What is Curve25519?
Learn what Curve25519 is, how its elliptic-curve math works, why X25519 and Ed25519 use it, and what its cofactor and side-channel tradeoffs mean.
Introduction
Curve25519 is an elliptic curve designed for modern public-key cryptography, especially fast and robust key exchange. Its importance is not just that it offers roughly 128-bit security, but that it was shaped around a harder engineering problem: how to get strong cryptography that implementations can realistically do correctly under side-channel pressure, interoperability constraints, and messy real-world inputs.
That design goal explains why Curve25519 shows up so often. In practice, people usually meet it through X25519, the Diffie–Hellman function defined over the curve and standardized in RFC 7748, or through Ed25519, a signature system built on an equivalent Edwards-form curve as specified in RFC 8032. The curve itself is the mathematical object underneath those protocols. If you understand what the curve is solving, why its parameters look the way they do, and how its arithmetic is used, the surrounding algorithms make much more sense.
The central puzzle is this: elliptic-curve cryptography had been known for a long time, so why did Curve25519 become such a default choice? The answer is not merely “because it is secure.” Many curves aim at security. Curve25519 became influential because it combines three things that are often in tension: a mathematically sound group, arithmetic that maps well onto ordinary hardware, and scalar-multiplication formulas that can be implemented in a regular, exception-free way.
What group structure does Curve25519 use and why does it matter?
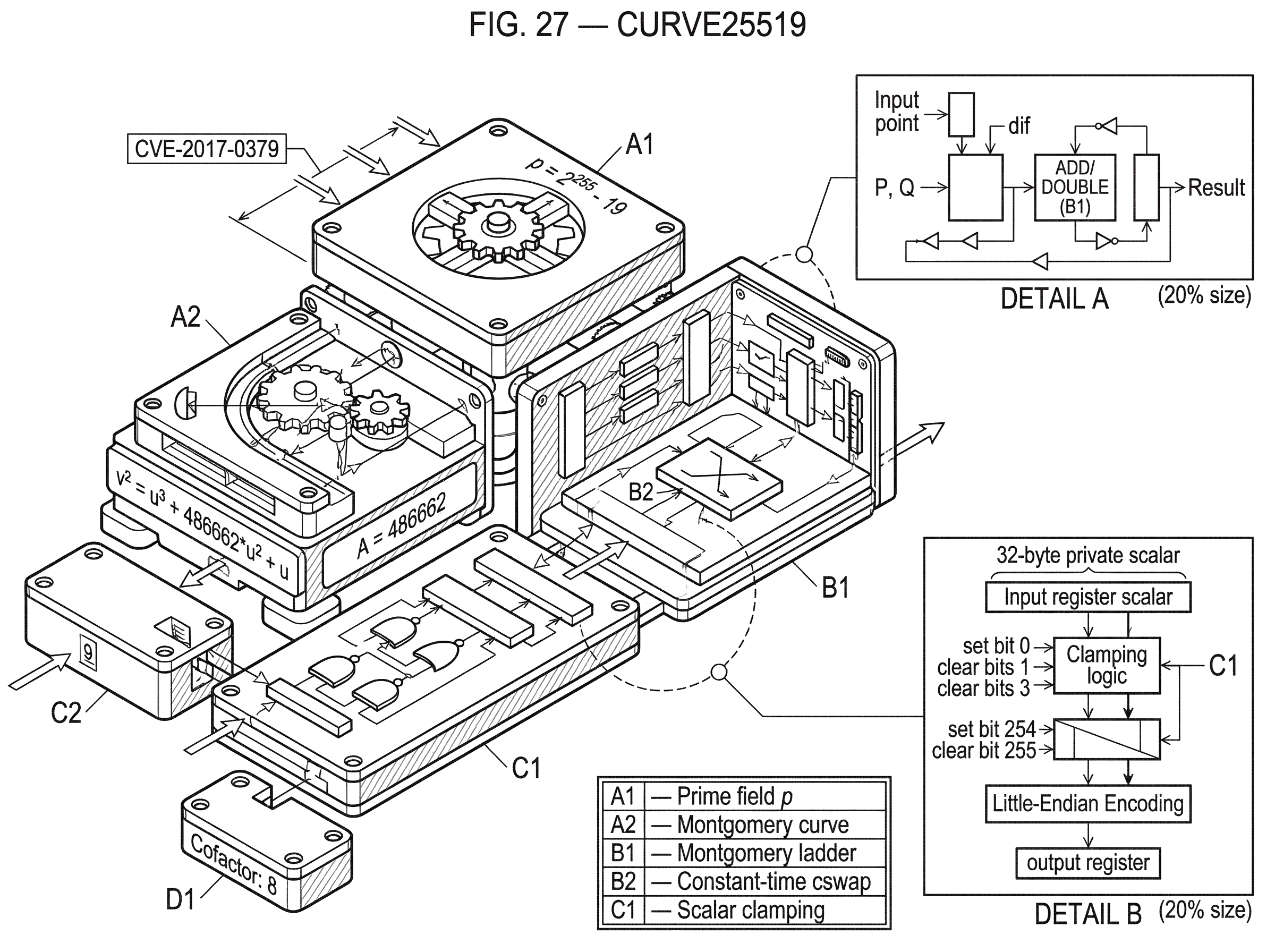
At the mathematical level, Curve25519 is an elliptic curve over the finite field with prime modulus p = 2^255 - 19. Saying “over a finite field” means all arithmetic is done modulo that prime. Numbers wrap around after p, and every coordinate lives in that finite arithmetic world.
The curve is usually presented in Montgomery form as v^2 = u^3 + A*u^2 + u, with A = 486662. For Curve25519, that gives the specific equation v^2 = u^3 + 486662*u^2 + u over the field modulo 2^255 - 19. RFC 7748 standardizes exactly these parameters, along with a cofactor of 8 and a standard base u-coordinate of 9 for the commonly used generator.
