What is an Airdrop?
Learn what crypto airdrops are, how token and NFT airdrops work, why projects use them, and the key tradeoffs around claims, standards, incentives, and scams.
Introduction
Airdrops are a way to distribute crypto tokens or NFTs to many recipients, often at low or zero direct cost to those recipients. The idea sounds almost trivial (send assets to wallets, attract attention, reward users, spread ownership) but the interesting part is that giving assets away is not the same thing as creating a healthy network. An airdrop is really a coordination tool: it tries to turn a token supply into users, governance participants, liquidity, loyalty, or publicity. Whether it works depends less on the slogan of “free tokens” than on the mechanism used to decide who gets what, when, and under what conditions.
That is why airdrops sit at the intersection of token standards, wallet mechanics, incentive design, and security. A fungible token airdrop on Ethereum inherits the behavior of ERC-20 transfers and events. An NFT airdrop inherits the stricter delivery semantics of ERC-721, including the problem of sending tokens to contracts that may reject them. On Solana, a distributor may need to create and fund the recipient’s associated token account before the recipient can receive anything at all. On Substrate-based chains, asset roles and privileged minting matter. The phrase airdrop names the outcome, but the actual mechanism is chain-specific.
The central question is simple: what problem is the airdrop trying to solve? If the goal is just to put tokens into many wallets, the mechanism is easy. If the goal is to reward meaningful participation, decentralize governance, avoid Sybil abuse, limit costs, and keep users engaged after claiming, the problem becomes much harder. That gap between apparent simplicity and real difficulty is the reason airdrops deserve careful explanation.
Why do projects airdrop tokens instead of selling them?
Every token project has to answer a supply question: who should own the asset? A market-based answer is to sell it. An administrative answer is to allocate it internally. An airdrop is a different answer: distribute some supply to a set of addresses according to eligibility rules chosen by the project.
What makes this attractive is straightforward. Early in a network’s life, the project may want users, not just buyers. It may want governance to start with a wider base of holders. It may want to reward people who used the protocol before a token existed. It may want attention, because wallets, social feeds, and block explorers make token receipt visible. In that sense, an airdrop is a way to spend supply instead of cash. Rather than buying user acquisition with dollars, the project uses tokens it can mint or reserve.
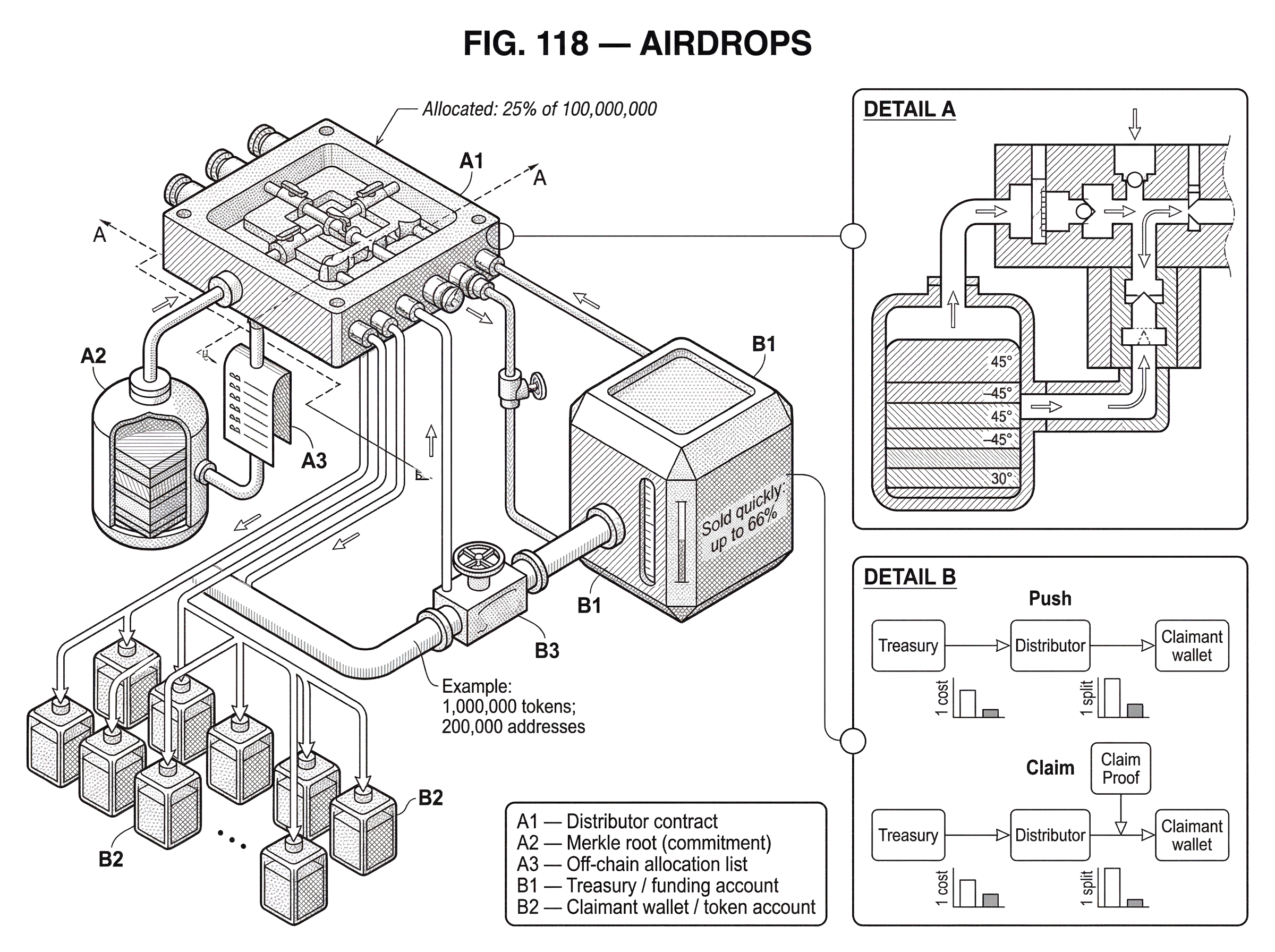
