What is a Soft Fork?
Learn what a soft fork is in blockchain, how backward-compatible consensus upgrades work, why they matter, and how activation differs from hard forks.
Introduction
Soft fork is the name for a backward-compatible change to a blockchain’s consensus rules. That phrase gets repeated so often that it can become less helpful than it sounds. The important question is not merely whether old nodes keep running, but why they can keep running at all when the rules have changed.
The key fact is this: a soft fork works by making previously valid behavior more restrictive, not by permitting brand-new behavior that old nodes would reject. In other words, the upgraded network agrees to accept a smaller set of blocks or transactions than before. Because every block that satisfies the new stricter rules also satisfies the old looser rules, non-upgraded nodes can still follow the chain. They may not fully understand the new constraints, but they do not see compliant blocks as invalid.
That makes soft forks one of the central tools for evolving a blockchain without forcing every participant to upgrade at the same moment. But that convenience comes with a tradeoff: backward compatibility is achieved partly by letting old nodes remain permissive in places where upgraded nodes have become strict. That gap is useful, yet it is also where most of the subtlety and risk lives.
What does it mean that a soft fork ‘shrinks the valid set’?
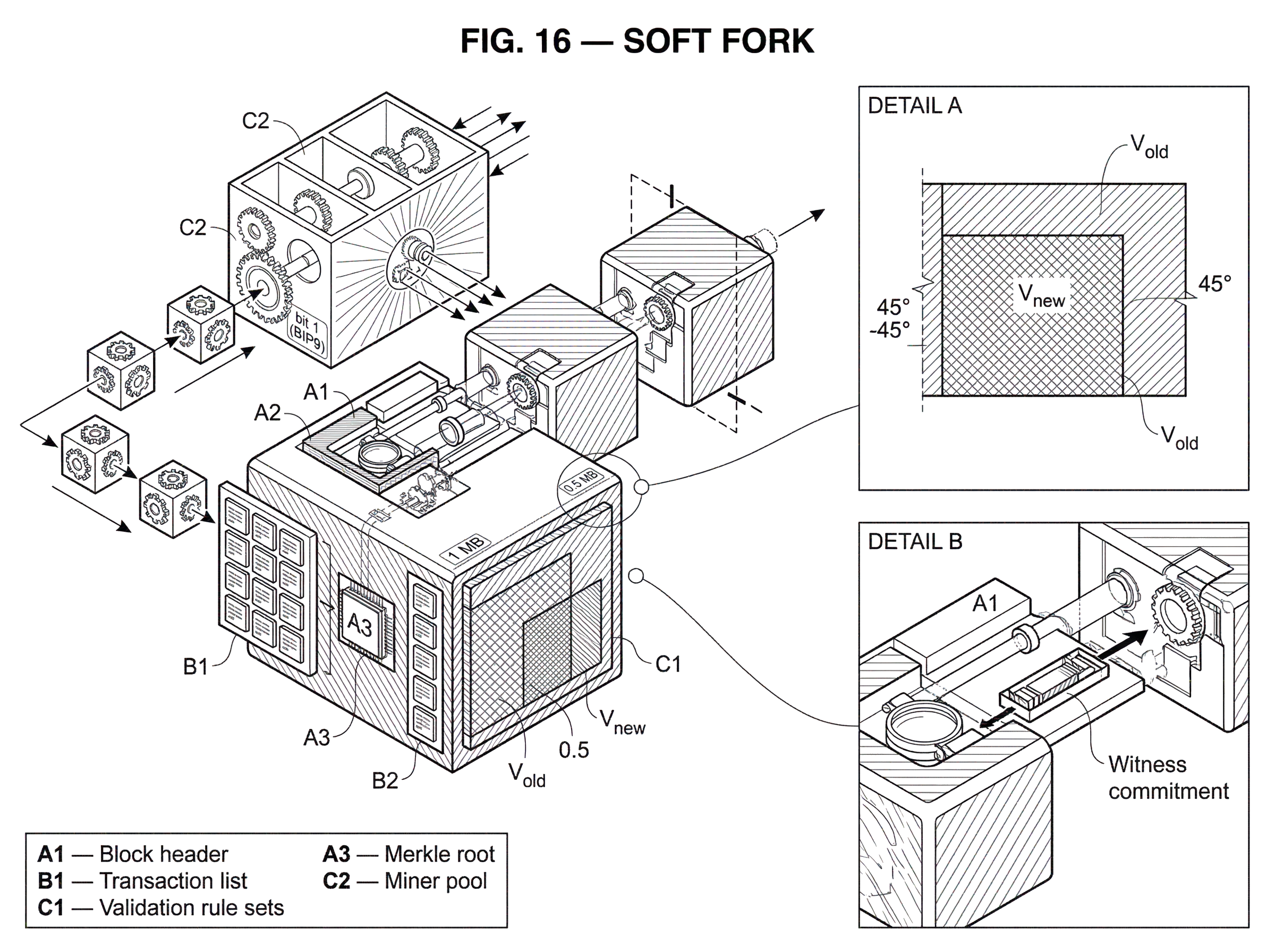
| Change type | Valid-set relation | Old-node effect | Upgrade requirement | Risk of lasting split | Common purpose |
|---|---|---|---|---|---|
| Soft fork | Vnew ⊂ Vold | Old nodes still accept blocks | Optional to remain on chain | Low | Tighten rules while preserving continuity |
| Hard fork | Vnew ⊄ Vold | Old nodes may reject new blocks | Required for compatibility | High | Introduce incompatible features or expand validity |
The cleanest way to understand a soft fork is to forget names like Bitcoin or Ethereum for a moment and think in terms of validity sets.
Every blockchain node has a rulebook for deciding whether a block is valid. Imagine the set V_old as all blocks the old software would accept. After an upgrade, the new software has its own set V_new. A change is a soft fork when V_new is a subset of V_old. Put plainly, the new node says, “I still accept many of the things you accepted before, but not all of them anymore.”
