What is DAO Treasury Management?
Learn what DAO treasury management is, how treasuries are controlled on-chain, why timelocks and multisigs matter, and where the main risks lie.
Introduction
DAO treasury management is the practice of deciding how a decentralized organization holds, deploys, protects, and spends its assets. That sounds straightforward until you notice the tension at the center of every DAO: the treasury is supposed to belong to the community, but blockchains require specific keys, contracts, and execution paths to move funds. The real problem is not just what assets to buy or how much to spend. It is how to turn collective intent into controlled on-chain action without making the treasury either unusably slow or dangerously easy to drain.
That tension explains why DAO treasury management sits at the intersection of finance, governance, and security. A treasury is not merely a balance sheet. In DeFi, it is often the operating runway, the grants budget, the market backstop, the source of protocol incentives, and sometimes the last line of defense in a crisis. If the treasury is badly structured, even a DAO with a good product and active community can be forced into reactive token sales, governance fights, or irreversible losses.
The useful way to think about this topic is simple: a DAO treasury is a system for controlled optionality. It exists to preserve the DAO’s ability to act later. That means surviving downturns, funding work, meeting commitments, and responding to emergencies without depending on a single founder, signer, or lucky market cycle. Once that idea is clear, the mechanics of multisigs, timelocks, modules, budget policies, and diversification all make more sense: they are not separate tools so much as different ways of protecting the DAO’s future choices.
How does a DAO separate custody, authority, and policy for its treasury?
| Model | Custody | Latency | Best for | Main risk | Example |
|---|---|---|---|---|---|
| Governance + Timelock | Timelock contract | Days to execute | Major protocol changes | Slow in crises | OpenZeppelin Governor + Timelock |
| Safe + Modules | Programmable Safe | Minutes to hours | Routine ops with constraints | Module bugs or config errors | Gnosis Safe + Zodiac |
| Multisig | Signer‑held wallet | Minutes | Early‑stage speed and agility | Key compromise | Squads / on‑chain multisig |
A newcomer might imagine a DAO treasury as a shared wallet with many signers. That is part of it, but it misses the deeper structure. A treasury has at least three layers operating at once: custody, meaning where the assets technically sit; authority, meaning who is allowed to cause transactions; and policy, meaning what kinds of transactions the DAO actually wants to permit.
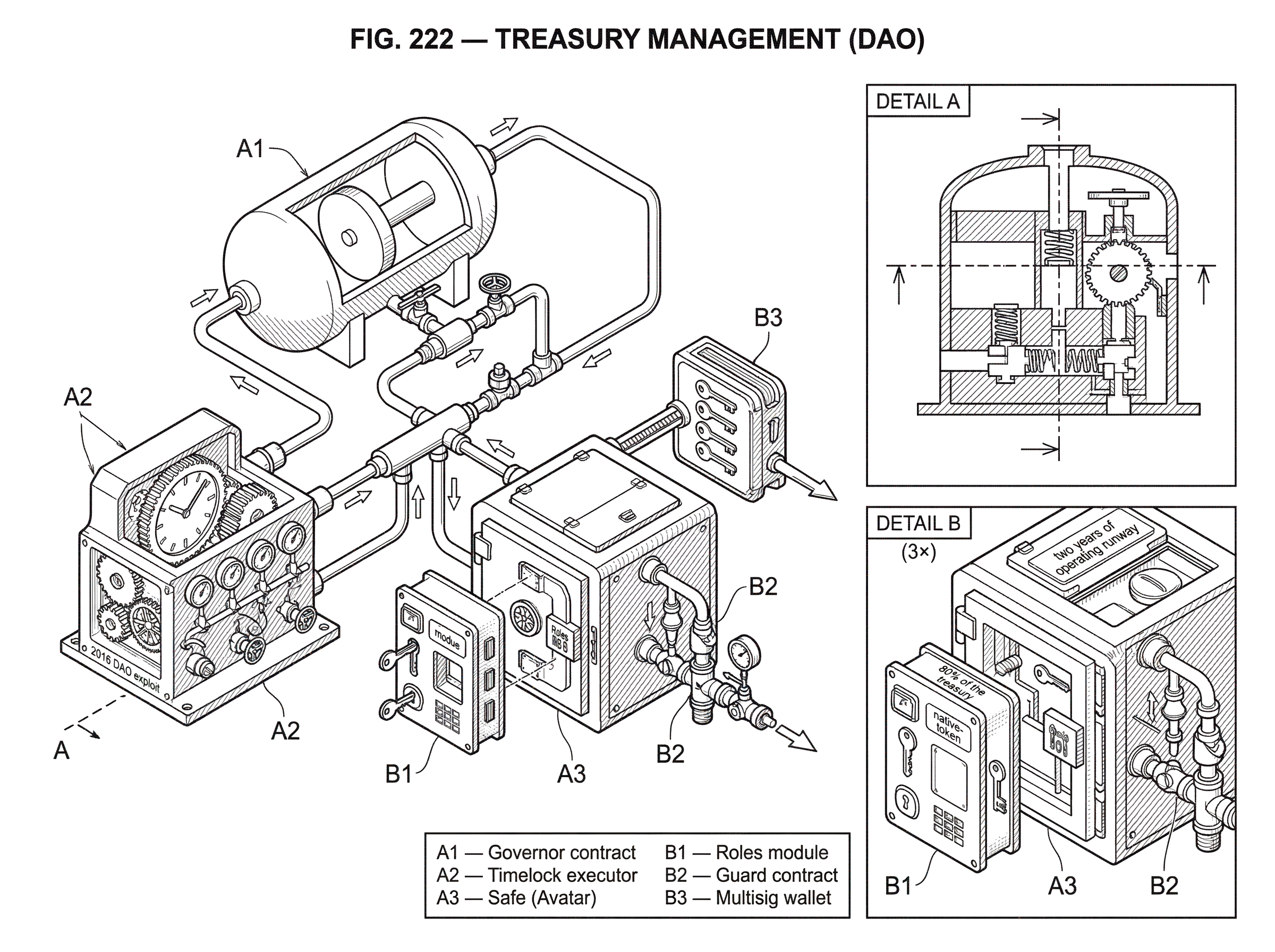