But this immediately creates a tension. If the tokens are valuable, recipients may just sell them. Research on major Ethereum and Layer-2 airdrops found that a substantial share of tokens (in some cases up to 66%) were sold quickly, often in the first post-claim transaction. That does not mean airdrops never work. It means their effect is not “free community.” The token leaves the treasury and enters the market, and recipients respond to incentives, not the project’s narrative.
So the key distinction is this: an airdrop distributes ownership, but it does not by itself create commitment. That is the idea that makes the topic click. If a project wants commitment, it must build it into eligibility, vesting, governance rights, or product value. Otherwise the airdrop is mostly a transfer of value from issuer to claimant.
What types of assets are distributed in airdrops (ERC‑20, ERC‑721, SPL)?
The word airdrop is used for several related but mechanically different actions. Sometimes the issuer sends fungible tokens directly to wallets. Sometimes users must claim them through a contract. Sometimes the distribution is an NFT rather than a fungible token. Sometimes the “airdrop” is really an eligibility right that becomes valuable only if the recipient chooses to act.
For fungible tokens on Ethereum-like chains, the usual baseline is an ERC-20 token. ERC-20 defines the standard interface for token balances and transfers. The practical consequence is that airdropped tokens can be handled by wallets, indexers, and exchanges using common methods such as transfer, balanceOf, and approve. ERC-20 also matters for observability: transfers must emit a Transfer event, and token creation should emit a Transfer event from 0x0. Indexers and wallet interfaces often detect distributions through these events.
That point is easy to overlook. An airdrop is not just a bookkeeping decision inside a contract. It is also an event stream that outside tools interpret. If the token follows standard behavior, recipients can see it, explorers can track it, and tooling can reconcile the distribution. If not, the airdrop becomes harder to discover and harder to trust.
For NFTs, ERC-721 changes the story because each token is unique. The unit being dropped is not an interchangeable balance but a specific tokenId, and the pair of contract address plus tokenId uniquely identifies the asset. Transfer behavior matters more here because sending an NFT to a smart contract can fail unless the recipient implements the receiver interface for safe transfers. In other words, NFT airdrops are not just “ERC-20 airdrops with pictures.” The delivery constraints are stricter.
Outside the EVM world, the object being dropped may still be “a token,” but the account model changes the mechanics. On Solana, a wallet does not simply receive every token into one universal balance slot. SPL tokens are held in token accounts, and the conventional receiving account is the associated token account for that mint and wallet. If that account does not exist, an airdrop campaign often creates and funds it on the user’s behalf, then transfers the tokens in the same transaction. That extra step matters operationally because it costs SOL for rent and fees.