That subset relation is the whole mechanism. If miners or validators produce blocks from V_new, then old nodes also accept those same blocks, because those blocks were already inside V_old. So the network can move onto the new rules without instantly ejecting everyone who has not upgraded.
A hard fork flips that relation. In a hard fork, some blocks in V_new are not in V_old. Old nodes reject them outright. That is why hard forks require coordinated upgrades from everyone who wants to stay on the same chain.
This “shrinking the valid set” view also explains what soft forks are good at. They can add restrictions, reinterpret reserved space, disable old behaviors, or require extra commitments that old nodes do not examine. What they cannot do easily is arbitrary expansion of what counts as valid. If the new rule would make old nodes reject upgraded blocks, it is not a soft fork.
A simple fictional example helps. Suppose a chain originally allows blocks up to 1 MB, and the upgraded rule lowers the limit to 0.5 MB. Upgraded nodes reject any block larger than 0.5 MB. Old nodes still accept those smaller blocks, because 0.5 MB was already within the old 1 MB limit. So the chain can continue without old nodes splitting away, as long as block producers follow the new smaller limit. The failure mode is equally revealing: if a non-upgraded miner produces a 0.8 MB block, old nodes may accept it, but upgraded nodes reject it. That block will likely be orphaned if enough upgraded hashpower enforces the new rule.
The example is artificial, but the structure is real. A soft fork is not magic compatibility. It is compatibility created by asymmetry: old nodes are more permissive, new nodes are more strict.
Why do blockchains use soft forks instead of only hard forks?
A blockchain that can never change is not really robust; it is merely frozen. Bugs are found. Denial-of-service limits need tuning. Signature systems age. New script features become useful. Privacy and scalability improvements may depend on new transaction forms. If every consensus change required a hard fork, upgrading would often mean a clean coordination deadline where laggards fall off the network immediately.
Soft forks exist because decentralized systems need a way to evolve while preserving as much continuity as possible. They lower the coordination burden. Exchanges, merchants, wallet providers, and ordinary users do not all have to upgrade on the same day just to keep recognizing the latest chain tip.