Those layers are often separated on purpose. For example, in common Ethereum governance patterns built with OpenZeppelin Governor and Timelock, the Governor contract does not directly hold funds and should not be the final custodian. Instead, the timelock is the executor and should hold the funds, ownership, and privileged roles. A proposal, in that model, is a sequence of actions: each action specifies a target contract, calldata describing the function call, and any ETH value to send. If token holders approve the proposal, the actions are queued and later executed by the timelock after a delay. The key idea is that the treasury is governed through an execution pipeline, not through a single human pressing “send.”
This design solves a specific problem. If governance could immediately execute any successful vote, token holders and integrators would have no review window before funds moved or permissions changed. A timelock inserts time between approval and execution. That delay is not bureaucracy for its own sake; it is a safety buffer. It gives users time to inspect what was passed, exit if they distrust it, and detect mistakes before they become irreversible.
On the other hand, a pure governance-plus-timelock model can be too slow for routine operations. Paying contributors weekly, rolling over stablecoin positions, claiming rewards, or rebalancing liquidity may not justify full token-holder votes every time. That is why many DAO treasuries are built around programmable accounts such as Safe, often extended with modular controls. In the Zodiac model, the account holding assets is the Avatar; commonly a Safe. Modules add decision logic, modifiers add constraints like delays or role restrictions, and guards can inspect transactions before or after execution. This modular design matters because it lets a DAO separate custody from workflow. The Safe can still hold the assets, while narrower tools control what different actors are allowed to do with them.
So the treasury is better understood as an operating system for collective capital. The wallet is only the outer shell.
Why is DAO treasury management about survival rather than maximizing returns?
The most important mistake DAOs make is treating treasury management as an investment problem before treating it as a survival problem. A DAO usually begins life with a lopsided balance sheet. It may hold a large amount of its own governance token, a smaller amount of ETH or stablecoins, and some protocol-specific assets or LP positions. On paper this can look large. In practice it may be fragile, because the treasury’s value is tied to the DAO’s own market sentiment.
That fragility creates a dangerous feedback loop. If the market falls, the treasury shrinks. If the DAO must sell its native token to fund operations, the sale can push the token lower. The lower token price then weakens the treasury further. Treasury management exists in large part to break that loop by making sure the DAO has enough assets that are liquid, durable, and not perfectly correlated with itself.
This is why many treasury guides emphasize capital preservation first. The principle is almost boring, which is exactly why it matters: the first job of a treasury is not to be clever; it is to avoid forced errors. A DAO with two years of operating runway in relatively liquid assets has time to make decisions. A DAO whose treasury is mostly its own token has fewer real choices than the dashboard suggests.
