What Is an MPC Wallet?
Learn what an MPC wallet is, how threshold signing works, why it avoids single-key custody, and where MPC wallet security depends on design.
Introduction
MPC wallet usually sounds like a wallet category, but the real idea is deeper: it is a different way to hold signing authority. In a conventional wallet, one device, one file, or one hardware module ultimately possesses the private key needed to authorize a transaction. An MPC wallet tries to remove that concentration point. Instead of ever assembling the private key in one place, it spreads the signing capability across multiple parties and has them compute a valid signature together.
That matters because cryptocurrency custody is really key custody. If the relevant signing key is lost, access is usually lost; if someone unauthorized gets the key, they can often move the assets. Regulators describing crypto custody have emphasized exactly this point: control follows the cryptographic keys, and institutions providing custody must treat key protection as central to the service. From a first-principles view, MPC wallets exist because strong cryptography is not enough if the operational model still creates a single object whose theft or misuse is catastrophic.
The key insight is simple: you do not always need to reconstruct a secret in order to use it. Threshold cryptography combines secret sharing with secure multi-party computation so that participants can jointly generate keys and jointly sign, while the secret-sharing remains in place even during the computation. The blockchain still sees an ordinary signature under an ordinary public key. What changes is not the chain’s verification logic, but the way the signer side produces that signature.
What custody failures do MPC wallets prevent?
A standard wallet has a clean mental model: there is a private key, and whoever controls it controls the funds. That simplicity is useful, but it creates an uncomfortable invariant. No matter how carefully the key is stored, there is usually some moment or location where the full signing authority exists together. It might live in a browser wallet, a phone secure enclave, a hardware wallet, an HSM, or a backup phrase written on paper. Different implementations improve security, but the basic structure remains: compromise that one authority, and you compromise the wallet.
This creates two distinct failure modes. The first is theft: malware, insider abuse, server compromise, backup leakage, or supply-chain compromise can expose the key. The second is loss: damage to a device, loss of a seed phrase, or operational mistakes can render the key unavailable. Traditional controls such as backups, dual control, approval workflows, and cold storage help, but they often do so by adding layers around a single signing secret rather than changing the secret’s structure.
MPC wallets attack the problem at the cryptographic layer. Instead of saying “protect this one key better,” they say “arrange things so that no single party ever has enough information to sign alone.” NIST’s key-management guidance uses the language of split knowledge and key shares: a key can be divided into shares such that the shares individually reveal no knowledge of the key, while some threshold of shares can be used to reconstruct or operate with it. Threshold cryptography takes that further by arranging for the operation itself (in this case, digital signing) to happen without reconstructing the whole key.
This is why MPC wallets became attractive for both institutions and end-user products. Institutions want to remove single points of compromise across teams, devices, regions, or vendors. Consumer wallets want recovery and device flexibility without putting a single seed phrase at the center of everything. The common motive is not fashion; it is that concentrated signing authority is brittle.
What is an MPC wallet and how does it work?
| Concept | Local material | Signing outcome | Trust model | Typical use |
|---|---|---|---|---|
| Key sharding | Pieces of the private key | Requires reconstruction to sign | May depend on dealer | Simple split backups |
| Threshold signatures | Secret shares | Single standard signature | t‑of‑n threshold security | Custody without on‑chain multisig |
| Multi‑party computation | Shares + joint computation | Standard signature produced jointly | Dealerless DKG possible | User+service recovery; flexible ops |
At a high level, an MPC wallet is a wallet whose private signing capability is distributed across multiple participants. Those participants may be devices controlled by one person, separate services within one organization, independent custodians, or some combination. Each participant holds a share rather than the whole key. When it is time to authorize a transaction, a sufficient subset of participants cooperates to produce a signature.
The underlying cryptographic object is usually a threshold signature scheme. In the standard threshold definition, there are n players and a threshold parameter. Any authorized subgroup above the threshold can sign, while any smaller subgroup cannot. The important security property is not merely that the shares are stored separately, but that the signature protocol is designed so unauthorized subsets learn nothing that lets them sign by themselves.
