What Is Key Derivation (BIP32/39/44)?
Learn how BIP-39, BIP-32, and BIP-44 turn one seed phrase into a structured wallet tree of keys, accounts, and addresses.
Introduction
Key derivation is the system that lets a wallet generate many private keys, public keys, and addresses from a single starting secret. That may sound like a convenience feature, but it solves a deeper problem: without deterministic derivation, every new address would require fresh backup material, and a wallet would become harder to recover every time it was used.
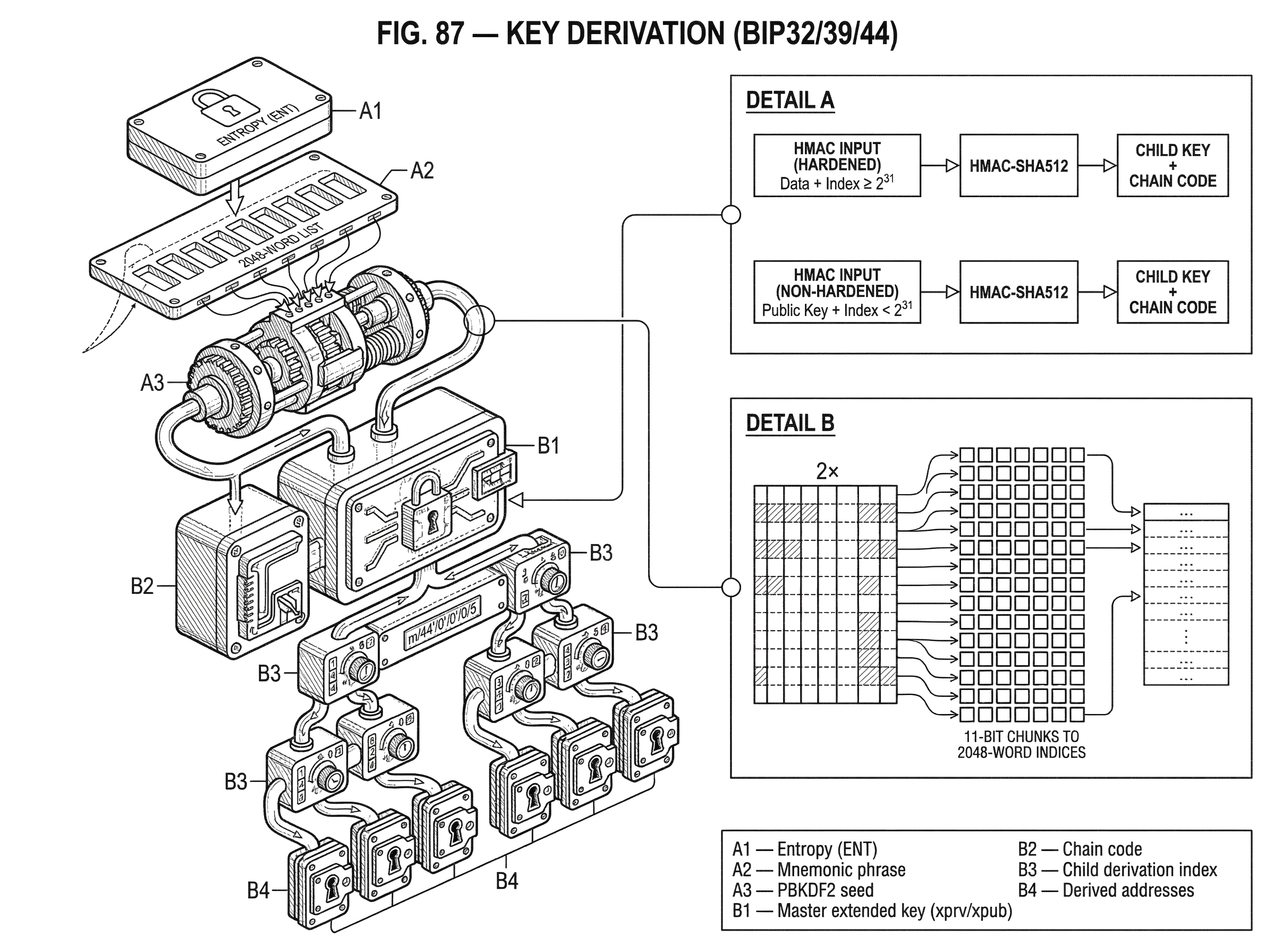
Modern wallets usually hide this machinery behind a seed phrase, a balance screen, and a receive button. Underneath, though, three standards usually do most of the work. BIP-39 defines how raw entropy can be encoded as a human-readable mnemonic and then turned into a binary seed. BIP-32 defines how that seed becomes a hierarchical deterministic tree of keys. BIP-44 defines a common layout for that tree so wallets can agree on where to look for accounts, change addresses, and coin-specific branches.
