What is a TWAP Oracle?
Learn what a TWAP oracle is, how it computes time-weighted average prices on-chain, why it resists manipulation, and where its limits matter.
Introduction
TWAP oracle means time-weighted average price oracle: a price feed that reports an asset’s average price over a chosen time window instead of just its latest spot price. That sounds like a small change, but it solves a very specific problem in on-chain finance. A single trade can push the visible price in a decentralized exchange pool far away from the broader market for a moment. If a lending protocol or derivatives system blindly trusts that momentary price, it can make bad decisions instantly.
The core idea behind a TWAP oracle is to make price manipulation expensive by forcing an attacker to sustain the distortion across time, not merely create it for one transaction. In other words, TWAP does not try to make bad prices impossible. It changes the economics so that moving the oracle becomes much costlier than moving the spot price. That distinction matters, because oracle security in DeFi is usually less about perfect truth and more about economic resistance to profitable lies.
This is why TWAP oracles became so important around AMM-based exchanges. AMMs always expose a current reserve-implied price, but that raw price is mechanically sensitive to trades. A protocol that needs collateral values, liquidation thresholds, or settlement prices often wants something slower and harder to jerk around. TWAP is one of the simplest ways to get that from on-chain market state.
Why do protocols use TWAP oracles instead of a single spot price?
A spot price answers the question, “What price does this market imply right now?” A TWAP oracle answers a different question: “What price has this market implied on average over the recent past?” The difference matters because many protocols do not care about the exact last trade; they care about a price that is difficult to manipulate at low cost.
Consider a lending protocol using a DEX pool as its price source for collateral. If the protocol reads the pool price at a single instant, an attacker may be able to borrow capital, trade aggressively to move the pool, trigger the oracle read, and then unwind the trade. In the flash-loan era, that entire sequence can happen inside one transaction or one block. The spot price was real in a narrow mechanical sense, but it was not representative enough for the protocol’s risk decision.
Averaging over time changes the mechanism. Now the attacker cannot merely create a brief spike; they must hold the pool in a distorted state long enough for that bad price to meaningfully influence the average. On an AMM, holding price away from the external market usually means losing money to arbitrageurs and paying trading fees repeatedly. So the oracle becomes safer not because it detects manipulation directly, but because the market structure punishes sustained distortion.
This is the central tradeoff: freshness versus resistance. A shorter TWAP window reacts faster to real market moves, but it is easier to manipulate. A longer window is harder to manipulate, but slower to reflect genuine price changes. There is no setting that perfectly maximizes both.
What does time-weighted average price (TWAP) mean for on-chain oracles?
At first glance, TWAP sounds like “sample the price a few times and average the samples.” That intuition is close, but the important part is the weighting. Time-weighting means a price that persists longer contributes more to the oracle than a price that exists only briefly.
If a market stayed at 100 for 9 minutes and then briefly jumped to 130 for 1 minute, a 10-minute TWAP should be much closer to 103 than to the midpoint 115. The oracle is saying: the 100 price described most of the interval, so it deserves most of the weight.
