What is a Custodial Wallet?
Learn what a custodial wallet is, how it works, why exchanges use it, and the key tradeoffs around control, recovery, and counterparty risk.
Introduction
Custodial wallet means a wallet arrangement in which a third party holds the private keys that control your crypto-assets. That sounds like a small implementation detail, but it changes the basic shape of ownership, risk, and responsibility. In crypto, control is not mainly a matter of your name being on an account. It is mainly a matter of who can produce the cryptographic signature that moves assets onchain. A custodial wallet exists because many people and institutions do not want to manage that burden themselves, yet the moment they hand it off, they replace key-loss risk with counterparty risk.
That trade is the heart of the topic. If you keep your own keys, you can usually transact without asking permission, but losing those keys can mean permanent loss of access. If a custodian keeps the keys, the experience becomes more familiar: passwords can often be reset, accounts can be recovered, and buying or selling can be integrated into the same platform. But now your practical access depends on the custodian’s security, operations, policies, and financial condition. A custodial wallet is therefore not just a wallet feature. It is a trust model.
How does custody hinge on private keys and who can sign transactions?
A wallet in the digital asset sense is a software application, hardware device, or service that stores a user’s public and private cryptographic keys and lets the user interact with blockchains. The important part here is the private key. A private key is the secret needed to authorize movement of assets associated with a blockchain address. In ordinary language, it is the thing that proves control.
That is why the cleanest way to understand custodial wallets is this: custody means someone else holds the secret that can move the assets. The provider may show you balances, transaction history, deposit addresses, and a friendly app interface, but those interface elements are not the fundamental fact. The fundamental fact is who signs.
This is also where many newcomers get confused. They hear “my crypto is in my exchange wallet” and imagine something like a bank account where ownership and control are naturally bundled together. On a blockchain, those can come apart. If the custodian holds the private keys, the blockchain recognizes the key-holder’s signature, not your customer relationship. Your rights against the custodian may still be real, but they are mediated by contracts, internal ledgers, and operational processes rather than by your direct ability to sign an onchain transaction.
That is the basic contrast with a non-custodial wallet. In a non-custodial wallet, the user is responsible for the private key. If the key or recovery phrase is lost, forgotten, or destroyed, there is typically no built-in institution that can restore access. In a custodial wallet, the provider usually takes on that key-management role and gives the user an account-based experience instead.
Why do platforms and exchanges offer custodial wallets?
Custodial wallets exist because secure key management is hard, and many of the things people want from financial services become easier when a professional operator stands between the user and the blockchain.
The first problem is human error. Self-custody asks the user to generate, store, back up, and protect secrets that cannot safely be guessed, shared, or casually recovered. That is a sharp departure from most internet products. Forgetting a password to email is annoying; forgetting the only secret controlling a blockchain address can be irreversible. For many users, especially beginners, the hardest part of crypto is not understanding the asset. It is safely handling the keys.
The second problem is operational convenience. Centralized trading platforms commonly provide custodial, or hosted, wallets because trading works better when deposits, withdrawals, and internal transfers can be coordinated inside one service. If a user wants to buy crypto with fiat, sell it quickly, move between assets, or transfer to another customer on the same platform, a custodian can make those actions feel immediate and familiar. The blockchain may still matter at the edges, but a large portion of the user experience is handled offchain inside the provider’s own system.