But the problem soft forks solve is narrower than “upgrades in general.” They solve the specific problem of changing consensus rules while preserving acceptance by old nodes. They do not remove the need for social coordination, implementation work, testing, or activation planning. In practice, a soft fork often succeeds only because a network also has a credible process for getting miners, validators, client developers, and major infrastructure operators aligned enough to enforce the stricter rules.
This is why soft forks sit at the boundary between protocol design and governance. The technical design is the subset relation. The operational question is how enough of the network begins enforcing that subset at the same time.
How do old and upgraded nodes see blocks differently during a soft fork?
The phrase “backward-compatible” can be misleading because it sounds like everyone sees the same thing. They do not.
An upgraded node validates both the old rules and the new restrictions. A non-upgraded node validates only the old rules. If an upgraded block obeys the new restrictions, both nodes accept it. If a block violates the new restrictions but still obeys the old rules, the non-upgraded node may accept it while the upgraded node rejects it.
That asymmetry has two immediate consequences.
First, old nodes are not giving full security guarantees after a soft fork if they do not understand the new rule. They may still track the chain, but they are outsourcing some validation to the upgraded majority. This is why Bitcoin soft-fork specifications repeatedly note that older software continues operating, yet may treat new constructions permissively. In SegWit, for example, non-upgraded nodes do not validate witness data and treat witness programs as effectively anyone-can-spend, even though upgraded nodes enforce the actual spending conditions. Taproot has a similar property for SegWit version 1 outputs: older software keeps running, but does not fully validate the new witness program semantics.
Second, enforcement depends on upgraded block producers and economically relevant nodes actually rejecting non-compliant blocks. If very few participants upgrade, the stricter rules are mostly theoretical. The NIST overview puts this plainly: if no or very few nodes upgrade, the updated rules will not be followed. A soft fork is backward-compatible, but it is not self-executing.
This is a common misunderstanding. People sometimes say a soft fork is “safe because old nodes still work.” More precisely, old nodes can still track the chain, but they may no longer be independently verifying all of the conditions that define validity under the upgraded protocol.
How do soft forks repurpose ignored fields or opcodes in practice?
A successful soft fork usually takes one of two shapes.
The first shape is to tighten an existing rule. Reducing a limit, requiring a stricter form of script execution, or invalidating a previously allowed edge case all fit this pattern. Here the mechanism is direct: new nodes simply reject some behavior that old nodes would still allow.
The second shape is subtler: use space or behavior that old nodes already ignore or treat permissively, then assign it stricter meaning for upgraded nodes. Bitcoin has done this repeatedly. An old opcode that effectively did nothing can be redefined to impose a real condition, as happened when OP_NOP2 was repurposed as CHECKLOCKTIMEVERIFY. Older nodes still treat the opcode as harmless and so do not reject the transaction; upgraded nodes apply the new rule and reject spends that fail the locktime requirement.
SegWit is a more sophisticated example of the same design philosophy. Its witness data is committed separately, nested through the coinbase transaction so that the new information can be anchored to the block without breaking older block validation. The result is a consensus change that old nodes still accept as blocks, while upgraded nodes enforce additional rules around witness structure, witness transaction identifiers, and block weight. The witness commitment mechanism was chosen precisely because it made the change soft-fork compatible.
Taproot continues this pattern. It defines new rules for SegWit version 1 witness programs, while older nodes still see those programs in a permissive way. The design also reserves room for future extensions, which is another recurring soft-fork idea: if you reserve version bits, opcode behavior, or commitment fields today, you create places where stricter meaning can be introduced tomorrow.
The analogy here is a contract with blank fields that older readers ignore but newer readers agree must contain valid data. That analogy explains how compatibility is preserved. Where it fails is that blockchains are not merely interpreting optional text; they are enforcing consensus. If too many participants disagree about whether the blank field matters yet, the result is orphaned blocks or chain instability, not harmless ambiguity.
How did SegWit deploy as a soft fork?
SegWit is worth examining because it shows how a major feature change can still fit soft-fork logic.
