What is a Smart Account?
Learn what smart accounts are, how they work, why they exist, and how features like recovery, multisig, batching, and gas sponsorship become possible.
Introduction
Smart accounts are blockchain accounts whose authorization and execution rules are defined by code, not just by possession of a single private key. That may sound like a technical detail, but it changes the basic shape of a wallet: instead of asking only *"does this signature match this key?" , the network or surrounding infrastructure can ask "does this account’s own logic approve this action?" * The result is a wallet that can recover from lost devices, require multiple approvals, batch actions together, let someone else sponsor fees, or use nonstandard signing schemes.
The puzzle smart accounts solve is simple. Most wallet UX problems are really account design problems disguised as interface problems. Seed phrases are brittle because a plain externally owned account, or EOA, is controlled by one signing key. Gas onboarding is awkward because a plain account must usually pay fees in the chain’s native token. Team custody is risky because a plain account has no native notion of shared control. If the account itself cannot express richer rules, apps can only patch around the problem.
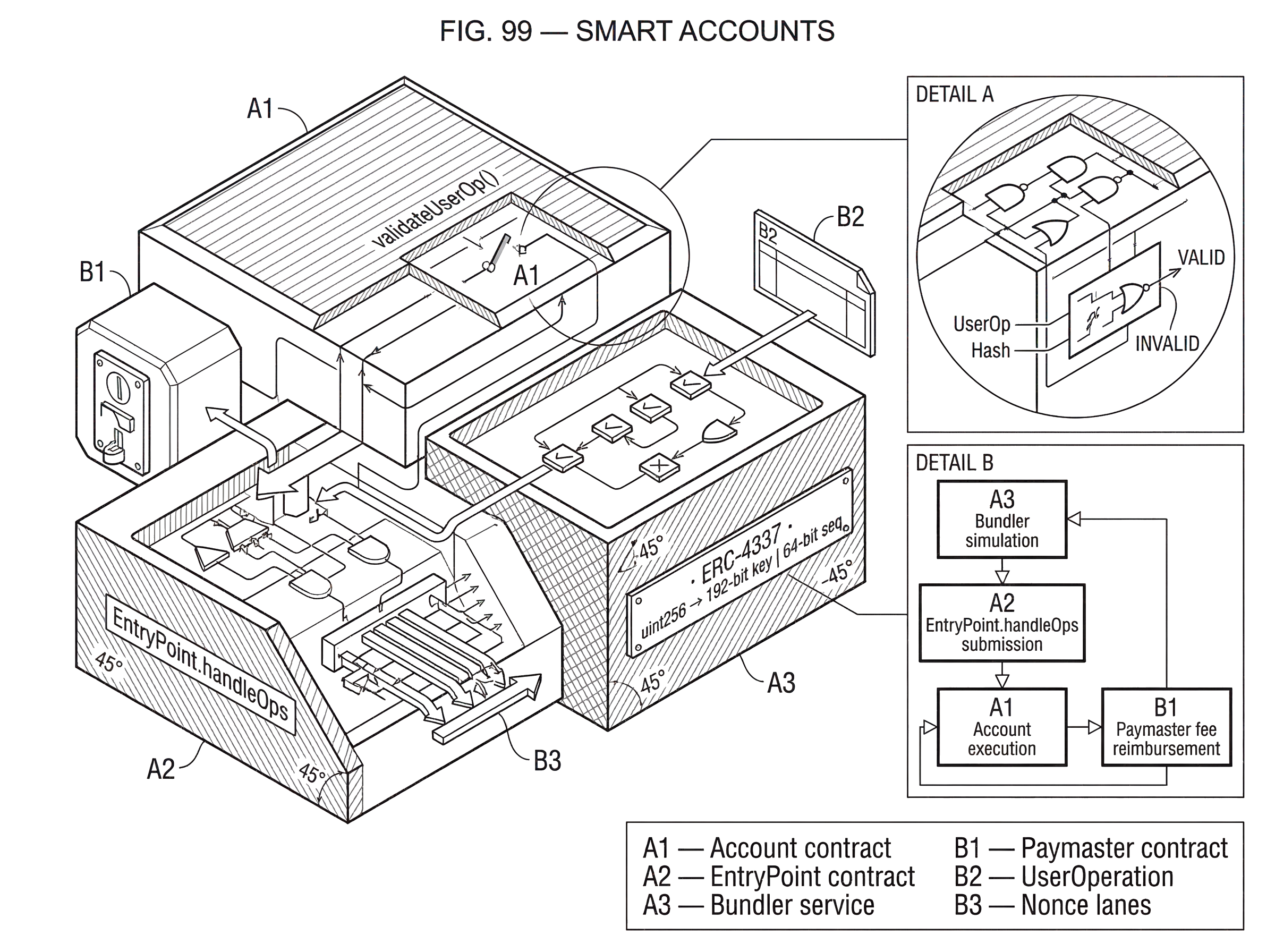
A smart account changes that by moving the rules into code. On Ethereum, this is most commonly done through account abstraction systems built around ERC-4337, where user intent is packaged into a UserOperation, checked by account code, and executed through a shared EntryPoint contract without changing Ethereum consensus. On other systems the same idea appears in different forms: ZKsync supports native smart accounts at the protocol level, Starknet was built around native account abstraction, and Substrate-based chains expose similar behavior through a mix of programmable accounts, multisig, proxies, batching, and recovery primitives.
