What is Self-Custody?
Learn what self-custody means in crypto, how wallets and keys work, why seed phrases matter, and the security tradeoffs of holding assets yourself.
Introduction
Self-custody means you, rather than an exchange, bank-like service, or other intermediary, control the cryptographic keys that authorize the movement of your assets and the use of your onchain account. That is the attraction: if control comes from possession of a key, then holding the key yourself can remove a large class of counterparty risk. But it also creates a different problem. The system no longer asks, "Do you have an account with a trusted institution?" It asks, "Can you produce the valid authorization right now?" If the answer is no because a device is lost, a seed phrase is forgotten, or a signing workflow is tricked, there is usually no administrator who can restore access.
That tension is the point of self-custody. It replaces institutional recovery and discretionary control with cryptographic control and user responsibility. wallet software makes this feel approachable, but the underlying rule is unforgiving: whoever can correctly sign for the account has control, and whoever cannot does not. Once that rule is clear, the rest of self-custody (seed phrases, hardware wallets, multisig, smart wallets, backups, phishing resistance) starts to make sense.
How does signing authority replace account records on blockchains?
In ordinary online finance, your balance is tied to a legal and operational relationship with an institution. You log in with a username, password, maybe two-factor authentication, and the institution updates its own database according to its policies. If you forget your password, customer support can reset it because the institution is the ultimate source of truth.
A blockchain works differently. The ledger is public and shared, and it accepts state changes only when they are authorized according to the protocol's rules. In the simplest case, that authorization is a valid digital signature under a private key. A public key can be shared; from it, a wallet or protocol derives an address others can send funds to. The corresponding private key must remain secret because it is what signs transactions and proves control.
That is why Ethereum's wallet documentation describes wallets as applications that give you control over your account and let you sign in to applications, read balances, send transactions, and verify identity. The wallet is not usually the thing that holds funds in the way a bank account does. It is the tool that manages the credentials needed to interact with assets recorded onchain. Ethereum's docs make this distinction directly: wallet providers do not have custody of your funds; they provide a window into your assets and tools to manage them.
The same logic applies well beyond Ethereum. Bitcoin's security guidance is built around the same premise: control of money depends on good handling of wallet secrets, backups, and signing devices. The chain differs, the transaction format differs, the address format differs, but the core structure is the same. Self-custody is not fundamentally about a particular app or device. It is about direct control over the authorization mechanism.
What does a non‑custodial wallet do to manage keys and transactions?
The word wallet is slightly misleading because it suggests a container. In practice, a wallet is better understood as a key manager plus a transaction/signing interface. It does three jobs.
First, it generates or imports key material. Second, it derives addresses and monitors the chain for balances and activity relevant to those addresses. Third, it prepares transactions and signs them when the user approves. If the wallet is non-custodial, the critical signing secret is controlled by the user, either directly in software, in hardware, or through a more complex arrangement like multisig or a smart-contract wallet.