This leads to an important distinction. People sometimes use “MPC wallet,” “threshold wallet,” “TSS wallet,” and “key-sharded wallet” almost interchangeably. They overlap, but they are not identical ideas. Key sharding refers to splitting secret material into shares. Threshold signatures are the signing schemes that let shares jointly produce a standard signature. Multi-party computation is the broader cryptographic framework for computing on secret inputs without revealing them. In practice, many wallets branded as MPC wallets are specifically using threshold signature protocols, often for ECDSA or Schnorr-family signatures.
The user-visible result is often surprisingly ordinary. A Bitcoin transaction signed via threshold ECDSA still produces an ECDSA signature that Bitcoin nodes verify in the usual way. A wallet using FROST over secp256k1 or P-256 still aims to output a normal Schnorr-style threshold-produced signature under the relevant public key. NIST’s threshold-cryptography work emphasizes this interchangeability: threshold outputs should verify under the same verification algorithm as conventional outputs. That property is why MPC wallets can fit into existing chains without requiring protocol changes.
How can a signing key exist without ever being reconstructed?
The conceptual move behind MPC wallets is easier to see if we separate two questions that are often blurred together. The first question is: what public key will the blockchain recognize? The second is: how do we arrange the hidden signing authority behind that public key? Conventional wallets answer both questions with one object: generate a private key, derive its public key, store the private key somewhere secure. MPC wallets answer them in two stages.
First, the parties jointly run a key generation process. In a strong design, this is dealerless: there is no trusted coordinator who creates the whole private key and then chops it up. Instead, the parties collectively generate shares such that the resulting group public key is well defined, while no one ever sees the full secret. This dealerless property matters because a trusted dealer would reintroduce the very concentration point the system is trying to avoid.
Second, each participant stores only its local share. That share is not a portable copy of the whole private key in miniature. By design, holding fewer than the threshold number of shares should provide no useful knowledge of the full key. When enough parties later participate in signing, they run an interactive protocol that transforms their local shares, randomness, and message-specific values into partial results, which can be combined into a valid final signature.
A useful analogy is a vault that opens only when enough independent combination wheels are aligned. The analogy helps explain why no single participant can open it. But it fails in an important way: in threshold cryptography, the secret is not physically reassembled in the middle of the room before use. The protocol is constructed so the parties compute the effect of using the key without exposing the key itself.