The core idea to keep in mind is this: a smart account is not just a place that holds assets; it is a program that decides under what conditions assets move and actions execute. Once that clicks, the features people associate with modern wallets stop looking like add-ons and start looking like direct consequences of programmable authorization.
Key‑controlled vs code‑controlled accounts: how do they differ?
| Account type | Authority model | Expressiveness | Security surface | Best for |
|---|---|---|---|---|
| Key-controlled | Single private key | Single signature rule | Small; cryptography only | Simple wallets; low overhead |
| Code-controlled | On-chain programmable policy | Multisig, recovery, batching | Larger; code + modules | Recovery, sponsored fees, orgs |
A traditional account model is intentionally narrow. There is an address, a nonce, and a rule that says a valid transaction must be authorized by the private key corresponding to that address. This simplicity has advantages. The account is easy to reason about, signing is straightforward, and the validation rule is cheap for the protocol to check.
But that simplicity is also the limitation. If you want a wallet that lets your phone and laptop both authorize low-risk actions, but requires a hardware key plus a guardian for withdrawals above a threshold, a plain key-controlled account cannot express that. If you want to recover access through trusted contacts, or pay fees in a token instead of the native asset, or let a game session spend only within tightly scoped permissions, the account itself has no place to encode those rules.
A smart account introduces that missing layer. The address still exists, and the account still holds tokens or other state, but the authorization rule becomes programmable. Instead of the protocol hard-coding one acceptable validation rule, the account contract can implement its own. That logic might still be as simple as checking a single ECDSA signature from an owner key. But it can also require multiple signatures, validate a passkey-derived signature, enforce a time window, distinguish between admin actions and routine actions, or delegate limited powers to a session key.
This is why smart accounts are often described as making wallets more like applications. The account is no longer a dumb container attached to a key. It is a stateful program with policy.
That phrase needs a caveat. Programmable does not mean arbitrarily Safe. Code can encode powerful rules, but it can also encode dangerous ones. A key failure mode of smart accounts is that flexibility increases attack surface. A badly designed module, factory, recovery flow, or deployment path can create backdoors that do not exist in simpler accounts. The important point is not that smart accounts are automatically better, but that they move the design space from fixed protocol rules to wallet-level engineering choices.
What practical features define a smart account?
In practice, a smart account usually combines two kinds of logic: validation logic and execution logic. Validation logic answers who or what is allowed to authorize this action? Execution logic answers what can happen once authorized, and how should it be carried out?
That distinction matters because many wallet features are really validation features. Social recovery works because the account can accept a guardian-approved key rotation even if the original key is lost. Multisig works because the account validates a threshold of owners rather than one signer. Session keys work because the account can treat a temporary key as valid only for certain apps, values, or time periods. Spending limits work because validation can inspect state and reject actions beyond policy.
Other features are execution features. Batching works because the account can make several calls in one authorized action. Fee sponsorship works because execution is integrated with infrastructure that lets a third party cover gas. Automation and recurring payments work because the account can permit pre-approved logic to trigger under specified conditions.
Safe is a useful example because it shows the idea in a concrete, widely used form. A Safe wallet is a smart-account system where control is distributed across multiple owners and extended through modules and guards. The central security gain is easy to see: instead of one compromised key meaning total loss, movement of funds can require multiple approvals. But the same architecture also shows the tradeoff: modules and deployment paths are highly privileged, so a malicious or unsafe module can be more powerful than the nominal owners if the system is configured badly. In other words, smartness adds expressiveness and shifts the security question from “who has the key?” to “what logic actually has authority?”
