What is secp256k1?
Learn what secp256k1 is, how its curve parameters define keys and signatures, and why Bitcoin, Ethereum, and other systems use it.
Introduction
secp256k1 is a specific elliptic curve together with a specific generator point and related parameters, used to build public-key cryptography such as ECDSA, ECDH, and Schnorr signatures. It matters because these systems only work if everyone is doing arithmetic in exactly the same mathematical setting. In Bitcoin, that setting is secp256k1. In Ethereum transaction signing, it is secp256k1. In many wallets, hardware devices, SDKs, and cryptographic libraries, secp256k1 is the curve that turns a 256-bit secret into a public key and a usable signature system.
That can sound almost trivial: just pick a curve and use it. But the choice is doing more work than it first appears. The curve determines the field where arithmetic happens, the shape of the set of valid points, the generator from which public keys are derived, the size of the scalar space for private keys, and some of the implementation tradeoffs that make software fast or fragile. A curve name is really shorthand for a tightly specified package of rules.
The most useful way to think about secp256k1 is this: it is not “a Bitcoin algorithm.” It is a shared coordinate system for elliptic-curve cryptography. Signature schemes like ECDSA and Schnorr sit on top of it. key exchange can sit on top of it. Address derivation conventions can be built from its public keys. Different chains and applications can use the same curve while choosing different signature formats, different public-key encodings, and different address schemes.
Why do blockchains use secp256k1 for public‑key cryptography?
Public-key cryptography needs a function that is easy to compute in one direction and hard to reverse. On secp256k1, that function is scalar multiplication of a point on an elliptic curve. You choose a secret integer d, multiply a fixed public base point G by d, and get a public point Q = dG. Computing Q from d is efficient. Recovering d from Q is believed to be computationally infeasible when the parameters are chosen well.