How does a 2-of-3 MPC signing flow work (example)?
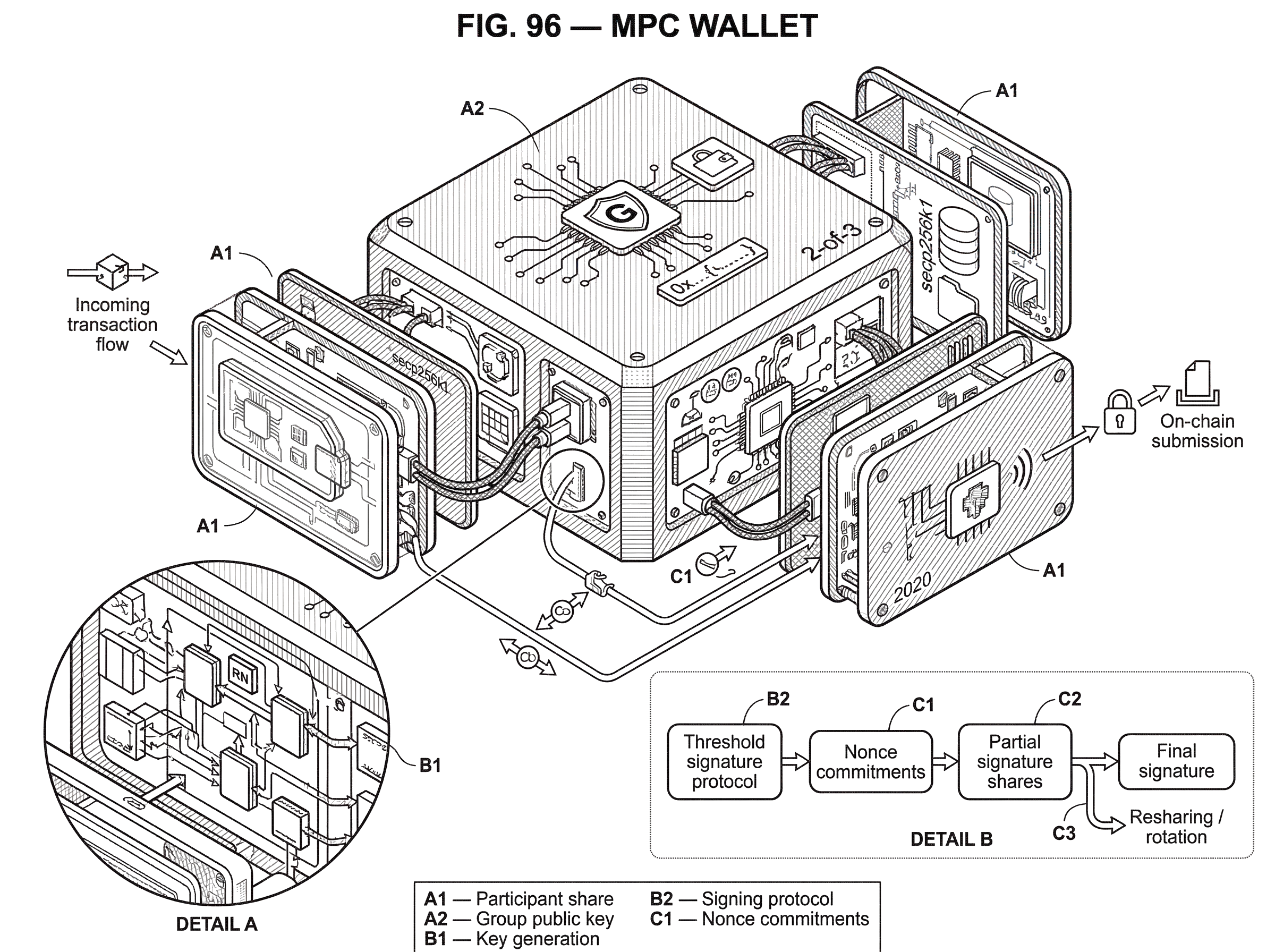
Imagine a treasury wallet controlled by three parties: a finance device, a security service, and a recovery service. The wallet is configured as 2-of-3. During setup, those three parties run distributed key generation and end with a single public address that can receive assets. Each party retains a local share. No one has a recoverable plaintext copy of the full signing key sitting in storage.
Now the treasury wants to send funds. The transaction details are prepared, and the finance device requests a signature. Under the policy, any two of the three parties can authorize. The finance device and the security service decide to sign.
What happens next depends on the signature scheme, but the pattern is the same. Each signer creates fresh secret randomness for this message and computes commitments or encrypted intermediate values. They exchange the required protocol messages over authenticated channels. Each party uses its own share, the message, and the session’s fresh randomness to compute a partial signing contribution. Those contributions are mathematically linked so that, when combined, they form a single valid signature under the wallet’s public key.
To the blockchain, nothing unusual has occurred. It sees one signature that verifies against one public key. It does not see that two parties participated, which two they were, or how the signing authority was distributed behind the scenes. This privacy is one reason threshold signatures are often compared favorably with on-chain multisig. In a threshold-signature wallet, the cooperation happens off-chain and the chain only verifies the final signature.
MPC vs multisig: which fits my use case?
| Feature | Multisig (on-chain) | MPC / Threshold | Best for |
|---|---|---|---|
| Visibility | Policy visible on‑chain | Single public key on‑chain | Regulatory audit |
| Verification cost | Multiple signatures / scripts | One ordinary signature | Fee / blockspace savings |
| Privacy | Signers revealed on‑chain | Signers hidden off‑chain | Privacy‑sensitive custody |
| Enforcement | Chain enforces policy | Off‑chain cryptographic enforcement | Flexible workflows |
MPC wallets and multisig solve a similar operational problem: they distribute control so one compromised component is not enough. But they do it at different layers.
In multisig, there are multiple independent private keys, and the blockchain script or account logic requires multiple signatures on-chain. The chain knows that several keys exist and enforces the policy directly. In MPC or threshold signing, the blockchain usually sees a single ordinary public key and a single ordinary signature. The access policy is enforced off-chain by the signing protocol.