In continuous form, the idea is simple: add up price × time over the interval, then divide by the interval length. Many smart contracts implement this without storing every second’s price history. Instead, they maintain a running cumulative value that already represents the time integral of price. If you know the cumulative value at the start and end of a window, the average price over that window is just:
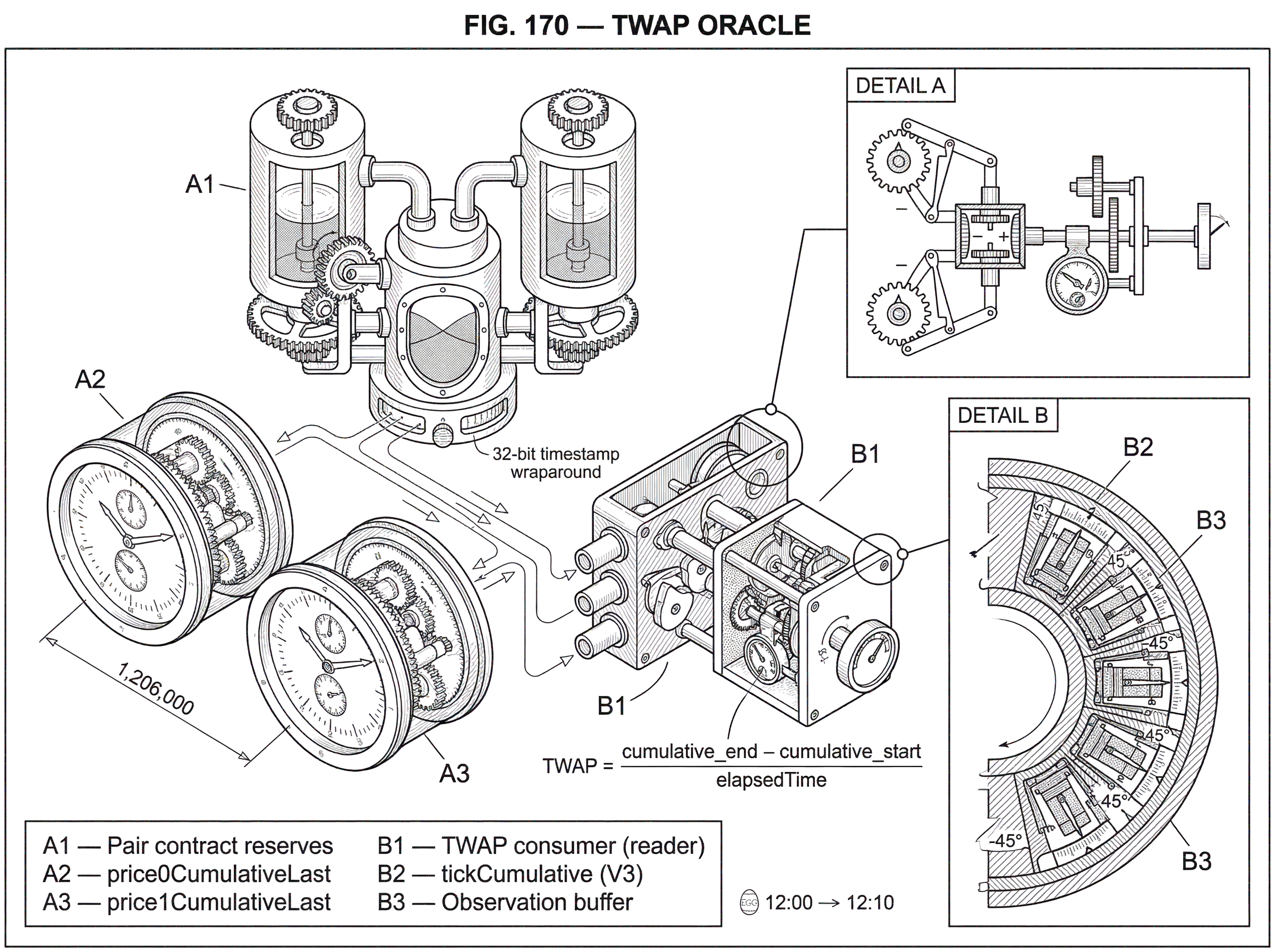
TWAP = (cumulativePrice_end - cumulativePrice_start) / elapsedTime
That formula is the key that makes on-chain TWAPs practical. You do not need a giant array of historical prices. You need a cumulative counter that advances as time passes.
How do AMM-based TWAP oracles compute on-chain averages?
The most influential on-chain TWAP design came from Uniswap. Its insight was not merely “average prices.” It was to store a cumulative price state that other contracts can read cheaply and deterministically.
In Uniswap V2, each pair contract maintains cumulative price variables. Conceptually, each variable is the sum of the pool’s implied price for every second in the pair’s history. When reserves are updated and time has elapsed, the contract increments the cumulative value by currentPrice × timeElapsed. Because this accumulation happens over time, the difference between two readings tells you the total area under the price curve during that interval. Divide by seconds elapsed, and you have a time-weighted average.
