What is a Cold Wallet?
Learn what a cold wallet is, how offline key storage and signing work, why it improves security, and where backups and device trust still matter.
Introduction
Cold wallet means a wallet setup in which the private keys are kept offline, away from internet-connected systems. That idea matters because in crypto, control of assets ultimately reduces to control of signing keys: if an attacker gets the key, they can usually move funds, and those transfers are often irreversible once finalized. A cold wallet is therefore not mainly about convenience or interface design. It is a security architecture built around a narrow goal: reduce the number of ways a key can be exposed.
The key contrast is with a hot wallet. A hot wallet keeps keys on a device that is routinely online; a phone, browser extension, laptop, or server. That makes everyday use easier, but it also means the same environment that displays balances and prepares transactions is exposed to malware, phishing flows, malicious browser extensions, credential theft, and other network-mediated attacks. Cold storage tries to break that coupling. The machine that talks to the network may still prepare information, but the secret that authorizes spending is kept elsewhere.
That sounds like a simple binary (offline or online) but in practice cold wallets are better understood as a design principle: keep private keys offline for as much of their lifecycle as possible, and move only the minimum information needed across the boundary between online and offline systems. Once you see that, many familiar tools fall into place: hardware wallets, air-gapped signing devices, mnemonic backups, PSBT workflows in Bitcoin, and chain-specific offline signing formats elsewhere.
What problem does a cold wallet solve?
| Aspect | Hot wallet | Cold wallet | Best choice |
|---|---|---|---|
| Connectivity | Routinely online | Key stored offline | Cold for long-term holdings |
| Attack surface | High remote exposure | Reduced remote exposure | Cold for high-value custody |
| Convenience | Fast, mobile | Extra steps, slower | Hot for frequent small spends |
| Recovery risk | Device present eases restore | Backup (seed) critical | Plan backups for cold |
A blockchain does not know who you are in any ordinary sense. What it can verify is whether a transaction carries a valid signature from the key authorized to spend certain funds or control an account. So the real custody problem is not “where are my coins?” but “where is the signing authority, and who can make it produce a valid signature?”
If that signing authority lives on a general-purpose online device, the attack surface is broad. Malware can try to steal seed phrases, scrape memory, alter destination addresses, replace copied addresses in the clipboard, or trick the user into approving the wrong transaction. Phishing can try to capture recovery words. Malicious software updates can target the wallet itself. In an institutional setting, the risks widen further to insider abuse, weak operational procedures, and overexposed infrastructure.
Cold storage narrows this by changing the mechanism. Instead of asking an online computer to both construct and sign a transaction, it splits those roles. The online environment can gather chain data, calculate balances, choose inputs or accounts, and build an unsigned transaction. But the actual signature is produced in an environment designed to keep the private key isolated. That isolation is the point. If the network-facing machine is compromised, the attacker may still have influence (for example, by preparing a deceptive transaction) but they should not be able to directly extract the key merely because the wallet was used.
This is why cold wallets are especially associated with storing larger amounts or long-term holdings. The less often you need to spend, the more rational it becomes to accept extra friction in exchange for a smaller attack surface. Bitcoin.org describes hardware wallets as ideal for storing large amounts of bitcoin for exactly this reason: they keep funds offline and are connected only when management is required.
What does “offline” mean for a cold wallet?
It is easy to misunderstand cold storage as meaning “a device that never touches a cable” or “something hidden in a safe.” Those can be part of the practice, but the deeper idea is more precise: the private key should not be exposed to a networked environment as data that can be copied out and reused elsewhere.