That difference has consequences. Threshold signatures can preserve signer privacy because the chain does not learn which subset participated. They can also avoid chain-specific multisig machinery and the associated on-chain overhead, since nodes verify a normal signature rather than multiple signatures or custom script logic. This is one reason threshold signing is attractive across ecosystems that already expect standard ECDSA or Schnorr verification.
But the comparison should not be oversimplified. Multisig has the advantage of on-chain explicitness: the chain itself enforces the requirement for multiple signers. In MPC, that enforcement depends on the correctness of an off-chain cryptographic protocol and its implementation. So the tradeoff is not “modern versus old.” It is on-chain transparency and simplicity of verification versus off-chain privacy and flexibility with heavier cryptographic machinery.
Why is distributed signing harder than single-key signing?
| Property | Schnorr (FROST) | ECDSA (GG‑style) | Best for |
|---|---|---|---|
| Rounds | 2 rounds (often) | Multiple interactive rounds | Low‑latency Schnorr |
| Nonce handling | Cleaner, fewer pitfalls | Complex MtA / Paillier nonces | Where ECDSA compatibility needed |
| Auxiliary proofs | Simpler ZKPs typical | Extensive Paillier/ZK stack | High‑assurance ECDSA |
| Operational risk | Nonce errors critical | More protocol complexity | Mature ECDSA ecosystems |
The phrase “the private key is never assembled” can make MPC wallets sound almost magically safer. The reality is more technical. Digital signatures such as ECDSA and Schnorr are built from algebraic relations that were originally designed around a single signer holding a single secret scalar. Once several parties each hold only a share, the wallet must somehow reproduce the same algebraic end result without leaking the secret.
For some signature families, this is cleaner than for others. Schnorr-style signatures are structurally friendlier to threshold designs, which is why protocols such as FROST can achieve two-round signing. The FROST specification describes a two-round threshold Schnorr protocol over a prime-order group and warns that secure nonce handling is critical: in the multi-party setting, deterministic nonce derivation can enable complete key recovery. That warning reveals a broader truth about MPC wallets: once multiple parties share signing, coordination state like nonces becomes part of the security boundary.
ECDSA is more awkward. Practical threshold ECDSA protocols required substantial research progress because ECDSA’s signing equation involves multiplicative relationships that are hard to distribute securely. The Gennaro-Goldfeder line of work was important because it presented fast multiparty threshold ECDSA with efficient dealerless setup for arbitrary thresholds and security against malicious adversaries even with a dishonest majority. Later work pushed further on efficiency and operations, including protocols with a non-interactive asynchronous online phase and identifiable abort, meaning the system can tell which participant caused a malicious failure instead of merely observing that signing failed.
That operational detail matters more than it first appears. In a custody system, “the protocol aborted” is not enough. Someone needs to know whether the network dropped packets, a device is offline, or a participant actively misbehaved. Identifiable abort turns a cryptographic failure into something an operational process can react to.
How do nonce mistakes and missing proofs compromise MPC wallets?
The hardest thing to explain about MPC wallets is that the theory can be sound while real deployments are still fragile. The reason is that threshold signing protocols are not just “split the key and do some math.” They rely on a dense web of auxiliary components: nonce generation, commitments, zero-knowledge proofs, Paillier-based subprotocols in many ECDSA designs, transcript encoding rules, message transport, participant authentication, and final verification checks.
If any of those parts are weakened, the system may lose the very property it was adopted for. This is not hypothetical. Researchers have documented practical key-extraction attacks against leading threshold-ECDSA wallet implementations and vendors, with outcomes including denial of service, signature forgery, and private-key exfiltration. Other analyses have shown how omitting range proofs or mishandling the Paillier-based multiplication-to-addition subprotocol in GG18-style designs can leak secret information. The common theme is sobering: an MPC wallet can fail not by reconstructing the key outright, but by leaking it gradually through malformed protocol interactions.
A particularly important lesson is that zero-knowledge proofs and well-formedness checks are not decorative. They are there to stop one party from sending cleverly malformed values that still pass superficial checks but bias the protocol in a way that reveals another party’s secret share or nonce information. The NIST workshop material on attacks against threshold ECDSA wallets explicitly calls for more standardization of these associated proofs and checks, especially around Paillier well-formedness and range proofs.