Push vs claim airdrops; which delivery model should a project use?
| Model | Recipient effort | Issuer cost | Treasury control | Common risk |
|---|---|---|---|---|
| Push | No claim needed | High per-recipient cost | Low reclaimability | Incompatible recipients |
| Claim | User must claim | Low upfront cost | High reclaimability | Low claim uptake |
Most airdrops reduce to two delivery models because the core design choice is where the work happens.
In a push airdrop, the distributor sends assets directly to recipients. If there are 100,000 recipients, the distributor initiates the transfers, or batches of transfers, needed to populate those wallets or token accounts. This is conceptually simple. The project controls timing, the recipient does not need to visit a website to claim, and the distribution is complete once the transfers settle.
The weakness of the push model is cost and compatibility. Sending to many addresses is operationally expensive. Some recipients may be contracts that cannot safely receive the asset. On chains with per-recipient account setup, such as Solana, the distributor may also need to create accounts first. And if the eligibility list changes or contains mistakes, correcting a direct push can be cumbersome or impossible.
In a claim airdrop, the distributor publishes the allocation logic or a compact commitment to it, and each eligible user claims their own allocation later. This shifts gas, fees, and timing to the claimant. It also lets the project publish a large recipient set without paying the full cost of delivering to every address up front. Unclaimed tokens can remain under treasury control or be swept back after a deadline.
The ENS token distribution is a good illustration of this logic. ENS allocated 25% of its 100 million token supply to an airdrop for past .eth registrants, opened a claim window, and later transferred unclaimed tokens back to the DAO treasury when the window closed. Mechanically, that is not just generosity. It is a way to define eligibility, allow opt-in claiming, and avoid permanent allocation to inactive recipients.
Once you see the push-versus-claim distinction, many design choices become clearer. Push optimizes convenience for recipients. Claim optimizes scalability and treasury control for issuers.
How do Merkle proofs make claim-based airdrops cheaper on-chain?
Claim systems need a way to prove eligibility cheaply on-chain. If the contract stored every recipient and every allocation directly in contract storage, deployment and execution costs would be high. The common solution is a Merkle tree.
The intuition is simple. Start with a list of eligible claims such as (address, amount). hash each entry into a leaf. Repeatedly hash pairs of leaves upward until only one hash remains: the Merkle root. That root is a compact fingerprint of the entire allocation table. The contract stores only the root. When a user claims, they submit their allocation and a Merkle proof; the sibling hashes needed to reconstruct the path from their leaf to the root. If recomputing that path yields the stored root, the contract accepts that the user’s claim was part of the original list.
This matters because the on-chain contract now stores one root instead of a huge mapping of recipients. The cost of proving membership moves partly off-chain, where generating the tree is cheap. On-chain, the contract verifies only the proof.
A concrete example helps. Imagine a project wants to distribute 1,000,000 tokens across 200,000 addresses. Instead of deploying a contract with 200,000 storage slots for entitlements, it generates an off-chain table of allocations, builds a Merkle tree over those entries, and deploys a distributor contract containing the token address, the Merkle root, and claim-tracking state. When Alice claims 500 tokens, she sends the tuple describing her entitlement plus the branch of hashes connecting her leaf to the root. The contract checks the proof, checks that Alice has not claimed before, marks her as claimed, and transfers 500 tokens. The mechanism works because changing Alice’s amount, or inserting a fake claimant, would alter the root. The root acts as a cryptographic commitment to the entire distribution list.
This pattern is common enough that there are well-known implementations built around it. Uniswap’s merkle-distributor is exactly described as a smart contract that distributes a balance of tokens according to a Merkle root. Sablier’s airdrop contracts use the same high-level idea for ERC-20 distributions, including not only instant claims but also vesting-based variants.
Merkle proofs are powerful, but the details matter. OpenZeppelin’s utilities warn against unsafe leaf constructions, including 64-byte leaf values before hashing under common assumptions, because internal node concatenations can be confused with leaf data in poorly designed trees. That is a reminder that “Merkle drop” is not a magic phrase. The security comes from the exact encoding, hashing, and proof rules.
What additional checks does a secure airdrop claim flow require?
A secure claim flow has to do more than verify a proof. It must also transfer the asset correctly, prevent double-claims, and handle wallet reality.
