What Are Privacy Coins?
Learn what privacy coins are, why they exist, how Monero and Zcash hide transaction data, and what tradeoffs shape real-world privacy.
Introduction
Privacy coins are cryptocurrencies designed to make transactions hard to trace on a public blockchain. That sounds contradictory at first. A blockchain is supposed to be a shared ledger that everyone can verify, while privacy seems to require hiding information. Privacy coins exist to solve exactly that tension: how to let a network confirm that money is valid and not double-spent without exposing the full transaction graph to everyone who looks.
The need for this is not theoretical. In a transparent system, every transfer can reveal relationships between addresses, balances, spending habits, and business flows.
Even if addresses are only pseudonyms, repeated use and off-chain data can turn pseudonymity into practical surveillance.
- exchange records
- merchant logs
- IP information
- public donation addresses
- payout disclosures
The result is not just less personal privacy. It also weakens fungibility, the idea that one unit of money should be interchangeable with any other. If coins can be labeled by their history, then some coins become more acceptable than others.
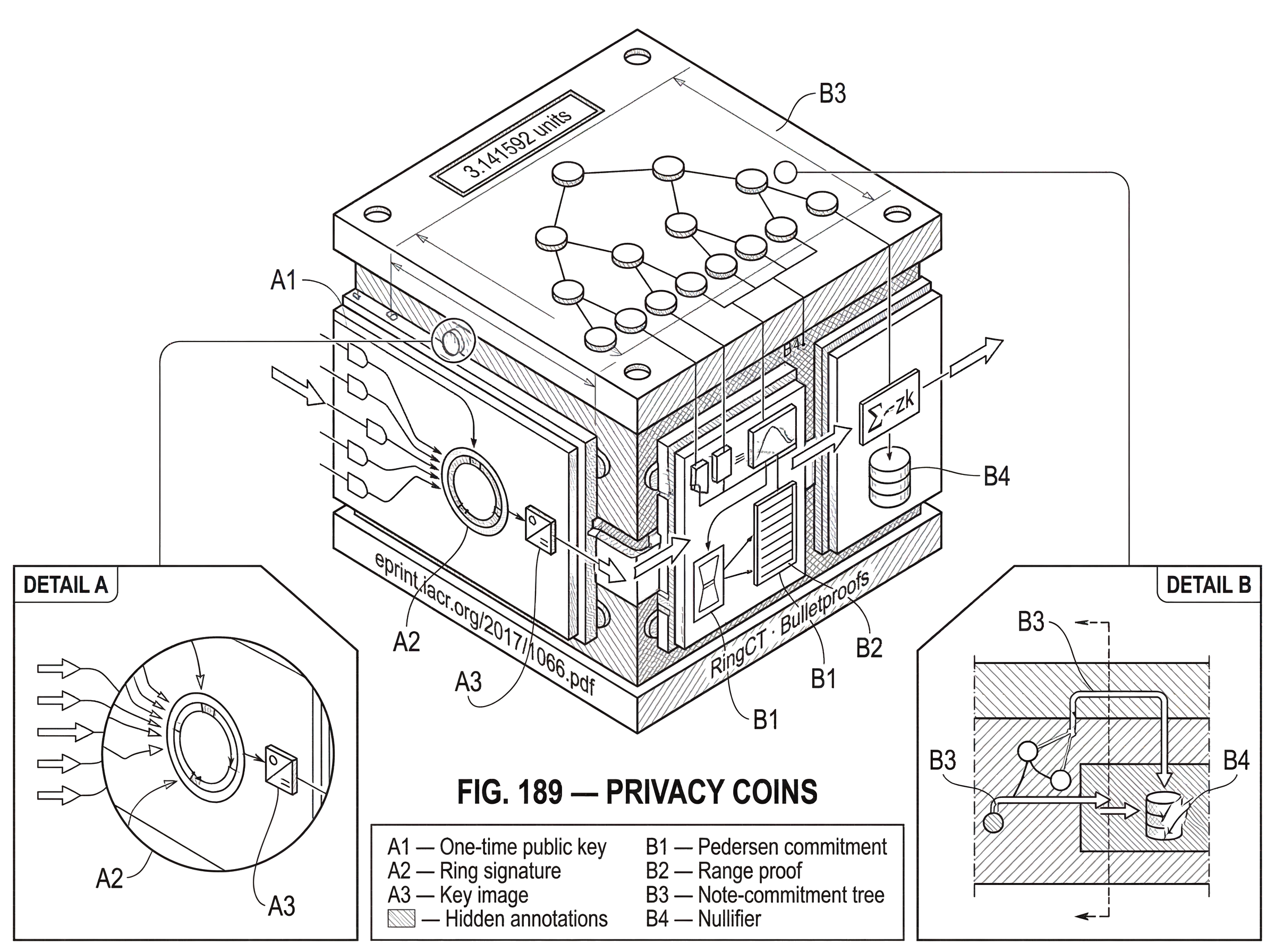
So the core problem privacy coins solve is simple to state and hard to implement: keep the ledger publicly verifiable while hiding the links that make users easy to map. Different systems solve this with different cryptographic tools. Some, like Monero, obscure senders with ring signatures, give each payment a unique destination key, and hide amounts with confidential transactions. Others, like Zcash, use zero-knowledge proofs so the chain can verify a shielded transfer without revealing the underlying note, recipient, or value. These designs are different in mechanism, but they are trying to preserve the same invariant: the network must still be able to say, with high confidence, “this spend is authorized, balanced, and not a double-spend,” even though outside observers cannot reconstruct the full story.