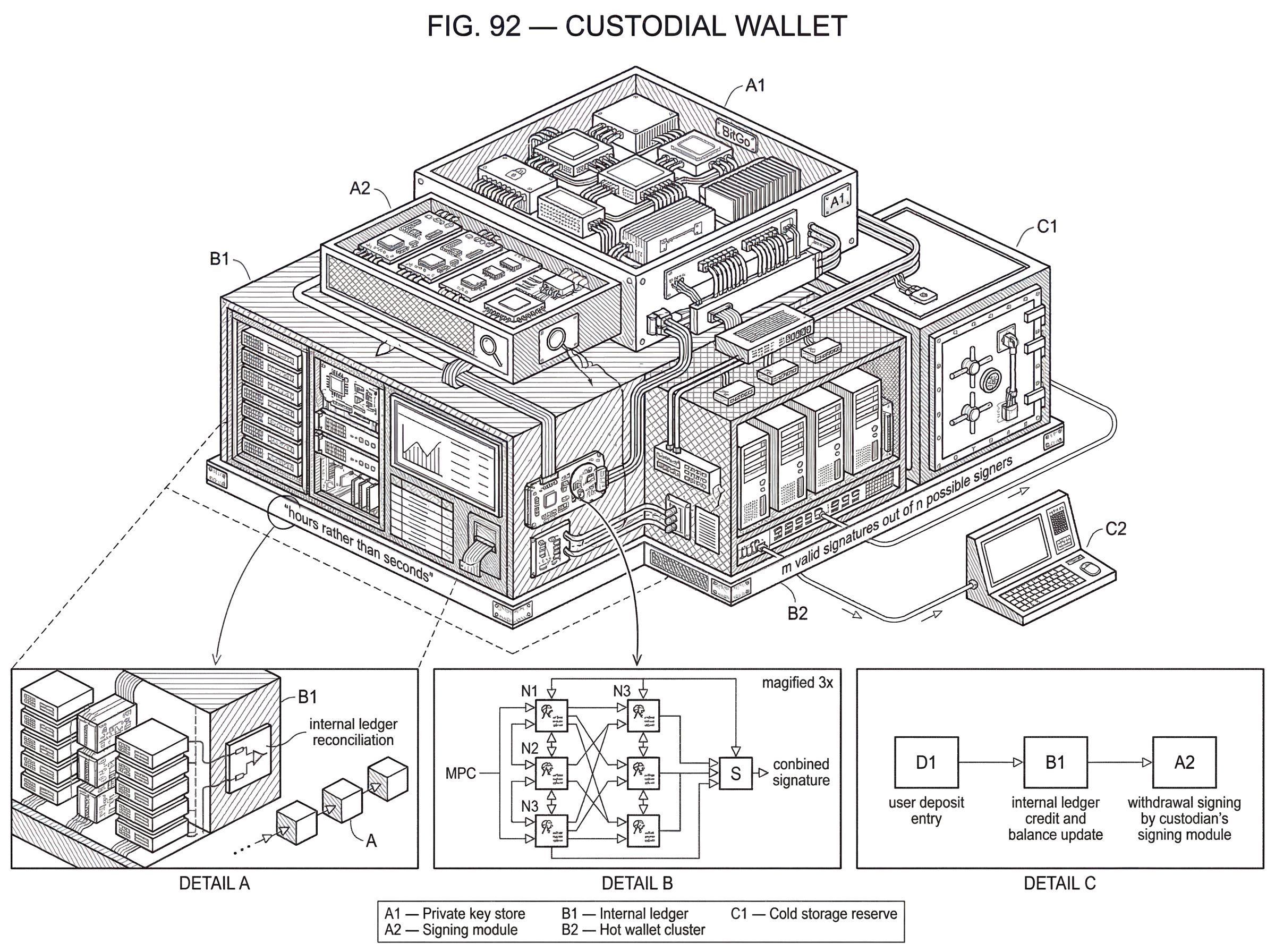
The third problem is institutional control. Businesses, funds, broker-dealers, and other organizations often cannot rely on one individual writing down a seed phrase and putting it in a drawer. They need approval workflows, audit trails, separation of duties, recovery plans, and sometimes regulated custody partners. A custodial wallet, especially one built around cold storage, multisignature, or MPC-based controls, can support those operational requirements more naturally than pure individual self-custody.
So custodial wallets do not exist because crypto “needs middlemen” in some abstract sense. They exist because key management, recovery, compliance, governance, and transaction operations are real tasks, and outsourcing those tasks is often attractive.
How does a custodial wallet operate day-to-day (internal ledgers, pooled balances)?
Mechanically, a custodial wallet usually combines two different systems that the user experiences as one. One system is the blockchain itself, where assets ultimately live and where valid signatures move them. The other is the custodian’s internal ledger, which records what each customer is entitled to.
Imagine a user opens an account on a centralized exchange and buys bitcoin. The app shows that the user now owns some amount of BTC. But the blockchain does not necessarily contain a neat one-wallet-per-customer picture. Instead, the exchange may control a set of addresses and wallets, often with pooled balances and internal accounting. The exchange’s database tracks that this particular customer has a claim to x BTC, while the exchange’s key-management system controls the onchain funds needed to honor customer withdrawals in aggregate.
When that user sends BTC to another customer on the same platform, the transfer may not touch the blockchain at all. The custodian can simply decrement one internal account and increment another. That is faster and cheaper because no onchain transaction is needed. When the user withdraws BTC to an external wallet, the custodian must eventually create and sign an onchain transaction using keys it controls. The customer requested the movement, but the custodian performed the signing.
This internal-ledger model is one reason custodial wallets can feel easier than self-custody. The provider can batch transactions, manage fees, screen requests, freeze suspicious activity, restore account access, and present a simple account view. But this same structure means the user is depending on the provider’s records being accurate and on the provider actually possessing the assets and operational ability to satisfy claims.
