become catastrophic. Monitoring failures then make it worse, because by the time the theft is noticed, onchain finality makes reversal unlikely.
The Binance breach described by TechCrunch shows another form of the same pattern: once attackers obtain the credentials and authority needed to move funds, the transfers themselves can succeed quickly, and the organization is forced into reactive containment. In crypto, prevention matters more than it does in systems where fraudulent transfers can routinely be reversed.
Research on browser-extension wallets points in the same direction. The WALLETRADAR paper argues that browser-based wallets have become prime targets and reports many discovered vulnerabilities across popular wallets. The exact categories vary, but the important point is structural: browser wallets are not risky because a few teams made avoidable mistakes. They are risky because they sit at the intersection of web threats, extension threats, cryptographic signing, and asset custody.
How does reducing reachable signing power improve hot-wallet security?
| Strategy | Primary goal | How it reduces reachability | Trade-off | Best for |
|---|---|---|---|---|
| Isolation & permissions | Limit webpage access | Separate provider from page | Slight UX friction | Consumer wallets |
| Multi-sig / MPC | Remove single point failure | Distributed key shares | Operational complexity | Institutions |
| Policy & velocity controls | Prevent unauthorized transfers | Whitelists and limits | Potential delays | Exchanges, treasuries |
| Decoding & simulation | Stop blind signing | Expose human intent | False negatives possible | All hot wallets |
| Monitoring & posture | Detect anomalies quickly | Alerts and posture checks | Detection may be late | Large operations |
Once you view the problem clearly, the security principle becomes simple: a hot wallet is safer when less authority is reachable by any single compromise.
There are several ways to do that, and they all express the same idea in different forms. A consumer wallet may isolate extension code from webpage code and require explicit permission before exposing accounts. EIP-1193’s standard errors for user rejection, unauthorized access, and disconnection exist partly so applications can respect these boundaries rather than guessing. Cardano’s CIP-30 similarly requires explicit enablement before a dapp can read wallet state, and it expects signing methods to ask for consent per call. These are permission boundaries around online power.
An institutional wallet may distribute power across multiple keys or key shares, separate initiation from authorization, and require a different device or trusted execution environment for approval. Fireblocks highlights multi-device approval, TEEs, and policy engines for exactly this reason: if the machine that prepares a transaction can also unilaterally approve it, a single compromise may be enough. Separate those roles, and the attacker’s job gets harder.
Another layer is policy. Whitelisting approved destinations, limiting transfer velocity, restricting who can move which assets, and forcing additional approval for large transfers do not change the blockchain’s cryptography. They change which signatures the system is willing to produce. Fireblocks argues that misconfigured policies are a primary root cause of incidents. Whether that statistic generalizes perfectly or not, the mechanism is persuasive. If the wallet signs exactly what a compromised operator or compromised app requests, the strongest cryptography in the world does not help.
The same logic explains transaction simulation and decoding. Users often imagine that the key risk is loss of secret material. In practice, blind signing is often just as dangerous. If a wallet shows opaque call data and the user approves it, the user may authorize token approvals, permit signatures, or contract interactions that later drain assets. Better interfaces reduce but do not eliminate this risk, because contract behavior can be subtle and user attention is limited.
Hot vs cold wallets: how to choose based on value, activity, and response time
People often talk as if hot wallets are “bad” and cold wallets are “good.” That is too crude to be useful.
Cold wallets reduce exposure by moving signing authority out of online reach, but they also increase friction. Hot wallets increase usability by keeping signing authority reachable, but they increase exposure. Neither is universally correct. The right question is: what amount of value, what kind of activity, and what response time does this setup need to support?
For a person experimenting with small sums in DeFi, a hot wallet may be entirely reasonable, especially if it is segmented from long-term savings. Ledger’s practical recommendation captures this well: keep a “vault” account for long-term holdings and a separate active wallet for web3 interactions, transferring only what you need. The exact tooling can vary, but the principle is durable. Do not expose your entire balance to the part of your setup that must remain online.
For an exchange, bridge, or institutional treasury, the same principle becomes architecture rather than personal habit. Some assets remain in hotter environments for operational liquidity; larger reserves stay in colder or more heavily controlled systems. BitGo explicitly recommends pairing hot, cold, and custody solutions. That is not marketing fluff so much as an admission of a real design constraint: no single wallet temperature solves every operational problem.
This also shows where the category boundary starts to blur. If a wallet uses MPC, hardware-backed approval devices, or policy-gated countersigning, is it still hot? Usually yes, if the system can still authorize transactions in an online workflow without an offline air-gap ceremony. “Hot” and “cold” are best understood as security postures defined by availability of signing authority, not by whether a product looks like a phone app or a hardware device.
What are common misconceptions about hot wallets?
A common misunderstanding is that a hot wallet is defined by where coins are stored. They are not stored in the wallet in the ordinary sense; the wallet controls keys and signatures that affect onchain state.
Another misunderstanding is that a hot wallet and a browser provider are the same thing. They are related but distinct. A provider is the API surface a dapp talks to. EIP-1193 explicitly says the provider is not responsible for private key or account management; the wallet middleware behind it is. This matters because developers sometimes over-trust the injected object they can see, while the truly sensitive logic should be elsewhere and more strongly isolated.