Why do transparent blockchains reveal transaction relationships?
A transparent blockchain leaks information because it publishes exactly the data needed to follow value from one place to another. In Bitcoin-like systems, outputs are visible, amounts are visible, and spending an output explicitly points back to the earlier output being spent. That gives the system its auditability, but it also creates a transaction graph that analysts can study indefinitely. Once a single address or payment is linked to a real-world identity, nearby parts of that graph often become easier to interpret.
This is why the usual phrase pseudonymous can be misleading. It suggests that using fresh addresses is enough. In practice, address reuse is only one source of leakage. Transaction structure, timing, amount patterns, wallet behavior, and interactions with exchanges or merchants can all create linkages. Privacy coins begin from the observation made explicit in the CryptoNote whitepaper: a useful private payment system needs stronger properties than pseudonymity. In that framing, untraceability means that, for an incoming transaction, all plausible senders should be equiprobable. Unlinkability means that an observer should not be able to prove two outputs belong to the same recipient.
Those two properties are worth separating because they solve different leaks. If I can hide the recipient but still reveal exactly which old coin was spent, then sender privacy is weak. If I can hide the sender among decoys but every payment to you lands on the same public address, then recipient privacy is weak. A credible privacy coin has to break both kinds of linkage while keeping the accounting rules intact.
How can privacy coins hide transaction data while keeping validation possible?
The deepest idea behind privacy coins is that a blockchain does not actually need to reveal everything it verifies. It only needs enough information for validator to check a few conditions.
Those conditions are the heart of the system. A spend must be authorized by whoever controls the coin. The same coin must not be spent twice. The total value consumed must equal the total value created plus any fee. And the hidden values must still be well-formed; for example, not negative or absurdly out of range. If a protocol can prove those statements without disclosing the underlying transaction details, it gets privacy without abandoning consensus.
This is why privacy-coin design revolves around a small set of cryptographic building blocks. You need some way to hide the recipient while still letting the recipient detect and spend the payment. You need some way to hide or blur the sender while preserving the fact that exactly one legitimate input was authorized. You often need a commitment scheme so amounts stay hidden but still add up correctly. And you need some anti-double-spend marker that reveals reuse without revealing identity. The exact tools vary, but the architectural pattern repeats.
A useful way to think about it is this: transparent chains publish the whole equation and let everyone inspect it directly. Privacy coins publish commitments, proofs, and carefully chosen public markers instead. The network checks the proof rather than reading the plaintext.
How does Monero use one‑time keys, ring signatures, and key images for privacy?
Monero is the clearest example of a privacy coin where privacy is built into normal transaction flow rather than bolted on as an extra step. Its design descends from CryptoNote and combines three main mechanisms: one-time destination keys for recipients, ring signatures for sender ambiguity, and confidential transactions for amount hiding.
The first mechanism solves a common problem in public ledgers: if a user publishes a reusable address, then every incoming payment to that address can be linked. CryptoNote avoids this by turning a public address into a template, not a visible destination reused on-chain. When Alice pays Bob, she uses Bob’s public address material plus fresh randomness to derive a unique one-time public key for that specific output. She also includes a public value derived from her randomness so Bob, using his private view data, can recognize that the output is his and recover the corresponding one-time private key.