That asymmetry is the whole game. A private key can stay small and secret. The public key can be published. Anyone can verify that signatures match the public key, but they should not be able to work backward to the private key. SEC 1, the main ECC specification, defines an elliptic-curve key pair in exactly this way: a private scalar d in the interval [1, n - 1] and a public key Q = dG, where n is the order of the base point.
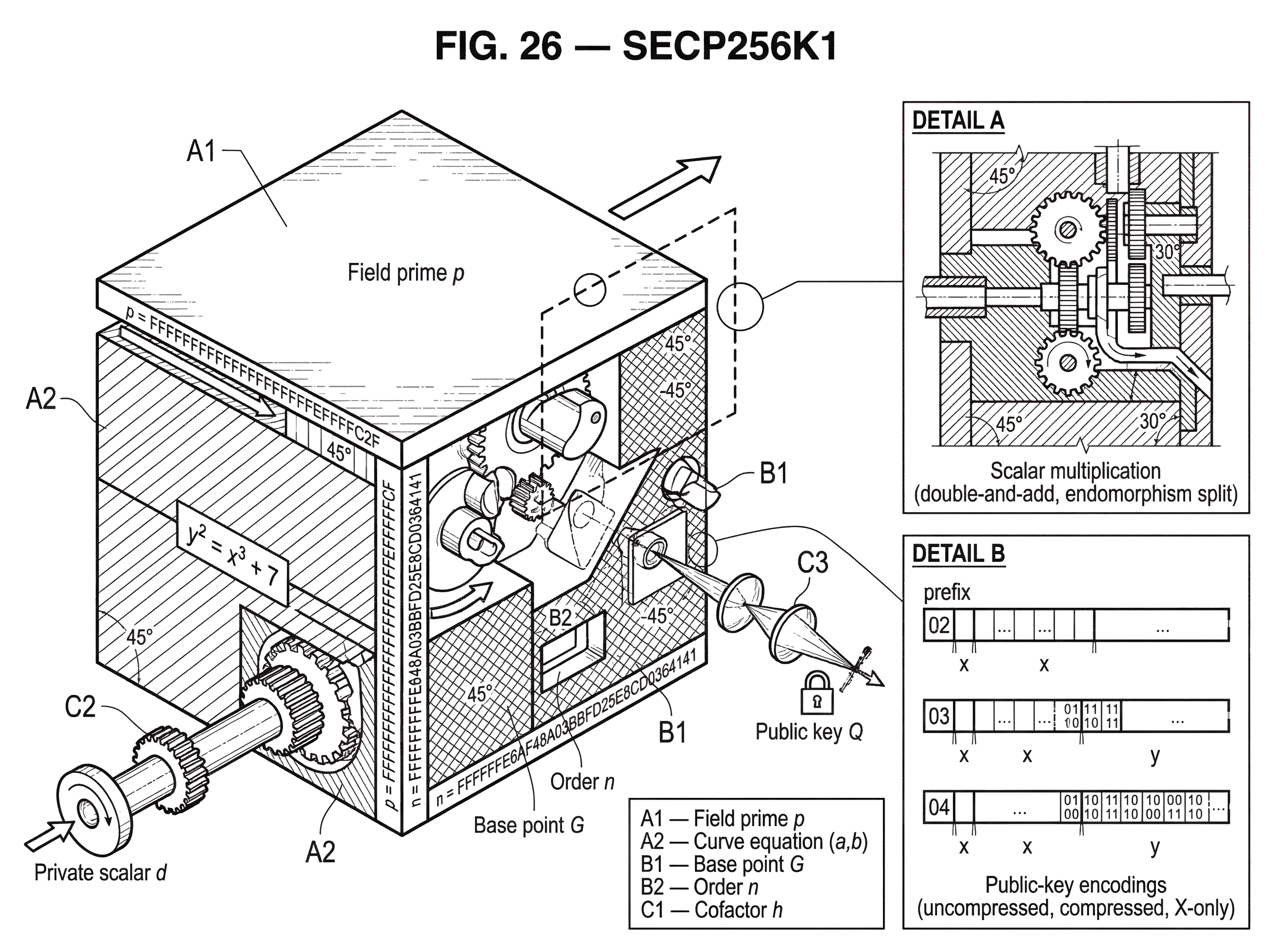
What secp256k1 contributes is the underlying group where this multiplication takes place. Without an agreed curve and generator, Q = dG is meaningless because G and the arithmetic rules would be ambiguous. The point of named curves such as secp256k1 is interoperability: everyone agrees on the same field prime p, the same curve equation coefficients a and b, the same base point G, the same order n, and the same cofactor h. SEC 1 describes this package as the domain-parameter tuple T = (p, a, b, G, n, h). SEC 2 publishes the concrete tuple for secp256k1.
What are the concrete parameters of secp256k1 (p, a, b, G, n, h)?
At the most concrete level, secp256k1 is an elliptic curve over a prime field Fp. The field prime p is
FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEFFFFFC2F
and SEC 2 also writes it as 2^256 - 2^32 - 2^9 - 2^8 - 2^7 - 2^6 - 2^4 - 1. That special form is not cosmetic. SEC 2 explicitly notes that its recommended prime-field parameters use special-form primes to facilitate especially efficient implementations. In plain language, reduction modulo p can be implemented faster than for a generic 256-bit prime.
The curve equation is the short Weierstrass form
y^2 = x^3 + ax + b over Fp
with a = 0 and b = 7, so for secp256k1 this becomes
y^2 = x^3 + 7.
This equation defines which pairs (x, y) count as points on the curve, together with a distinguished point at infinity that acts like the additive identity. The public arithmetic is not ordinary addition and multiplication of coordinates. Instead, points on the curve form a group under a special addition law. That is what makes repeated addition (scalar multiplication) possible.
The base point G is a published point on the curve. SEC 2 gives it in compressed form beginning with 02 79BE667E... and in uncompressed form beginning with 04 79BE667E...483ADA77... . Its order is
FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141
and the cofactor is h = 1.