That dependence becomes even clearer in omnibus or pooled custody designs. Some custody products hold customer assets in a commingled pool and use offchain ledgers to assign beneficial balances. That can improve liquidity and operational speed, but it also means that the customer’s visible balance is not the same thing as direct, segregated control over a specific onchain UTXO or account balance.
How do custodial wallets simplify the user experience by taking on key-management?
| Type | Connectivity | Speed | Main risk | Best for |
|---|---|---|---|---|
| Hot wallet | Internet connected | Fast, immediate | Higher online theft risk | Daily transfers, trading |
| Cold wallet | Offline storage | Slower withdrawals | Physical loss or operational risk | Long-term reserves |
| Hybrid | Hot + cold mix | Balanced availability | Compromise of hot pool | Exchanges and custodians |
A useful way to think about custodial wallets is that they hide cryptographic complexity by moving it into an organization. The user no longer needs to protect the only signing secret. The custodian now has to solve that problem at scale.
This is not a trivial shift. Once a provider holds keys for many users, it becomes a concentrated target. The provider must defend against external attackers, insider abuse, operational mistakes, bad recovery procedures, poor accounting, and liquidity stress. The wallet becomes less of a personal tool and more of a security-critical infrastructure system.
That is why custody operations often split assets across hot and cold environments. hot wallets are connected to the internet and are easier to use for routine transfers, but that accessibility makes them more vulnerable to theft and fraud. Cold wallets keep key material offline, reducing exposure to online compromise, but they are operationally slower and can be vulnerable to physical loss, theft, or damage if not handled well. In practice, custodians often keep some funds accessible for day-to-day withdrawals while storing a larger reserve in colder systems with stricter controls.
The design goal is simple even if the implementation is not: keep enough liquidity available to serve users, while making it hard for any single compromise to expose the full pool of assets.
How do institutional custodians manage signing authority (multisig, MPC)?
| Model | Single-point failure? | Key exposure | Signing workflow | Best for |
|---|---|---|---|---|
| Single-key | Yes | Full private key stored | Single signer signs | Small services, simple ops |
| Multisig | Reduced | Multiple independent keys | m-of-n signatures onchain | Protocol- and multisig-friendly chains |
| MPC | Reduced | Key never assembled whole | Distributed threshold signing | Institutional custody at scale |
At a high level, secure custody is a key-management problem. General cryptographic guidance, such as NIST’s key-management recommendations, emphasizes the lifecycle of keying material: generation, storage, access control, backup, recovery, audit, and response to compromise. Custodial wallets apply those same concerns in a digital-asset setting.
In a simple custodial model, one organization may generate and protect the private keys, often using hardened systems or hardware security modules. More advanced models distribute authority so that no one operator or device can unilaterally move funds.
Two common ways to do that are multisignature and MPC, short for multi-party computation. The intuition is similar in both cases: instead of one secret in one place, signing authority is split across multiple parties or components. That reduces single-point-of-failure risk.
In a multisignature setup, a transaction may require m valid signatures out of n possible signers. On some chains this is enforced directly by the protocol or by a smart contract. In an MPC setup, the private key is not fully assembled in one place; instead, multiple parties each hold shares and cooperate to produce a signature. Institutional custody providers increasingly use MPC because it can support distributed signing workflows while keeping the complete key from ever appearing in one environment.
A concrete example helps. Some custody providers let a client initiate a withdrawal but require operators inside the custodian to verify the request and participate in signing from separate secured environments. In BitGo’s custody model, for example, custody wallets are cold wallets, users can initiate transactions, but they do not sign them directly. Signing involves operator-mediated checks and separated key roles, and withdrawals may take hours rather than seconds. The mechanism is not merely bureaucratic friction. It is there because each additional independent check makes a fast, total compromise less likely.
This is where the bank analogy partly helps and partly fails. It helps because a custodian is offering safekeeping, operational support, and recovery processes. It fails because the underlying asset is controlled by cryptographic signing, not by a central account master record alone. The custodian is not just updating a database entry; it is managing the means to create valid blockchain transactions.
Custodial vs. self-custody: which risks change and why?
Most discussion of wallets becomes clearer once you see that the central tradeoff is between user error risk and counterparty risk.
With self-custody, the catastrophic failure mode is usually personal mistake: a lost seed phrase, malware on a device, a phishing attack that tricks the user into approving a bad transaction, or poor backup practices. No third party can freeze the funds, but no third party can reliably rescue the user either.