The pool exposes two cumulative values because a pair has two price directions: token0 priced in token1, and token1 priced in token0. Internally, Uniswap V2 computes price from reserve ratios using fixed-point arithmetic. The implementation updates price0CumulativeLast and price1CumulativeLast in the pair’s _update function, and only does so when time has advanced and both reserves are non-zero. That means the oracle state is tied directly to actual AMM reserve state.
Here is the mechanism in plain language. Suppose a USDC/ETH pool ends one block with reserves implying 2,000 USDC per ETH. If no one touches the pool for 30 seconds, the cumulative price grows as though 2,000 were added every second for those 30 seconds. If then a trade moves the pool to 2,020, the cumulative value starts growing at the new rate from that moment forward. When an oracle consumer later subtracts the earlier cumulative snapshot from the later one, the result naturally gives more influence to the price that lasted longer.
This design also explains why TWAP is resistant to trivial same-block manipulation. Uniswap V2 documentation emphasizes that each pair effectively measures the market price at the beginning of each block, before any trades in that block take place. To corrupt what the oracle will later average, an attacker generally needs to leave the pool in a distorted state at the end of the previous block, so that the next block begins from the manipulated price. That is much more expensive than briefly moving the price and reversing it in the same block.
But “more expensive” is not the same as “impossible.” If enough value depends on the oracle, manipulation can still be profitable. Uniswap’s own documentation warns that end-of-block measurement alone is not enough to guarantee safety, and that factors like network congestion can lower attack cost. The oracle is economically harder to move, not magically correct.
How do cumulative price counters produce a TWAP? (worked example)
Imagine a protocol wants a 10-minute ETH price from a USDC/ETH Uniswap V2 pool. At 12:00, it reads the pair’s cumulative price and stores it. At 12:10, it reads the cumulative price again. Suppose the second reading exceeds the first by an amount equal to 1,206,000 in “price-seconds.” Dividing by 600 seconds gives a TWAP of 2,010 USDC per ETH.
Why did that number emerge? Because over the 10-minute interval, the pool may not have sat at one price. Perhaps it spent 7 minutes around 2,000, then 2 minutes around 2,015, then 1 minute around 2,070 after a large buy. The short spike matters, but only for 1 minute of the 10-minute window. The average reflects the whole interval rather than the dramatic final moment.
Now imagine an attacker wants the protocol to believe ETH is worth 2,200 during that 10-minute window. If they distort the pool only in the final block, the TWAP barely moves. To meaningfully raise the average, they must either push the price much farther for a very short time or hold it moderately higher for many blocks. On an arbitraged AMM, both are costly. The further they push, the worse the execution they suffer. The longer they hold, the more often arbitrageurs can trade against them and the more fees they burn.
This is the security logic of a TWAP oracle in one sentence: it converts a price attack from a momentary state change into a sustained economic position.
How do liquidity depth and averaging window affect TWAP attack cost?
The strength of a simple TWAP oracle comes from two levers that interact directly with AMM mechanics: pool liquidity and averaging window length.
More liquidity means reserves are deeper, so moving price by a given percentage requires a larger trade. In a constant-product AMM, price impact is tied to how far you push the reserve ratio. A shallow pool can be moved dramatically with modest capital. A deep pool resists the same move. That is why “this pool has a TWAP oracle” says very little by itself; the question is really whether the underlying pool is deep enough for the protocol’s risk.
A longer averaging window means the attacker must either sustain the distortion for longer or create an even more extreme temporary distortion to compensate for the many honest minutes in the window. Uniswap’s documentation states that for a simple TWAP, manipulation cost grows approximately linearly with both liquidity and the averaging period. As a rough mental model, the attacker is paying some combination of arbitrage losses and swap fees every block they keep the market offside.