How do smart accounts work on Ethereum without changing consensus?
Ethereum originally separates accounts into EOAs and contract accounts. EOAs can initiate transactions directly because they are controlled by signatures recognized by the protocol. Contract accounts can execute logic, but they do not natively start transactions on their own. That split makes smart-account wallets awkward if you want them to feel like first-class accounts.
ERC-4337 is the main workaround. Instead of changing Ethereum’s consensus rules or transaction format, it introduces a higher-layer object called a UserOperation. This is not a normal Ethereum transaction. It is a pseudo-transaction that expresses user intent for a smart account. Users send UserOperation objects into a separate mempool, bundlers collect them, simulate whether they will validate successfully, and then package them into a regular transaction that calls handleOps on a singleton EntryPoint contract.
This architecture matters because it explains both the power and the complexity of Ethereum smart accounts today. The network still only understands normal transactions at the consensus layer. But a layer above that has been built to let contract accounts behave as if they were first-class user accounts.
The mechanical flow is easier to understand through a narrative. Imagine Alice has a smart account wallet and wants to swap tokens and then deposit the proceeds into a vault in one action. Her wallet does not create a conventional transaction from an EOA. Instead it constructs a UserOperation describing the sender account, the intended call data, gas parameters, nonce, and signature or other authorization data. If Alice’s account has not yet been deployed, the operation can also include initialization code so the account is created just in time.
Alice sends this UserOperation to a bundler. The bundler cannot trust it blindly, because smart-account validation is arbitrary code and running invalid operations on-chain would cost the bundler gas. So the bundler simulates the operation against the EntryPoint. During this simulation, the EntryPoint calls the account’s validateUserOp(...) function. That function is where the smart account proves the operation is authorized and that required funds or sponsorship are available. If a paymaster is involved, the EntryPoint also calls paymaster validation logic. Only if the simulation succeeds does the bundler include Alice’s operation in a bundle and submit a real transaction to EntryPoint.handleOps(...) .
Once on-chain, EntryPoint repeats the validation and then executes the requested action. The bundler, having paid gas up front for the bundle transaction, is reimbursed from the account’s deposit or by the paymaster if sponsorship was approved.
The important structural point is that Ethereum smart accounts under ERC-4337 rely on a three-part split of responsibility. The account contract defines authorization. The bundler decides whether an operation looks safe and economically worth including. The EntryPoint is the on-chain referee that enforces the validation and payment flow.
Why is validateUserOp critical for ERC‑4337 smart accounts?
If there is one function that captures what a smart account is on Ethereum, it is validateUserOp. ERC-4337 requires smart contract accounts to implement a validation hook with that shape. This is the moment when the account’s own logic decides whether the requested action is valid.
That function can be thought of as replacing the protocol’s normal signature check with wallet-defined policy. A minimal account might do nothing more than recover a signer from the operation hash and compare it to an owner address. A richer account can do much more: verify multiple signatures, accept signatures from different schemes, enforce expiry times, route different nonce channels to different policies, or require that a recovery delay has elapsed before a new key takes effect.
This is where smart-account features become mechanically real instead of marketing claims. Social recovery is not magic; it is validation logic that accepts a guardian-mediated change under certain conditions. Gasless onboarding is not magic; it is validation plus paymaster logic that allows execution even when the user does not hold the native token. Passkey support is not magic; it is alternate signature verification logic. Batching is not magic; it is account execution logic reached after successful validation.
It is also where many misunderstandings begin. People sometimes imagine smart accounts as merely “wallet apps with nicer UX.” But in a smart-account architecture, the critical policies live on-chain in the account contract and its trusted components. The wallet interface matters, but it is only the front end to account logic that has actual authority.
How do smart accounts handle nonces and prevent replay attacks?
| Model | Ordering | Use case | Failure mode | Best when |
|---|---|---|---|---|
| Sequential | Strict sequence | Simple replay protection | Blocks concurrent flows | Single-user wallets |
| Parallel lanes (ERC-4337) | Multiple nonce lanes | Admin vs user separation | Complex mempool handling | Multichannel workflows |
| Arbitrary ordering (ZKsync) | Out-of-order allowed | High-concurrency apps | Mempool rejections/stuck txs | Native AA with flexible nodes |
Every account system needs replay protection. If an attacker can resubmit the same authorized action repeatedly, authorization is meaningless. EOAs usually solve this with a single sequential nonce: each transaction must use the next number.