Why do cryptographers care about a curve equation at all? Because the set of points satisfying that equation, together with a special point at infinity, forms a group under a geometric-looking addition law. The geometry is usually drawn over the real numbers, but the same algebra works over finite fields. That group structure is what lets you take a point P and repeatedly add it to itself to form kP, where k is an integer. Public-key cryptography on elliptic curves is built around the fact that computing kP is easy, while recovering k from P and kP is believed to be hard.
That is the invariant worth remembering: Curve25519 gives you a group where scalar multiplication (taking a scalar k and a point P to compute kP) is the fundamental operation. Everything else is arranged around making that one operation secure, efficient, and regular.
Why does Curve25519 use the prime 2^255−19 and coefficient 486662?
The prime 2^255 - 19 is not an arbitrary flourish. It is close to a power of two, which matters because computers naturally operate on binary words. Arithmetic modulo a prime that looks like a power of two plus or minus a tiny adjustment can be implemented very efficiently: reductions can exploit the identity 2^255 ≡ 19 (mod p). That means large intermediate values can be folded back into range with relatively simple operations.
This is a good example of a design choice that is fundamental rather than conventional. The cryptographic security goal could in principle have been pursued with many different primes, but picking one of this form changes the implementation cost in a deep way. Faster field arithmetic is not just about speed benchmarks. The simpler the reduction structure, the easier it is to write code with fewer special cases and fewer opportunities for timing leakage.
The coefficient A = 486662 also comes from a design process, not from aesthetic preference. RFC 7748 describes deterministic criteria used to generate the curve family, including conditions on the trace of Frobenius, embedding degree, and CM discriminant. The point of that procedure is to avoid hidden parameter choices. In elliptic-curve cryptography, unexplained constants make people nervous for good reason: if a curve’s parameters seem hand-picked without an auditable method, readers may worry that some subtle weakness was engineered into them. Curve25519’s parameter generation was intended to be inspectable rather than mystical.
So the field shape helps computation, and the parameter-generation process helps trust. Those are different problems, but both matter if a curve is going to be adopted widely.