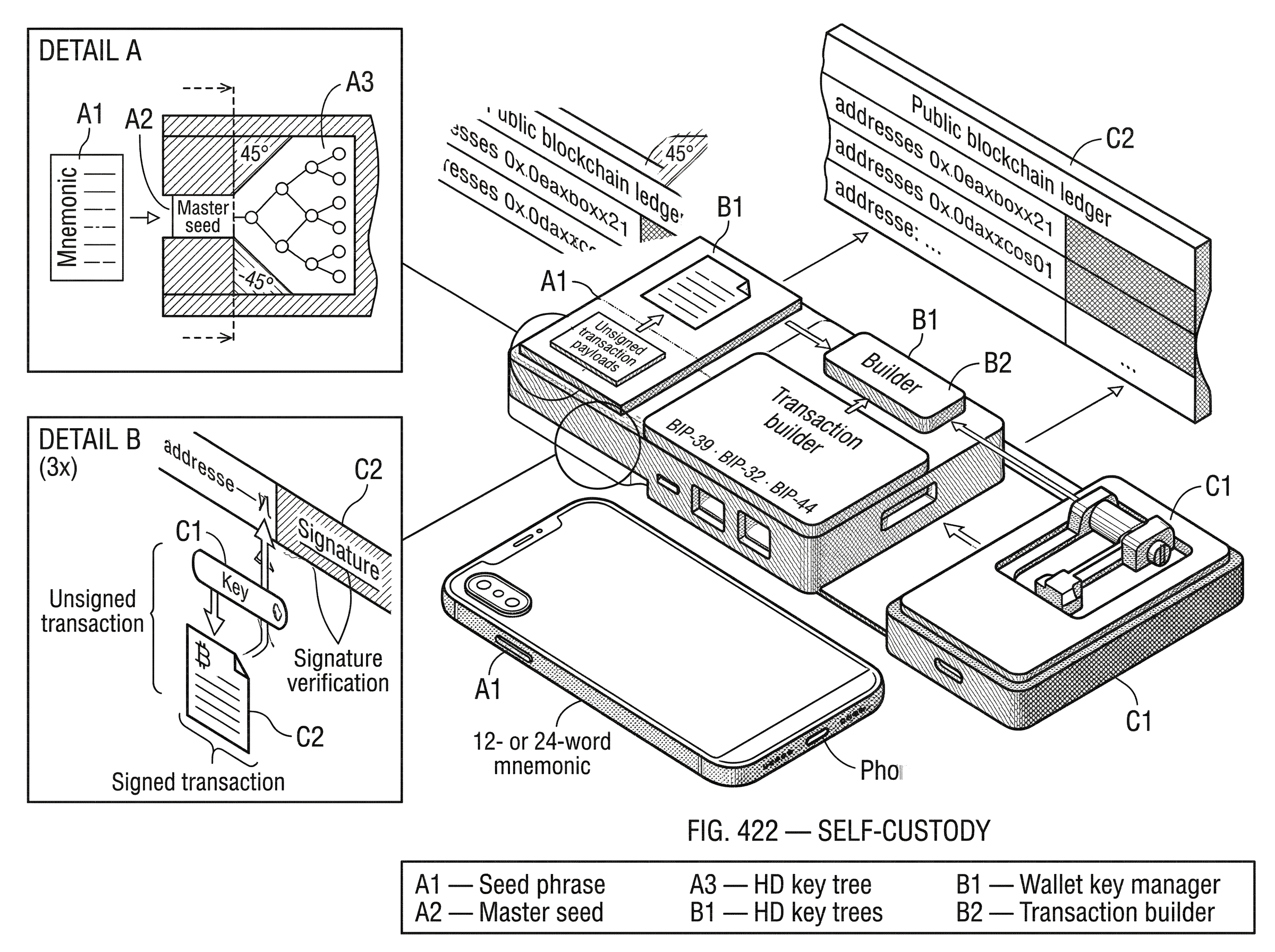
This is why two different wallet apps can often show the same funds when you import the same seed phrase. The assets were never inside the app. The app was reconstructing control over the same key hierarchy and looking up the same onchain state. Standards such as BIP-39, BIP-32, and BIP-44 became important because they made this reconstruction portable: a human-manageable recovery phrase can regenerate a deterministic tree of keys, and wallets can organize that tree in interoperable ways.
That portability is one of self-custody's strongest features and one of its sharpest edges. If a wallet company disappears, your assets are still recoverable in another compatible wallet if you still control the recovery material. But if that recovery material is exposed, the attacker gets the same portability.
Why do wallets use seed phrases (BIP‑39) and how do they work?
The raw problem is simple: private keys are long, random secrets that humans cannot memorize or safely retype. Early wallet designs often required many independent backups because they generated keys separately. That made backup fragile. Hierarchical deterministic wallets changed the model by deriving many keys from a single root secret.
