What Is Exchange Security Features?
Learn what exchange security features are, how they work, and why controls like passkeys, withdrawal allowlists, and API limits matter.
Introduction
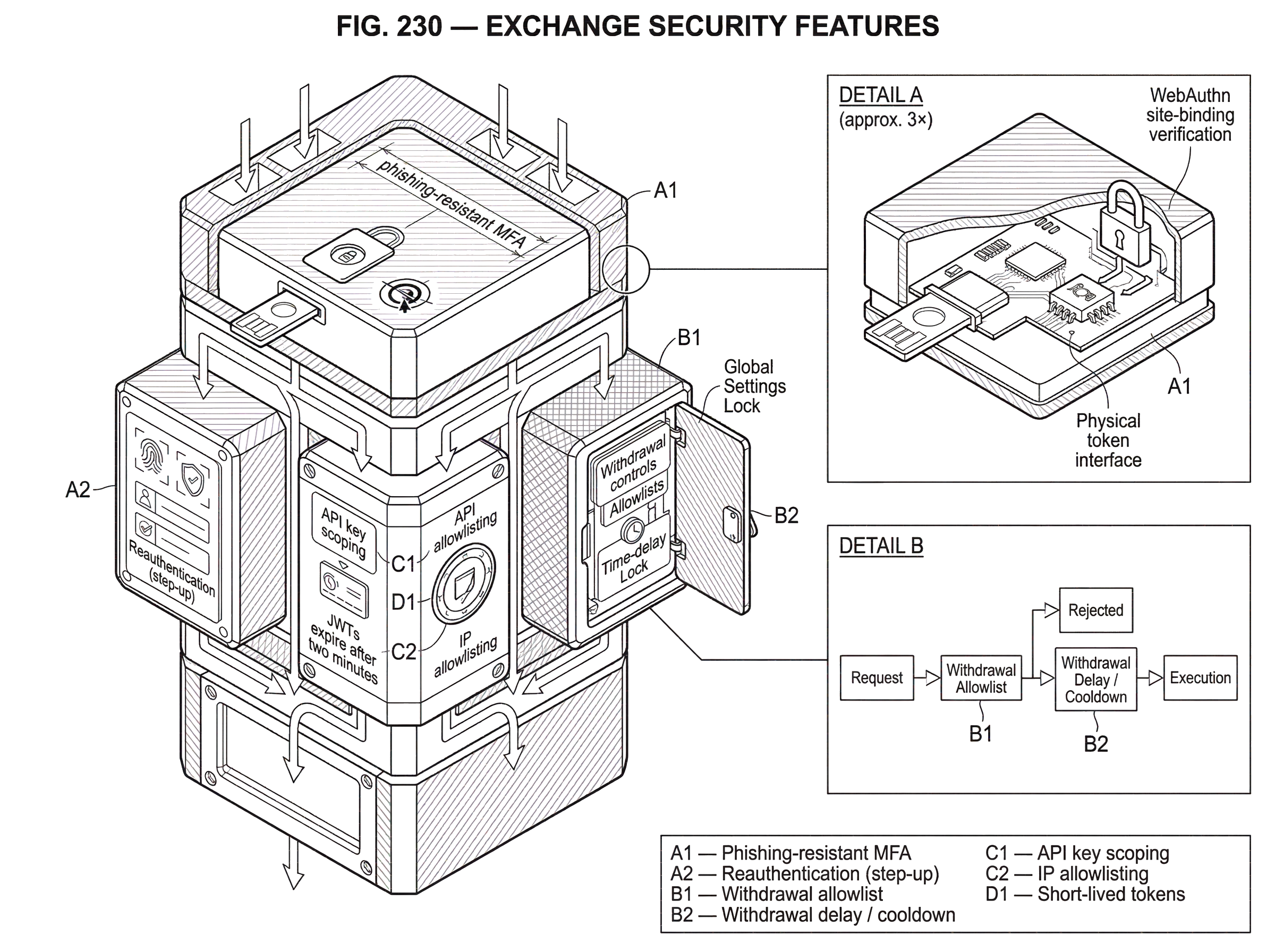
Exchange security features are the controls a trading platform uses to stop account takeover, unauthorized withdrawals, and misuse of API access. That matters because an exchange account is unusually high-value: if an attacker gets in, the goal is often not just to read data, but to change settings, create withdrawal destinations, or move assets out.
The useful way to think about these features is not as a checklist of toggles in a settings page. They are better understood as defenses placed along an attack chain. An attacker might steal a password, trick a user into approving a login, add a new withdrawal address, or compromise an API secret with transfer permission. Good exchange security features are designed to break that chain at multiple points, ideally before funds can move.