How does scalar multiplication power X25519 key exchange?
| Algorithm | Branches on secret? | Constant-time friendly? | Best for | Typical use |
|---|---|---|---|---|
| Montgomery ladder | No | Yes | Regular scalar multiplication | X25519 key exchange |
| Double-and-add | Yes | No | Simple implementations | Older ECC code |
| Fixed-window methods | Can be avoided | Requires care | Faster at scale | High-performance libs |
Most users never manipulate arbitrary points on Curve25519 directly. Instead, they use a function like X25519, which takes a scalar and a u-coordinate and returns another u-coordinate. This is Diffie–Hellman on the Montgomery form of the curve.
That restriction to the u-coordinate is one of the ideas that makes Curve25519 practical. For key exchange, you do not need the full point representation in the usual way. You only need enough structure to compute scalar multiplication consistently and derive a shared secret. By staying in the Montgomery setting and working with u-coordinates, the protocol can use a very regular algorithm: the Montgomery ladder.
The ladder matters because it gives a nearly uniform pattern of computation across scalar bits. Instead of branching wildly depending on secret data, it performs a fixed rhythm of doubling and differential addition as it scans bits of the scalar. RFC 7748 specifies a ladder structure with a constant-time conditional swap, usually called cswap, and explicitly advises implementing that swap in constant time.
This is the compression point for understanding Curve25519 in practice: it is not just a curve with good algebra; it is a curve whose form supports a scalar-multiplication algorithm that is unusually friendly to constant-time implementation. That regularity is why Curve25519 became associated with “safe by design” engineering, even though no real implementation is automatically safe just because it uses the curve.
How does an X25519 key exchange work step‑by‑step?
Suppose Alice and Bob want to agree on a shared secret over an untrusted network. Each generates a 32-byte private scalar. In X25519, those bytes are not used completely raw. RFC 7748 defines a decoding step often called clamping: certain low bits are cleared, the top bit is cleared, and another high bit is set. For X25519 this is specified by masking the first and last bytes so the scalar has the required form.
Why do that? The immediate effect is that the scalar becomes a multiple of the cofactor-related structure the algorithm expects, and it falls into a range that avoids some edge cases. The deeper point is consistency: every compliant implementation transforms secret scalar bytes into a form that interacts with the curve in a controlled way.
Alice then computes X25519 with her private scalar and the standard base u-coordinate 9. The result is her public key, a 32-byte little-endian encoding of a u-coordinate. Bob does the same with his own scalar. They exchange public keys.
Now Alice takes her private scalar and Bob’s public u-coordinate and computes X25519 again. Bob takes his scalar and Alice’s public u-coordinate and computes the same function. Both sides arrive at the same output because elliptic-curve scalar multiplication has the commutative property that matters here: a(bP) = b(aP) = (ab)P, where a and b are the private scalars and P is the base point.
Nothing in that story is specific to TLS, a wallet, or a blockchain. It is the same mechanism whether X25519 is used in a secure messaging protocol, a VPN, or a TLS 1.3 handshake. TLS 1.3 includes x25519 as a named group for ephemeral Diffie–Hellman key agreement, which is one reason Curve25519-based exchange became so widely deployed on the public internet.
What are X25519 encoding rules and why do they matter for interoperability?
Cryptographic interoperability often fails at the boundaries: how keys are serialized, how inputs are decoded, and what implementations accept or reject. Curve25519’s modern standardization paid unusual attention to those details.
RFC 7748 defines X25519 inputs and outputs as fixed-length 32-byte strings in little-endian form. It also specifies that X25519 implementations must accept non-canonical values on input and mask the most significant bit of the final byte when receiving an input u-coordinate. Those rules are not decorative. They reduce needless incompatibility and keep the function’s behavior close to “take bytes, decode them, do the ladder, return bytes.”
This matters because many cryptographic bugs happen when libraries disagree about what counts as a valid input. Some implementations reject twist points or non-canonical encodings; others follow the Montgomery-ladder behavior more permissively. RFC 7748 warns that such choices can produce observable differences. That does not automatically create a break, but it does create room for fingerprinting, interop surprises, or protocol assumptions that were never written down.