BIP-39 defines the common mnemonic format: a list of easy-to-handle words, often 12 or 24, that encodes underlying entropy and a checksum. That mnemonic is then converted into a binary seed, and that seed can drive deterministic wallet generation. BIP-32 defines how a tree of keys can be derived from one root using extended keys and chain codes. BIP-44 adds a common path structure so wallets can separate coins, accounts, change addresses, and receive addresses in a predictable way.
The practical consequence is that a single backup can often restore a large wallet structure. That is why wallet software tells users to write down a seed phrase and keep it safe. Ethereum's wallet guidance states plainly that the seed phrase is often the only way to recover the wallet. Bitcoin.org similarly emphasizes that backups are essential and that partial backups can fail if the wallet uses hidden internal keys.
A helpful way to think about the seed phrase is as a master backup for future signing authority. It is not the coins themselves. It is the compact secret from which the wallet can regenerate the keys that control those coins.
That analogy explains the convenience, but it has a limit. A house key opens one lock; a seed phrase can regenerate an entire family of keys and accounts, sometimes across assets and applications. So the consequences of disclosure are much larger. If someone obtains the phrase (and any necessary extra passphrase, if used) they do not need your original device.
How does self‑custody work in practice? A step‑by‑step example
Imagine someone installs a wallet app for the first time. The app generates fresh randomness on the device and turns it into a 12- or 24-word mnemonic. The app asks the user to write those words down because the words are the recoverable representation of the wallet's root secret. From that root, the wallet deterministically derives account keys and addresses.
Now a friend sends funds to one of those addresses. Nothing is delivered into the phone in the ordinary sense. The blockchain records that assets are now spendable according to the rules tied to that address. When the user later opens the wallet, the app scans relevant addresses derived from the wallet's key tree and shows the balance.
Suppose the user wants to pay someone. The wallet constructs a transaction that says, in effect, move these assets under these conditions to this destination. The critical step is signing. The wallet uses the relevant private key to produce a cryptographic authorization. Nodes can verify the signature against the public key or address relationship required by that chain's rules. If valid, the network accepts the transaction into its normal processing flow.
If the phone is destroyed the next day, the assets are not gone merely because the device is gone. The user can install another compatible wallet, enter the mnemonic, regenerate the same key hierarchy, and recover control. But if the written seed phrase was also lost and no other recovery arrangement exists, access may be permanently lost. That is the essential self-custody bargain in one story.
Why choose self‑custody instead of a custodial wallet or exchange?
The obvious alternative is to let a third party manage keys for you. Sometimes that is reasonable. Custodial wallets and exchanges reduce operational burden, offer familiar account recovery, and hide complexity. But they also create concentrated trust. The custodian can become insolvent, be hacked, freeze accounts, mismanage reserves, or simply refuse service.
Self-custody exists because blockchains make a different ownership model possible. If the protocol itself can verify authorization, then an individual or organization does not need a custodian to intermediate every transfer. This is a structural change, not just a new user interface. It means someone can hold assets directly, interact with applications directly, and verify state directly.
That directness matters for people who want censorship resistance, global accessibility, or independence from platform-specific account systems. It also matters for organizations that want stricter internal control over treasury movement than a general-purpose exchange account may provide. But the benefit only exists if the user can manage the new responsibilities better than the third party would have. Self-custody removes one trust assumption by increasing the importance of operational security.
Why is key management more important than cryptography for wallet security?
NIST's key-management guidance states the core principle bluntly: strong cryptography is useless if an adversary learns the key. That matters because newcomers often imagine self-custody as a software choice; which wallet should I use? ; when the deeper issue is lifecycle management of secrets. How are keys generated? Where do they live? How are they backed up? When are they used? What happens on device loss, compromise, or inheritance?
This is also why "not your keys, not your coins" is only half the truth. The other half is "if your key management fails, your control fails." A self-custodied setup is secure not because it is labeled non-custodial, but because the full system around the keys is sound.