With custodial wallets, many of those user-facing failures are softened. Password resets, identity checks, fraud monitoring, customer support, and transaction review can all reduce the chance that one personal mistake causes irreversible loss. But the catastrophic failure mode moves outward. Now the danger is the custodian itself: hacked systems, compromised operators, inaccurate accounting, misuse of customer assets, insolvency, or freezes imposed by policy or law.
This is why saying “custodial is safer” or “self-custody is safer” without context is not very meaningful. Safer for whom, against which failure, under what assumptions? A beginner who cannot securely manage backup secrets may in practice be safer with a reputable custodian than with a handwritten seed phrase stored badly. A sophisticated user who needs censorship resistance and direct onchain access may rationally prefer self-custody despite the added responsibility. The architecture changes the type of risk more than it eliminates risk.
What are the major failure modes for custodial wallets (key compromise, misuse, insolvency)?
The failure cases are illuminating because they reveal what custody really means when conditions are bad.
One class of failure is key compromise. If an attacker gains enough signing authority inside a custodial system, they may be able to move assets directly. The Ronin bridge breach is a stark illustration of what concentrated validator-key control can mean in practice: attackers obtained enough validator keys to authorize fraudulent withdrawals, and weak monitoring delayed detection. The lesson is not that all custodial systems are the same as bridge validators. It is that distributed signing only works if the surrounding controls are strong too: access management, revocation of old privileges, monitoring of large outflows, and human review of exceptional transactions.
Another class of failure is asset misuse and poor accounting. A custodian may appear solvent and functional while actually deploying customer assets in ways users do not understand. The Celsius examiner’s report is important here because it shows how commingling, weak reconciliation, inadequate risk management, and use of customer deposits in broader corporate activity can make a custodial promise much less solid than the interface suggests. If the platform says you have a balance, but it cannot reliably track assets and liabilities coin by coin, the wallet experience is masking accounting fragility.
A third class of failure is legal ambiguity in insolvency. Treasury has pointed out that in hosted-wallet arrangements there can be unresolved questions about which party (owner, custodian, or sub-custodian) has ownership or control over the assets, and that these questions matter greatly in bankruptcy or receivership. This is one of the hardest points for users because it cuts against the intuitive meaning of “my wallet.” If a custodian fails, the user may discover that the practical and legal status of the assets depends on terms of service, custody structure, asset segregation practices, and the role of any downstream custodian.
Does calling a service a 'custodian' give you bank-style legal protections?
Many users hear “custodian” and import assumptions from banking or brokerage. That is understandable, but it can be misleading.
Treasury has emphasized that many crypto custodial arrangements do not necessarily provide the same customer protections that apply to traditional financial intermediaries, such as segregation rules, investment restrictions, or insurance. In other words, the word custody describes who holds the keys and manages access; it does not by itself guarantee a familiar legal or prudential regime.
That distinction matters because the user experience of a custodial wallet is deliberately familiar. You log in with an email address, recover access through support channels, and view balances in an app. Psychologically, this feels like online banking. Mechanically, it is a mixture of blockchain control, internal bookkeeping, and contractual rights. The closer the interface feels to traditional finance, the easier it is for users to overestimate the protections sitting underneath it.
This does not mean all custodians are unreliable or that regulated custody is meaningless. It means the important question is more specific: what controls, disclosures, segregation practices, reserves, audits, and legal arrangements does this custodian actually have?
Can proofs-of-reserve and audits remove the need to trust a custodian?
| Tool | What it shows | What it doesn't show | Best use |
|---|---|---|---|
| Proof-of-reserve | Onchain asset snapshot | Offchain liabilities and governance | Quick solvency signal |
| External audit | Historical accounting checks | Real-time balances or hidden liabilities | Regulatory confidence |
| Security certification | Module-level cryptographic assurance | Operational accounting or treasury practices | Technical assurance |
Because custody introduces opacity, the ecosystem has tried to build tools that reduce blind trust. Proof-of-reserve approaches are one example. The idea is to provide cryptographic or attestational evidence that a custodian’s assets match, or at least support, its liabilities to users.
This is a useful step because it addresses a genuine structural problem: users of custodial wallets often cannot independently verify that a provider is fully backed. If a reserve-verification system is well designed, it can make hidden shortfalls harder to conceal. But it does not solve everything. A reserve snapshot does not automatically prove clean governance, proper segregation, absence of undisclosed liabilities, or safety of key-management operations. Transparency can narrow the trust gap; it does not erase the need for trust.