A third misunderstanding is that strong cryptography alone makes a hot wallet safe. It does not. Most catastrophic failures involve some combination of phishing, malware, poor permissions, blind signing, bad UX, compromised dependencies, operational exceptions, or policy mistakes. The signature algorithm may be flawless while the human and software system around it remains easy to exploit.
And finally, people often assume that “not your keys, not your coins” cleanly separates wallet categories. In reality, hot wallets exist in both self-custody and custodial forms. A self-custody mobile wallet may hold your own keys directly. A custodial exchange may operate a hot-wallet layer on your behalf. An institutional self-custody product may split keys across customer and provider roles. The relevant question is not only who legally or operationally holds the keys, but how reachable the signing authority is and what controls govern its use.
How should systems be designed to limit hot‑wallet blast radius?
Because hot wallets are inherently exposed, good design does not try to pretend they are as safe as offline storage. It limits blast radius.
That means minimizing balances held in hot environments, reducing permissions, segmenting accounts by purpose, using explicit consent flows, isolating wallet logic from untrusted page code, monitoring for anomalous outflows, and introducing approval friction precisely where the value at risk justifies it. It also means treating wallet software as security-critical infrastructure rather than simple UI.
The OWASP Web3 Wallet Security project exists for this reason. Even though its deliverables are still evolving, its premise is important: wallet security needs dedicated guidance, testing, and verification standards. Hot wallets are not just another application category. They combine identity, cryptography, user interaction, and irreversible asset transfer in one surface. That combination deserves specialized engineering discipline.
Conclusion
A hot wallet is a wallet whose signing authority is available from an internet-connected environment so that transactions and signatures can happen quickly. That online availability is why hot wallets power everyday crypto use (connecting to dapps, trading, staking, operational treasury flows, and automated services) and it is also why they are more exposed than colder forms of custody.
The idea to remember is simple: a hot wallet is not mainly about where assets are; it is about how reachable the power to sign is. Everything else follows from that. The more reachable that power is, the more useful the wallet becomes; and the more carefully its permissions, interfaces, policies, and failure modes must be designed.
How do you secure your crypto setup before trading?
Secure your crypto setup before trading by limiting online signing authority, segmenting funds, and inspecting every signature request. Cube Exchange uses a non-custodial MPC approach to keep signing available for fast trades while distributing authority; use the steps below to prepare your account and reduce reachable risk before you interact with markets or dapps.
- Deposit a small operating balance into your Cube account; move only the funds you expect to use in the next 24–72 hours.
- Confirm your Cube non-custodial MPC signers and enroll multi-factor authenticators; perform a low-value signed transfer to validate the signer and recovery flow.
- Create a dedicated hot address or sub-account for trading and dapp activity, and keep long‑term holdings in a separate cold vault or offline store.
- Before approving any on‑chain signature, expand the wallet prompt and decode intent: check the destination contract address, token approvals, and reject opaque hex or unfamiliar calls.
- For withdrawals to new external addresses, verify the recipient and chain via an independent channel and send a small test transfer first.
Frequently Asked Questions
A wallet is “hot” when its signing authority - that is, the ability to produce valid transaction signatures - is reachable from an internet-connected environment, meaning transactions can be authorized without moving to an offline device or ceremony.
The injected provider is a JavaScript object exposed to page code and the EIP-1193 spec explicitly separates that provider API from the wallet middleware that actually manages keys; implementers and dapps should treat the provider as potentially adversarial and not rely on it for secrecy or key management.
Multisignature and MPC reduce the danger of a single point of compromise by distributing signing power across multiple keys or shares, but they remain “hot” if the distributed signing can be exercised in an online workflow; they lower single‑component risk but introduce coordination, policy, and residual trust considerations.
Blind signing is approving opaque transaction data without meaningful decoding or simulation; it’s dangerous because attackers commonly rely on tricking holders into signing malicious contract calls or token approvals that drain assets even when cryptography itself is correct.
WebAuthn makes authenticators usable in general-purpose devices and changes the architecture of online credentials, but the spec does not define how WebAuthn keys should be mapped to blockchain wallet protocols, so using WebAuthn as a wallet key is an integration decision with privacy and lifecycle caveats.
For most users the recommended pattern is to segment funds: keep a smaller ‘active’ hot wallet for day‑to‑day interactions and a separate cold or hardware-backed vault for long‑term holdings, transferring only what you need into the hot environment.
Browser‑extension wallets are structurally attractive targets because they sit at the intersection of web threats, extension attack surface, and signing authority; empirical studies of browser wallets have found numerous vulnerabilities and many developers had to patch or confirm fixes after disclosure.
Institutions lower hot‑wallet risk by reducing reachable authority through controls such as whitelists, velocity limits, role separation (separate devices for initiation and approval), TEEs or hardware backends, pre‑execution simulation, and policy‑gated countersigning - each control raises the bar for an attacker but requires careful configuration and monitoring.
Related reading