Bitcoin.org's guidance reflects this operational view. It recommends backups, encryption, caution with online services, and cold storage for savings. It warns that password recovery options are limited and that online backups are highly vulnerable to theft. These are not secondary details. They are the mechanism by which self-custody succeeds or fails in practice.
Hot vs hardware vs cold storage: what are the security and convenience trade‑offs?
| Wallet type | Connectivity | Typical use | Remote-attack risk | Ease of use | Best for |
|---|---|---|---|---|---|
| Hot wallet | Always online | Day-to-day spending | High | Very easy | Small frequent payments |
| Hardware wallet | Occasional online | Everyday & savings | Moderate | Moderate | Everyday holdings & savings |
| Cold storage | Never online | Long-term savings | Very low | Cumbersome | Long-term holdings |
The main tradeoff in self-custody is between convenience and attack surface. A wallet connected to the internet and used frequently is easy to operate but exposed to more kinds of compromise. A wallet whose signing keys stay offline is harder to use but safer against remote attack.
A software wallet on a phone or laptop is often called a hot wallet. It is useful for day-to-day activity because it can readily connect to apps, submit transactions, and display balances. But if the device is compromised by malware or the user is phished into approving the wrong action, the fact that the wallet is self-custodial does not help much.
A hardware wallet improves this by moving key operations into a dedicated device designed to resist general-purpose software attacks. Bitcoin.org describes hardware wallets as a strong balance between high security and ease of use because they are purpose-built and can support backups. The important idea is not magic tamper-proofing; it is reduction of exposed surface. The private key does not need to sit inside the web browser or general desktop environment that is parsing websites and plugins all day.
Cold storage goes further. In Bitcoin's terminology, an offline wallet stored in a secured place and not connected to the network offers the highest security for long-term savings. Here the mechanism is straightforward: attacks delivered over a network have much less opportunity when the signing environment is never online. The tradeoff is slower, more cumbersome spending and more operational burden when funds do need to move.
How can hardware wallets still fail? Common attack vectors and user risks
A common misunderstanding is that if the private key never leaves a hardware wallet, the user is safe. That is too simple. The hardware device may protect the key, but the transaction still has to be understood by the human approving it.
The EthClipper research illustrates one class of failure. The attack does not steal the private key directly. Instead, it tampers with a copied destination address so the user is tricked into approving a payment to an attacker-controlled address that looks similar. Because many users verify only a few characters of a long address, address-substitution can evade casual checking even when a hardware wallet displays the destination.
A more dramatic example comes from multisig workflows around smart-contract wallets. In the 2025 Bybit theft analyzed by NCC Group, attackers allegedly compromised the off-chain web interface used in a signing flow and altered what signers approved. The keys themselves and the fact of multiple signatures did not automatically prevent the loss. The weakness was in the human and software layer that framed the transaction for approval. Self-custody protects against some failures of trusted intermediaries, but it does not remove the need to trust your own tooling, user interface, and operational process.
How does multisig reduce single‑point failure and what are the downsides?
| Scheme | Setup | Single-point risk | Recovery resilience | Operational friction | Best for |
|---|---|---|---|---|---|
| Single-key | Simple | High | Low | Low | Beginners & small amounts |
| 2-of-3 multisig | Moderate | Reduced | Good (one key lost) | Moderate | Individuals & small teams |
| 3-of-5 multisig | Complex | Low | High (tolerates multiple loss) | High | Organizations & treasuries |
The most basic self-custody setup has one secret controlling everything. That is elegant, but brittle. Lose it and you may lose access. Leak it and an attacker may gain full control. Multisig exists to change that failure mode.
In Bitcoin, multisignature lets spending require multiple independent approvals. Bitcoin.org highlights this as a way to prevent theft from a single compromised device or server. The crucial idea is that control is distributed across several keys. A 2-of-3 or 3-of-5 arrangement means no single signer can move funds alone, and one lost key need not destroy access.