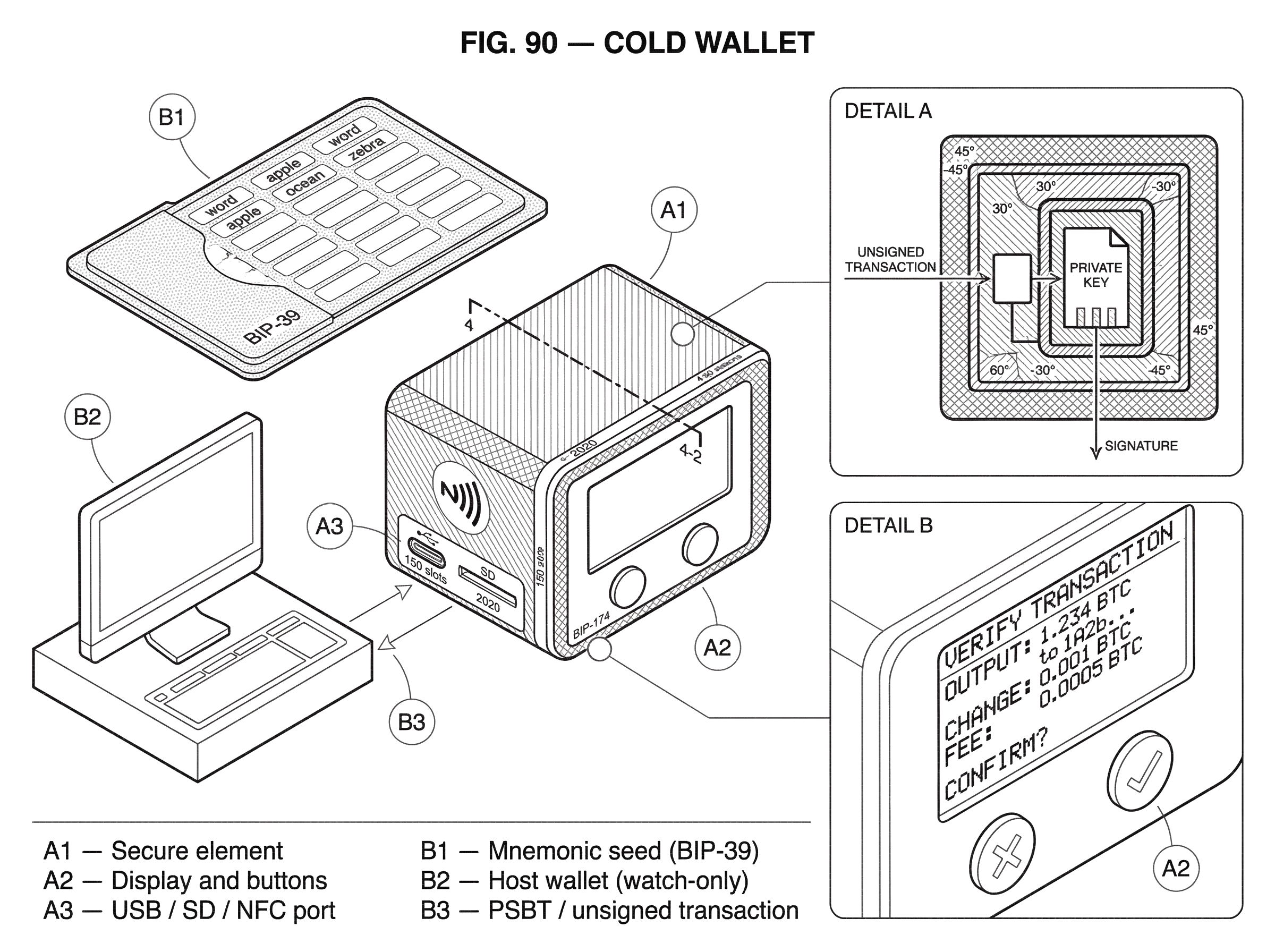
A hardware wallet illustrates this well. It is a purpose-built signing device that stores key material offline and is connected to a computer only when you need to manage funds. The important property is not merely that it is small or separate. It is that the host computer should not receive the private key. Instead, the host sends transaction data to the device, the device shows critical details to the user, and if approved, the device returns only the signature or signed transaction.