This is also why protocols often choose different TWAP windows for different assets. A deep ETH/stablecoin pool may support a shorter window while still remaining expensive to attack. A thin long-tail governance token may require a much longer window, or may be unsuitable for an AMM-only TWAP at all.
Importantly, aggregate TVL is not a perfect safety metric. Research on Uniswap V3 manipulation risk emphasizes that liquidity distribution matters, not just the headline dollar value in the pool. In concentrated-liquidity AMMs, liquidity can be dense near the current price and sparse farther away, or asymmetrical across directions. An attacker cares about the cheapest path to push price where they need it to go.
How does Uniswap V3 implement TWAPs differently from Uniswap V2?
| Protocol | On-chain state | Data unit | History capacity | Update constraint |
|---|---|---|---|---|
| Uniswap V2 | Cumulative price variables | Price × time (seconds) | Implicit via cumulative reads | Updated only when time advances |
| Uniswap V3 | Observation circular buffer | Tick cumulative (observations) | Limited by observation cardinality | Writable at most once per block |
Uniswap V3 still offers a TWAP-style oracle, but the internal representation is different. Instead of cumulatively storing the raw reserve ratio as in V2, V3 stores observations containing accumulators such as tickCumulative. A tick is the pool’s logarithmic price index, and the oracle computes a time-weighted average tick over an interval. That mean tick can then be mapped back to price.
The important conceptual point is that the invariant is unchanged: store a cumulative quantity that advances with price-like state × time, then recover an average from differences across time. In V3, the “price-like state” is tick rather than a direct reserve ratio. This is natural because V3’s concentrated-liquidity architecture already represents price movement along discrete ticks.
V3’s oracle stores observations in a circular buffer. Each observation includes a block timestamp and cumulative values such as tickCumulative. Consumers query the pool with a lookback like “30 minutes ago” and “now,” receive the two cumulative values, subtract them, and divide by elapsed time to get the arithmetic mean tick. Periphery helpers such as consult package this logic and also provide a harmonic mean liquidity measure for the interval.
This makes V3 more flexible, but it also introduces implementation details that matter operationally. Observation storage has finite cardinality and must be grown if users want deeper history. Observations are writable at most once per block. Queries can revert if you ask for data older than the oldest stored observation. So a V3 TWAP oracle is not just a formula; it also depends on whether the pool has enough observation history and whether someone paid the gas to expand that history.
Does proof-of-stake change TWAP manipulation risk?
| Consensus | Proposer predictability | Consecutive-block risk | Effect on TWAP safety | Primary mitigation |
|---|---|---|---|---|
| Proof-of-Work | Generally unpredictable | Low | TWAP relatively safer against multi-block attacks | Pool depth and longer windows |
| Proof-of-Stake | Proposer look-ahead possible | Higher | Multi-block manipulation more plausible | Wide-range liquidity and protocol guards |
For a long time, a comforting intuition about on-chain TWAPs was that attackers could not easily guarantee control over consecutive blocks. That made sustained manipulation difficult, because they might distort the market in one block only to have another participant or arbitrageur clean it up in the next. Proof-of-stake systems changed some of that reasoning, especially where proposers can know in advance when they will produce blocks.
Research from Uniswap on V3 oracles in Ethereum’s proof-of-stake setting argues that two-block manipulation of major pools remains prohibitively expensive today, largely because of wide-range liquidity. But it also emphasizes that multi-block manipulation becomes materially more plausible as the attacker’s validator market share rises. This is an important nuance. The oracle’s resistance is not only a function of pool design; it also depends on the chain’s block-production environment.
That does not mean TWAP stopped working under proof of stake. It means the old “a single-block spike will be arbitraged away” story was incomplete. A realistic security model now asks: how much liquidity is in the pool, how is it distributed, what window is being averaged, and how likely is it that an attacker can influence consecutive block boundaries? On some chains or under some validator distributions, those answers can be different enough to matter.
When should a protocol use a TWAP oracle?