That last detail, cofactor 1, is more important than it may look. It means the subgroup generated by G already has the full large prime order used for cryptography. In practice, this simplifies reasoning about subgroup structure and avoids some of the complexity that appears with curves whose cofactor is larger than 1. It does not remove the need for validation checks, but it does mean the main cryptographic subgroup is the whole relevant group for protocol purposes.
How do points and scalar multiplication produce public keys on secp256k1?
If elliptic curves feel abstract, the key invariant is simple: secp256k1 gives you a set of points where there is a well-defined notion of adding points, and that addition stays inside the set. Once you have that, you can define repeated addition. If P is a point, then 2P means P + P, 3P means P + P + P, and in general kP means adding P to itself k times.
SEC 1 calls scalar multiplication the fundamental elliptic-curve operation and notes that it can be computed efficiently with double-and-add and related methods. That efficiency is what makes public-key cryptography practical. A verifier may need to do one or more scalar multiplications for every signature. A wallet generating a public key performs scalar multiplication. Key agreement performs scalar multiplication. The curve is chosen so these operations are fast enough to use and structured enough to resist known attacks.
Here is the simplest nontrivial example in prose. Imagine Alice chooses a private key d, a secret integer between 1 and n - 1. She starts from the fixed generator G, which everyone knows. She computes Q = dG, meaning she adds G to itself d times using the curve’s group law. The result Q is her public key. Anyone can now use Q in a signature verification equation, but the security assumption is that seeing Q does not let them feasibly recover d. That assumed hardness is the elliptic-curve discrete logarithm problem for this group.
Notice what changes and what stays fixed. Alice’s private scalar d changes from user to user. Her public point Q changes accordingly.
But the domain parameters stay fixed for the entire ecosystem.
p- the curve equation
- the generator
G - the order
n - cofactor
h
That fixed structure is what lets two implementations written in different languages, on different devices, still agree on the same public key and the same signature checks.
Why does secp256k1 use the equation y^2 = x^3 + 7 and a special prime?
The name secp256k1 is partly administrative and partly descriptive. SEC 2 lists it among recommended 256-bit elliptic-curve domain parameters over prime fields. It also identifies secp256k1 as being associated with a Koblitz curve, generalized in that document to mean parameters admitting an efficiently computable endomorphism. The practical consequence is straightforward: implementations can exploit extra algebraic structure to speed up scalar multiplication.
This is one reason secp256k1 has long been attractive in performance-sensitive systems. The widely used libsecp256k1 library explicitly says it uses the endomorphism to split scalar multiplications, alongside techniques such as wNAF representations, large-window precomputation for multiples of G, and Shamir’s trick for combined multiplications during verification. None of these change the cryptographic definition of secp256k1. They are implementation-level ways of reaching the same mathematical result faster.
There is an important distinction here between fundamental structure and engineering choice. The field prime, curve equation, base point, order, and cofactor are fundamental. A library’s internal limb representation, precomputation tables, or exact multiplication algorithm are conventions and optimizations. Different libraries can implement the same curve differently and still be interoperable, as long as they produce the same mathematically valid outputs and enforce the same required checks.
How are keys and ECDSA/Schnorr signatures derived from secp256k1 parameters?
| Scheme | Purpose | Pubkey encoding | Signature size | Main benefit | Main risk |
|---|---|---|---|---|---|
| ECDSA | Single‑party signatures | Compressed or uncompressed (33/65 B) | DER variable | Widespread support | Signature malleability |
| Schnorr (BIP‑340) | Single‑party and multisig | X‑only 32 B | 64 bytes | Non‑malleable, linear | Nonce handling for multisig |
The curve by itself does not tell you how to sign a message. It gives you the group in which signing algorithms operate. That is why “secp256k1” and “ECDSA” are related but not interchangeable terms. The curve is the stage; ECDSA is one performance on that stage.
With ECDSA on secp256k1, the private key is still a scalar d, the public key is still Q = dG, and signatures are pairs of integers often written (r, s). SEC 1 is the main specification for these elliptic-curve signature schemes, while SEC 2 provides the concrete secp256k1 parameters they run on. Bitcoin’s traditional signatures are exactly this pairing: ECDSA using secp256k1.