Implementation details that seem mundane can also be fatal. Ambiguous transcript encoding, missing message hashing at the integration layer, omitted final verification steps, insufficient validation of cryptographic parameters, side channels, insecure demo transports, or “performance optimizations” that silently weaken proofs have all appeared in real codebases. This is why a secure paper alone is not enough, and why an audited library alone is not enough. The attack surface includes the protocol, the implementation, the transport, and the operational environment.
How does MPC change key management and lifecycle operations?
It is tempting to think of an MPC wallet as just a signing protocol. In practice, it is a key-management architecture. Once the signing key is split into shares, each share has its own lifecycle: generation, storage, backup, activation, suspension, rotation, recovery, compromise handling, and destruction. NIST’s key-management guidance is helpful here because it reminds us that strong algorithms do not rescue poor lifecycle management.
For example, a share stored on a phone, a share held by a server-side co-signer, and a share reserved for recovery do not face identical threats. They may need different hardware protections, different authentication policies, different cryptoperiods, and different incident-response procedures. If one share is suspected compromised, the right response is not necessarily “the wallet is instantly dead,” but neither is it “nothing happened.” The system needs a way to reshare, rotate, suspend, or migrate signing authority safely.
This is why many threshold-signing libraries include not just key generation and signing, but also resharing or dynamic group management. Resharing changes the group of participants while keeping the underlying secret protected, allowing organizations to replace devices, rotate operators, or change custody structures without moving funds immediately. Done correctly, this is one of the strongest operational benefits of MPC wallets. Done poorly, it becomes another delicate protocol stage that must be secured.
What security and liveness assumptions do MPC wallets require?
An MPC wallet does not eliminate trust; it rearranges it. The security claim is always conditional on assumptions.
One assumption is the threshold itself: if the scheme is t-of-n, then security depends on no attacker controlling enough participants to meet the threshold. Another is that participants follow the protocol, or that the protocol remains secure even when some behave maliciously. Another is that local devices protect their shares adequately. Another is that the communication channels are authenticated and confidential enough for the protocol’s requirements. Open-source implementations frequently emphasize that the application must supply secure broadcast and point-to-point transport; without that, the cryptography does not sit on solid ground.
There are also liveness assumptions. Some protocols are efficient but not robust: a misbehaving participant can cause denial of service by refusing to complete or by contributing invalid values. FROST, for example, explicitly does not provide robustness and notes that all participants must complete honestly to generate a valid signature, even though invalid shares can be detected. In operational terms, that means the cryptography can tell you who misbehaved in some cases, but it cannot force progress.
So the right question is not “Is MPC safer?” in the abstract. It is: safer against which failures, under which adversary model, with which implementation discipline? MPC wallets reduce the single-key failure mode. They do not remove compromise risk, implementation bugs, insider threats, or operational outages.
When should organizations choose MPC wallets in production?
Once the mechanics are clear, the practical uses follow naturally. Institutions use MPC wallets to distribute approval authority across teams, regions, and security domains without exposing an on-chain multisig footprint. Exchanges and custodians use them to enforce workflow policies while keeping the resulting assets under addresses that look like standard single-key accounts. Wallet providers use them to split authority between a user device and service-assisted recovery infrastructure, aiming to improve recoverability without returning to a seed phrase that must be perfectly protected forever.
The design is not tied to a single chain. Threshold ECDSA is relevant wherever chains or assets rely on ECDSA-style signatures, while FROST and related threshold Schnorr constructions fit environments using Schnorr-family signatures or prime-order-group abstractions. Specifications and implementations now exist across common ciphersuites including P-256, secp256k1, Ed25519, and others. The unifying requirement is that the threshold-produced signature remains compatible with the chain’s ordinary verifier.
That said, “MPC wallet” should not be read as a guarantee of quality. Some products use the term for robust threshold-signing systems with dealerless key generation, audited code, and carefully designed operations. Others may use it more loosely for architectures that merely split duties around a service-controlled key. The only reliable way to evaluate an MPC wallet is to ask what protocol it uses, what threshold and trust assumptions it makes, how key generation works, how misbehavior is handled, how shares are protected, and how the implementation has been reviewed.