Protocols use TWAP oracles when they need an on-chain price that is local, permissionless, and economically smoothed. Lending markets use them to value collateral and debt. Derivatives protocols may use them for settlement or margining. Liquidation systems may prefer a TWAP to reduce sensitivity to one-block spikes. Vault strategies and treasury systems sometimes use TWAPs for swap execution checks or sanity bounds.
The appeal is straightforward. The data source is on-chain and transparent. Anyone can inspect the pool state and reproduce the oracle calculation. There is no off-chain committee required just to compute the average. For permissionless systems, that simplicity is powerful.
But this also explains where TWAP fits relative to neighboring oracle designs. A TWAP from one AMM pool gives you a smoothed view of that pool’s market. It does not automatically give you the best estimate of the global market price across many venues. That is why multi-source oracle systems, often using VWAP-style aggregation across exchanges, are frequently preferred for assets whose security needs exceed what any single pool can safely provide. TWAP is often best understood as a robust local on-chain price, not a universal truth machine.
What are the common failure modes of TWAP oracles?
The main failure mode is simple: the cost to move the oracle is lower than the value an attacker can extract by moving it. Once you see that, many practical limitations fall out naturally.
If the pool is illiquid, the oracle can be cheap to manipulate even with a long window. If the protocol settles a very large amount of value from that oracle, attackers can justify taking larger losses in the pool. If the chain environment makes consecutive-block control more feasible, sustained distortions become easier. If congestion prevents arbitrage from correcting a manipulated pool quickly, attack cost can fall. These are not edge cases outside the model. They are the model.
There is also the lag problem. A TWAP can be secure precisely because it is slow, but that same slowness can become dangerous in fast markets. If ETH really crashes 20% quickly, a long TWAP may overstate collateral values for too long. If a stablecoin really depegs, a smoothed average can underreact. So the mechanism that protects against fake moves also delays response to real ones.
Implementation details create additional edge cases. In Uniswap V2, cumulative prices only advance when time has elapsed and reserves are non-zero. Timestamp arithmetic uses a 32-bit value with intentional wraparound, so consumers need to handle elapsed-time math correctly. In Uniswap V3, insufficient observation cardinality can make the desired lookback unavailable. These are not conceptual flaws in TWAP, but they are places where an integration can be wrong even if the math is right in principle.
What guardrails should protocols add around TWAP signals?
In practice, strong systems rarely rely on a TWAP oracle alone. They combine it with caps, delays, circuit breakers, liquidity checks, or alternative feeds. The reason is not that TWAP is bad. The reason is that oracle risk is context-dependent, and no single averaging rule can handle every failure mode.
A risk-sensitive protocol might use a Uniswap TWAP as its primary signal but cap how fast certain assets can appreciate, as seen in custom adapter designs for liquid staking tokens and stablecoins. Another system may delay the adoption of new prices so humans or keepers have time to react, as Maker’s Oracle Security Module does in a different oracle architecture. A lending market may also restrict borrow or collateral parameters for assets whose AMM-based TWAP is cheap to move, which is the logic behind Euler’s oracle-risk grading approach.
These controls all express the same lesson: oracle design is about shaping failure modes, not eliminating them. TWAP is one layer in that design space.
How should I choose a TWAP window for a given asset?
| Window | Freshness | Manipulation cost | Best for |
|---|---|---|---|
| Short (minutes) | High freshness | Lower attack cost | Fast markets, deep pools |
| Medium (10–60min) | Balanced freshness | Moderate attack cost | General DeFi use |
| Long (hours+) | Low freshness | Higher attack cost | Slow markets, thin liquidity |
A natural question is: what is the right TWAP period? Ten minutes? Thirty minutes? Twenty-four hours? There is no universal answer because the parameter is not purely mathematical. It encodes a risk budget.
A shorter window gives better freshness and lower lag, which helps in fast markets and keeps the oracle closer to current executable price. But it lowers manipulation cost. A longer window raises attack cost, but can make the protocol slow to recognize genuine regime changes. Uniswap’s own guidance for V2 is operationally simple: sample once per desired TWAP period. For a 10-minute TWAP, sample every 10 minutes; for a one-week TWAP, sample weekly. That tells you how to implement the arithmetic, not how to choose the right economics.