Smart accounts often need something looser. A single strict sequence is simple, but it makes independent flows interfere with each other. An admin key rotation might block a normal payment if both consume the same nonce lane. A session key for a game should not necessarily have to wait behind a treasury action. ERC-4337 therefore uses what it describes as a semi-abstracted nonce model. The uint256 nonce is logically split into a 192-bit key and a 64-bit sequence, and EntryPoint.getNonce(sender, key) exposes the current value for a given lane.
The intuition is that a smart account can maintain parallel nonce channels. One channel might represent routine user actions, another administrative changes, another app-specific delegated permissions. Replay protection still exists because each lane has an advancing sequence. But ordering becomes more expressive.
Other systems make different choices around the same problem. ZKsync, for example, exposes configurable nonce ordering modes such as sequential and arbitrary. The benefit is similar: account designers can choose whether reliability through strict ordering matters more than flexibility through looser ordering. The tradeoff is also similar: more freedom in ordering usually means more complex mempool behavior and more ways for transactions to be rejected or get stuck.
How do paymasters let someone else pay gas for a smart account?
One of the most visible smart-account features is fee abstraction. In a plain account model, the actor and the fee payer are tightly coupled. If you send the transaction, you pay the network fee in the native asset. That is a protocol convenience, but it is bad product design for onboarding.
Paymasters loosen that coupling. In ERC-4337, a paymaster is an optional contract that can sponsor the gas cost of a UserOperation if its own validation rules approve it. Mechanically, the paymaster participates in validation through hooks such as validatePaymasterUserOp, and it must maintain deposits and stakes in the EntryPoint so bundlers have confidence that fees can actually be paid.
This enables several practical models. An app can sponsor a user’s first actions so the user does not need ETH up front. A service can reimburse fees under promotional or policy-based rules. A system can approximate token-paid gas by coordinating token transfers or off-chain pricing with a sponsoring paymaster. On ZKsync, similar goals appear in native paymaster support, where users can pay fees in ERC-20 tokens or receive sponsorship.
But here the mechanism explains the risk too. If a paymaster approves an operation and it later fails during execution, the sponsor may still be responsible for fees. That means gas sponsorship is not free magic; it is an underwriting business with griefing risk. The more flexible the sponsorship rules, the more carefully the sponsor must defend itself.
This is why paymasters tend to have operational controls beyond pure on-chain logic. Real implementations may use signature-based approvals, allowlists, API-mediated checks, spending caps, or bundler restrictions. Coinbase’s VerifyingPaymaster, for example, uses signature-based validation and can restrict sponsorship to certain bundlers, which makes the system more governable but also less permissionless. Smart accounts often improve user experience by introducing selective trust and policy; not by making trust disappear.
Why do bundlers simulate UserOperations, and what risks does that create?
A normal Ethereum node can check an EOA transaction with relatively standardized rules. A bundler facing ERC-4337 UserOperations has a harder job because account and paymaster validation are arbitrary code. If the bundler includes bad operations, it can lose money on gas.
So bundlers simulate. ERC-4337 requires bundlers to simulate validation and drop a UserOperation if the simulation reverts. This is the practical defense that makes smart accounts workable on today’s Ethereum: execute the validation logic off-chain first, try to see whether it will succeed, then only submit bundles that are expected to pass.
This simulation requirement creates a different trust and centralization picture from the base transaction pool. Bundlers apply local policies. Some validation constraints are only partially standardized. Reputation systems, opcode restrictions, and storage-access rules exist largely to protect bundlers from denial-of-service attacks and state interference. ERC-7562 is part of this broader effort, restricting what validation logic may do so that permissionless bundlers can safely process operations.
The consequence is subtle but important. Smart accounts are programmable, but not every imaginable program is equally processable by an open bundler market. If your validation logic reads or writes state in ways bundlers consider unsafe, your account may work only with private bundlers or bespoke infrastructure. So there is a real boundary between what a smart account can express in code and what the surrounding ecosystem can safely support in a permissionless way.