The important thing to see is that these are not three unrelated standards. They are three layers of one pipeline. First you need a durable secret humans can store. Then you need a way to derive many keys from it without randomness at each step. Then you need a shared convention so different wallets derive the same keys from the same secret. Once that clicks, the whole stack becomes much easier to reason about.
Why do wallets use deterministic key derivation for backup, sharing, and interoperability?
A wallet does not really hold coins. It holds secrets that authorize spending, and it usually needs many of them. Even a simple wallet may generate new receiving addresses over time, separate change addresses for returned funds, and multiple accounts for organization. If each address came from an unrelated private key, backup would be fragile: miss one key and some funds might become unrecoverable forever.
Deterministic key derivation changes the backup model. Instead of backing up every private key individually, you back up a single root secret and regenerate the rest when needed. The wallet becomes a reproducible structure rather than a bag of unrelated secrets.
The second problem is selective sharing. Sometimes you want another system to see addresses and balances without being able to spend. An accounting system, a watch-only wallet, or a hardware signer coordinator may need to derive public receiving addresses while never touching the private keys. A good derivation system should support that separation where possible.
The third problem is interoperability. If two wallets recover from the same seed but organize their key tree differently, both may be “correct” and still fail to find the same funds. So beyond the cryptography, wallets need conventions about where particular kinds of keys live.
How does BIP-39 convert entropy into a mnemonic and derive a seed?
| Entropy (bits) | Checksum bits | Total bits | Mnemonic words |
|---|---|---|---|
| 128 | 4 | 132 | 12 words |
| 160 | 5 | 165 | 15 words |
| 192 | 6 | 198 | 18 words |
| 224 | 7 | 231 | 21 words |
| 256 | 8 | 264 | 24 words |
BIP-39 starts with a practical observation: humans are bad at preserving raw binary data. A 128-bit or 256-bit secret is excellent cryptographic material, but terrible backup material. A short list of carefully chosen words is easier to write down, check, and re-enter.
The standard begins with random entropy, denoted by ENT, whose length must be a multiple of 32 bits and may range from 128 to 256 bits. It then appends a checksum of length ENT/32, taken from the first bits of SHA-256(entropy). That combined bitstring is split into 11-bit chunks, and each chunk indexes one word from a 2048-word list. Because 2^11 = 2048, every 11-bit value maps cleanly to one word.
This is why common mnemonic lengths come in familiar sizes. With 128 bits of entropy, the checksum is 4 bits, giving 132 bits total, which becomes 12 words. With 256 bits of entropy, the checksum is 8 bits, giving 264 bits total, which becomes 24 words. The words are not the seed themselves. They are an encoding of entropy plus a checksum that helps detect transcription mistakes.
That distinction matters because many people informally say “the 12 words are my private key.” Mechanically, that is not quite right. The mnemonic is a human backup representation. To get the binary seed used by HD derivation, BIP-39 runs a key-derivation function: PBKDF2-HMAC-SHA512 with the mnemonic as the password, the salt equal to the string "mnemonic" concatenated with the optional passphrase, 2048 iterations, and a 64-byte output.
The optional passphrase is often called the “25th word,” though that phrase is only an informal nickname. Every passphrase produces a different valid seed. That means the passphrase is not a checksum or a simple unlock code layered on top of a fixed wallet. It is part of the seed derivation itself. Change the passphrase, and you get a different wallet tree.