That is cold storage in miniature: data can cross the boundary, but the secret should not. Some devices go further and avoid a live wired connection entirely, using SD cards, QR codes, or NFC to move unsigned and signed transaction data between the online wallet software and the offline signer. COLDCARD, for example, supports PSBT transfer by SD card, virtual disk, NFC, and on some models QR code, while keeping private keys completely offline as its core security model.
The phrase air-gapped is often used here. Strictly speaking, an air gap means the signing device is never directly network-connected. That can improve isolation, but it is not magic. A USB-connected hardware wallet can still be “cold” in the meaningful sense if the key never leaves the secure signing environment. Conversely, an air-gapped workflow can still fail if users do not verify what they are signing, or if backups are mishandled.
How does a cold wallet sign transactions offline?
The simplest way to understand a cold wallet is to separate the workflow into three distinct things: key generation, transaction construction, and transaction signing.
The first step is creating the secret. In modern wallets this is usually done through a deterministic seed. BIP-39 specifies a mnemonic sentence (a short list of words) that represents underlying entropy and can be converted into a binary seed. That seed then feeds into an HD wallet structure such as BIP-32, which derives a tree of keys from one root. The practical consequence is important: instead of backing up every address separately, you back up the seed once and can later regenerate the wallet’s keys.
This is one reason cold wallets became operationally practical. Before deterministic wallets, secure backup was awkward and error-prone. With an HD wallet, a single seed can recreate the whole key tree. BIP-32 defines how the master key is derived from a seed and how child keys are derived in a structured hierarchy. It also defines extended public keys and extended private keys, which matter because they let a system share viewing or address-generation capability without sharing spending power; at least within certain limits.
Now consider a spend. The online wallet prepares transaction data using public information from the chain and, depending on the architecture, public derivation data from the wallet. In Bitcoin, this often means creating a PSBT, a Partially Signed Bitcoin Transaction. BIP-174 defines PSBT specifically so a signer can be offline while still receiving all information needed to produce signatures. The PSBT contains the unsigned transaction plus additional data the signer needs to verify inputs, scripts, and related details.
The offline signer then reviews that transaction. This review is not cosmetic. It is one of the most important controls in the entire design. If the host computer is compromised, it may try to substitute a different destination address, manipulate change outputs, or attach an excessive fee. A trustworthy cold signer therefore needs its own display and confirmation path so the user can verify what is actually being signed. COLDCARD’s workflow shows this clearly: before signing, it displays a detailed breakdown and warnings for unusual fees or suspicious change.
Once approved, the signer computes the required signatures and returns only the signed transaction data. The online machine can then broadcast it to the network. The secret key never needed to reside on the internet-facing device.
How do I send funds using an offline signer?
Imagine Alice holds a meaningful amount of bitcoin in a hardware wallet and uses desktop wallet software on her laptop for balance tracking and transaction preparation. Her laptop is online; the hardware wallet is her cold signer.
Alice opens the desktop wallet and enters Bob’s address and amount. The desktop wallet looks at available unspent outputs, estimates a fee, and prepares an unsigned transaction. If it supports offline workflows well, it packages this as a PSBT. At this point, the laptop has done all the computationally messy but non-secret work. It knows public chain data. It knows what Alice wants to send. But it still cannot authorize the spend.
Alice transfers the PSBT to the signer. Depending on the device, that may happen through USB, SD card, NFC, or QR code. The hardware wallet parses the transaction and shows her the outputs, fee, and often the change details. This moment is the heart of the security model. If malware on the laptop quietly replaced Bob’s address with an attacker’s address, the signer’s display is where Alice can catch it; assuming she actually checks.
If she confirms, the hardware wallet signs the necessary inputs and returns the partially or fully signed transaction. The laptop receives only the signatures and assembles the final transaction. It then broadcasts that transaction to the Bitcoin network. The laptop helped construct and relay the spend, but the authority to spend remained isolated.