The lesson is easy to miss: on curves like Curve25519, the encoding rules are part of the cryptographic object as used in practice. A protocol that says “we use Curve25519” but does not make clear whether it means raw curve arithmetic, X25519 as standardized, or some library-specific subset is leaving important behavior implicit.
What does Curve25519’s cofactor 8 mean for security and implementations?
| Issue | Cause | Effect | Recommended mitigation |
|---|---|---|---|
| Small-order inputs | Group has cofactor 8 | Private contribution can cancel | Reject or validate input points |
| All-zero output | Input order divides cofactor | Shared secret becomes zero | Check for all-zero and abort |
| Optional checks in RFC | RFC leaves check as MAY | Different implementations differ | Protocols should mandate behavior |
Curve25519 has cofactor 8. That means the full group of curve points is not itself prime order; instead, it contains a large prime-order subgroup, and the total group size is eight times that subgroup order.
Why is that important? In an idealized cryptography course, one often imagines working in a prime-order group where every non-identity point behaves cleanly. Real curves often have extra small-order structure. On Curve25519, points of small order exist, and if an implementation performs scalar multiplication on such an input, the result can erase the contribution of the private key in ways protocol designers need to understand.
RFC 7748 calls out a specific consequence: because of the cofactor, an input point of small order can cause X25519 to produce the all-zero output. The RFC says implementations may check for this all-zero result and abort. The fact that the check is optional is worth noticing. It means the curve and function are standardized with a certain permissiveness, but protocols that rely on stronger guarantees may need to impose a stricter rule themselves.
This is a place where smart readers often misunderstand the slogan “Curve25519 is safe.” The safer statement is narrower: the curve and its standard algorithms were designed to be easier to implement securely than many alternatives. That does not mean cofactors disappear, invalid inputs stop mattering, or protocol-level checks become unnecessary. It means the core arithmetic is better behaved under implementation pressure.
How are Ed25519 and X25519 related, and when should you use each?
| Primitive | Curve form | Primary use | Wire format | Interchangeable? |
|---|---|---|---|---|
| X25519 | Montgomery | Diffie–Hellman key exchange | 32-byte u-coordinate | Not directly, conversion is tricky |
| Ed25519 | Twisted Edwards | Digital signatures | Encoded y with sign bit | Not directly, different API |
Many people first hear “Curve25519” in a signature context, but signatures and Diffie–Hellman use different representations. RFC 8032 states that Ed25519 uses a curve equivalent to Curve25519 under a change of coordinates. Equivalent here means the discrete-log difficulty is the same, not that the wire formats and formulas are interchangeable.
This distinction exists because different jobs favor different curve forms. The Montgomery form underlying X25519 is excellent for simple and regular scalar multiplication on u-coordinates. The twisted Edwards form underlying Ed25519 is excellent for signatures because it has fast formulas and, importantly, complete addition formulas that reduce exceptional cases.
So Curve25519 is best thought of as a family center rather than a single user-facing API. X25519 is the key-exchange function on the Montgomery form. Ed25519 is the signature system on an equivalent Edwards form. They are neighbors by deep mathematics, but they are not the same operation wearing different names.
That is also why key conversion between Ed25519 and X25519 needs care. Libsodium documents APIs for converting Ed25519 keys to X25519 keys, but it also recommends using distinct keys for signing and encryption when possible. The mechanism exists because the underlying curves are equivalent enough to permit conversion. The caution exists because long-term signing keys and ephemeral key-exchange keys have different security roles.
Where is Curve25519 used in TLS, blockchains, and custody systems?
Once you see the mechanism, the adoption pattern becomes unsurprising. TLS 1.3 includes x25519 as a standard named group for ephemeral Diffie–Hellman, and includes ed25519 as a signature scheme. That pairing reflects the broader modern pattern: use Curve25519-family constructions for compact keys, high performance, and implementations that can be made regular and side-channel resistant.
In blockchain systems, the connection often appears through Ed25519 rather than X25519. Solana exposes an Ed25519 signature verification precompile because native verification is much faster than doing such work inside the general-purpose virtual machine. Cardano’s wallet standards use BIP32-Ed25519 for hierarchical deterministic key derivation rather than standard BIP32 over secp256k1-style assumptions. These are not “Curve25519 key exchange” deployments, but they are part of the same curve family and reflect the same engineering preferences.