In practice, the strongest exchange security design combines three ideas. First, it makes login harder to phish. Second, it makes sensitive actions like withdrawals and API changes require stronger proof than ordinary browsing. Third, it limits what a stolen credential can do, so a single mistake does not automatically become a total loss.
How do exchanges prevent stolen credentials from becoming stolen funds?
A normal website mostly needs to answer, “Is this really the user?” An exchange has to answer a harder question: “Is this really the user, and should this session be allowed to change anything that can move money?” That distinction explains why exchange security often feels layered or inconvenient. The system is not only verifying identity once; it is continuously deciding how much trust to place in a user, a device, a session, and a specific action.
This is why basic username-and-password security is not enough. NIST’s authentication guidance makes the point clearly: stronger authentication raises the capability an attacker needs. A password can be guessed, reused from another breach, or captured in a phishing flow. Even one-time codes entered by hand are better than nothing, but they are not considered phishing-resistant, because a user can still be tricked into typing the code into an impostor site.
For exchanges, that difference is central. The most common real-world failure is not cryptography breaking; it is a human being being redirected, impersonated, rushed, or socially engineered. So the best modern security features do not merely add another code prompt. They change the authentication mechanism so the secret is not handed to the attacker in the first place.
Why are passkeys and FIDO/WebAuthn preferred for exchange logins?
| Authenticator | Phishing resistance | Usability | Recovery risk | Best for |
|---|---|---|---|---|
| Passkeys / hardware keys | High | User-friendly | Moderate | High-value accounts |
| PKI (enterprise) | High | Lower usability | High | Enterprise admins |
| Authenticator app OTP | Medium | Familiar | Low | General users |
| SMS / voice OTP | Low | Very easy | High | Legacy fallback |
The strongest login controls on an exchange are now built around phishing-resistant MFA, usually through FIDO/WebAuthn security keys or passkeys. Here is the mechanism. Instead of the user sharing a reusable secret with the site, the user’s device or security key holds a private key, and the exchange verifies a cryptographic response tied to the real site. That site-binding matters: a fake exchange page cannot successfully collect and replay the credential the way it can with a password or manually entered OTP.
NIST distinguishes between general multi-factor authentication and phishing-resistant methods. It explicitly says authenticators that rely on manual entry, such as OTPs or out-of-band codes, are not phishing-resistant. It also recognizes verifier name binding, such as WebAuthn, as a way to achieve phishing resistance. CISA goes further in practical terms and calls phishing-resistant MFA the gold standard, noting that FIDO/WebAuthn is the only widely available phishing-resistant authentication method today.
That has a direct consequence for exchange users. If your exchange supports passkeys or hardware security keys, those methods are usually protecting you against a different class of attack than SMS codes or authenticator-app codes. SMS and voice are among the weakest options because they can fail through phishing, SIM swaps, and telecom-layer issues. App-based OTP is stronger than SMS, but it still depends on the user noticing they are on the legitimate site. Passkeys and security keys reduce that burden by making the protocol itself reject the fake site.
There is a trade-off. Stronger authentication can be less forgiving when a device is lost or a user is not prepared for recovery. The FIDO Alliance emphasizes that moving to passkeys is not a one-day switch; the login flow and the recovery flow both have to be strengthened. Otherwise, an exchange may harden sign-in while leaving a weak account recovery process that attackers can exploit instead.
When and how do exchanges use step-up authentication for risky actions?
A well-designed exchange does not treat all actions as equally risky. Reading balances is not the same as creating an API key with transfer permission, changing 2FA settings, or adding a withdrawal address. So many exchange security features are really forms of step-up security: the system asks for stronger proof, or imposes a delay, when the action would materially increase the attacker’s ability to take funds.
This is where the idea behind authentication assurance levels is useful. NIST describes increasing assurance levels as requiring stronger proof and, at higher levels, phishing-resistant authenticators. An exchange may not label its controls as AAL1, AAL2, or AAL3, but the design principle still applies. Routine account access can have one threshold; withdrawals, admin actions, and privileged API operations should have a higher threshold.
A concrete example makes this easier to see. Imagine a user logs in from a familiar laptop and only wants to view positions. That is a lower-risk event. Now imagine the same session tries to disable 2FA, create a new API credential, and add a fresh withdrawal address. A security-conscious exchange should not treat that as “already authenticated, so allowed.” It should either require a phishing-resistant reauthentication, impose a waiting period, or block the action until additional controls are satisfied. The mechanism is simple: high-risk changes are separated from ordinary login so a single stolen session does not immediately grant full control.