Ethereum also uses ECDSA over secp256k1 to derive the sender of a transaction. The Ethereum Yellow Paper states that the sender mapping happens through ECDSA on the SECP-256k1 curve using the hash of the transaction, excluding the signature fields, as the signed datum. Ethereum transactions carry r and s plus a parity-related field used in public-key recovery. That is already a useful reminder that the same curve can appear inside different surrounding conventions. Bitcoin and Ethereum share secp256k1, but they do not use identical transaction formats, hashing conventions, or address derivations.
The same curve also supports Schnorr signatures. BIP-340 defines a concrete 64-byte Schnorr signature standard over secp256k1. Here the public key is encoded in an X-only 32-byte form, and signatures are encoded as (r, s) with specific even-y conventions. The verification equation differs from ECDSA, and the motivation differs too: Schnorr signatures offer stronger provable properties, non-malleability, and linearity that enables efficient multisignatures and threshold constructions. But the underlying curve arithmetic is still secp256k1.
This is a good place to guard against a common misunderstanding. When people say “Bitcoin uses secp256k1,” they often really mean a bundle of choices: secp256k1 for the curve, ECDSA for older signatures, BIP-340 Schnorr for newer Taproot signatures, compressed or X-only public-key encodings, and then Bitcoin-specific transaction and script rules around all of that. The curve is only one layer.
How do compressed, uncompressed, and X‑only encodings differ for secp256k1 public keys?
| Encoding | Prefix byte | Bytes | Contains y? | Interop note |
|---|---|---|---|---|
| Uncompressed SEC | 0x04 | 65 | Yes | Legacy format larger on wire |
| Compressed SEC | 0x02 / 0x03 | 33 | Implicit parity | Common wallet format |
| X‑only (BIP‑340) | none (implicit) | 32 | No, even‑y convention | Requires X‑only validation |
A point on secp256k1 is not the same thing as its byte encoding. That distinction matters in every real system.
SEC 2 publishes the generator G in both uncompressed and compressed form. In uncompressed form, a point is encoded with a prefix byte 04 followed by both coordinates. In compressed form, only the x coordinate is stored, along with a prefix byte that tells you which of the two possible y values to choose. Because the curve equation is symmetric in y and -y, a given valid x typically corresponds to two possible points, so the extra parity bit breaks the tie.
Cosmos SDK documentation shows this convention directly for secp256k1 public keys: compressed serialization uses a 0x02 or 0x03 prefix followed by the x coordinate, and secp256k1 public keys are 33 bytes in this form. BIP-340 goes one step further and uses X-only public keys, with an implicit even-y rule. That produces 32-byte public keys, but only because the protocol fixes a convention for which of the two corresponding points counts as the representative.
This is a place where implementations often go wrong. If one system expects compressed SEC-style points and another expects X-only keys, they are not using “different curves,” but they are using different encodings and different validation rules. Interoperability failures often happen at this boundary, not in the abstract math.
What validation checks must implementations perform for secure secp256k1 use?
From a distance, elliptic-curve cryptography can look like pure algebra. In practice, much of the real security comes from rejecting malformed inputs.
SEC 1 is unusually explicit on this point: conformant implementations must perform the cryptographic checks included in the scheme specifications, and those checks are essential to prevent subtle attacks. The reason is structural. Signature verification and key agreement assume that supplied points and scalars really belong to the intended mathematical objects: that a public key is actually on the right curve, that it is not the point at infinity, that it lies in the right subgroup, that signature components are in range, and so on.
What breaks if these assumptions change? You can get invalid-curve attacks, small-subgroup problems, signature acceptance mismatches across implementations, or side channels that leak secrets because edge cases are handled differently. The evidence around secp256k1 implementations illustrates this clearly. The libsecp256k1 project emphasizes constant-time, constant-memory-access signing and public-key generation, because timing differences can leak information about secret-dependent operations. Its release history also records fixes for compiler-specific constant-time issues in ECDH, showing that even correct-looking source code may fail the intended side-channel model after compilation.