A more application-level example appears in threshold signing and custody systems. When systems rely on multi-party cryptography or threshold signatures, the underlying design problem is similar to Curve25519’s original motivation: preserve strong cryptography while minimizing dangerous special cases and single points of failure. For decentralized settlement, Cube Exchange uses a 2-of-3 threshold signature scheme in which the user, Cube Exchange, and an independent Guardian Network each hold one key share; no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. That is not “Curve25519 itself,” but it is a good reminder that modern cryptographic engineering is as much about implementation shape and fault containment as about abstract hardness assumptions.
What implementation failures and side‑channel risks remain with Curve25519?
The clean algebra and ladder regularity of Curve25519 do not eliminate implementation attacks. They narrow some attack surfaces, but they do not erase them.
A good example is the documented microarchitectural attack against Libgcrypt’s Curve25519 ECDH implementation, disclosed as CVE-2017-0379. The attacked implementation already used the Montgomery ladder, branchless formulas, and constant-time swaps. The failure was lower down: field arithmetic leaked through cache-observable behavior. Researchers showed that chosen low-order inputs could interact with the ladder and non-constant-time field operations in a way that exposed the secret scalar.
That example is valuable because it punctures a common oversimplification. Constant-time cryptography is not achieved by selecting the right high-level algorithm and stopping there. If multiplication, reduction, memory access, or carry handling still depend on secret-influenced values in an observable way, the implementation may leak anyway. Curve25519 helps because it gives you a better starting structure. It does not exempt implementers from careful field-arithmetic design.
Input validation is another place where assumptions matter. In the X25519 setting, RFC 7748 deliberately allows broad input acceptance and leaves the all-zero-output check optional. In Ed25519-related code, point validation and subgroup checks continue to matter. Recent hardening work in libsodium tightened subgroup validation for Ed25519 points after cases where points outside the main subgroup could be mishandled in atypical use cases. The broader lesson is that small-subgroup structure is not a historical curiosity. It remains operationally relevant wherever code accepts externally supplied points.
Which parts of Curve25519 are mathematical fundamentals and which are protocol conventions?
It helps to separate the layers.
What is fundamental is the finite field modulo 2^255 - 19, the elliptic-curve group defined by the Curve25519 equation, the hardness assumption behind scalar multiplication, and the existence of a large prime-order subgroup with cofactor 8. Also fundamental is the fact that the Montgomery form supports an efficient ladder for scalar multiplication.
What is more conventional, though still very important, is how standards package that mathematics into APIs and byte strings: little-endian encodings, the base u-coordinate 9, scalar clamping rules, acceptance of non-canonical inputs, and protocol-level decisions about whether to reject all-zero outputs. Those conventions are not arbitrary, but they are choices at the interface between math and deployed software.
This distinction matters because people often ask whether Curve25519 and X25519 are “the same thing.” They are not. Curve25519 is the mathematical curve. X25519 is a standardized function over that curve with specific encodings and decoding rules. In the same way, Ed25519 is not the curve itself but a signature scheme built on an equivalent form of it.
Conclusion
Curve25519 is best understood as an elliptic curve chosen to make a hard cryptographic operation (scalar multiplication) both secure in principle and practical to implement well. Its prime field supports efficient arithmetic, its Montgomery form supports a regular ladder algorithm, and its standard descendants such as X25519 and Ed25519 turned those properties into widely deployed protocols.
The short version to remember tomorrow is this: Curve25519 won not because elliptic curves were new, but because it made good elliptic-curve cryptography easier to do correctly. That is why it sits underneath so much of modern secure communication.
What should you understand before using Curve25519 in wallets, transfers, or protocols?
Before using Curve25519-based keys or protocols, understand the concrete checks that reduce interoperability and security mistakes and follow a simple Cube Exchange workflow to move or trade assets safely. Start by confirming which curve form the protocol or counterparty expects (Ed25519 signatures vs. X25519 key-exchange), then fund and execute the transfer or trade on Cube using the matching key and encoding rules.