On Ethereum, if the contract transfers an ERC-20 token, it must not blindly assume every token behaves perfectly. ERC-20 explicitly says callers must handle false returns from functions that return bool. A distribution contract or script that ignores return values may believe it paid users when the transfer actually failed. That sounds like a narrow implementation detail, but it changes whether the airdrop is real or only logged as real.
Some claim systems also use signatures rather than, or in addition to, Merkle proofs. In that model, an authorized signer attests off-chain that a claimant may receive a certain amount, and the contract verifies the signature on-chain. If this route is used, signature verification must be done carefully. OpenZeppelin’s utilities emphasize that ECDSA verification should use properly hashed messages, and SignatureChecker exists to support both externally owned accounts and contract wallets via ERC-1271. That matters because airdrops increasingly interact with smart contract wallets, not just single private keys.
NFT claims add another layer. If the claim contract mints the NFT to the claimant, then minting logic is contract-specific because ERC-721 does not standardize minting itself, even though transfers and Transfer events are standardized. If the contract transfers an already minted NFT, safeTransferFrom can revert when the recipient contract does not implement onERC721Received. So the issuer has to choose between stricter safety and broader compatibility.
On Solana, the same issue appears in a different form. A recipient may not yet have an associated token account for the mint being distributed. The standard SPL token documentation explicitly describes an airdrop campaign pattern where the sender creates that associated token account on the recipient’s behalf and then performs the transfer in the same transaction. The mechanism is elegant, but not free: the distributor pays SOL for rent-exemption and transaction fees.
How should airdrop eligibility and incentives be designed to avoid farming and Sybil attacks?
The transfer mechanism explains how an airdrop happens. Incentive design explains whether it achieves its purpose.
Most projects claim some mix of three goals: reward early users, decentralize ownership, and bootstrap community. Those goals can conflict. If the eligibility rules are too broad, mercenary claimants dominate. If they are too narrow, the distribution looks arbitrary or insider-favoring. If the token is immediately liquid and valuable, recipients have a strong incentive to sell. If it is locked too aggressively, the airdrop may feel illusory.
The ENS airdrop is useful here because its eligibility rules tried to encode a theory of contribution. Allocation depended on the time an address had held .eth registrations, future registration time up to a cap, and whether the address had set a primary ENS name, which received a multiplier. That is not random generosity. It is a scoring system intended to reward past commitment and a stronger form of usage. Whether any particular formula is ideal is debatable, but the deeper point is that every airdrop contains an implicit theory of what counts as valuable participation.
This is exactly where “airdrop farmers” appear. If users believe a future token distribution will reward some measurable behavior, they can optimize that behavior without sharing the project’s long-term goals. The empirical work on major airdrops argues that much rapid selling is driven by such actors. So airdrop design is partly an adversarial problem: you are writing rules in a public environment where strategic agents can prepare for them.
What breaks if assumptions change? If you assume each address corresponds to one genuine community member, Sybil attacks break the model. If you assume claimants value governance, liquid markets may reveal that they value immediate cash more. If you assume short-term activity means adoption, post-airdrop usage decay may prove otherwise. Airdrops fail when the proxy being measured is easier to game than the underlying behavior the project wanted.
How does vesting affect recipient behavior after an airdrop?
| Option | Liquidity timing | Recipient incentive | Treasury control | Main drawback |
|---|---|---|---|---|
| Immediate | Fully liquid at claim | High sell incentive | Low | Rapid sell pressure |
| Vesting/streaming | Unlocks gradually | Encourages retention | Medium | May not ensure engagement |
| Variable Claim Amount | Partial unlocks; forfeiture | Rewards waiting claimants | High | More complex UX |
A common response to immediate sell pressure is to add vesting. Instead of giving the recipient fully liquid tokens at claim time, the project releases them over time.
This can help, but it is important to be precise about why. Vesting does not automatically create alignment. What it does is change the claimant’s payoff curve. The recipient now has to stay engaged, or at least wait, to receive the full allocation. That can reduce immediate circulating supply and slow sell pressure. It can also give the project more time to turn recipients into actual users.
Sablier’s airdrop contracts make this explicit. They support instant airdrops, vesting airdrops in which claimed tokens are streamed over time, and variable claim amount designs in which unvested tokens are forfeited back to the campaign creator when the user claims early. These are all ways of changing the timing function attached to the same base idea: a recipient has some entitlement, but the contract determines when that entitlement becomes liquid.