This same pattern appears outside Bitcoin, even though the formats differ. On Solana, for example, a transaction includes instructions, signatures, and a recent blockhash. Cold signing must account for the fact that the blockhash expires after 150 slots unless durable nonces are used. In Cosmos SDK chains, the offline signer must sign exact canonical bytes determined by the relevant sign mode, such as SIGN_MODE_DIRECT, because the network validates signatures over a specific serialized message. The details differ, but the architecture is the same: online system prepares, offline system signs, online system broadcasts.
Why are deterministic seeds and backups essential for cold wallets?
| Scheme | Recovery guarantee | Resilience | Complexity |
|---|---|---|---|
| BIP-39 single seed | Full wallet restore | Single point of failure | Low complexity |
| BIP-39 + passphrase | Alternate/hidden wallets | Loss if passphrase lost | Low–medium complexity |
| SLIP-39 Shamir | Threshold restore | Distributed resilience | Higher complexity |
| Multisig backups | On-chain multi-key restore | Removes single custodian | Operationally heavy |
A cold wallet is only as good as its recovery story. If the signing device is lost, destroyed, or becomes unusable, the user still needs a way to regenerate the keys. That is why seed phrases are not a side detail; they are part of the foundation.
BIP-39 mnemonics turn entropy into a list of words that humans can record and later re-enter. The wallet uses that mnemonic, optionally with a passphrase, to derive the binary seed. Because every key in the HD wallet flows from that seed, the backup becomes compact and portable. Lose the device, keep the seed, and you can usually restore the wallet elsewhere. Lose both, and the funds may be unrecoverable.
That last point is not theoretical. Bitcoin.org explicitly warns that loss of a hardware device without a proper backup can make funds unrecoverable. Cold storage removes some classes of remote attack, but it also increases the importance of operational discipline. A hot wallet often feels forgiving because the device is always present and easy to access. A cold wallet asks you to take backup seriously before anything goes wrong.
This is also where passphrases and split backups enter the picture. BIP-39 allows an optional passphrase, and every passphrase yields a valid seed. That can provide an extra protection layer and even plausible deniability, but it also means the passphrase becomes part of the recovery secret. Forget it, and the mnemonic alone may restore the wrong wallet.
For more elaborate backup schemes, SLIP-39 standardizes mnemonic Shamir secret sharing, where the secret is split into multiple shares and only a threshold is needed to reconstruct it. This can reduce single-point-of-failure risk in backup storage. But it also increases procedural complexity. That trade-off is typical in cold storage: stronger resilience often comes not from a single trick, but from adding structure and accepting more operational burden.
What security assumptions must a cold wallet device meet?
| Threat | Effect on cold wallet | Mitigation |
|---|---|---|
| Supply-chain tamper | Compromised seed generation | Buy sealed device; verify |
| Malicious firmware | Fake UI and confirmations | Verify firmware hash/auth |
| Counterfeit device | Backdoored hardware | Purchase from trusted seller |
| Physical coercion | Forced signing or seed theft | Legal and operational controls |
People sometimes speak as if “offline” alone guarantees safety. It does not. A cold wallet still depends on several assumptions, and one of the biggest is that the signing environment itself has not been compromised.
A hardware wallet is useful because it gives the user a trusted place to verify and authorize a transaction.
If that trust is broken the cold-wallet model weakens sharply.
- through malicious firmware
- counterfeit hardware
- tampering before delivery
- a compromised display path
Trezor’s public security material reflects this by treating seed extraction, PIN bypass, bypassing user confirmation, private key extraction, and physical or supply-chain attacks as top-tier threats. That framing is important: once the device becomes the root of trust, attacks on the device become central.
This is why firmware authenticity checks and device authentication matter. Trezor provides both a firmware hash check and a device authenticity check for some devices. The goal is not abstract compliance. It is to answer a concrete question before you entrust a seed to the device: am I really using the device and firmware I think I am using?