This gives a useful property and a dangerous one. The useful property is plausible deniability: multiple passphrases can lead to different valid wallets. The dangerous one is that there is no built-in signal telling you that a passphrase was “wrong.” A typo can produce a perfectly valid but empty wallet.
BIP-39 also discourages treating user-invented sentences as seeds. The security comes from the original entropy, not from words that merely look mnemonic-like. The wordlists are designed for reliable encoding and recovery, not for turning memorable phrases into high-entropy secrets.
How does BIP-32 derive a hierarchical tree of keys from a seed?
If BIP-39 gives you a 64-byte seed, BIP-32 answers the next question: how do you turn that one seed into a large, structured family of keys?
The core idea is simple. A wallet should be able to derive child keys from parent keys in a way that is deterministic, reproducible, and branchable. If you know the root, you can regenerate the whole tree. If you know only a subtree root, you can regenerate only that subtree. This is why BIP-32 wallets are called hierarchical deterministic wallets: deterministic because the same input always yields the same tree, hierarchical because the results are arranged as parent-child branches rather than as one flat sequence.
BIP-32 does not use an ordinary private key alone as the parent material. Instead it defines an extended key, which is a pair: the key itself plus a 32-byte chain code. For an extended private key that pair is (k, c), where k is the private key and c is the chain code. For an extended public key it is (K, c), where K is the public key corresponding to k.
The chain code is the piece many readers first overlook, but it is what makes the construction work cleanly. Without it, derivation would be too tightly tied to the key material itself. The chain code acts as additional derivation entropy. Child derivation depends on both the parent key and the chain code, which lets the wallet derive structured descendants without simply “reusing the private key in a clever way.”
The master extended private key is derived from the seed S by computing HMAC-SHA512 with key "Bitcoin seed" and data S. The 64-byte output is split into left and right halves, usually called IL and IR. IL becomes the master private key material, and IR becomes the master chain code.
From there, child derivation repeats the same pattern: hash parent material plus an index, split the result into two halves, use one half to tweak the key, and use the other half as the child chain code. The index tells the wallet which child it is deriving, so the parent can have many children.
How does BIP-32 child derivation work (normal vs hardened indices)?
| Index range | HMAC input | Derive from xpub? | Typical use |
|---|---|---|---|
| 0..2^31−1 | parentpub || index | Yes | watch-only address generation |
| 2^31..2^32−1 (i') | 0x00 || parentpriv || index | No | isolation / limit upward recovery |
Each parent can derive children numbered by 32-bit indices. BIP-32 splits that space into two halves. Indices 0 through 2^31 - 1 are normal children. Indices 2^31 through 2^32 - 1 are hardened children. A hardened index is often written as i' or iH, meaning i + 2^31.
This split is not arbitrary notation. It creates two different derivation modes with different security and sharing properties.
When deriving a child private key from a parent private key, BIP-32 uses HMAC-SHA512 keyed by the parent chain code. For a hardened child, the HMAC input includes `0x00
| parent_private_key | child_index. For a normal child, it includes parent_public_key | child_index`. The left half of the output is interpreted as a number and added to the parent private key modulo the curve order; the right half becomes the child chain code. |
The consequence is the part worth remembering. Normal derivation can be aligned between private and public trees; hardened derivation cannot. For normal children, you can derive a child public key either from the parent private side or directly from the parent extended public key. For hardened children, you must have the parent private key.
BIP-32 also defines public-parent to public-child derivation, usually called CKDpub, but only for non-hardened indices. Mechanically, it uses the parent public key and chain code to derive a tweak, then adds that tweak at the public-key level. This is what makes watch-only wallets possible: an extended public key can generate many descendant public keys and addresses without exposing any spending ability.
A worked example makes this concrete. Imagine a merchant server that should generate a fresh receive address for every invoice, while the hardware wallet holding funds stays offline. The owner exports an account-level extended public key to the server. Each time a customer checks out, the server increments an address index and derives the next public key on the external chain. It can display a new address and monitor payments, but it cannot sign a transaction because it has no descendant private keys. The offline signer, starting from the same seed, can derive the matching private keys when spending is needed. That is the mechanism, not just the outcome: both sides stay in sync because they are traversing the same deterministic branch, but only one side has the private half of the tree.
