What Is a Non-Custodial Wallet?
Learn what a non-custodial wallet is, how it works, why private keys matter, and the main security, backup, and recovery tradeoffs of self-custody.
Introduction
**A non-custodial wallet is a wallet where you, not a service provider, control the private keys that control your assets. ** That is the whole idea, and it is the point from which everything else follows. If a blockchain is designed so that control comes from possession of valid signing keys, then the practical question is never just “where are my coins?” It is “who can produce the signature that the network will accept?”
That question matters because blockchains do not recognize names, customer accounts, or support tickets. They recognize valid transactions. A wallet, in the most basic sense, is the software or device that helps you manage the keys and transaction data needed to create those valid transactions. In a custodial setup, a company holds the keys and acts on your behalf. In a non-custodial setup, the wallet helps you hold and use those keys directly.
The appeal is obvious: if no third party holds your keys, no third party can normally freeze, seize, or misdirect your funds from the wallet side. But the cost is just as direct: you become responsible for security, backups, and recovery. There is no deeper escape hatch hidden behind the interface. If the keys are lost, the blockchain will not distinguish that from a deliberate choice to make the assets inaccessible.
This is why non-custodial wallets are not best understood as just a product category like “mobile wallet” or “hardware wallet.” They are a different trust model. Mobile, desktop, hardware, browser, and full-node wallets can all be non-custodial if the user retains key control. The meaningful distinction is not the shape of the app. It is who holds the power to sign.
How do private keys give control instead of account login?
| Custody model | Who controls keys | Can funds be spent without you | Recovery owner | Best for |
|---|---|---|---|---|
| Non‑custodial | User | No | User (seed/backup) | Self‑sovereignty; long‑term holdings |
| Custodial | Service provider | Yes | Provider (support) | Convenience; on‑ramp services |
A useful way to think about a blockchain wallet is that it does not really store coins in the way a bank account stores balances. The chain stores a public state: unspent outputs, account balances, token ownership records, smart-contract state, and so on, depending on the architecture. What the wallet stores is the ability to authorize changes to that state.
That ability comes from private keys. A private key is secret material used to produce digital signatures. The network can verify those signatures using corresponding public keys or addresses derived from them. If the signature is valid and the transaction obeys the chain’s rules, the network accepts the transaction. If not, it rejects it. This is the invariant that matters: the network accepts cryptographic proof, not human identity.
From that first principle, “non-custodial” becomes precise. A wallet is non-custodial when the user retains control of the private keys or seed material needed to derive them, rather than delegating that control to an intermediary. Bitcoin-oriented user guides describe this as giving you “full control” over your Bitcoin: no third party can freeze or take your funds, but you must secure and back up the wallet yourself. That is not marketing language. It is the operational consequence of how signature-based systems work.
This also explains a common misunderstanding. People often say the wallet “holds” their assets. In ordinary speech that is fine, but mechanically it can mislead. Your assets remain represented on-chain. The wallet is better understood as a key manager and transaction authoring tool. Some wallets add far more than that (portfolio views, swaps, staking, token discovery, dApp connections) but those are layers on top of the same base function: protect the signing authority and use it correctly.
How can you tell if a wallet is truly non‑custodial?
In practice, control can be implemented in several ways, but the decisive question stays the same: can the service spend without you? If a provider can unilaterally move funds because it holds the operative keys, that is custody. If the provider merely supplies software while the keys remain under your control, that is non-custodial.
This is easiest to see through a concrete example. Suppose you install a wallet app on your phone and it generates a recovery phrase for you. The app derives your keys locally, stores them on your device or in secure hardware on the device, and asks you to write down the recovery phrase. When you send funds, the transaction is assembled on the phone and signed with key material the provider never receives. Even if the wallet company disappears, you can usually recover the wallet elsewhere with the same seed phrase, assuming compatible standards and derivation paths. That is the non-custodial pattern.
Now contrast that with an exchange account. You log in with email and password, see a balance, and request a withdrawal. The exchange decides whether and when to sign a blockchain transaction on your behalf. You may have an economic claim against the exchange, but you do not have direct cryptographic control over the assets in the same way. The interface can feel similar; the trust structure is not.
This is why non-custodial and custodial wallets are the foundational comparison in wallet design.
Everything else comes downstream from that split.