The need is not hypothetical. Public research has shown that supply-chain and architecture-level weaknesses can undermine hardware-wallet assumptions. Saleem Rashid’s Ledger Nano S research described how a non-secure microcontroller in front of the secure element could be manipulated to affect seed generation and user-facing trust signals in certain attack models. Whether or not a particular device family has since changed its mitigations, the lesson is general: cold-wallet security is not just about keeping a key offline. It is about whether the entire path from user review to signature generation remains trustworthy.
What threats do cold wallets protect against, and which do they not?
Cold wallets are strong against a particular family of threats: attacks that rely on your private key living in an internet-connected environment. That includes many forms of malware-driven key exfiltration, remote compromise of a desktop or phone, credential-stealing browser extensions, and some phishing outcomes where the attacker needs the actual secret key to move funds.
But the protection is narrower than marketing sometimes implies. A cold wallet does not automatically protect against physical theft, coercion, insider collusion, poor backup handling, malicious firmware, device tampering, or being socially engineered into signing the wrong transaction. It also does not protect against exposing your seed phrase during setup, photographing your recovery words, storing the mnemonic in cloud notes, or entering the seed into a fake recovery webpage. In practice, many real compromises happen through these side channels rather than through pure cryptographic failure.
Cold storage also does not eliminate privacy risk. Ledger’s 2020 e-commerce and marketing data breach did not reportedly affect hardware wallets, Ledger Live security, or customer assets, but it did expose customer contact and order data. That matters because customer lists for cold-wallet purchases can become phishing targets. The lesson is subtle but important: you can keep keys offline and still be exposed through the surrounding business and support infrastructure.
So the right mental model is not “cold wallets make theft impossible.” It is “cold wallets shrink remote key-exposure risk, while shifting the remaining risk toward device trust, backups, physical security, and human procedure.”
How do extended public keys (xpubs) enable watch‑only wallets and what are the risks?
Cold-wallet setups often need the online side to generate receiving addresses or monitor balances without gaining spending authority. HD wallets make this possible through extended public keys. In BIP-32, an extended key is not just a key; it is a key plus a chain code, which allows deterministic derivation down a tree.
This is useful because the cold signer can keep the private root offline while sharing a “neutered” public version with a watch-only wallet. The watch-only wallet can then derive addresses, detect incoming funds, and prepare transactions without access to the private keys. That is one of the enabling tricks behind practical cold storage.
But it is not free of sharp edges. BIP-32 explicitly notes an important weakness: knowledge of a parent extended public key together with any non-hardened descendant private key can reveal the parent extended private key. For most end users, the operational takeaway is simple: extended public keys are more sensitive than ordinary single public keys, and derivation choices matter. The convenience of letting an online system derive addresses must be balanced against what other key material could leak elsewhere.
How do cold‑signing workflows differ across blockchains (Bitcoin, Solana, Cosmos)?
It is tempting to think of cold wallets as a Bitcoin-specific culture because Bitcoin has mature hardware-wallet and PSBT tooling. But the concept applies anywhere a network accepts cryptographic signatures authorizing state changes.
What changes from chain to chain is not the reason for cold storage but the exact bytes that must be signed and the constraints around doing so. Solana, for example, ties transaction validity to a recent blockhash unless durable nonces are used. That means naive offline signing can fail simply because too much time passes before broadcast. In Cosmos SDK chains, sign modes exist partly because signing needs canonical, deterministic bytes, and the newer SIGN_MODE_TEXTUAL is explicitly designed to improve hardware-wallet readability on small screens.
These examples show something deeper. A cold wallet is not a single device type. It is a separation-of-duties pattern that each chain has to support through its transaction model. Bitcoin expresses this with PSBT. Other ecosystems use different transaction containers and signing modes. The implementation changes, but the invariant stays the same: keep the signing secret isolated from the network-facing environment.
Why are cold wallets less convenient than hot wallets?
The inconvenience of cold storage is not a bug that designers forgot to fix. Much of it is the cost of preserving the security boundary.