The important consequence is that outside observers do not see “payment to Bob’s public address” repeated over time. They see outputs addressed to distinct one-time keys. Bob can scan the chain and detect which ones belong to him, but an outsider cannot simply cluster all of Bob’s receipts by looking for repeated addresses. This is often described as a stealth-address mechanism, though the underlying CryptoNote construction is more specific than the casual label suggests.
Now consider spending. If Bob later wants to spend one of those outputs, a transparent system would simply reference that exact prior output and prove ownership with a signature tied to it. That would restore a clear chain link. Monero-style systems instead use a ring signature. Bob forms a ring containing his real output and several decoy outputs taken from the chain. The signature proves that one member of the ring is legitimately controlled by the spender, but it does not reveal which member is the real one.
This creates sender ambiguity, but it immediately raises a new problem. If the network cannot tell which ring member is real, how can it detect a double-spend? The answer is a key image. A key image is a public value deterministically derived from the real spending key in a way that lets the network spot reuse of the same underlying output. If the same output is spent again, the same key image reappears, so validators can reject it. Yet the key image is constructed so that seeing it does not tell outsiders which ring member was the true signer.
That combination is the mechanical heart of CryptoNote-style privacy. The ring signature says, in effect, “someone in this set is authorized.” The key image says, “and whoever that someone is, they have not spent this coin before.” The network gets the anti-double-spend guarantee it needs, while observers lose the direct pointer from spend to exact earlier output.
A concrete example helps. Imagine Bob received an output last month. Today he wants to pay Carol. His wallet selects that real output, then chooses several unrelated outputs from the blockchain as decoys. The transaction signature is built over the whole set, so a verifier can confirm that one of those outputs is genuinely spendable by Bob’s wallet, but not which one. Alongside the signature, the wallet publishes the key image tied to Bob’s actual spent output. Nodes check two things: the signature is valid for the ring, and this key image has never appeared before. If both hold, the network accepts the spend. An outside analyst can list the ring members, but cannot cryptographically prove which prior output funded Carol’s payment.
That is the intended mechanism. But the phrase intended matters, because ring-based privacy depends heavily on how decoys are selected and how many there are. The CryptoNote whitepaper already notes the core trade-off: larger rings improve ambiguity, but signature size grows roughly linearly with ring size. Better privacy costs more block space and usually more fees. Later Monero research showed that decoy selection matters just as much as ring size. If decoys are sampled in ways that do not resemble real spending behavior, the true spend can become statistically conspicuous.
This is not an edge case. Monero Research Lab papers and later empirical work documented chain-reaction and temporal-analysis weaknesses in earlier versions of the system. Historically, many transactions used no mixins at all, or used weak decoy-selection policies. Once some real spends become obvious, they can contaminate anonymity assumptions elsewhere, because outputs known to have been spent can still appear later as decoys. Researchers found that a substantial share of older Monero inputs were deducible under these conditions, and that “guess newest” heuristics worked surprisingly well because real spends tended to be newer than sampled decoys.
This does not mean ring signatures are pointless. It means privacy is not created by cryptography alone; it also depends on wallet defaults, protocol rules, and user behavior. Monero responded over time with protocol-level changes such as minimum mixin policies, RingCT, and later efficiency improvements including CLSAG and Bulletproofs-related upgrades. The lesson is broader than Monero: an anonymity set is only as good as the system that populates it.
Why do privacy coins hide amounts in addition to sender and recipient identities?
| Amount visibility | Deanonymization risk | Verification method | Proof size cost | Implementation complexity |
|---|---|---|---|---|
| Amounts visible | High (fingerprints) | Direct sum checks | Minimal | Low |
Even if sender and recipient links are blurred, visible amounts can still deanonymize users. Amounts act like fingerprints. If a transaction spends 3.141592 units and shortly afterward another transaction creates an output of the same unusual size, analysts can often narrow the possibilities dramatically. That is why mature privacy-coin designs usually try to hide amounts too.
The standard tool here is a commitment. In plain language, a commitment lets a wallet lock in a value while hiding it. The commitment is published on-chain, and later proofs show that the hidden values balance correctly. A common design, used in confidential-transaction systems, relies on homomorphic commitments such as Pedersen commitments. Homomorphic means that commitments can be added and subtracted in a way that mirrors addition and subtraction of the hidden values themselves.