That boundary is easy to miss when smart accounts are presented purely as a UX upgrade. Under the hood, they are a coordination system among contracts, bundlers, mempools, simulation rules, and fee sponsors. The user sees “sign in with a passkey” or “no gas required.” The infrastructure sees a fragile anti-DoS equilibrium.
How do smart accounts differ across chains (Ethereum, ZKsync, Starknet, Substrate)?
| Chain | Implementation layer | Native initiation | Fee abstraction | Typical tradeoff |
|---|---|---|---|---|
| Ethereum (ERC-4337) | Layered EntryPoint + bundlers | No; via UserOperation | Paymasters via EntryPoint | More indirection; bundler risk |
| ZKsync | Protocol-native accounts | Yes; accounts initiate | Native paymasters; token fees | Simpler infra; fewer relayers |
| Starknet | Native contract accounts | Yes; contract-initiated | Paymasters / guardian flows | Early AA features; platform-specific |
| Substrate / Polkadot | Composable FRAME primitives | Varies by parachain | Proxies or pallet-based fees | Flexible primitives; assembly required |
Although ERC-4337 dominates the Ethereum conversation, the idea of a smart account is broader than that standard and broader than Ethereum itself.
On ZKsync, smart accounts are native to the protocol. Accounts can both initiate transactions and contain arbitrary logic, which means the chain does not need ERC-4337’s exact alt-mempool architecture to achieve the core result.
The same broad wallet features still appear but the mechanism is built into the system rather than layered on top through an EntryPoint contract.
- custom signatures
- native multisig
- spending limits
- paymasters
On Starknet, account abstraction is also native. Wallets are contract accounts by design, which is why features like guardian-based recovery and richer signing models appeared there early in products such as Ready. The user-facing lesson is that smart-account behavior is not tied to a single Ethereum standard. The engineering lesson is that native support usually reduces some of the indirection and coordination burden seen in ERC-4337.
On Substrate and Polkadot, the equivalent idea appears through what is often described as origin abstraction and flexible account primitives. There is not necessarily one universal “smart account” module. Instead, developers combine multisig, proxies, derivative accounts, recovery systems, batching, and token-fee mechanisms. The concept is the same at a high level: account behavior is no longer reducible to one key, and authority can be structured by programmable or composable rules.
So the fundamental concept is chain-agnostic even though the implementation is not. Smart accounts are the wallet expression of account abstraction. Different systems choose different layers to implement that abstraction: protocol-native, contract-native, or a mixture of primitives.
Where does authority live in smart accounts and what are the security implications?
The promise of smart accounts is better security through better policy. The danger of smart accounts is hidden authority through more moving parts. Both are true.
A multisig smart account can remove the single-key failure mode. A recovery-enabled account can make loss less catastrophic. Transaction simulation and guards can reduce operational mistakes. These are real improvements, and much of the ecosystem’s adoption reflects that. Safe’s large footprint in treasury and organizational use is not accidental; many users genuinely need shared control, programmability, and operational protections that EOAs cannot provide.
But smart accounts also create new privileged surfaces. The account implementation itself can have bugs. The factory that deploys accounts can initialize them unsafely. Modules may be able to execute with more power than nominal owners. Paymasters can become policy bottlenecks. Bundlers may censor or selectively process operations. A user can still be socially engineered into signing a malicious approval flow, and a more advanced wallet does not automatically prevent that. Recent drainer campaigns show that attackers often do not need to break cryptography; they only need to trick users into granting valid authority.
The OpenZeppelin analysis of backdoored Gnosis Safe deployments is a good example of this principle. The vulnerability was not “multisig is broken.” The problem was that flexible deployment and modules allowed arbitrary delegatecall during setup, letting a malicious deployer attach privileged backdoors before owners realized it. That case captures the core security lesson of smart accounts: the account is a program, so every initialization path, extension hook, and trusted module becomes part of the wallet’s threat model.
This does not make smart accounts a bad idea. It means they must be evaluated like software systems, not like inert key containers.
What are common uses for smart accounts?
Once the mechanics are clear, the common uses follow naturally from the programmable-account model. Consumers use smart accounts to replace fragile seed-phrase-only custody with recovery, passkeys, or device-based policies. Teams use them to replace single-operator wallets with threshold approvals, role separation, and execution controls. Apps use them to smooth onboarding through sponsored fees and one-click flows. Power users use them to batch actions, automate routine tasks, and isolate risk through session keys or spending limits.