This is useful for both individuals and organizations. An individual might keep keys in separate physical locations so a burglary, house fire, or one-device compromise does not become catastrophic. An organization can require multiple people or departments to approve treasury movements. The security benefit comes from eliminating a single decisive secret.
But multisig is not free security. It increases setup complexity, backup complexity, and transaction workflow complexity. It can also shift risk from key theft toward coordination failure. If a scheme requires three signatures and the organization can only reliably obtain two during an emergency, the design has created a different kind of fragility.
How do smart‑contract wallets and account abstraction change control and recovery?
On some chains, especially Ethereum, self-custody no longer has to mean a single externally owned account controlled by one private key. A smart-contract wallet can define its own authorization logic. That logic might require multiple signers, allow session keys, enforce spending limits, or support recovery rules.
Two standards help explain why this matters. ERC-1271 provides a standard way for a contract to say whether a signature is valid on its behalf. That lets applications recognize contract-based accounts, not just externally owned accounts. ERC-4337 goes further by enabling smart contract accounts to function as primary accounts through a higher-layer architecture involving UserOperations, bundlers, and an EntryPoint contract, without changing Ethereum's consensus layer.
Mechanically, this means self-custody can become more programmable. The user may still control the account, but control is expressed through policy rather than a lone secret. A wallet could require two devices plus a recovery guardian, or allow a sponsored transaction where a paymaster covers fees, or let a user log in through a more user-friendly flow while preserving non-custodial control under the hood.
This is promising because it can soften the harshest edges of classic seed-phrase self-custody. But it also changes the trust surface. The account's safety may depend on contract correctness, audited infrastructure, transaction simulation, and the integrity of off-chain services. ERC-4337 itself notes that the EntryPoint contract becomes a central trust point that needs strong auditing and verification.
So the fundamental question remains the same even as the machinery evolves: who can authorize actions, under what rules, and what must fail for control to be lost?
What recovery options exist for self‑custody and what risks do they introduce?
| Method | Recoverability | Security if leaked | User burden | Trust required |
|---|---|---|---|---|
| Seed phrase | Single-point recovery | Very poor if leaked | Low to moderate | No third-party |
| Seed + passphrase | Single recovery with extra secret | Better if passphrase strong | Higher (must remember passphrase) | No third-party |
| Social recovery | Recoverable via guardians | Depends on guardians' security | Moderate (coordination) | Trusted contacts or services |
| Smart-contract recovery | Policy-based recovery | Depends on contract code | Higher (setup & audits) | Audited contracts & infrastructure |
Traditional self-custody is severe about recovery. Ethereum's wallet docs warn that if you lose your keys or seed phrase, there is typically no customer support and recovery may be impossible. That is not an implementation accident. It follows from the design goal of removing intermediaries with override power.
This creates a deep tension. Strong self-custody wants no one else to be able to reset your credentials. Human life, however, includes forgetfulness, hardware failure, death, travel, theft, and emergencies. So every real self-custody system needs some answer to recovery, even if that answer is "the user accepts irrecoverability."
Seed-phrase backup is the simplest answer, but it creates a single, highly sensitive recovery artifact. An optional BIP-39 passphrase can add another layer, and the specification notes that every passphrase generates a valid seed, which provides plausible deniability. But this also means forgetting the passphrase can be just as fatal as losing the mnemonic.
Newer wallet designs try to improve this with social recovery, device clusters, passkeys, or smart-account policies. Some ecosystems market experiences that reduce or remove visible seed phrases. That may improve usability, but it does not make the recovery problem disappear. It means the recovery mechanism has moved into a different combination of cryptography, hardware enclaves, delegated trust, threshold schemes, or service assumptions. The right question is never "Does this wallet hide the seed phrase?" It is "What is the actual path by which control can be restored, and who must be trusted along the way?"