The same principle applies to security certifications or validated cryptographic modules. A custodian may use strong hardware and validated cryptographic components, which is valuable. But module validation does not tell you whether the provider has sound accounting, prudent treasury management, reliable recovery procedures, or good internal governance. In custody, technical assurance and organizational assurance must work together.
When should I use a custodial wallet instead of self-custody?
A custodial wallet makes the most sense when the main problem you are solving is safe delegation rather than direct sovereign control.
That is often true for beginners entering crypto through an exchange, for active traders who need rapid access to markets and fiat rails, and for institutions that need formal approvals and operational oversight. In all of those cases, the user values recovery, support, integrated trading, and managed operations more than maximal independence from intermediaries.
But the fit changes once the goal becomes active participation in the onchain economy. If you want to interact directly with decentralized applications, sign transactions locally, hold assets without platform dependency, or minimize censorship and counterparty exposure, a custodial wallet becomes limiting. Some advanced users therefore adopt a hybrid strategy: keep trading balances or operational funds with a custodian while holding longer-term or sovereignty-sensitive assets in self-custody.
That hybrid pattern is not indecision. It is recognition that different trust models are good at different things.
Key takeaway: how custody changes ownership, control, and risk
A custodial wallet is not defined by its app design or by whether it looks modern or simple. It is defined by who controls the private keys. Once a third party controls those keys, your risk profile changes: key management becomes easier for you, but trust, security, accounting, and solvency become central.
So the simplest durable way to think about custodial wallets is this: they turn crypto from a pure key-possession problem into a relationship problem. That relationship can be useful, efficient, and sometimes necessary. But it is never free. You gain recovery and convenience by accepting dependence on the custodian’s systems and promises. Understanding that trade is what makes the concept click.
How do you secure your crypto setup before trading?
Secure your crypto setup before trading by verifying account protections, destination hygiene, and execution choices. On Cube Exchange, fund your account, confirm the chain and destination for transfers, and pick order types that match your exposure so you avoid costly mistakes during execution.
- Fund your Cube account with fiat on-ramp or a supported crypto transfer.
- Turn on two-factor authentication (2FA) and confirm your recovery contact methods.
- Verify the destination chain and address before any withdrawal: copy the address from your hardware or self-custodial wallet, confirm the chain/network, then send a small test transfer and wait for the chain-specific finality threshold (e.g., X confirmations) before sending the full amount.
- Open the relevant market on Cube and choose an order type that fits the situation: use a limit order to avoid slippage in thin markets or a market order for immediate fills; review estimated fees and the expected fill before submitting.
- Move long-term holdings to self-custody (hardware wallet or an MPC-based custody you control) and store recovery material offline in multiple secure locations.
Frequently Asked Questions
When a custodian holds the private keys, the blockchain recognizes whoever can produce the signature - not your customer relationship - so you typically have a contractual claim against the custodian rather than direct onchain control; the legal status of those claims in insolvency can be unresolved and depends on custody structure and terms of service.
Yes - custodial providers commonly offer account-style recovery (password resets, identity checks, customer support) that can restore access for users who lose their personal secrets, at the cost of relying on the provider’s policies and processes rather than a self-managed recovery phrase.
It depends: custodial wallets reduce the risk of individual user mistakes (lost seed phrases, device malware) but introduce counterparty risks such as hacks, insider abuse, accounting failures, freezes, or insolvency; which is “safer” depends on which failure modes matter most to you.
Custodians reduce single-point-of-failure risk by distributing signing authority using multisignature schemes (m-of-n signatures) or MPC so no single device or operator can unilaterally move funds, though these approaches require strong surrounding controls and operational processes to be effective.
If a custodian is hacked, misuses assets, or becomes insolvent, customers may face direct loss, delayed detection, or legal uncertainty - real-world examples (Ronin bridge, Celsius examiner findings) show compromises, commingling, and accounting weaknesses can turn hosted balances into fragile claims.
Proof-of-reserve-type transparency tools can help verify that a provider’s visible liabilities are backed by onchain assets at a point in time, but such proofs do not by themselves demonstrate correct accounting, segregation of assets, absence of undisclosed liabilities, or sound key-management and governance.
Custodial wallets are most appropriate when you value delegated operational safety, integrated trading, fiat rails, or institutional workflows (approval controls, audits); they are less appropriate if your priorities are direct onchain sovereignty, censorship resistance, or holding assets without platform dependence.
No - calling a service a “custodian” doesn’t automatically confer bank-like legal or prudential protections; custodial crypto arrangements may lack traditional segregation rules, insurance, or regulatory safeguards unless the provider specifically implements and discloses them.
Related reading