There are also examples of range-checking problems. A RustSec advisory for a libsecp256k1 crate reported acceptance of signatures whose R or S parameter was larger than the secp256k1 curve order, differing from other implementations and potentially leading to invalid signatures being verified. That is not a failure of secp256k1 as a mathematical object. It is a failure to enforce the mathematical rules at the software boundary.
So when people ask whether secp256k1 is “secure,” the answer has two layers. The curve parameters support cryptographic schemes under standard hardness assumptions. But actual safety depends heavily on implementation discipline: constant-time arithmetic, strict parsing, proper key validation, careful nonce handling, and rejection of malformed data.
How can nonce mistakes lead to private‑key recovery on secp256k1?
The curve gives you the key relation Q = dG, but signature algorithms introduce another secret value that must be handled correctly: the per-signature nonce. This is where many real-world signature failures historically come from across ECC systems.
libsecp256k1 highlights derandomized ECDSA via RFC 6979 or caller-provided randomness. The point of deterministic or carefully mixed nonce generation is to avoid catastrophic dependence on a weak random-number generator. If the nonce in ECDSA is biased, reused, or otherwise predictable, the private key can often be recovered.
BIP-340 makes the same concern visible for Schnorr signatures on secp256k1. Its signing algorithm derives the nonce through a tagged hash construction and recommends unpredictable auxiliary randomness for extra side-channel protection. It also warns that multisignature schemes are insecure when using the default nonce generation naively. That warning gets at a broader principle: the curve is stable, but protocol composition changes the risk model. Once multiple parties coordinate a signature, or once signing happens on constrained devices, or once secrets cross software and hardware boundaries, the hardest part is often nonce hygiene rather than point multiplication itself.
Which other chains and wallets use secp256k1 and how do their conventions differ?
Because secp256k1 is just a named curve, not a chain-specific protocol, it appears in ecosystems that otherwise have very different designs.
We already saw Ethereum use it for ECDSA transaction signing and public-key recovery. Cosmos SDK supports secp256k1 as a built-in signature key scheme for account authentication, serializing public keys in compressed form and using BIP32/BIP44-style derivation for wallets. Substrate and Polkadot tooling supports ECDSA on secp256k1 as a selectable key scheme even though sr25519 is often the default; the Beefy session key type uses ECDSA in that stack.
These examples are useful because they show what is fixed and what is not. The curve and its group law remain the same. But addresses may be 20-byte hashes, SS58 strings, Bech32 strings, or something else entirely. Public keys may be compressed, uncompressed, or X-only. Signatures may be DER-encoded ECDSA, fixed-width encodings, or BIP-340 Schnorr. What secp256k1 gives all of them is the same hard underlying discrete-log problem and the same point arithmetic.
secp256k1 vs other curves (ed25519, NIST): what are the trade‑offs?
| Curve | Form | Performance | Implementation friendliness | Typical adoption |
|---|---|---|---|---|
| secp256k1 | Weierstrass prime‑field | High using endomorphism | Requires specialized optimizations | Bitcoin, Ethereum, many chains |
| ed25519 | Twisted Edwards | High constant‑time friendly | Simpler safe implementations | SSH, privacy coins, libraries |
| secp256r1 (P‑256) | Weierstrass prime‑field | Good | Widely standardized, more conservative | TLS, NIST aligned systems |
Curve choice is never only about raw security level. It is also about implementation complexity, side-channel resistance, ecosystem inertia, and standardization.
NIST guidance today includes newer Edwards curves and notes advantages such as increased performance, side-channel resistance, and simpler implementation compared with traditional Weierstrass curves. secp256k1, by contrast, is a short Weierstrass prime-field curve. That does not make it obsolete, but it does explain why engineers often compare “the curve itself” with “the quality of the software ecosystem around it.” A curve that is mathematically sound may still be harder to implement safely than a newer design with more implementation-friendly formulas.