Before SegWit, transaction signatures and scripts were part of the transaction data committed in the traditional transaction identifier path. SegWit introduced a separate witness structure containing data needed to validate the spend but not to determine the transaction’s effects in the UTXO set. It also introduced a witness-aware identifier, wtxid, while preserving the original txid definition.
The puzzle is obvious: how can moving important validation data around be backward-compatible? Wouldn’t older nodes reject blocks they cannot fully interpret?
The mechanism is that witness data is committed separately and anchored through the coinbase transaction in a way older nodes do not need to understand in order to keep recognizing the block as valid under the old rule set. Upgraded nodes, however, check the witness commitment and enforce the new spending rules. Older nodes continue seeing the transaction outputs and their effects, but they do not validate the witness itself.
That gives two benefits at once. Mechanically, it enables the change to deploy as a soft fork. Functionally, it removes nonintentional transaction malleability and supports more advanced constructions such as trust-minimized chains of unconfirmed transactions, which matter for systems like the Lightning Network.
But it also exposes the exact boundary of soft-fork backward compatibility. Older nodes are still participating, yet they are no longer performing the full validation that upgraded nodes perform. So “compatible” does not mean “equivalent.” It means “able to stay on the same chain if others enforce the stricter rule.”
How is activation different from the soft-fork rule change?
| Method | Who enforces/signals | Trigger | Activation guarantee | Main operational risk |
|---|---|---|---|---|
| BIP9 | Miners via version bits | Threshold reached in signalling windows | No guarantee if miners hold out | Signalling stalls upgrade |
| BIP8 (no lockin) | Miners via block-height windows | Height-based activation window | No guarantee without miner support | Same miner-cooperation risk |
| BIP8 (lockin) / UASF | Users/nodes enforce by deadline | Lock-in on timeout forces activation | Can force activation | May follow lower-work chain / cause reorgs |
A soft fork has two distinct parts: the new rule and the activation method.
The rule says what becomes invalid after activation. The activation method says how the network coordinates the moment when nodes start enforcing that new invalidity. These are separate design problems. Many public discussions blur them together, which makes contentious upgrades harder to understand.
Bitcoin’s BIP9 is the classic miner-signalling mechanism. It repurposes the block header nVersion field as a bit vector so multiple soft-fork deployments can be tracked in parallel. Each deployment has parameters such as a name, a bit position, a start time, and a timeout. Nodes compute a deployment state machine over retarget periods: DEFINED, STARTED, LOCKED_IN, ACTIVE, or FAILED. If enough blocks in a signalling window set the relevant bit, the deployment locks in and later becomes active.
The important insight here is that version bits do not make the soft fork safe by themselves. They are a coordination signal. They tell nodes and miners when enough support appears to exist for enforcement to begin. BIP9 also includes warnings for “unknown upgrades,” precisely because a node may detect that miners are signalling for rules the software does not understand.
BIP8 modifies this basic approach. Instead of time-based start and timeout values, it uses block heights, because wall-clock block time is noisy. It also adds a lockinontimeout option, which can guarantee eventual activation. That guarantee comes with operational caveats: the BIP explicitly notes that nodes may, for a period, follow a lower-work chain or require careful peering to avoid partitioning if activation becomes contentious.
These activation schemes matter because a soft fork’s subset property only helps once enough of the network begins enforcing the stricter subset together. Before that, the new rule is just code sitting idle in binaries.
Why does soft-fork activation become politically contentious?
The technical elegance of soft forks sometimes hides a governance reality: someone must decide when the new stricter rules are enforced, how much support is enough, and what happens if signalling stalls.
SegWit’s activation debate made this visible. BIP141 specified the SegWit consensus change and deployed it through BIP9 version bits on bit 1. But miner signalling did not initially reach the threshold quickly, which led to alternative activation strategies. BIP148 proposed a user-activated soft fork with a flag day: during a defined enforcement window, nodes running BIP148 would reject blocks that did not signal for SegWit. The idea was to make non-signalling blocks economically unattractive by orphaning them.
BIP91 proposed a different route: a reduced-threshold miner-activated soft fork that required signalling for SegWit once enough support for the intermediate mechanism existed. In both cases, the underlying SegWit rules were not the only issue. The conflict was over who coordinates activation and under what conditions the stricter rule begins to bite.