The analogy here is an employment offer with stock vesting. It helps explain timing as incentive. But the analogy fails in an important place: blockchain claimants usually have much weaker obligations than employees. They can still claim, sell whatever is unlocked, and disengage. So vesting is a lever, not a solution.
Which token standards and chain rules affect how airdrops are executed?
| Standard | Delivery constraint | Discovery signal | Account setup cost | Typical issue |
|---|---|---|---|---|
| ERC-20 | Simple transfer semantics | Transfer events | Low | Approve/return-value pitfalls |
| ERC-721 (NFT) | Safe transfer may revert | Transfer + tokenId | Low | Recipient contracts can reject |
| SPL (Solana) | Associated token account required | Token-account records | Medium (SOL rent) | Must create token accounts |
| Substrate Assets | Role-based minting/privileges | Runtime asset events | Varies by chain | Privileged reversals possible |
It is tempting to speak about airdrops as if they were purely marketing. Mechanically, they are deeply shaped by token standards.
ERC-20 determines how fungible tokens are transferred, how wallets inspect balances, and how indexers detect token movement through Transfer events. It also defines approve and allowances, which can matter if a claim or helper contract pulls tokens from a funding account. The standard warns about allowance race conditions and notes that callers must handle false returns. Those sound like implementation footnotes until a poorly written distributor loses funds or silently fails to pay claimants.
ERC-721 determines uniqueness and safe transfer semantics for NFTs. Because the token is identified by (contract address, tokenId), each airdropped NFT is an individual asset. Optional metadata functions such as tokenURI improve discoverability, but they are not guaranteed. Safe transfers to contracts require the receiver hook. So a project that wants NFT airdrops to “just work” across wallets, marketplaces, and custody contracts has to respect those rules.
On Solana, the associated token account convention changes what “send tokens to a wallet” means. Anyone can create and fund a user’s associated token account, which is exactly what enables third-party-funded airdrop campaigns. But because account creation consumes SOL, distribution cost includes more than the token itself.
On Substrate chains using pallet_assets, the story includes roles such as Issuer, Admin, and Freezer. Minting, burning, force transfers, freezing, and approvals are explicit privileged operations. That means an airdrop is not just a token movement plan; it is also a governance and authorization plan. Who is allowed to mint? Who can reverse or freeze balances later? Those powers affect how recipients interpret the value of the asset they just received.
How do airdrop scams work and what steps stop common phishing lures?
There is a second reason airdrops are confusing for newcomers: the word refers both to a legitimate distribution mechanism and to a common scam lure.
The reason scams use airdrop language is obvious once you see the psychology. Airdrops promise free value and urgency. Attackers imitate that promise, then ask users to connect wallets or sign transactions to “claim.” Chainalysis documented fake airdrop lures used by crypto drainers, including cases where users were prompted to connect wallets to claim fake tokens. In that attack pattern, the airdrop is not the asset being delivered. It is the bait used to obtain approvals, signatures, or wallet interactions that let the attacker steal funds.
This is why airdrop safety is not only about contract correctness. It is also about user-interface trust boundaries. A real claim page may ask the user to submit a transaction that calls a distributor contract. A fake one may ask for approvals or signatures unrelated to the supposed claim. To a user, both can look similar. Generative AI makes that worse by lowering the cost of producing convincing fake websites, branding, and social accounts.
There is no purely technical way to remove that risk, because the scam often happens before the chain sees anything suspicious. The best defense is a combination of verified sources, careful transaction review, and healthy skepticism about “free” opportunities that require broad wallet permissions.
When is an airdrop the right tool to bootstrap users, governance, or liquidity?
Given the cost, gaming, and scam risk, why do projects keep using airdrops? Because they solve a real problem that few alternatives solve as cleanly.
A sale raises money, but it concentrates ownership among buyers. Liquidity mining rewards capital provision, but often over-rewards mercenary liquidity. Retroactive grants require subjective judgment and administrative overhead. An airdrop can say: this protocol already has users, and we want some ownership to begin with them. That is a meaningful political and economic statement, especially for governance tokens.
It also creates visibility. Tokens appearing in wallets are socially legible in a way abstract promises are not. Airdrops can therefore compress several goals into one event: recognition of prior users, circulation of a new asset, marketing, and the first step toward governance decentralization.
The mistake is to think that this makes them easy. The distribution event is the visible part. Underneath it sit token-standard semantics, proof systems, wallet compatibility, treasury budgeting, recipient account creation, adversarial eligibility design, and post-claim market behavior.