How do withdrawal allowlists, delays, and locks prevent rapid theft?
| Control | What it stops | Delay / detection | User friction | Best for |
|---|---|---|---|---|
| Address allowlist | Blocks new destinations | No delay | Low friction | Standing balances |
| Activation delay | Slows attacker withdrawals | Detection window | Medium friction | New address additions |
| Account-level lock (GSL) | Prevents critical changes | Configurable delay | Medium-high friction | High-risk accounts |
| Manual review | Catches suspicious transfers | Variable | High friction | Large withdrawals |
The most exchange-specific security features usually appear around withdrawals, because that is where account compromise becomes irreversible loss. The simplest version is a withdrawal address allowlist: funds can only be sent to addresses the user has pre-approved. This works because it narrows the attacker’s freedom. Even if someone gains account access, they cannot immediately invent a new destination and drain the account if withdrawals are restricted to known addresses.
Often this control becomes more effective when paired with time. Some exchanges also use activation delays, cooldowns, or account-level locks before newly added addresses can be used or before certain security settings take effect. The reason is not arbitrary friction. The delay creates a detection window. If an attacker adds a malicious address or changes a critical setting, the legitimate user has time to notice the alert and respond before funds leave.
Account-level locks apply the same idea more broadly. Kraken’s documented metadata around Global Settings Lock describes a control intended to prevent changes to withdrawal addresses, 2FA, and API settings, with an unlock delay and master-key override. Even without relying on every implementation detail, the design logic is clear: some settings are so powerful that the safest default is to freeze them unless the user deliberately unlocks them ahead of time. That makes urgent, attacker-driven changes much harder.
These controls are especially useful for users who keep meaningful balances on an exchange, use the platform operationally, or know they may be vulnerable to phishing and social engineering. They are less important for a person who only deposits, trades briefly, and withdraws immediately; but that is exactly the point. Exchange security features are tuned to protect the scenarios where an account holds standing value.
How should API keys be scoped and limited to reduce blast radius?
| Control | Attack mitigated | Blast radius | Operational cost | Best for |
|---|---|---|---|---|
| Permission scoping | Prevents unauthorized transfers | Small blast radius | Low cost | Trading bots |
| IP allowlisting | Blocks requests off-network | Small blast radius | Medium cost | Server-hosted integrations |
| Short-lived tokens | Limits leaked token lifetime | Minimal blast radius | High cost | High-security integrations |
| Rotation & revocation | Removes compromised keys | Variable blast radius | Medium cost | All API users |
For active traders, funds are not only exposed through the web login. They are also exposed through API keys. That changes the security problem. With API access, the question is not just “Can someone log in?” but “What can a leaked machine credential do?”
Coinbase’s developer documentation gives a good picture of the model. API keys are meant to access your own account, not other users’ accounts. They can be scoped by permission, and the documentation explicitly warns that if someone obtains an api_secret with transfer permission, they can send all digital currency out of the account. That is the security story in one sentence: a machine credential can be as dangerous as a compromised password, or worse, if its permissions are broad.
So the relevant exchange security features for API users are controls that reduce blast radius. Permission scoping means a key used for reading balances or placing orders should not also be able to withdraw. IP allowlisting means even a stolen key should fail outside approved network locations. Short-lived tokens go further by reducing how long a captured credential remains useful. Coinbase’s approach of generating JWTs that expire after two minutes is an example of this design: the system is trying to make secrets less reusable and less durable.
This is who those controls are for: traders using bots, firms automating treasury or execution, and anyone integrating exchange accounts into software. For them, the security risk is often not a phishing email but a leaked environment variable, a badly scoped key, or an application deployed from the wrong host. The protective mechanism is therefore different: less about user prompts, more about minimizing privilege and constraining where credentials work.
Which exchange security signals protect accounts versus which signal solvency?
Some exchange security features help with authentication directly; others help users detect impersonation. Anti-phishing codes, for example, are useful because they let a user recognize whether an exchange email contains a code or phrase that only the real service should know. That can reduce some forms of email spoofing and social engineering. But it is important to be precise about what such a feature does and does not do. It helps the user authenticate the message; it does not make the login protocol itself phishing-resistant in the way passkeys do.
The same need for precision appears with proof of reserves. It is often presented alongside exchange trust and security messaging, but it solves a different problem. Authentication features protect against account compromise. Proof-of-reserves claims are about whether an exchange appears to hold certain assets. And even there, both the PCAOB and SEC have warned that third-party proof-of-reserve reports are inherently limited, not audits, and may not address liabilities, borrowing, ongoing availability of assets, or internal controls. So they should not be treated as a substitute for account-level security or as a complete picture of exchange safety.