Self-custody across chains: the idea is stable, the machinery varies
The exact shape of self-custody depends on the chain's account model and wallet architecture. Bitcoin commonly emphasizes UTXOs, deterministic address chains, cold storage, and native multisig. Ethereum often emphasizes account-based balances, smart-contract wallets, typed signing, and account abstraction. Solana pushes further toward programmable wallet behavior and fee sponsorship, with wallet experiences that can feel more like app accounts while still aiming to preserve user control.
These differences matter for implementation, but they do not change the core concept. In every case, self-custody concerns direct control over whatever the chain accepts as valid authorization. Sometimes that is a signature from a single private key. Sometimes it is a threshold of keys. Sometimes it is smart-contract logic that validates signatures and enforces policy. The details vary because chains expose different primitives. The underlying question does not.
When and how does self‑custody fail? Common failure modes and mitigation checks
The romantic version of self-custody says: hold your keys and you are sovereign. The more accurate version is: hold your keys well, understand what you are signing, preserve recovery, and avoid compromised tooling; then you reduce dependence on external custodians.
Several assumptions can fail. The device generating or storing keys can be compromised. The backup can be lost or copied. The user can be Socially engineered. The signing interface can misrepresent the transaction. The smart wallet contract can contain a bug. The recovery design can be too weak or too hard to use. Even interoperable standards introduce edge cases: BIP-44's gap-limit discovery can miss addresses beyond expected windows, and BIP-32's non-hardened derivation has subtle security implications if extended public keys and child private keys are mishandled.
None of this means self-custody is broken. It means self-custody is a security system, not a slogan. Its success depends on matching the setup to the holder's threat model, amount at risk, technical ability, need for recovery, and frequency of use.
Conclusion
Self-custody is direct control over the cryptographic authority that a blockchain recognizes. That is why it matters: it can remove reliance on custodians and give users genuine control over assets and onchain identity. But the same mechanism makes responsibility unavoidable. If control comes from keys and signing logic, then backups, device security, transaction understanding, and recovery design are not accessories; they are the system.
The shortest way to remember it is this: self-custody means no one can save you from losing control, and no one can easily take control from you without defeating your key management. Everything else is the engineering tradeoff around that fact.
Frequently Asked Questions
Usually not; most wallet documentation (Ethereum, Bitcoin) warns that the seed phrase is often the only recovery mechanism and if it is lost there is typically no customer support to restore access.
A BIP‑39 mnemonic encodes entropy plus a checksum so one human-readable phrase can deterministically regenerate a tree of keys (BIP‑32/BIP‑44); that makes backups convenient but also means disclosure of the phrase (and any extra passphrase) lets an attacker recreate all derived accounts.
No; hardware wallets reduce the exposed attack surface by keeping private keys in a dedicated device, but they do not stop attacks that misrepresent transactions or addresses to the user - address‑substitution (EthClipper) and compromised signing UIs (Bybit/Safe incident) have led to losses even when keys stayed in hardware.
Multisig distributes control so no single compromised key can move funds (e.g., 2‑of‑3 setups), which reduces single‑point failures, but it increases setup, backup, and coordination complexity and can create availability problems if too many signers are unreachable.
Smart‑contract wallets let the account enforce programmable authorization (multisig rules, session keys, spending limits) and standards like ERC‑1271 and ERC‑4337 enable contract accounts and account abstraction, but they shift part of the trust to contract correctness, off‑chain services, and shared infrastructure like the EntryPoint contract.
No; guides such as Bitcoin.org and NIST emphasize that any backup stored online remains highly vulnerable to theft, so online/cloud backups introduce substantial risk even when encrypted.
Often yes when wallets follow compatible standards (BIP‑39/BIP‑32/BIP‑44), because a mnemonic can regenerate the same key hierarchy, but interoperability caveats exist (different derivation paths, gap‑limit discovery) that can make recovered addresses or balances appear missing in another wallet.
No; self‑custody reduces dependence on custodians but replaces that with dependence on your own tooling, processes, and recovery design - failures in device security, UI rendering, smart‑contract bugs, or weak recovery arrangements can still cause loss despite non‑custodial keys.
Related reading