That property is exactly what a blockchain needs. Validators do not have to know each hidden amount individually. They only need confidence that the sum of inputs equals the sum of outputs plus the fee. If commitments preserve arithmetic structure, nodes can check balance at the commitment level.
But there is another subtle issue. A commitment can hide a value while still allowing nonsense values unless the protocol proves the hidden amount lies in an acceptable range. Without such a proof, someone might try to create a commitment to a negative value and exploit the arithmetic to mint money invisibly. So confidential systems need range proofs: proofs that a hidden amount is non-negative and within allowed bounds.
Monero’s RingCT work extended the earlier CryptoNote design to hide amounts as well as senders and recipients, and later Bulletproofs dramatically reduced the size of these range proofs. That mattered because early confidential-transaction constructions had bulky proofs, which made private transactions expensive in bandwidth and storage. Bulletproofs reduced proof size to grow logarithmically with the witness size and avoided trusted setup, making confidential transactions more practical on-chain. This is a good example of privacy engineering being constrained by economics. A privacy mechanism that is cryptographically elegant but too large to use routinely will not create much real privacy in deployment.
How does Zcash use zero-knowledge proofs and nullifiers to achieve privacy?
| System | Sender privacy | Recipient privacy | Amount privacy | Anti-double-spend marker | Practical weakness |
|---|---|---|---|---|---|
| Monero | Ring signatures (probabilistic) | One-time stealth keys | RingCT confidential amounts | Key images | Decoy selection & ring size |
| Zcash (shielded) | zk‑SNARK proofs (proof‑based) | Encrypted shielded addresses | Hidden via commitments | Nullifiers | Shield adoption & usage patterns |
| Transparent Bitcoin | None (public graph) | Public addresses | Visible amounts | Explicit UTXO reference | Permanent traceability |
Zcash starts from a different design instinct. Instead of obscuring a spend among decoys, it aims to prove correctness of a shielded transaction directly with zero-knowledge proofs. In the Zcash model, a shielded value object is represented as a note. When a note is created, only a commitment to it appears publicly. That commitment is inserted into a note-commitment tree. When the note is later spent, the spender reveals a nullifier, a unique anti-double-spend marker tied to that note, and provides a zk-SNARK proof showing that they know a valid note in the tree, are authorized to spend it, and that the transaction balances according to protocol rules.
The nullifier plays a role similar in spirit to Monero’s key image: it lets the network detect duplicate spending without revealing which prior hidden object is being spent. But the surrounding mechanism is different. In Monero, ambiguity comes from a ring of plausible outputs. In Zcash, the proof says the spender knows some valid note consistent with the public commitments and consensus rules, without exposing which one.
This allows a stronger form of on-chain hiding in principle. The protocol specification emphasizes that Zcash bridges transparent Bitcoin-like payments and shielded payments protected by zero-knowledge proofs. In fully shielded usage, sender, recipient, and amount information can all be concealed while consensus still checks validity. Zcash also uses key-private encryption in its shielded address system so ciphertexts do not reveal which recipient key they target, and it supports viewing keys so a user can reveal incoming and outgoing note information without delegating spending authority.
The catch is that privacy in practice depends on how many users actually remain in the shielded pool and how they use it. Empirical work on deployed Zcash found an important gap between cryptographic capability and realized anonymity. It is possible to use Zcash privately, but many users and services interacted in ways that created recognizable patterns, and simple heuristics could shrink the effective anonymity set considerably. This is a recurring theme across privacy coins: the protocol may make privacy available, but optional privacy often leads to fragmented anonymity.
That is why the contrast between Monero and Zcash is not just “ring signatures versus zk-SNARKs.” It is also default privacy versus optional shielding, and statistical ambiguity versus proof-based concealment. Neither framing makes one system universally superior in all respects. Ring-based systems tend to expose different trade-offs in transaction size, decoy quality, and statistical analysis. zk systems tend to concentrate complexity in proving systems, trusted-setup questions for some constructions, implementation correctness, and practical shielded adoption. The right comparison is not which sounds more advanced, but which assumptions each design asks users and validators to rely on.
How do wallet behavior and network leaks undermine privacy coins?
A smart reader might assume that once transaction data is hidden, privacy is solved. But much of the risk sits outside the core spend proof.