Conclusion
An MPC wallet is best understood not as a new kind of blockchain account, but as a new way to hold and exercise signing power. It replaces the idea of “there exists one private key somewhere” with “there exists a distributed capability to sign, and no single participant possesses it alone.”
That shift solves a real problem: single-key custody is a natural single point of failure. But it replaces simplicity with protocol complexity. The promise of MPC wallets is strongest when the threshold design, nonce handling, proofs, transport, and lifecycle operations are all treated as part of one security system. The short version to remember is this: an MPC wallet makes key control safer by making it shared; but only if the sharing protocol itself is engineered and operated with the same care as the key it is replacing.
How to use an MPC wallet model more safely when trading
Use an MPC wallet model more safely when trading by combining strong account authentication, network and asset verification, and cautious test orders before scaling up. On Cube, follow a simple trade-first workflow: secure your account, fund it on the correct network, run a small verification trade, then execute the full order with explicit order-type and protection choices.
- Enable strong authentication on your Cube account (set up MFA with a hardware key or TOTP and register approved devices).
- Verify the asset and network before funding: confirm the token contract/address and choose the exact blockchain network in Cube’s deposit flow.
- Fund your account with a small on-chain transfer or fiat on-ramp, then place a small test buy using a limit order to check routing, estimated fees, and settlement.
- After the test trade confirms, place your main order: pick limit for price control or market for immediacy, set size and slippage limits, review estimated fees, and submit.
Frequently Asked Questions
An MPC wallet distributes signing power across multiple participants so no single party ever holds the full private key; threshold signing protocols let those parties jointly produce an ordinary blockchain signature that verifies with the chain’s usual verification algorithm. This contrasts with on-chain multisig, where multiple independent keys and on-chain logic explicitly require multiple signatures and the chain knows about each signer.
No - the key is not reconstructed in a single place during normal operation; parties run dealerless distributed key generation to produce a group public key and then run an interactive threshold-signing protocol that produces a valid signature without assembling the plaintext private key. This is the core idea behind threshold cryptography and MPC wallets.
No - MPC reduces a single-point-of-failure but does not eliminate trust or all risks: security depends on the threshold t-of-n, correct protocol behavior (or malicious‑secure variants), local protection of shares, and authenticated/confidential transport; implementations and operational practices therefore remain critical.
Nonce generation and handling are critical because multi-party signing turns nonces and other per-session randomness into part of the security boundary; flawed or deterministic nonce handling can allow full key recovery, and FROST explicitly warns that nonce mistakes can be catastrophic in multi-party settings.
Some signature families (Schnorr-style) are structurally friendlier to threshold constructions (enabling protocols like FROST), while ECDSA required substantial additional research and more complex subprotocols (e.g., Paillier‑based multiplication-to-addition, GG18/GG20 lines) to achieve secure, dealerless threshold signing.
No - real-world attacks and analyses have shown that implementation weaknesses (missing zero-knowledge proofs, malformed transcript encodings, weak Paillier checks, or transport/encoding bugs) can leak key material gradually or enable forgery, denial-of-service, or private‑key exfiltration; several PoCs and publications document such failures.
Treat an MPC wallet as a key‑management system: each share has its own lifecycle (generation, backup, rotation, suspension, reshare, destruction), and secure deployments provide resharing and dynamic group management so participants can be replaced or keys rotated without moving funds. Proper lifecycle controls are as important as the signing protocol itself.
Because threshold signatures usually produce a standard on‑chain signature under a single public key, MPC wallets can be used without changing blockchain verification logic, making them compatible with chains that expect ECDSA or Schnorr‑style signatures; the challenge is ensuring the threshold-produced signature conforms to the chain’s expected encoding and verification rules.
Standardization and guidance work is underway but not finished: NIST’s threshold-cryptography project (MPTC) and documents like the FROST RFC and NIST key-management guidance provide useful practices, but there is not yet a single binding standard or validation program covering all threshold schemes and implementations.
When evaluating an MPC wallet product, ask which threshold/signature protocol it uses, whether key generation is dealerless, the threshold and adversary model, how nonce and proof checks are enforced, how misbehavior and aborts are handled, what resharing/recovery options exist, and what audits or tests cover transport and implementation details - these were highlighted as the critical evaluation points in the literature and guidance.
Related reading