These are not separate categories so much as different expressions of the same underlying capability. If an account can define its own authorization and payment logic, then user experience can be shaped around human needs instead of around the fixed assumptions of a one-key account model.
That is the real significance of smart accounts. They do not merely add features to wallets. They change the unit of design from a key to an account policy.
Conclusion
A smart account is a wallet account controlled by programmable logic rather than only by a single protocol-defined signature rule. That shift makes recovery, multisig, batching, session keys, custom signatures, and sponsored fees possible because those behaviors are encoded in the account itself.
On Ethereum, ERC-4337 delivers this through UserOperations, bundlers, paymasters, and a shared EntryPoint without consensus changes. On systems with native account abstraction, the same idea appears more directly. The detail that matters most is easy to remember: a smart account is a program that holds assets and decides what counts as valid authority. Once you see wallets that way, both their new capabilities and their new risks make sense.
How do you secure your crypto setup before trading?
Secure your crypto setup before trading by verifying who can sign for your account, how recovery works, and that the destination and network are correct. On Cube (a non-custodial MPC-backed workflow), perform a short checklist: confirm account authority and recovery, test destinations with a small transfer, then fund and execute trades through Cube.
- Confirm account authority and recovery: verify your Cube MPC signing setup and that your recovery devices or contacts are current. If you added a session key or delegated signer, revoke or update it now.
- Verify destination address and network: copy the recipient address, check the chain/network, compare checksum characters (first/last 4), and confirm any contract address matches the official source.
- Run a low-value test transfer or approval: send a small amount of the same token on the chosen network or approve a minimal allowance to the contract you will use; confirm the outcome and gas behavior.
- Fund your Cube account and place the real action: deposit the token or native gas, open the market or contract flow, choose an execution type (use a limit order or a small-sized market order to control slippage), review estimated fees, then submit.
Frequently Asked Questions
ERC-4337 introduces a paymaster contract that can sponsor gas: the paymaster validates the UserOperation via EntryPoint hooks, must hold deposits/stake so bundlers can be reimbursed, and remains liable for fees even if the sponsored execution later fails, so sponsorship is an underwriting risk rather than free gas.
Smart accounts increase attack surface because authority now lives in on‑chain code, factories, modules, recovery flows, and off‑chain infrastructure; mistakes or malicious modules, unsafe deployment hooks, or compromised paymasters/bundlers can create backdoors that do not exist for a simple EOA.
Bundlers must simulate each UserOperation off‑chain because account and paymaster validation are arbitrary contract code; that protects bundlers from wasting gas but concentrates economic and operational risk in bundlers and raises infrastructure and centralization concerns.
ERC-4337 avoids consensus changes by introducing a UserOperation mempool, off‑chain bundlers, and a shared on‑chain EntryPoint contract: bundlers pack validated UserOperations into a normal transaction that calls EntryPoint.handleOps, which repeats validation and executes the account’s requested actions.
Smart accounts typically use a more flexible nonce model (ERC‑4337’s semi‑abstracted nonce) that splits a 256‑bit nonce into a lane key and a per‑lane sequence so the account can maintain parallel nonce channels for independent flows, reducing interference between unrelated actions.
Not always - some validation logic (or designs that read/write unsafe storage/opcodes) can violate the constraints bundlers expect, so those accounts may only be processable by private or bespoke bundlers; ERC‑7562 and similar limits exist precisely to keep permissionless bundlers safe, which constrains expressiveness.
Social recovery is implemented as account validation logic that accepts guardian-mediated key rotations under specified conditions, but the exact guardian selection, rotation, and threat model vary by product and are often under‑specified, so recovery relies on external trusted actors and design details matter for security.
No; smart accounts enable stronger policies (multisig, recovery, limits) but also introduce new privileged surfaces (deployment factories, modules, paymasters, bundlers) and user‑approval risks, so they must be evaluated as software systems rather than assumed inherently safer.
EntryPoint is the shared on‑chain referee that validates and executes UserOperations, so it centralizes important responsibility and must be carefully audited and maintained; relying on a canonical EntryPoint also creates an operational focal point for risk and upgrades.
Chains with native account abstraction (Starknet, ZKsync) let contract accounts initiate and validate operations as a first‑class protocol feature, reducing the off‑chain mempool and bundler indirection ERC‑4337 requires, but the same high‑level tradeoffs about expressiveness versus operational complexity still apply.
Related reading