Bitcoin.org notes that hardware wallets are difficult to use while mobile and are not designed for scanning QR codes in the same way many phone wallets are. More broadly, every extra review step, cable, QR transfer, or SD card shuffle is friction added to prevent the online environment from quietly doing too much. If you could spend from cold storage with the same speed and invisibility as from a browser extension, you would usually have removed the very separation that makes it cold.
That is why many people and institutions do not choose a single wallet type for everything. They use hot wallets for frequent, low-stakes activity and cold wallets for larger or long-term holdings. The split mirrors the trade-off: convenience where speed matters, isolation where consequence matters.
At larger scale, this logic extends to multisignature setups, MPC workflows, or HSM-backed vaults. Those are not replacements for the core cold-wallet idea so much as more elaborate versions of the same principle: do not let a single online compromise immediately turn into total loss of control.
Conclusion
A cold wallet is a wallet architecture that keeps private keys offline so an internet-connected device can prepare transactions without directly holding the authority to sign them. Its value comes from a simple mechanism: separate network access from key custody, and many common remote attacks stop at the boundary.
But that boundary is only as strong as the system around it. Cold wallets depend on trustworthy signing devices, careful on-device verification, solid backups, and realistic threat modeling about physical access, supply-chain compromise, and human error. The memorable version is this: a cold wallet does not make keys invincible; it makes key exposure much harder by refusing to keep the secret where the network can easily reach it.
How do you secure your crypto setup before trading?
Secure your setup by verifying devices, backups, and transfer details before you fund or trade. Use Cube Exchange’s non-custodial MPC account to hold and execute trades while you keep signing control with your cold wallet. Follow the checklist below to test devices, confirm recovery, fund Cube safely, and verify every destination before you sign.
- Verify your cold signer and firmware: check vendor attestation or firmware hash and sign a small test transaction to confirm the device behaves correctly.
- Create and test recovery backups: record your BIP‑39 mnemonic (and optional passphrase) offline or split it with SLIP‑39 shares, then restore to a spare device to confirm the backup works.
- Fund your Cube Exchange non‑custodial account with a small test deposit on the exact chain and token you plan to trade, and confirm the on‑chain credit before moving more funds.
- Always verify destination details on your cold signer when authorizing transfers: confirm the full receiving address, amount, and fee on the device before signing.
- When trading on Cube, pick an order type that fits your need (limit for price control, market for immediate execution), review estimated fees and slippage, then submit.
Frequently Asked Questions
Deterministic seeds (BIP-39) and HD derivation (BIP-32) let you back up one mnemonic and later regenerate an entire tree of addresses and keys, which makes cold wallets operationally practical because you avoid backing up each address separately.
Cold wallets reduce remote key‑exposure risk but do not stop physical theft, coercion, insider collusion, supply‑chain or firmware tampering, careless seed handling, or social‑engineering tricks that get you to sign the wrong transaction.
If a hardware wallet's firmware, microcontroller, or supply chain is compromised it can manipulate seed generation, user-facing displays, or attestation paths and thereby undermine the device’s trust assumptions, so firmware authenticity and device verification are critical parts of cold‑wallet security.
An air gap means the signer is never directly connected to a network, which can improve isolation, but it is not a guarantee: security still depends on a trustworthy device, correct verification of what is being signed, and proper backup handling.
Sharing an extended public key (xpub) lets an online watch‑only wallet derive addresses and monitor balances without spending power, but xpubs are more sensitive than single public keys because knowledge of an xpub combined with a non‑hardened child private key can reveal the parent private key.
Chain specifics change the signing constraints: on Solana a transaction needs a recent blockhash (so naive offline signing can fail as blockhashes expire), and on Cosmos SDK chains signers must produce signatures over the chain’s canonical serialized bytes and correct sign mode such as SIGN_MODE_DIRECT.
Seed phrases are the canonical recovery mechanism for cold wallets; adding a BIP‑39 passphrase increases security and plausible deniability but also becomes part of the recovery secret, while SLIP-39 Shamir shares let you split recovery into threshold shares at the expense of greater operational complexity.
Related reading