Why do wallets use hardened derivation and what attack does it prevent?
If non-hardened derivation enables convenient public-key-only workflows, why not make everything non-hardened?
Because the convenience comes with a sharp edge. BIP-32 notes an important weakness: if someone knows a parent extended public key and also learns any non-hardened descendant private key, that combination is enough to recover the parent extended private key. In other words, a leaked child private key can climb back up the tree if the matching ancestor xpub is known.
That is the reason hardened derivation exists. It breaks that upward relation by making the child derivation depend on the parent private key directly. A hardened child can still be deterministically regenerated from the seed, but it cannot be derived from an xpub alone, and the parent xpub plus child private key attack no longer applies across that hardened boundary.
This is also why common wallet path schemes harden the higher structural levels, such as purpose, coin type, and account. Those levels separate major branches of identity and organization. If a wallet leaks a receive-side private key somewhere lower in the tree, hardened boundaries reduce how far upward that leak can propagate.
There is a tradeoff. Hardened derivation improves isolation, but it removes the ability to derive that branch from public data alone. So wallet designers typically use hardened derivation for branch boundaries and non-hardened derivation where watch-only address generation is useful.
What are extended keys (xprv/xpub) and why are they sensitive?
An extended key is more than the raw key and chain code in memory. BIP-32 also defines a standard serialized form containing version bytes, depth, parent fingerprint, child number, chain code, and key data. That serialized structure is then Base58Check-encoded.
On Bitcoin mainnet, serialized extended private keys commonly appear with the prefix xprv, and extended public keys with xpub. On testnet they commonly appear as tprv and tpub. These prefixes are convenient signals, but the important thing is what the data represents: not a single key, but the root of a subtree.
That makes an xpub much more sensitive than an ordinary public key. A normal public key reveals one verifying key. An xpub can reveal an entire family of descendant public keys, addresses, and wallet structure below its level. In operational terms, giving out an xpub is closer to giving read access to part of a wallet than to publishing a single address.
That sensitivity shows up in multisig and PSBT workflows too. Standards such as PSBT carry BIP-32 derivation information so signers can locate which keys correspond to which inputs and outputs. Hardware wallets often rely on xpubs, fingerprints, and derivation paths to verify change outputs and reconstruct how a transaction fits into a known wallet. If those xpubs are wrong or maliciously substituted, the wallet can be tricked into deriving and approving the wrong addresses. That is why xpub verification is a real security issue, not just a bookkeeping detail.
What is the BIP-44 path format and how does it organize accounts and addresses?
| Level | Hardened? | Role | Reason |
|---|---|---|---|
| purpose' | Yes | scheme id | identifies derivation standard |
| cointype' | Yes | separates coins | avoid cross-coin reuse |
| account' | Yes | user accounts | isolate user identities |
| change | No | external/internal | allow xpub address gen |
| addressindex | No | address index | enumerate receive addresses |
BIP-32 gives you a tree, but not a single canonical way to organize it. BIP-44 adds a shared layout so wallets can derive and discover accounts consistently.
Its standard path is:
m / purpose' / coin_type' / account' / change / address_index
Here m means the master node. The apostrophe marks hardened derivation. The first three levels are hardened; the last two are not.
The logic of this layout is easier to understand from the top down. The purpose' field says which derivation scheme the subtree follows. For BIP-44 itself this is 44'. The coin_type' field separates coins into different hardened branches so keys for one network are not silently reused on another. The account' field separates user-level account groupings. Then change picks between the external chain 0 and the internal change chain 1. Finally address_index walks forward through individual addresses.
This is not merely aesthetic structure. It encodes where isolation is needed and where public derivation is useful. The high-level branches are hardened because they represent major administrative boundaries. The change and address_index levels are non-hardened because wallets often need to derive receiving and change addresses from an account xpub.