From that first principle follow the central treasury questions. How much of the treasury should remain in the native token because it aligns the DAO with its own ecosystem? How much should sit in stable assets to cover payroll, grants, or buyback commitments? How much can be staked or deployed into DeFi to earn yield without turning operating reserves into risk capital? The right answer varies by protocol, but the structure of the problem is stable: match the asset to the liability and the time horizon.
If the DAO owes salaries and grants in the next twelve months, those obligations should not depend on a volatile token rally. If the DAO wants strategic exposure to its own ecosystem over several years, some native-token retention may be reasonable. If funds may be needed urgently in a crisis, lockups and bridge dependencies become more expensive than their yield implies. Treasury management is therefore less about maximizing return than about aligning asset behavior with operational needs.
How do governance proposals translate into on-chain treasury transactions?
Mechanically, a DAO treasury acts by encoding decisions as transactions. In OpenZeppelin’s governance pattern, a proposal is not an abstract vote; it is a list of concrete calls. A grant can be expressed as a single action whose target is an ERC-20 token contract and whose calldata encodes transfer(team_wallet, grant_amount). If the proposal passes, governance queues that exact action into the timelock, and after the delay the timelock executes it.
That might sound like a small implementation detail, but it changes how to think about treasury operations. Governance is not deciding in principle to pay a grant. It is authorizing a precise state transition on-chain. That precision is useful because it narrows ambiguity. It is also risky because an incorrectly encoded call can still be faithfully executed. Good treasury systems therefore invest heavily in review, simulation, and transparent tooling.
There is also an important operational subtlety: some Governor designs do not store all proposal parameters on-chain to save gas. Instead, queueing and execution require the full proposal data (not merely a proposal ID) and tooling must reconstruct those details from emitted events. The consequence is practical rather than philosophical: treasury governance depends on surrounding infrastructure such as interfaces, indexers, and scripts. A DAO may have formally decentralized execution logic while still relying on fairly centralized operational tooling to prepare and submit transactions correctly.
A more operationally flexible setup uses a Safe treasury with attached modules. Imagine a DAO whose main treasury lives in a Safe. The community approves a budget framework through governance, but it does not vote on each small payment. Instead, the Safe enables a Roles module that gives the operations team permission to pay approved vendors, but only to specified addresses, only through specified token contracts, and only up to set thresholds over a given period. In Zodiac Roles, permissions can be scoped by address, function, parameter values, frequency, and thresholds. That means the DAO can delegate action without delegating unlimited power.
This is the basic mechanism behind modern DAO treasury operations: broad legitimacy from governance, narrow authority in execution. Governance sets who may act and within what limits; a constrained execution layer handles the day-to-day flow.
When and how should a DAO delegate treasury authority with constrained roles?
People sometimes frame delegation as a regrettable departure from “true decentralization.” In treasury management, that is usually the wrong framing. A treasury that requires full token-holder participation for every transfer is not maximally decentralized in a meaningful sense; it is often just operationally brittle. The real question is whether delegated actors are constrained, observable, and replaceable.
This is where roles, modules, and guards become valuable. A Safe or other smart account can remain the treasury custodian while delegated actors interact through carefully scoped modules. A guard can restrict callable functions. A delay modifier can ensure that even authorized modules cannot execute instantly. A roles system can define that a grants steward may transfer up to a daily amount of a specified stablecoin to pre-approved grantee addresses, while a liquidity manager may rebalance only among approved venues and only within capped exposure.
The advantage is not merely convenience. It is reduction of blast radius. If a delegate key is compromised, the attacker should inherit only the constrained permissions of that role, not the full treasury. If a team member leaves, the DAO can revoke a role without migrating all assets. If a workflow proves unsafe, a module can be disabled while the custody account stays intact.
This design principle appears across chains, even when the tooling differs. On Solana, for example, Squads presents a multisig-first treasury model in which teams jointly manage treasuries, programs, validators, tokens, and NFT collections through a smart-contract wallet infrastructure layer. The exact account model differs from Ethereum, but the underlying problem is the same: collective control needs a mechanism that is legible to humans and restrictive enough to reduce single-key risk.
What changes from chain to chain is the implementation surface. Ethereum DAOs often rely on Governor, Timelock, Safe, and module ecosystems. Solana DAOs often center the treasury around multisig wallet infrastructure like Squads. Cosmos-based systems may involve cross-chain accounts, relayers, and IBC messaging when treasury operations span multiple chains. But the invariant remains: treasury management is the art of translating group intent into bounded transaction authority.