Network observers may correlate transaction broadcast timing or IP-level metadata if wallets and nodes are careless. Monero’s own implementation guidance acknowledges operational precautions such as Tor integration and restricted public RPC operation because socket-level and node-level leaks can weaken user privacy even if the chain data itself is opaque. The cryptography can hide chain linkages and still leave room for network surveillance.
Wallet behavior matters too. If wallet software reuses patterns, chooses poor decoys, reveals view keys too broadly, or steers users into transparent flows for convenience, privacy degrades. The same is true for exchanges and merchants. A privacy coin may conceal on-chain details, but if a service records deposits, withdrawals, shipping addresses, and timestamps, then off-chain logs can still anchor an investigation. Privacy coins reduce the amount of information exposed by default; they do not create magical immunity from every source of correlation.
This is also why privacy and compliance debates often talk past the technical reality. The important technical point is simply that privacy coins change what the public ledger reveals. They do not erase all evidence, and they do not remove the need for trust decisions around custodians, endpoints, or software quality. Some systems, such as Zcash, intentionally include viewing keys for selective disclosure. That reflects a broader design truth: privacy is not always all-or-nothing. Sometimes users want public verifiability to the world; sometimes they want confidentiality to the world but inspectability to an auditor, accountant, or wallet service.
What legitimate use cases and monetary goals do privacy coins serve?
People often frame privacy coins only around illicit use, but that is too shallow to explain why the concept exists. Ordinary financial life contains many situations where full transparency is inappropriate. Salaries, supplier relationships, treasury operations, charitable donations, consumer purchases, and personal savings all reveal sensitive information when put on a public graph. A company may not want competitors inferring margins and counterparties. An individual may not want every payer to learn their full balance history. A donor may want to support a cause without creating a permanent public trail.
The monetary reason is even more fundamental. A currency works better when units are interchangeable. If coins carry visible, queryable histories, recipients can discriminate between “clean” and “tainted” units, even when the current holder did nothing wrong. Privacy mechanisms try to prevent that sort of history-based pricing and acceptance. In that sense, privacy coins are not only about secrecy; they are about preserving money-like behavior on an open ledger.
What are the main limitations and trade-offs of privacy coins?
| System | Primary failure mode | Root cause | Mitigation | User cost |
|---|---|---|---|---|
| Ring‑based systems | Temporal/decoy analysis | Poor decoy sampling | Enforce mixins; better sampling | Larger signatures, higher fees |
| zk‑based systems | Fragmented anonymity set | Optional shielding; usage leaks | Drive default shielded use and UX | Heavy prover resources |
| Confidential‑amount systems | Proof overhead and range gaps | Large or missing range proofs | Use Bulletproofs and aggregation | Longer sync; more CPU |
The main limitation of privacy coins is that they operate under assumptions that can weaken in deployment. Ring-based privacy weakens if decoys are poorly chosen or too few. Zero-knowledge systems weaken in practice if users keep moving between transparent and private pools in identifiable ways. Confidential amounts increase computational and proof overhead. More advanced proofs may reduce chain size but increase implementation complexity. And because the cryptography is subtle, bugs can have severe consequences: privacy loss, inflation bugs, or consensus failure.
There is also no free lunch between privacy and convenience. Strong privacy often makes wallets more complex, synchronization heavier, and transaction construction more expensive. It can complicate exchange integration and monitoring. Some of these are engineering costs, not conceptual flaws, but they matter because unused privacy features do not create much real privacy.
Finally, privacy is rarely absolute. Most systems aim for resistance to casual observers, blockchain analytics, and many forms of structured tracing. That is already a meaningful improvement over transparent ledgers. But the actual privacy achieved depends on the attacker’s side information, the user’s behavior, and the protocol’s current state. The honest claim is not “unbreakable anonymity.” It is that privacy coins try to minimize what the ledger itself reveals, and in good designs they do so without sacrificing the core consensus rules that keep a digital currency coherent.
Conclusion
Privacy coins are attempts to answer a hard question: can a public blockchain verify money without exposing everyone’s financial graph? Their answer is to replace visible transaction details with commitments, decoys, one-time keys, nullifiers, key images, and zero-knowledge proofs. The mechanisms differ, but the purpose is the same: preserve verifiability while reducing traceability.
The durable idea to remember is simple. Privacy in cryptocurrencies is not the absence of rules; it is the use of stronger cryptography so the network can enforce the rules without revealing more than it has to.