Conclusion
An airdrop is best understood as a token distribution mechanism that tries to trade supply for adoption, legitimacy, or decentralization. The transfer itself is the easy part. The hard part is deciding who should receive assets, proving that cheaply and safely, and shaping incentives so that distribution becomes more than immediate sell pressure.
If you remember one thing, remember this: an airdrop puts tokens into wallets, but only good design gives those tokens a reason to stay connected to the network that issued them.
How do you evaluate a token before using or buying it?
To evaluate a token before buying or approving it, check the token contract, tokenomics (supply, vesting, allocation), and the delivery or claim mechanics described by the issuer. Use Cube Exchange to inspect the token’s market and then complete the trade or approval flow on Cube once you’ve verified these details.
- Look up the token contract on a block explorer and confirm the exact contract address and token standard (ERC‑20, ERC‑721, SPL, etc.).
- Inspect on‑chain history: review Transfer events, holder concentration, and any on‑chain vesting or timelock contracts referenced in the token or distributor contracts.
- If the token originated from an airdrop or claim, open the issuer’s claim contract on the explorer and verify Merkle root/signature scheme, claim window, and whether unclaimed tokens were swept back to the treasury.
- Fund your Cube account with fiat or a supported crypto transfer, then open the token’s market on Cube to view orderbook liquidity and recent fills (use a limit order if liquidity is thin).
- When approving a spender from Cube or in-wallet, set a minimal allowance, use a single‑use or tight allowance if available, and recheck the exact contract address shown in the approval transaction before submitting.
Frequently Asked Questions
In a push airdrop the distributor sends tokens directly to recipients, which is simple for users but expensive and fragile (e.g., sending to contracts that can’t receive the asset); in a claim airdrop the issuer publishes an allocation commitment and eligible users submit on-chain claims, which shifts gas and compatibility work to claimants and lets the issuer keep or reclaim unclaimed tokens (ENS reclaimed unclaimed tokens after the window closed).
Merkle trees let a contract store a single compact root instead of a huge on-chain mapping; claimants submit a Merkle proof that their (address,amount) leaf is in the committed tree, so verification on-chain is cheap while the full allocation table is kept off-chain, though careful leaf encoding and hashing are required to avoid security mistakes.
NFT airdrops are more fragile because each token is a distinct (contract, tokenId) pair, ERC‑721 minting is not standardized, and safe transfers can revert if the recipient is a contract that does not implement the ERC721 receiver hook, so senders must choose between stricter safety and broader compatibility.
On Solana you usually must create and fund an associated token account before a wallet can hold an SPL token, so distributors commonly create and rent-exempt those accounts and pay the SOL rent/fee cost in addition to the token transfer, which raises operational cost compared with a simple balance transfer on account-model chains.
Vesting changes recipients’ payoff timing and can reduce immediate sell pressure by making tokens unlock over time, but it does not by itself align recipients’ incentives with the project - the article and Sablier examples stress that vesting is a lever that makes selling less immediate, not a guaranteed solution for long-term engagement.
Scammers impersonate airdrops to trick users into connecting wallets or signing transactions that grant approvals or move assets; the recommended defenses are to rely on verified official sources, carefully inspect the exact transactions and approvals requested, and be skeptical of unsolicited ‘claim’ pages, especially as AI lowers the cost of convincing fakes.
Common implementation pitfalls include assuming ERC‑20 transfers always succeed (contracts must handle tokens that return false) and misusing the approve/allowance pattern without the recommended UI patterns to avoid race conditions; these details can cause distributions to fail silently or behave unexpectedly if ignored.
Merkle proofs prove membership in an allocation list cheaply, but they do not prevent Sybil attacks or gaming of the eligibility metric; airdrop design must address adversarial behavior and choose eligibility rules and anti‑Sybil measures because empirical studies show significant rapid sell‑off and farming in many major airdrops.
Claim-based campaigns typically leave unclaimed allocations under treasury control or explicitly sweep them back after a deadline; ENS, for example, returned unclaimed tokens to the DAO treasury when its claim window closed.
To support contract wallets you must use verification approaches that handle ERC‑1271 (contract signatures) rather than only EOAs; OpenZeppelin supplies utilities like SignatureChecker to validate both EOA signatures and ERC‑1271 contract wallets so claims work across wallet types.
Related reading