How should a DAO allocate treasury assets to match its liabilities and time horizons?
| Liability | Recommended asset | Liquidity | Main risk | Horizon |
|---|---|---|---|---|
| Near‑term operating | Stablecoins / fiat‑pegged | High | Issuer or depeg risk | 0–12 months |
| Strategic deployment | Native token / L1 assets | Variable | Market correlation to protocol | 1–5 years |
| Contingency demand | Diversified uncorrelated reserves | High to moderate | Bridge or custody dependencies | Immediate to unknown |
Once the control layer is in place, the next question is what the DAO should actually hold. Here it helps to avoid generic portfolio language and start from obligations.
A DAO usually has three broad kinds of claims on its treasury. The first is near-term operating needs: contributor compensation, grants, service providers, audits, and predictable recurring costs. The second is strategic deployment: liquidity seeding, protocol-owned liquidity, incentives, ecosystem investments, or reserve capital for acquisitions and partnerships. The third is contingency demand: emergency responses, reimbursements, recapitalization, or defensive market actions.
Those claims behave differently under stress. Operating needs require liquidity and stability. Strategic deployment can tolerate more volatility if it serves the DAO’s long-term mission. Contingency demand is uncertain in timing but highly sensitive to access: funds that are technically there but trapped in a risky venue, delayed behind governance, or stranded on a compromised bridge may fail when most needed.
This is why diversification in a DAO treasury is not just about improving return distribution. It is about ensuring the treasury contains assets that fail in different ways. Stablecoins may reduce mark-to-market volatility but add issuer, custody, and depeg risk. Layer-1 assets such as ETH may be more endogenous to the crypto economy and have long security track records, but they still fluctuate sharply against fiat-denominated expenses. Staking can generate rewards and partly offset token inflation, but staked positions may introduce lockup, slashing, or smart-contract dependencies. Bridged assets may seem liquid until the bridge is the problem.
A simple example makes this concrete. Suppose a DAO raises capital in its native token during a bull market and keeps 80% of the treasury in that token. Contributor expenses are effectively in dollars, even if paid in crypto. Six months later the token drops 70%. The DAO now faces a worse exchange rate exactly when it needs to sell more tokens to fund the same obligations. Contrast that with a treasury that had previously converted part of its balance into stable operating reserves and a smaller portion into long-duration strategic positions. The second DAO may earn less upside in the boom, but it avoids the reflexive spiral in the bust. Treasury management often looks conservative in the short run because it is buying resilience rather than excitement.
How do security incidents create treasury losses and what protections reduce that risk?
In DeFi, treasury management cannot be separated from security architecture because assets do not disappear only through bad trades. They also disappear through bugs, key compromise, bad permissions, weak monitoring, and unsafe dependencies.
The 2016 DAO exploit remains the foundational example. The immediate cause was a recursive calling vulnerability (what would later be widely discussed as reentrancy) which let an attacker repeatedly withdraw ether in a single transaction flow. The lesson was not merely “audit your contracts.” It was that a treasury contract holding large value is itself a concentrated attack surface. The Ethereum Foundation’s response at the time explicitly warned contract authors to be careful about recursive-call bugs and even to avoid creating contracts that hold very large amounts of value until tooling and experience improved. The deeper principle still applies: treasury architecture should assume that code is never perfect.
That assumption explains the use of timelocks, limits, separate modules, and emergency controls. A well-designed treasury does not rest on one perfect defense. It layers constraints so that a single mistake is less likely to become terminal.
Bridge incidents make the same point with different mechanics. Research surveying interoperability incidents reports multi-billion-dollar losses from cross-chain hacks, with a large share linked to insecure key operations and permissioned intermediary networks. The Wormhole exploit showed how a verification flaw could allow unauthorized wrapped-asset minting. The Ronin exploit showed the danger of centralized validator control, stale delegated permissions, and absent monitoring. For a DAO treasury, the practical consequence is clear: a bridged asset is not just “the same asset on another chain.” It carries the security assumptions of the bridge, validators, relayers, and surrounding operational process.
This matters directly for treasury policy. If a DAO holds reserves on multiple chains, bridge exposure should be treated as a risk budget, not as invisible plumbing. A treasury that is perfectly diversified by token symbol may still be highly concentrated by infrastructure dependency if all of those positions ultimately rely on the same bridge or custodian path.