A practical example is a standard Bitcoin single-account wallet using m/44'/0'/0'/0/5. Read in plain English, that means: start at the master node, use the BIP-44 subtree, go to Bitcoin coin type 0', choose account 0', use the external receiving chain 0, then take address index 5. The matching change address branch would live under ... /1/... instead.
BIP-44 also defines wallet discovery behavior. When recovering from a seed, a wallet cannot scan infinitely many possible addresses, so it uses an address gap limit. BIP-44 sets that limit to 20 for the external chain: if the wallet sees 20 consecutive unused addresses, it assumes there are no used addresses beyond that point and stops scanning. This is a practical compromise between exhaustive search and acceptable recovery cost.
The compromise matters. If a wallet or user generates long runs of unused receive addresses beyond the gap limit, another wallet importing the same seed may fail to discover later used addresses. So interoperability depends not only on the path shape but also on shared assumptions about discovery.
When does BIP-44 apply and which ecosystems use different derivation standards?
BIP-44 became common because it gave wallet developers a simple answer to a coordination problem. If everyone says “account 0, external chain, address 12” in the same way, seed recovery across wallets becomes much more reliable.
But the underlying idea is broader than Bitcoin, and the exact details can differ across ecosystems. Many wallets use BIP-39 mnemonics even on chains that do not use secp256k1 in the same way Bitcoin does. Many also borrow BIP-44-style path notation while changing curve assumptions or derivation rules underneath.
That is where adjacent standards matter. SLIP-0010 generalizes hierarchical derivation to curves beyond secp256k1, including ed25519 and curve25519. The crucial difference is that for ed25519-style schemes, normal public derivation is generally not supported, so wallets often use hardened-only derivation. This changes the design space: if you cannot derive public descendants from an xpub-like object, watch-only patterns and account sharing work differently.
You can see that divergence in real ecosystems. Cardano’s CIP-1852 keeps the broad shape m / purpose' / coin_type' / account' / role / index, but uses purpose 1852' and BIP32-Ed25519 rather than standard BIP-32. Polkadot uses a different derivation syntax entirely, with distinct hard and soft derivation markers. Cosmos documentation has wrestled with the mismatch between BIP-44’s UTXO-oriented structure and account-based chains. So the central idea (derive a family of keys from one root) travels widely, but the exact mechanics and path conventions are not universal.
That is why a recovery phrase alone does not guarantee cross-wallet compatibility. You also need agreement on the mnemonic standard, the seed derivation method, the curve, the path convention, and sometimes the address format layered on top.
What common mistakes and recovery failures arise from key derivation?
The first common misunderstanding is to blur together the mnemonic, the seed, and the keys. They are related, but not identical. The mnemonic encodes entropy and checksum. The seed is derived from the mnemonic, optionally with a passphrase. The master extended key is derived from the seed. Child keys are then derived from the master. If any layer changes, the resulting wallet changes.
The second misunderstanding is to treat xpubs as harmless. They cannot spend funds, but they can reveal a large portion of wallet activity and structure. In some setups they also become security-critical metadata. Especially in multisig, substituting the wrong xpubs can redirect funds or sabotage recovery.
The third is to assume path notation is cosmetic. It is not. m/44'/0'/0'/0/0 and m/44'/60'/0'/0/0 are different branches. Even on the same seed, different paths produce different keys. A wallet recovered with the wrong path may appear empty even when the seed is correct.
There are also edge cases at the specification level. BIP-32 notes that some derived values are invalid, such as when the intermediate scalar is out of range or the resulting key becomes zero. Implementations are supposed to skip that index and try the next. The probability is extremely small, but it is part of the standard and matters for correctness.
Finally, there is a practical recovery limit built into wallet discovery. If software assumes the BIP-44 gap limit and the user has exceeded it, some used addresses may not be found automatically. Nothing cryptographic has failed; the wallet and the discovery policy have simply fallen out of sync.
How do wallets and services use key derivation in practice (watch-only, multisig, merchant flows)?