What does good exchange security look like in practice?
A strong exchange security posture usually has a recognizable shape. Login supports phishing-resistant methods such as passkeys or hardware security keys. Sensitive actions require reauthentication or stronger factors than routine browsing. Withdrawal destinations can be restricted, and changes to critical settings are delayed or locked. API credentials are scoped narrowly, stored carefully, and ideally limited by IP and token lifetime. Recovery is treated as part of the security model, not as an afterthought.
A weaker posture tends to have the opposite shape. It may advertise “2FA” but rely mainly on SMS or manually entered codes. It may protect login but not withdrawals, or allow a single successful login to change every important setting immediately. It may issue API credentials that are broad, long-lived, and usable from anywhere. In that design, security exists as a feature label, but not as a system of barriers.
Conclusion
Exchange security features are best understood as controls that interrupt the path from stolen credentials to stolen funds. The strongest ones do not merely ask the user for more codes; they change the protocol, restrict risky actions, and limit what any single credential can do. If you remember one thing, make it this: on an exchange, the real question is not whether security features exist, but whether they break the specific attack chain an adversary would actually use.
What security features should you look for in an exchange?
Look for phishing-resistant login, strict withdrawal controls, and narrowly scoped API keys; those three controls stop the most common attack chains that turn a breached account into lost funds. Cube Exchange supports WebAuthn/passkeys and hardware security keys, withdrawal allowlists with activation delays, and fine-grained API permissions so you can evaluate and enable these protections in your account settings.
- Open Cube Exchange > Security settings and register a passkey or hardware security key (WebAuthn) as your primary MFA.
- Enable a withdrawal allowlist, add your trusted addresses, and turn on an activation delay (for example, 24–72 hours) before new addresses are usable.
- Create API credentials scoped only to the permissions you need (read or trade only); disable withdraw/transfer on those keys, add IP allowlisting, and set a short token lifetime or rotate keys daily.
- Register a secondary recovery key or passkey and enable account-level locks or alerts for changes to 2FA, API keys, or withdrawal settings.
Frequently Asked Questions
Phishing-resistant methods like FIDO/WebAuthn (passkeys or hardware security keys) make credential use site‑bound so a fake site cannot successfully collect and replay the credential, greatly reducing phishing risk - but they do not eliminate other attack paths such as weak account recovery flows or social engineering of the user, so recovery and other controls must also be hardened.
The main trade-off is usability versus resilience: passkeys and security keys raise the bar for attackers by making credentials non‑replayable and site‑bound, but they are less forgiving if a device is lost or migration/recovery is not well planned, so organisations must strengthen login and recovery flows when they adopt them.
SMS and voice OTPs are among the weakest options because they can fail via SIM‑swap and telecom attacks, and manually entered OTPs (including most authenticator apps) are not considered phishing‑resistant by NIST; app‑based OTP is stronger than SMS but still vulnerable to phishing where users are tricked into entering codes.
Withdrawal allowlists and activation delays work by narrowing where funds can be sent and by creating a detection window: an attacker who adds a malicious address cannot immediately withdraw to an arbitrary destination, and a cooldown or delay gives the legitimate user time to notice and respond before funds leave.
For API credentials, effective controls are permission scoping (separating read/trade from transfer rights), IP allowlisting, and short‑lived tokens - these reduce the blast radius of a leaked secret; Coinbase’s developer docs illustrate this approach with short‑lived JWTs and recommended IP allowlists.
Step‑up security means requiring stronger proof or extra controls for higher‑risk actions (like creating withdrawal addresses, changing 2FA, or issuing transfer‑capable API keys) rather than treating every authenticated session the same; it can be implemented via reauthentication with phishing‑resistant factors, delays, or explicit locks on sensitive settings.
Proof‑of‑reserves addresses whether an exchange appears to hold certain assets at a point in time, but it is not an account‑level security control and third‑party PoR reports are limited: they are point‑in‑time procedures and may omit liabilities or ongoing availability, so they should not be treated as a substitute for robust authentication and withdrawal controls.
Anti‑phishing codes help users detect spoofed messages or emails from impostor sites, but they do not change the login protocol itself into a phishing‑resistant mechanism - only cryptographic, site‑bound authenticators like WebAuthn provide that class of protection.
Losing a security key or a passkey‑capable device can leave you locked out if the exchange’s recovery paths are weak; the article and FIDO guidance stress that adopting phishing‑resistant authenticators requires strengthening the recovery and lifecycle processes to avoid creating weaker fallback vulnerabilities.
Related reading