What should you know before using privacy coins?
Understand the privacy model, on-chain vs off-chain leaks, and whether the asset uses shielded transfers before you trade or move privacy coins. On Cube Exchange, check the asset page and deposit/withdrawal flow so you can fund, trade, or withdraw in the mode (shielded or transparent) that meets your privacy needs. Follow these concrete checks and actions to reduce operational, routing, and compliance surprises when working with privacy coins.
Frequently Asked Questions
Privacy coins use public, non-revealing markers that still detect reuse: Monero publishes a key image derived from the real spending key so nodes can spot double-spends without revealing which ring member was spent, and Zcash publishes a nullifier while proving in zero-knowledge that the spender knows a valid hidden note in the commitment tree. These markers let validators reject duplicate spends while keeping the spent object itself concealed.
Hiding identities but leaving amounts visible often lets analysts link inputs and outputs by matching unusual or distinctive values, so mature privacy designs hide amounts with commitments and range proofs so validators can check sums without learning individual values. Without range proofs, commitments could be manipulated (e.g., negative values) to create money out of thin air, so proving amounts lie in acceptable ranges is essential.
Common building blocks are one-time/stealth destination keys, ring signatures plus key images (for sender ambiguity and anti-double-spend), commitments (e.g., Pedersen) for amount hiding, range proofs to bound hidden values, and zero-knowledge proofs (zk‑SNARKs/zk‑SNARK-like systems) to prove correctness without revealing details. Which combo is used depends on the design trade-offs the protocol accepts.
Ring-based systems (like Monero) rely on statistical ambiguity from decoys and tend to be built for default-on privacy with simpler verifier costs but larger transaction sizes that scale with ring size; zk-based systems (like Zcash) use succinct zero-knowledge proofs to prove correctness directly, which can give stronger theoretical hiding but concentrate complexity in proof generation, trusted-setup and implementation correctness, and rely on users actually using the shielded pool. Neither approach is universally better - the practical privacy achieved depends heavily on defaults and real-world adoption.
If decoys are sampled poorly or rings are too small, the true input can become statistically conspicuous and deanonymization heuristics (e.g., “guess-newest”) can recover spends; empirical Monero research and follow-up studies showed early mixin/decoy choices allowed many inputs to be deduced. Thus ring privacy requires careful decoy-selection policies and sufficient ring sizes to work as intended.
No - privacy coins are not absolute. The article and empirical studies show on-chain hiding resists casual blockchain analytics, but effective anonymity depends on attacker side information, user and wallet behavior, protocol defaults, and off-chain logs; studies of deployed systems (e.g., Zcash) found real-world usage patterns can drastically shrink effective anonymity sets.
Commitments hide values but do not by themselves prevent invalid hidden values; range proofs prove hidden amounts are non-negative and within bounds. Bulletproofs are a practical range-proof construction that shrinks proof size (logarithmic growth) and avoids trusted setup, making confidential transactions much more efficient and deployable on-chain.
Network- and endpoint-level leaks remain major risks: transaction broadcast timing and IP metadata can correlate chain events to users; wallets that reuse patterns, leak view keys, or mix transparent and shielded flows reduce privacy; exchanges and merchants that record deposits/withdrawals create off-chain anchors that defeat on-chain hiding. Monero documentation and the article both recommend operational precautions (e.g., Tor integration, careful RPC exposure) because chain-level privacy does not eliminate these vectors.
Regulators and compliance bodies have highlighted challenges: FinCEN guidance and FATF discussion note that existing AML/CFT frameworks (e.g., the Funds Travel Rule) expect originator/beneficiary data, and privacy-enhancing designs complicate how obligated actors capture or transmit that information. The article notes compliance debates often conflate technical capability with policy requirements, so real-world legal obligations remain an important constraint on deployment and service integration.
Some privacy techniques can be added to Bitcoin-era ecosystems, but practical trade-offs vary: Zerocoin-style proofs were considered impractically large (~30 KB per proof) in early work, while coinjoin-style approaches (e.g., Wasabi Wallet) offer a practical, coordinator‑assisted mixing service that uses Tor for network privacy but has operational limitations (e.g., hot keys required, coordinator model). So privacy can be bolted on, but the costs and privacy guarantees differ from native privacy-coin designs.
Related reading