In everyday wallet use, this machinery enables three things at once. It gives users a single backup to protect. It lets wallets generate fresh addresses without asking the user to manage new secrets. And it allows different devices to hold different levels of authority.
A hardware wallet often keeps the seed and private derivation path offline, while a companion app holds account xpubs to watch balances and request fresh receive addresses. An exchange or merchant system may derive public addresses on a server but keep spending authority on a separate signer. In multisig, several devices contribute xpubs and signatures according to a known derivation structure. In each case, the wallet is really using the same underlying idea: derive exactly the keys you need, from exactly the branch you intend, while revealing as little else as possible.
That is why key derivation sits at the center of wallet design. It is backup design, permission design, interoperability design, and privacy design all at once.
Conclusion
BIP-39, BIP-32, and BIP-44 form a pipeline: words become a seed, the seed becomes a key tree, and the tree gets a shared layout. The memorable idea is that a modern wallet is not a collection of random keys. It is a reproducible structure grown from one root secret, with hardened boundaries for isolation and shared path conventions for recovery.
If you remember one thing, remember this: the seed is the root, the derivation path is the map, and the wallet’s addresses are just leaves on that tree.
How do you secure your crypto setup before trading?
Key Derivation (BIP32/39/44) belongs in your security checklist before you trade or transfer funds on Cube Exchange. The practical move is to harden account access, verify destinations carefully, and slow down any approval or withdrawal that could expose you to this risk.
- Secure account access first with strong authentication and offline backup of recovery material where relevant.
- Translate Key Derivation (BIP32/39/44) into one concrete check you will make before signing, approving, or withdrawing.
- Verify domains, addresses, counterparties, and approval scope before you confirm any sensitive action.
- For higher-risk or higher-value actions, test small first or pause the workflow until the security check is complete.
Frequently Asked Questions
The optional passphrase is folded into PBKDF2 with the mnemonic to produce the seed, so changing or omitting it yields a completely different wallet tree; it therefore provides plausible deniability but also means a typo or wrong passphrase produces a valid yet different (often empty) wallet with no built‑in warning.
Hardened derivation prevents attacks where a known child private key plus a parent xpub can recover the parent private key, so wallets harden high‑level boundaries (purpose, coin, account) to isolate branches; non‑hardened derivation preserves the ability to derive public children from an xpub and is used where watch‑only workflows are needed, at the cost of weaker isolation.
Yes - recovering funds requires matching not only the mnemonic but also the seed derivation method, passphrase, curve and the exact derivation path/account/coin_type and address format; recovering with the wrong path or different chain conventions can leave the wallet looking empty even though the seed is correct.
BIP‑44 defines an address gap limit of 20 on the external chain: a wallet stops scanning after 20 consecutive unused addresses, so if used addresses exist beyond that run of unused addresses another wallet importing the same seed may not discover them automatically.
Not reliably; cross‑wallet compatibility depends on agreeing on the mnemonic standard, the PBKDF2 seed derivation, the signature curve and derivation scheme (BIP‑32 vs SLIP‑0010/ed25519), and the path convention - differences in any of these can make the same words yield incompatible keys or addresses.
Watch‑only setups use an extended public key (xpub) and BIP‑32 non‑hardened child derivation: the xpub plus chain code lets the watcher compute descendant public keys and produce addresses but not private keys, while the signer (offline) derives the matching private keys from the seed when spending is needed.
The BIP‑32 spec requires implementations to skip indices that produce invalid intermediate values (e.g., parse256(IL) ≥ n or a zero key) and try the next index; these events are extremely unlikely but must be handled to be standards‑compliant.
PSBTs can carry xpubs and derivation paths to help signers reconstruct keys, but embedding xpubs or BIP‑32 derivation data can leak wallet structure and privacy, and a substituted or malicious xpub inside PSBT metadata can trick signers, so applications should treat embedded extended‑key data as sensitive and verify it when possible.
BIP‑39 explicitly discourages turning user‑created memorable sentences (brainwallets) into mnemonics because security derives from true entropy, not from mnemonic‑like phrases, so relying on a crafted low‑entropy phrase undermines seed strength and is discouraged.
Related reading