- convenience
- recovery options
- fraud resistance
- support burden
- feature richness
What is a seed phrase and why does one backup restore all accounts?
| Backup approach | Recovery ease | If exposed | Operational cost | Best for |
|---|---|---|---|---|
| Single HD mnemonic | Very easy | Full compromise | Low | Most users; everyday convenience |
| Per‑address keys | Hard | Single‑address loss | Very high | Paranoid or archival workflows |
| Multisig (shared control) | Moderate (policy) | Partial compromise only | Medium | Organizations; shared treasuries |
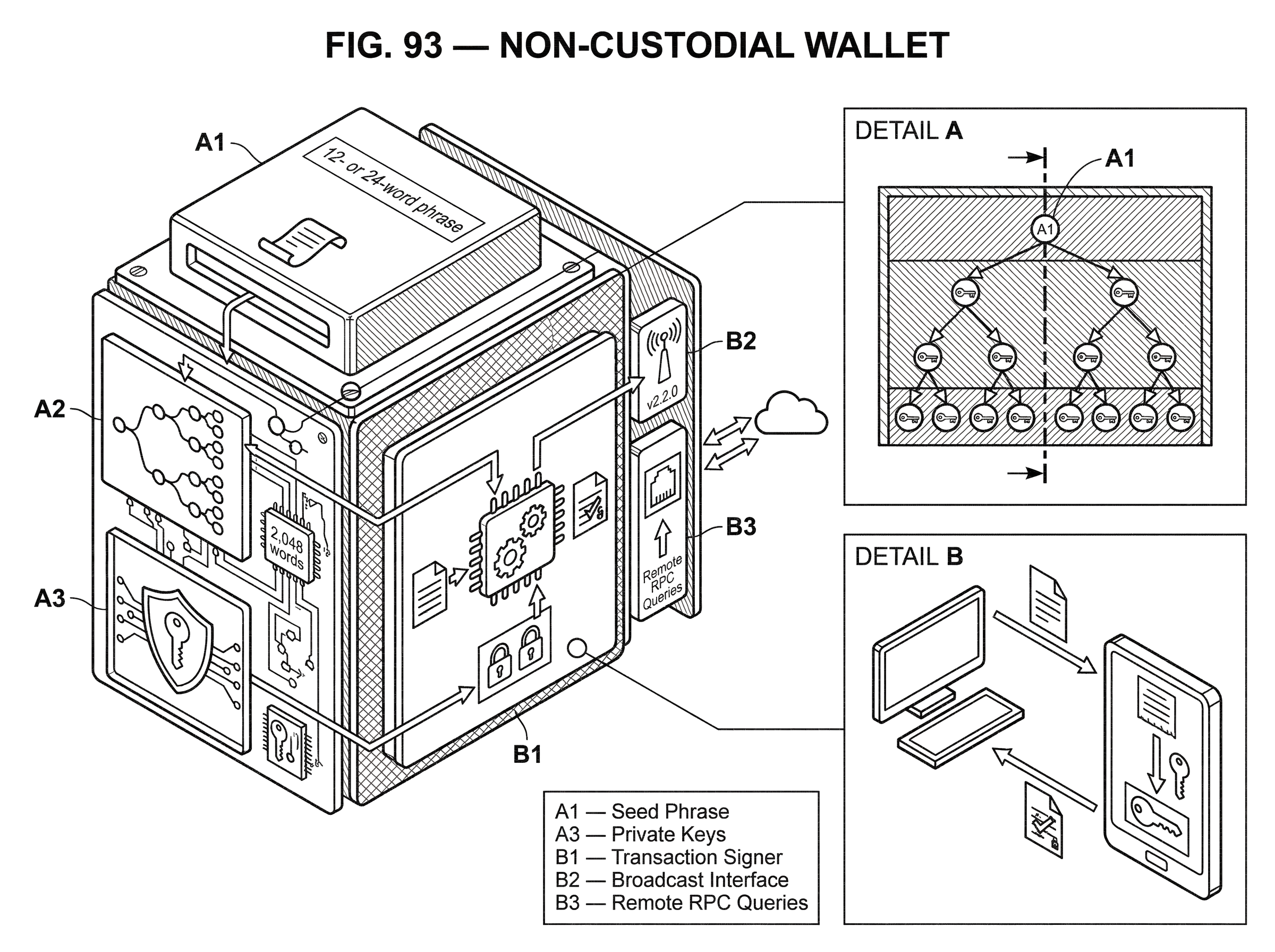
Most modern non-custodial wallets do not ask users to manage a separate private key for every address. That would be unusable. Instead, many wallets use deterministic key generation: a single secret seed can generate an entire family of keys, addresses, and accounts in a repeatable way.