- Verify whether the destination or protocol requires Ed25519 signatures or X25519 key-exchange by checking the receiving service docs or address format.
- Fund your Cube Exchange account with fiat or a supported crypto transfer so you can trade or send the asset needed for the operation.
- If you will send to an external wallet, confirm the recipient’s accepted key format and encoding (e.g., Ed25519 vs. X25519 byte formats) and do not reuse a long‑term Ed25519 signing key for ephemeral X25519 exchanges.
- For any on‑chain or protocol interaction that depends on ECDH, prefer ephemeral X25519 keys and follow RFC‑style rules (clamped scalars, little‑endian 32‑byte encodings); if you rely on key conversion APIs, use documented conversion functions only.
- Review the transfer/trade details, check for protocol notes about small‑subgroup or all‑zero outputs, then submit the transfer or place the trade on Cube.
Frequently Asked Questions
The Montgomery ladder is a scalar‑multiplication algorithm that scans the scalar bits performing a fixed sequence of doublings and differential additions with a constant‑time conditional swap (cswap), so implementations avoid secret‑dependent branching. RFC 7748 specifies this ladder for X25519 and the article highlights it as the core reason Curve25519 supports regular, constant‑time implementations.
Clamping is the RFC‑specified masking of certain low and high bits of the 32‑byte scalar before use; it forces the scalar into a form that avoids edge cases related to the cofactor and ensures consistent interaction with the ladder. The article and RFC 7748 explain clamping as a deliberate decoding step to make implementations behave in a controlled, interoperable way.
Curve25519’s group has cofactor 8, so small‑order or twist inputs can cause X25519 to return the all‑zero output; RFC 7748 therefore notes an all‑zero check is allowed but leaves it optional (MAY). In practice, protocols that need stricter guarantees should require explicit checks and handling rather than relying on the RFC’s permissive default.
Conversions exist (e.g., libsodium documents APIs to convert Ed25519 seeds/keys to X25519), but using the same key pair for both signing and key‑exchange is discouraged: signing keys are usually long‑term while ECDH keys should be ephemeral, and conversion/format differences can produce unexpected results. The article describes the mathematical equivalence but practical cautions, and libsodium’s docs explicitly recommend distinct keys when possible.
No - using Curve25519/X25519 does not automatically make an implementation constant‑time; the article and subsequent disclosures show low‑level field arithmetic and memory‑access patterns can still leak secrets (e.g., the Libgcrypt Flush+Reload attack demonstrated leakage despite ladder and cswap). Implementers must ensure constant‑time behavior across field operations and memory access, not just at the high‑level algorithmic layer.
X25519 encodes inputs and outputs as fixed 32‑byte little‑endian strings and RFC 7748 mandates masking of the most‑significant bit on received u‑coordinates; these byte‑level conventions were standardized to reduce interop failures. The article emphasizes that encoding rules are part of the practical specification and mismatches at this boundary commonly cause incompatibilities.
Accepting or rejecting non‑canonical encodings, twist points, or performing different validation choices can produce observable differences between implementations, which the article and RFC 7748 warn can lead to fingerprinting or interop surprises. For robust interoperability, protocols should explicitly state which behaviors (e.g., acceptance of non‑canonical inputs, handling of small‑order points) they require rather than leaving them implicit.
The Flush+Reload attack on Libgcrypt (CVE‑2017‑0379) showed that an attacker with shared memory on the same host could observe cache effects from field‑arithmetic code and recover scalar bits; the attack exploited microarchitectural leakage below the ladder level. That disclosure demonstrates an implemented Montgomery‑ladder algorithm can still leak unless its field operations and memory patterns are hardened against such local side channels.
Ed25519 verification and related code paths need careful subgroup/point validation; RFC 8032 and real‑world library changes (e.g., libsodium hardening commits) show implementers have tightened checks to reject certain malformed or non‑main‑subgroup encodings. The article similarly flags that subgroup structure and validation remain operationally important even though the curve was designed for easier secure implementation.
Related reading