Monitoring is the other neglected part of treasury security. The Ronin loss went undetected for days, which is astonishing only if one assumes treasury management ends once permissions are configured. It does not. A treasury requires continuous observation: large transfers, role changes, module enablements, unusual approvals, governance actions, and delays in expected cross-chain settlement should all be watchable. Tools such as OpenZeppelin Defender historically packaged relaying, monitoring, actions, transaction proposals, and access control into a single operational surface; other teams use custom bots, Forta-based alerting, or chain-specific dashboards. The tool choice matters less than the principle: if the treasury can move, it must also be watched.
When should a DAO use emergency powers and how should those powers be scoped?
| Option | Speed | Centralization risk | Oversight | Typical controls |
|---|---|---|---|---|
| No emergency powers | Slow | Low | Token‑holder votes only | Standard timelock |
| Small emergency council | Immediate | Medium | Mandatory post‑ratification | Narrow multisig + scoped roles |
| Protocol‑native shutdown | Immediate for settlement | Low to medium | DAO‑controlled trigger and parameters | Shutdown module + redemption rules |
There is an uncomfortable truth here: fully ordinary governance is often too slow for abnormal conditions. If an exploit is active, waiting through a normal proposal period and timelock may convert a recoverable problem into a total loss. That is why many DAOs introduce an emergency council or guardian structure with narrowly scoped authority.
Done badly, this reintroduces centralization through the back door. Done well, it creates a bounded exception path. Typical patterns use a small multisig or security council with power to pause contracts, trigger tightly defined emergency actions, or invoke a guarded timelock bypass. The crucial design questions are scope, transparency, and aftermath. What exact actions can the emergency body take? How quickly? Over which contracts? And must the broader DAO ratify those actions later?
The best rationale for emergency powers is not that trusted people are wiser than governance. It is that speed is itself a security property in certain states of the world. But because speed can be abused, emergency paths should be narrower than normal governance, not broader. They should be public, documented, tested in drills, and followed by post-incident disclosure and community review. If the treasury can be touched through emergency authority, the conditions and limits should be explicit.
Maker’s Emergency Shutdown illustrates a more protocol-native version of this logic. Shutdown is designed as a last-resort mechanism to stop and gracefully settle the system so that claimants receive the net value they are entitled to. The details are Maker-specific, but the treasury lesson generalizes: some systems need a way to prioritize orderly settlement over normal operation when the assumptions supporting ordinary governance or market function no longer hold.
What operational practices define a well-run DAO treasury?
A well-run DAO treasury usually combines several design choices that reinforce one another.
First, it uses a custody structure appropriate to the DAO’s maturity. Early-stage DAOs may rely more heavily on multisigs because they need speed and do not yet have robust token-holder participation. More mature DAOs often move strategic powers into on-chain governance with timelocked execution while keeping routine operations delegated under strict constraints. This is not a binary choice between multisig and governance; it is usually a staged architecture.
Second, it defines explicit operating reserves. This is the amount of capital that should remain highly liquid and relatively stable because it backs known obligations. The exact number is a policy choice, but the logic is universal: if expenses are predictable, the reserve backing them should not be speculative.
Third, it delegates recurring workflows through constrained permissions rather than broad human trust. If a grants committee needs to make small recurring payments, give it a role with narrow scopes and thresholds, not raw signing authority over the whole treasury. If a module can enforce delay, address allowlists, function restrictions, or spending caps, those are usually preferable to unenforced social promises.
Fourth, it treats infrastructure and counterparty risk as part of portfolio construction. Yield earned through staking, lending, LPing, or bridging is compensation for additional assumptions. The right question is not “what APY do we get?” but “what new failure modes are we accepting, and are they tolerable for this slice of the treasury?”
Fifth, it builds operational visibility: proposal tracking, role audits, transaction simulation, alerting, and incident runbooks. A DAO should know not only what assets it owns, but through which contracts, permissions, modules, and chains those assets are exposed.
Finally, it accepts that governance design is part of treasury design. A treasury is managed not just by markets but by decision latency. If the DAO cannot make budget changes, revoke permissions, or approve emergency actions in time, the portfolio is less useful than it appears.
Conclusion
DAO treasury management is the discipline of preserving a community’s ability to act with its capital over time. The core challenge is not simply choosing assets. It is designing custody, authority, and policy so that funds can be used when needed, but not easily misused when they should not be.