This is where mnemonic recovery phrases enter. In many wallet designs, the seed is represented to the user as a list of words drawn from a fixed wordlist. The widely used English BIP-39 wordlist contains 2,048 words. The point of the words is not to make the secret weaker or more human in a cryptographic sense. The point is backup and recovery: a person can write down words more reliably than raw binary data.
Under the hood, the seed becomes the root from which the wallet derives many keys. BIP-32 defines a hierarchical deterministic, or HD, wallet structure for Bitcoin-style key trees. Its basic idea is simple and powerful: start from one master seed, derive a master extended key, and from there derive child keys in a tree. This means a single backup can restore many addresses and accounts. It also means that the recovery phrase is extremely sensitive. Anyone who obtains it may be able to reconstruct every key derived from that wallet.
That “single backup controls many accounts” property is one of the biggest usability breakthroughs in self-custody, but it is also one of the biggest concentration risks. A user no longer has dozens of small secrets to lose. They have one master secret they absolutely cannot expose.
A practical narrative makes this clearer. Imagine a wallet creates a 12- or 24-word phrase during setup. You write it on paper and store it safely. Months later your phone is lost. The app itself is gone, but the funds are not. You install a compatible wallet, enter the same phrase, and the software deterministically regenerates the same master seed, the same key hierarchy, and therefore the same spend authority over the addresses previously used. Recovery works because the wallet is reproducing the same mathematics from the same root secret. If, however, someone photographed that phrase when you first wrote it down, they can often do the same thing from anywhere.
How does hierarchical deterministic (HD) derivation turn one seed into many addresses?
The reason one recovery phrase can drive an entire wallet is the structure of HD derivation. BIP-32 defines extended keys, which combine a key with a 32-byte chain code. The chain code is not just extra decoration; it is part of the derivation mechanism that allows child keys to be generated deterministically from parent material.
This structure makes several useful things possible at once. A wallet can create many receiving addresses without asking the user to back up every new key. It can separate spending history into accounts. It can derive internal change addresses that are not meant to be shared publicly. And, in some cases, it can let one system generate public receiving addresses without having access to the private keys needed to spend.
BIP-44 adds a widely used convention for organizing this tree. It specifies a path of the form m / purpose' / coin_type' / account' / change / address_index. The apostrophe marks hardened derivation at those levels. The organizing principle here is separation: the path partitions the key space by standard, by chain, by account, by whether an address is public-facing or change, and then by individual address number.
This matters because non-custodial recovery is only reliable if different wallets agree on how to derive keys from the same seed. If one wallet uses one path and another uses a different one, the same phrase may restore a different set of addresses. The seed phrase is not the whole portability story. Derivation conventions matter too. BIP-44 explicitly uses separate coin_type' branches so one seed can organize multiple cryptocurrencies without reusing the same addresses across coins.
The same general idea appears outside Bitcoin-style secp256k1 systems, but not always with identical mechanics. SLIP-0010 extends deterministic derivation across multiple elliptic curves, including ed25519, which is used by some chains and tools. That extension exists because not every ecosystem can simply reuse BIP-32 unchanged. For example, public child derivation is not supported in the same way for ed25519 and curve25519 in SLIP-0010. The consequence for users is that mnemonic portability across wallets and across chains is not automatic just because two products both mention “seed phrase.” The recovery words may look familiar while the derivation rules underneath differ.
You can see this in practice on Solana tooling, which supports BIP-39 mnemonics and derivation paths such as m/44'/501'/0'/0'. The broad principle is shared with other HD wallets (one mnemonic can deterministically derive accounts) but the exact path and curve assumptions are chain-specific. So a non-custodial wallet is portable only to the extent that the destination wallet supports the same seed format, derivation method, and path conventions.
How do signing and broadcasting differ, and when should you sign offline?
To use a non-custodial wallet, two different jobs must happen. First, a transaction must be signed with the private key. Second, that signed transaction must be broadcast to the network. Those jobs do not have to happen in the same trust environment.
That separation is why hardware wallets exist. A hardware wallet is a physical device designed to keep key material in a separate, usually offline or strongly isolated environment. When you want to spend, the host computer or phone prepares transaction data, the hardware wallet signs it internally, and the host broadcasts the already-signed transaction. The private key need not leave the device.
This is the mechanism behind the claim that hardware wallets are among the most secure non-custodial options for larger balances. The security gain does not come from magic. It comes from reducing the attack surface. Malware on a laptop may be able to observe what you are doing, but if the private key never becomes available to the laptop in raw form, remote theft becomes much harder.