The right choice depends on the asset, the underlying pool, the amount of value secured by the oracle, the chain’s execution environment, and what happens if the oracle is wrong for a while. A mature protocol effectively asks: how expensive must an attack be relative to the maximum extractable value from manipulating this feed? That is why teams increasingly use cost-of-attack tools and liquidity analysis rather than choosing windows by convention alone.
Conclusion
A TWAP oracle is a price oracle that reports an average over time rather than the latest spot price. Its power comes from a simple mechanism: by averaging across many seconds or blocks, it forces an attacker to sustain a distortion instead of creating a momentary spike.
That makes TWAP one of the most important on-chain oracle patterns, especially for AMM-based DeFi. But its safety is never automatic. It depends on liquidity, window length, market structure, chain conditions, and the size of the reward for getting the oracle wrong. The idea to remember is short: TWAP does not make prices true; it makes lies expensive for longer.
What should you understand before using a TWAP oracle?
Before relying on a TWAP oracle, verify who computes the average, which AMM pool or observation the protocol reads, and the averaging window and liquidity that back that signal. On Cube Exchange, use that information to size orders and choose execution styles that respect TWAP lag and manipulation risk.
- Inspect the protocol’s oracle source on-chain or in its docs and note the exact AMM pair address and the TWAP lookback (e.g., 10 minutes, 1 hour).
- Read the pair’s current reserves and recent 24h volume (USD-equivalent) and, for Uniswap V3, check liquidity concentration near the current price to judge how cheaply the pool can be moved.
- Confirm the pool’s observation history or cumulative-timestamp coverage so the desired lookback is available (check observation cardinality, last observation timestamp, and whether a lookback query would revert).
- Fund your Cube account, pick the market and order type that suit the asset’s TWAP risk (use limit orders or split execution for assets with long TWAP windows), review estimated fees and expected fill, and submit.
Frequently Asked Questions
A TWAP oracle stores a running cumulative (price × time) counter and computes the average over a window by subtracting two cumulative snapshots and dividing by elapsed time, so you do not need to store per-second prices.
Because TWAP averages across time, an attacker must sustain a distorted pool price long enough for the distortion to significantly affect the average, which on AMMs typically costs them trading fees and arbitrage losses; a single brief spike therefore has much less influence than on a spot read.
Shorter TWAP windows react faster to real market moves but are easier and cheaper to manipulate; longer windows raise manipulation cost by forcing sustained distortions but increase lag and slow the oracle’s response to genuine price changes.
Proof-of-stake changed some threat assumptions because block proposers can know or influence consecutive-block boundaries, which makes multi-block manipulation more plausible as an attacker’s validator share grows, so TWAP security must now account for the chain’s proposer dynamics as well as pool liquidity.
Watch for implementation edge cases: Uniswap V2 cumulative prices only advance when time has elapsed and reserves are non-zero and timestamps use 32-bit wraparound, while Uniswap V3 requires sufficient observation cardinality, observations are writable at most once per block, and queries can revert if the requested lookback is older than stored history.
A TWAP from a single AMM pool gives a smoothed view of that pool’s on-chain market but is not automatically the best estimate of the global market price; for higher-security needs protocols commonly aggregate multiple venues (VWAP-style) or add other feeds.
Attack cost scales with both pool liquidity and the averaging period: deeper reserves make a given price move more expensive, and longer averaging windows force attackers to sustain distortions or make even larger temporary moves; concentrated-liquidity AMMs complicate this because liquidity distribution (not just headline TVL) determines how cheaply price can be pushed.
Protocols rarely rely on a single TWAP alone; they layer guardrails such as caps, delays, circuit breakers, liquidity checks, or alternative feeds to limit how much value can be settled from a potentially manipulated average and to shape the protocol’s failure modes.
Related reading