If there is one idea to remember, it is this: a DAO treasury is healthy when its financial structure and its control structure fit together. Diversification without sound execution is fragile, and elegant governance without usable reserves is hollow. Treasury management exists to make both sides work at once.
How do you trade through a DEX or DeFi market more effectively?
Trade through DEXs and DeFi markets by matching execution to liquidity and minimizing price impact. Use Cube Exchange to fund your account and place orders while you compare on-chain pool depth and quoted spreads before execution.
- Fund your Cube account with fiat on-ramp or deposit the exact token (ETH/USDC/etc.) you plan to trade.
- Check market liquidity for the pair on on-chain DEX explorers or order-book sources: inspect 24h volume and top-of-book depth to estimate price impact for your intended size.
- Choose an execution method: use a market order on Cube for small trades; for larger trades place limit orders or split the size into multiple smaller orders and set a conservative slippage tolerance (for example 0.5–2%) when using market fills.
- Monitor fills and confirmations. If limit orders do not fill, adjust price or break the order into timed slices and re-evaluate pool depth between slices.
Frequently Asked Questions
Because governance contracts typically vote on a set of actions but should not be the final custodian: the timelock is the executor and should hold funds, ownership, and privileged roles so that approved proposals are queued and executed after a review delay that gives the community time to inspect or exit. This arrangement both enforces an execution pipeline and provides a safety buffer before irreversible transfers occur.
Safe-like programmable accounts act as the treasury’s custody layer while Zodiac-style modules, guards, and role systems provide narrowly scoped permissions (address allowlists, function/value thresholds, frequency caps, delays) so daily workflows can be delegated without granting unlimited signing power. This modular split between custody and constrained workflow reduces blast radius from compromised keys and makes delegates observable and replaceable.
Start from liabilities: keep near-term payroll and grants in liquid, low-volatility assets; hold strategic, long‑horizon exposure to native tokens or protocol-owned liquidity; and reserve contingency funds in assets and locations that can be accessed quickly during emergencies. Exact percentages are not prescribed in the article - the core principle is to match asset liquidity and failure‑modes to the timing and certainty of the DAO’s obligations.
Bridged assets inherit the bridge’s security assumptions, so a treasury diversified only by token symbol can still be concentrated by shared bridge/custodian risk; past incidents like Wormhole and Ronin show verification flaws and compromised validators can enable large unauthorized minting or transfers, so DAOs should treat bridges as a risk budget rather than invisible plumbing. The paper and incident analyses emphasize that cross-chain holdings require explicit consideration of relayers, validators, and bridge design.
Monitoring is essential because permissions and balances can change or be drained in minutes; the Ronin example shows losses that went undetected for days, and tooling such as on‑chain watchers, Forta alerts, or relayer/transaction monitors (historically packaged by services like Defender) are practical necessities for a treasury that can move. The article and supporting evidence stress that if the treasury can move, it must also be watched continuously.
Emergency councils or guardians are justified when speed is itself a security property (for example to pause contracts or trigger narrowly scoped emergency flows), but they must be explicitly scoped, transparent, time‑bound, and followed by community ratification; otherwise they reintroduce centralization. The article recommends documenting powers, publishing post‑incident disclosures, and restricting the emergency path more tightly than normal governance.
Delegation is not necessarily less decentralized; requiring token-holder votes for every transfer can be operationally brittle. The better metric is whether delegated authority is constrained, observable, and replaceable - appropriate role scoping, delays, and modules can preserve collective legitimacy while enabling practical operations.
On‑chain governance proposals are concrete lists of calls (target, calldata, ETH value); if a proposal passes, those exact calls are queued into and executed by the timelock, so governance decisions translate to precise state changes. Because some Governor implementations store proposal parameters off‑chain to save gas, queueing/execution may require the full proposal data and surrounding tooling (indexers, relayers, UIs) to reconstruct and submit the transaction correctly.
A common maturity path is early reliance on multisigs for speed and simplicity, then gradual migration of strategic powers into timelocked on‑chain governance while keeping routine flows delegated under constrained modules; this staged architecture balances usable reserves and governance latency as the DAO grows. The article emphasizes that this is not an either/or choice but a phased design matching custody to organizational needs.
Yield-generating activities like staking, lending, or LP positions add failure modes (lockups, slashing, counterparty or protocol risk) so they should be treated as explicit assumptions the treasury is buying; the right question is not only APY but what new risks those activities introduce and whether they are acceptable for that slice of reserves. The article recommends evaluating yield opportunities in terms of the new operational and security dependencies they create.