That said, the protection is specific. Hardware wallets help primarily against online key extraction. They do not eliminate every risk. If you reveal the recovery phrase, the attacker no longer needs the device. If you approve a malicious transaction, the device will faithfully sign what you approved. Some vendors distinguish between blind signing and clearer, human-readable signing because the unresolved problem is not only “is the key safe?” but also “does the user understand what they are authorizing?”
Which non‑custodial wallet type fits different threat models?
Non-custodial is about control, but the form factor still changes the threat model.
A desktop wallet can be powerful and flexible, especially for advanced workflows, but it lives on a general-purpose machine that may be exposed to malware, spyware, or poor operational hygiene. A mobile wallet is convenient for everyday use and payments, but phones are easier to lose, and app-store distribution creates an extra trust surface: malicious clones, delisting, or delayed updates. A browser wallet integrates well with web applications, but browser extensions sit close to phishing and malicious site interactions. A hardware wallet reduces online exposure, but introduces device-supply, firmware, and backup-handling concerns. A paper wallet stores keys offline in a very literal way, but becomes awkward and fragile in practice because spending safely from static printed secrets is harder than it first appears.
The important point is not that one category is universally best. It is that each form factor changes which failure modes dominate. For small daily balances, convenience often matters because users need frequent signing. For long-term holdings, isolation matters more because transactions are rare and the main job is preserving secret material over time.
This is why practical guidance often recommends hardware wallets for larger balances and lighter software wallets for routine use. The recommendation follows from threat exposure, not from branding.
How do full nodes, verification, and privacy affect non‑custodial wallets?
| Data source | Who validates blocks | Trust required | Resource cost | Privacy | Best for |
|---|---|---|---|---|---|
| Full node | Local full validation | Minimal third‑party trust | High (disk + CPU) | Best privacy | Security‑focused users |
| Light / SPV client | Partial validation | Some trust assumptions | Low–medium | Moderate privacy | Mobile and casual users |
| Remote API / indexer | Provider validates and indexes | High trust in provider | Minimal | Low privacy | Convenience; novices |
A non-custodial wallet can control keys while still depending on third parties for information about the chain. That is a subtle but important distinction.
Suppose your wallet asks a remote server for your balance, recent transactions, and the current fee environment. If the keys remain under your control, the wallet is still non-custodial. But you are trusting that server for data availability, transaction history, and perhaps some privacy-sensitive queries. The server may learn which addresses you care about. It may fail, censor, or return misleading information.
Running a wallet as a full node changes this by validating blocks and transactions locally. Bitcoin-oriented guidance describes this as removing trust in a third party when processing transactions, though it requires substantial memory and storage. Here the relevant mechanism is verification: instead of outsourcing your view of the chain, you check the rules yourself.
This also connects to privacy. Some wallets rotate addresses, avoid disclosing address relationships to arbitrary peers, or support routing through Tor to make it harder to link activity to your IP address. None of these tools creates perfect anonymity, and their effectiveness depends on the chain and the user’s broader behavior. But they address a real leak in many wallet designs: if the same infrastructure that helps you learn about the chain also learns exactly what you are watching, self-custody of keys does not automatically imply privacy of usage.
What are the main failure modes and risks of self‑custody?
The most important limitation is brutally simple: self-custody is unforgiving. If you lose the keys and the backup, there may be no recovery path. This is not a bug in customer service. It is the expected result of removing the custodian.
A second limitation is that “non-custodial” does not guarantee safe software. The Slope Wallet incident is a strong example. OtterSec’s investigation found that wallet versions since v2.2.0 were vulnerable to leaking private keys and mnemonics into Sentry logs, and analyzed logs contained private keys corresponding to a material share of hacked addresses. That is a particularly sharp lesson because the wallet model was still nominally self-custodial: the users, in theory, controlled the keys. But if wallet software serializes those secrets into telemetry, the practical security boundary collapses.
This points to a deeper truth. Non-custodial removes institutional custody risk, but it does not remove implementation risk. Bugs, supply-chain attacks, malicious updates, poor entropy, unsafe backups, phishing, and deceptive signing prompts remain. The trust surface becomes different, not nonexistent.