This reveals something fundamental. A soft fork is backward-compatible at the level of rule sets, but activation can still be contentious because enforcement changes profit, risk, and bargaining power. If a large minority refuses to enforce, temporary splits, reorgs, or operational confusion are possible even though the change is “just” a soft fork.
So the usual slogan (“soft forks don’t split chains”) is too strong. The more accurate statement is: soft forks are designed to avoid permanent incompatibility with old nodes, but poorly coordinated or contentious activation can still create chain instability or temporary divergence.
Which protocol changes are suitable for soft forks and which are not?
| Outcome | Why a soft fork fits | When unsuitable | Engineering cost |
|---|---|---|---|
| Tighten validation rules | New rules are a strict subset of old rules | If change requires new valid forms | Low to moderate |
| Reinterpret ignored fields | Old nodes ignore or treat the field permissively | If no reserved affordances exist | Moderate; careful compatibility design |
| Add new valid forms | Cannot make old nodes accept new forms | When feature expands validity set | Not feasible as a soft fork |
The strength of a soft fork is that it lets a network add restrictions without requiring everyone to upgrade immediately. This makes it well suited for new signature rules, script-system extensions, opcode reinterpretations, additional commitments, and resource-accounting changes that can be encoded as stricter acceptance conditions.
That is why major Bitcoin upgrades such as CHECKLOCKTIMEVERIFY, SegWit, and Taproot were designed as soft forks. In each case, the protocol gained meaningful new capability by narrowing permissible validation behavior or by assigning stricter meaning to structures that older nodes handled permissively.
The limitation is just as important. If a desired feature requires old nodes to accept something they currently reject, then a soft fork is the wrong tool. Likewise, if the new feature is so opaque to old nodes that the ecosystem cannot tolerate the resulting trust gap, backward compatibility may be less valuable than it first appears.
There is also a design cost. Soft forks often produce more complex constructions because they must fit into what the old protocol already tolerates. The engineering is constrained by the need to hide the new rule inside old validity. That can lead to clever but intricate designs, especially in mature systems with long compatibility histories.
How do other blockchains handle upgrades differently from Bitcoin-style soft forks?
The term “soft fork” is most at home in systems like Bitcoin, where old and new validation rules coexist during decentralized rollout and backward compatibility has sharp consensus meaning. Other blockchain families sometimes solve the underlying problem differently.
Ethereum, for example, coordinates consensus-changing upgrades through the EIP process and client implementation coordination. The EIP framework clearly covers changes to block and transaction validity rules, but Ethereum’s major network upgrades have generally been coordinated as network-wide forks rather than relying on the classic Bitcoin-style soft-fork pattern.
The surrounding problem is still familiar but the compatibility strategy differs.
- propose the change
- build consensus
- ship implementations
- coordinate activation
Cosmos SDK chains often use the x/upgrade module, which schedules an upgrade at a specific block height and intentionally halts the state machine until operators run the new binary. That is almost the opposite of the soft-fork idea. Rather than preserving continued acceptance by old nodes, it coordinates a clean upgrade stop.
Polkadot pushes even further from the classic soft-fork model through runtime upgrades, where chain logic can change without asking every validator to install a traditional new binary in the same way. The underlying goal is still protocol evolution, but the mechanism is often described as “forkless upgrades” rather than soft forks.
These contrasts are useful because they show what is fundamental and what is conventional. The fundamental problem is upgrading consensus safely in a decentralized environment. The classic soft fork is one solution: make the valid set smaller so old nodes can still follow along. Not every blockchain architecture chooses that solution.
What are the main risks to watch for with soft forks?
The first underestimated risk is false comfort from backward compatibility. Old nodes staying online does not mean they retain full verification power. In soft forks like SegWit and Taproot, non-upgraded nodes may accept outputs or spends in a permissive way and rely on upgraded nodes to enforce the true new conditions.