At the same time, secp256k1 has a very mature ecosystem. The bitcoin-core/secp256k1 library exists precisely because generic elliptic-curve libraries were not enough for the assurance and performance expected in production cryptocurrency systems. It focuses on portability, minimal dependencies, extensive testing, constant-time operations, and optimized arithmetic specialized to this one curve. That specialization is a tradeoff: less generality, more confidence and speed for a high-value target.
Conclusion
**secp256k1 is the named elliptic-curve parameter set that defines the mathematical world used by many blockchain signature systems. ** Its field prime, equation y^2 = x^3 + 7, generator point G, order n, and cofactor 1 together create a group where public keys are Q = dG and where schemes like ECDSA and Schnorr can operate.
The short version to remember is this: secp256k1 is not a signature algorithm by itself. It is the exact curve and generator that make those algorithms concrete, interoperable, and efficient. And in practice, the difference between secure use and insecure use is often not the curve choice alone, but whether implementations respect the mathematical rules with rigorous validation, constant-time code, and careful nonce handling.
What should you understand before using this part of crypto infrastructure?
Before trading, depositing, or approving contracts, know how secp256k1 affects addresses, signature formats, and validation rules so you avoid mismatched encodings or insecure signing. On Cube Exchange, use the transfer and account workflows to confirm chain, address format, and signing expectations before moving meaningful funds.
- Confirm the chain and address format: check the destination chain, and verify whether the address or public key expects compressed (0x02/0x03), uncompressed (0x04), or X-only (32‑byte) secp256k1 encodings.
- Verify the expected signature scheme: confirm if the destination uses ECDSA (traditional) or Schnorr/Taproot (BIP‑340) and choose the matching transfer or contract method on Cube.
- Check key custody and nonce hygiene: if you control signing keys, use wallets or devices that implement RFC 6979 or BIP‑340 nonce derivation (or hardware RNG); if a counterparty signs, ask for their nonce/derivation guarantees.
- Run a small test transfer from your Cube account, inspect the on‑chain receipt and public‑key encoding, then proceed to larger deposits or trades once confirmations and encodings match.
Frequently Asked Questions
Cofactor 1 means the subgroup generated by the published base point G already has the full large prime order used for cryptography, which simplifies subgroup reasoning and avoids small‑subgroup complications; it does not eliminate the need for validation checks (e.g., ensuring a public key is on the curve and not the point at infinity).
secp256k1 is a short Weierstrass, prime‑field curve (y^2 = x^3 + 7) with special‑form prime p and a Koblitz‑associated endomorphism that implementations can exploit for speed; by contrast, curves like ed25519 use different curve models (Twisted Edwards) and often trade different formula simplicity and side‑channel properties for similar security levels.
Yes - the curve supports ECDSA, Schnorr (e.g., BIP‑340), and ECDH: the curve defines the group law and scalar multiplication while the signature or key‑agreement protocol sitting on top (ECDSA/ECDH/Schnorr) determines exact signing, nonce, and encoding rules.
Most interoperability errors come from mismatched encodings and validation rules: compressed SEC (0x02/0x03) versus uncompressed (0x04) versus X‑only (32‑byte even‑y) representations change byte layouts and parity rules, so two systems using different public‑key encodings or different acceptance rules can disagree even though they use the same curve.
Implementation mistakes - missing curve or subgroup checks, accepting out‑of‑range signature components, or non‑constant‑time operations - cause most real failures; examples include projects accepting oversized R/S values and compiler‑dependent constant‑time bugs that were later fixed in libsecp256k1 and related forks.
Weak, repeated, or biased per‑signature nonces are the common root cause of private key recovery; recommended mitigations include deterministic nonces per RFC 6979 or nonce derivation schemes with auxiliary randomness (BIP‑340’s tagged‑hash plus optional randomness), and special care for multisignature protocols where naive nonce use is insecure.
SEC 2 publishes secp256k1’s concrete parameters (p, a, b, G, n, h) but does not provide a verifiable generation seed or transcript for the curve constants, so there is no auditable seed recorded in that document for secp256k1’s parameter selection.
Related reading