A third limitation is compatibility. Recovery phrases, derivation paths, address formats, and supported standards do not line up perfectly across ecosystems. On Bitcoin-like systems, BIP-32 and BIP-44 conventions created broad interoperability, though even there differences in script type and path conventions can matter. On ed25519-based systems or more programmable account models, the same mnemonic may not map cleanly into the same wallet state elsewhere. The comforting phrase “just import your seed” is only true when the receiving wallet reproduces the same derivation semantics.
Finally, some features that users expect can reintroduce trust. two-factor authentication in a wallet may depend on a third-party service. Sponsored transactions, relayers, and app integrations can improve usability while adding assumptions about availability or intent. The wallet may be non-custodial at the key layer while relying on outside infrastructure for parts of the experience.
When and why do people choose non‑custodial wallets?
Most people use non-custodial wallets for some mix of three goals: direct asset control, application access, and operational separation.
Direct asset control is the most basic. A user wants to receive, hold, and send assets without needing an exchange or broker to approve actions. That is the classic self-custody use case.
Application access becomes important on smart-contract platforms. Here the wallet is not only a vault; it is an identity and signing tool for interacting with dApps, swaps, NFTs, staking systems, and other on-chain programs. Solana’s wallet ecosystem emphasizes this programmable side, and Ethereum-style browser wallets do something similar in practice. The common mechanism is signature-based authorization of interactions with on-chain logic.
Operational separation matters for both individuals and organizations. A person may keep a hardware wallet for long-term holdings and a mobile wallet for spending. A team may use multisig arrangements so no one person can move treasury assets alone. HD structures and account separation make these patterns manageable because one seed or policy framework can organize many sub-accounts without collapsing them into one visible balance.
What is the single idea to remember about non‑custodial wallets?
A non-custodial wallet exists because blockchains grant control to whoever can produce the right cryptographic signature. If you hold the keys, you hold that power. If someone else holds them, they do.
Everything else is a consequence of that design. Self-custody gives you autonomy by removing the intermediary, and it gives you responsibility for exactly the same reason.
How do you secure your crypto setup before trading?
Secure your crypto setup before trading by confirming backups, device hygiene, and destination checks. Cube Exchange uses MPC-based non-custodial key management, so combine local key safety (or verified recovery for external wallets) with careful transfer and order checks before you trade or move funds on-chain.
- Fund your Cube account with fiat on-ramp or a supported crypto transfer so you have settlement currency available.
- Verify the exact asset and network you will trade or withdraw (token contract address, chain name, and address format).
- Confirm your recovery method: test that your seed phrase is correctly backed up offline or that you can access your Cube MPC recovery workflow.
- For any withdrawal or new destination, send a small test amount first and then place your trade (use a limit order if you need price control).
Frequently Asked Questions
If you truly retain the private keys or seed material, no intermediary can normally freeze or unilaterally move those on‑chain assets because blockchains accept cryptographic signatures, not human identity or support tickets.
Not usually - most modern non‑custodial wallets use a single mnemonic or seed to deterministically derive many keys and addresses (BIP‑39/BIP‑32 style), so restoring the same phrase in a compatible wallet recreates the same spend authority; however compatibility depends on matching derivation rules and paths.
No - a non‑custodial wallet can protect keys locally while still outsourcing chain data; if the wallet queries a remote server for balances or history you remain non‑custodial but you are trusting that server for data availability and privacy.
Hardware wallets reduce the risk of remote key extraction by keeping private keys isolated and signing transactions on‑device, but they do not remove all risk: revealing the recovery phrase, approving a maliciously constructed transaction, or device‑supply and firmware attacks can still lead to loss.
Self‑custody is unforgiving: if you lose both the device and any backup of the seed or private keys, the blockchain treats that as permanent loss of spend authority and there may be no recovery path.
Implementation and operational failures remain significant risks for non‑custodial wallets - examples include telemetry or logging bugs that leak mnemonics (as in the Slope incident), supply-chain compromises, phishing, and poor entropy - so non‑custodial custody changes the set of dominant threats rather than eliminating them.
No - mnemonic formats, derivation methods (paths, hardened vs non‑hardened derivation), and curve choices vary across ecosystems (e.g., BIP‑32/BIP‑44 for secp256k1 vs SLIP‑0010 for ed25519), so a phrase that restores keys on one chain or wallet may not reproduce the same addresses on another unless the destination supports the same standards and paths.
Non‑custodial wallets prioritize giving users signing control, but convenience features like two‑factor authentication, sponsored transactions, relayers, or third‑party APIs can reintroduce third‑party assumptions; those features can improve usability while creating additional availability or trust dependencies.
Related reading