The second is activation risk. Signalling thresholds, timeouts, mandatory signalling periods, and flag days are not ceremonial details. They are the operational machinery that decides whether the network converges smoothly or enters a period of uncertainty. BIP9’s state machine, BIP8’s MUST_SIGNAL logic, and UASF-style proposals all exist because decentralized networks need explicit rules for the transition, not just for the endpoint.
The third is biting off too much novelty under the banner of compatibility.
A soft fork works best when the old protocol has reserved affordances that can be reinterpreted cleanly.
- ignored opcodes
- version fields
- witness versions
- commitment slots
When designers have to contort the protocol too much to preserve backward compatibility, the result may be hard to reason about or operationally brittle.
Conclusion
A soft fork is a consensus upgrade that stays backward-compatible by making validity rules stricter: the new valid set is a subset of the old one. That is the whole idea, and it explains both the appeal and the hazard.
The appeal is graceful evolution. Old nodes can keep following the chain while the network adopts stronger rules. The hazard is that old nodes may no longer verify everything themselves, and activation still requires real coordination. If you remember one sentence tomorrow, make it this: a soft fork works not because old nodes understand the new rules, but because upgraded nodes enforce stricter rules that old nodes would have accepted anyway.
What should you understand before using this part of crypto infrastructure?
Soft Fork should change what you verify before you fund, transfer, or trade related assets on Cube Exchange. Treat it as an operational check on network behavior, compatibility, or execution timing rather than a purely academic detail.
- Identify which chain, asset, or protocol on Cube is actually affected by this concept.
- Write down the one network rule Soft Fork changes for you, such as compatibility, confirmation timing, or trust assumptions.
- Verify the asset, network, and transfer or execution conditions before you fund the account or move funds.
- Once those checks are clear, place the trade or continue the transfer with that constraint in mind.
Frequently Asked Questions
A soft fork narrows the set of blocks or transactions considered valid (V_new ⊂ V_old) so old nodes still accept upgraded blocks, while a hard fork expands or changes validity in ways old nodes would reject, requiring coordinated upgrades.
Old nodes remain able to track and accept blocks after a soft fork because every block that obeys the new stricter rules also met the old rules, but they often lose the ability to independently verify the new constraints (for example, non-upgraded nodes do not validate SegWit witness data and therefore treat some outputs as effectively anyone-can-spend).
Activation is the coordination process that decides when nodes start enforcing the stricter rules; it is separate from the rule change itself because the subset property only helps once enough block producers and economically relevant actors actually refuse non-compliant blocks.
Common Bitcoin-style activation mechanisms include BIP9 (miner signalling with a state machine and timeout) and BIP8 (height-based triggers with an optional lockinontimeout); their trade-offs include signalling visibility, timing reliability, and the risk that lockinontimeout=true can cause nodes to follow a lower-work chain or require preferential peering.
Yes - soft forks can still produce temporary chain instability, orphaned blocks, or reorgs if activation is poorly coordinated or a sizable minority refuses to enforce the new rules, because enforcement depends on actual upgraded hashpower or validators rejecting non-compliant blocks.
Soft forks work well for adding restrictions or reinterpreting ignored/reserved fields (examples: CHECKLOCKTIMEVERIFY from OP_NOP2, SegWit’s witness commitment, and Taproot’s SegWit v1 rules) but cannot easily enable protocol changes that require old nodes to accept things they currently reject.
Designs often reuse or repurpose parts of the old protocol that older nodes treat permissively - Bitcoin repurposed an unused opcode into CHECKLOCKTIMEVERIFY and anchored witness data so older nodes could still see blocks as valid while upgraded nodes enforced new semantics.
People commonly underestimate three risks: the false comfort that old nodes fully validate (they often don’t), activation risk around signalling thresholds and timing, and engineering complexity when squeezing new behavior into what the old protocol tolerates.
Blockchains take different approaches: Ethereum coordinates network-wide upgrades via the EIP process, Cosmos schedules height-based binary upgrades with the x/upgrade module, and Polkadot uses runtime upgrades for forkless changes - these alternatives trade the soft-fork subset trick for explicit coordinated upgrades or different upgrade primitives.
Related reading