What Is Restaking?
Learn what restaking is, how it reuses staked assets to secure new services, why it improves capital efficiency, and where its risks come from.
Introduction
Restaking is the idea of using already-staked assets to secure additional services beyond the base blockchain they were originally staked for. It matters because proof-of-stake systems tie security to capital: the more stake that can be credibly penalized for bad behavior, the harder the system is to attack. Restaking asks whether that same economic security can be reused instead of rebuilt from scratch for every new service.
That sounds almost too convenient. If one dollar of stake can protect several systems, why would anyone ever bootstrap security the old way? The puzzle is that the same feature that makes restaking attractive (reusing collateral) is also what makes it dangerous. The mechanism creates efficiency by stacking promises on top of the same stake, which means failures can become correlated.
The basic intuition is simple. In ordinary staking, a validator or delegator locks assets to help secure a network's consensus rules. If they misbehave under those rules, some of that stake can be slashed. In restaking, the staker opts into additional rules, usually on behalf of external services, middleware, or applications. That same stake is now backing more than one commitment. The reward is potentially higher yield or incentives; the cost is potentially more slashing exposure and more operational complexity.
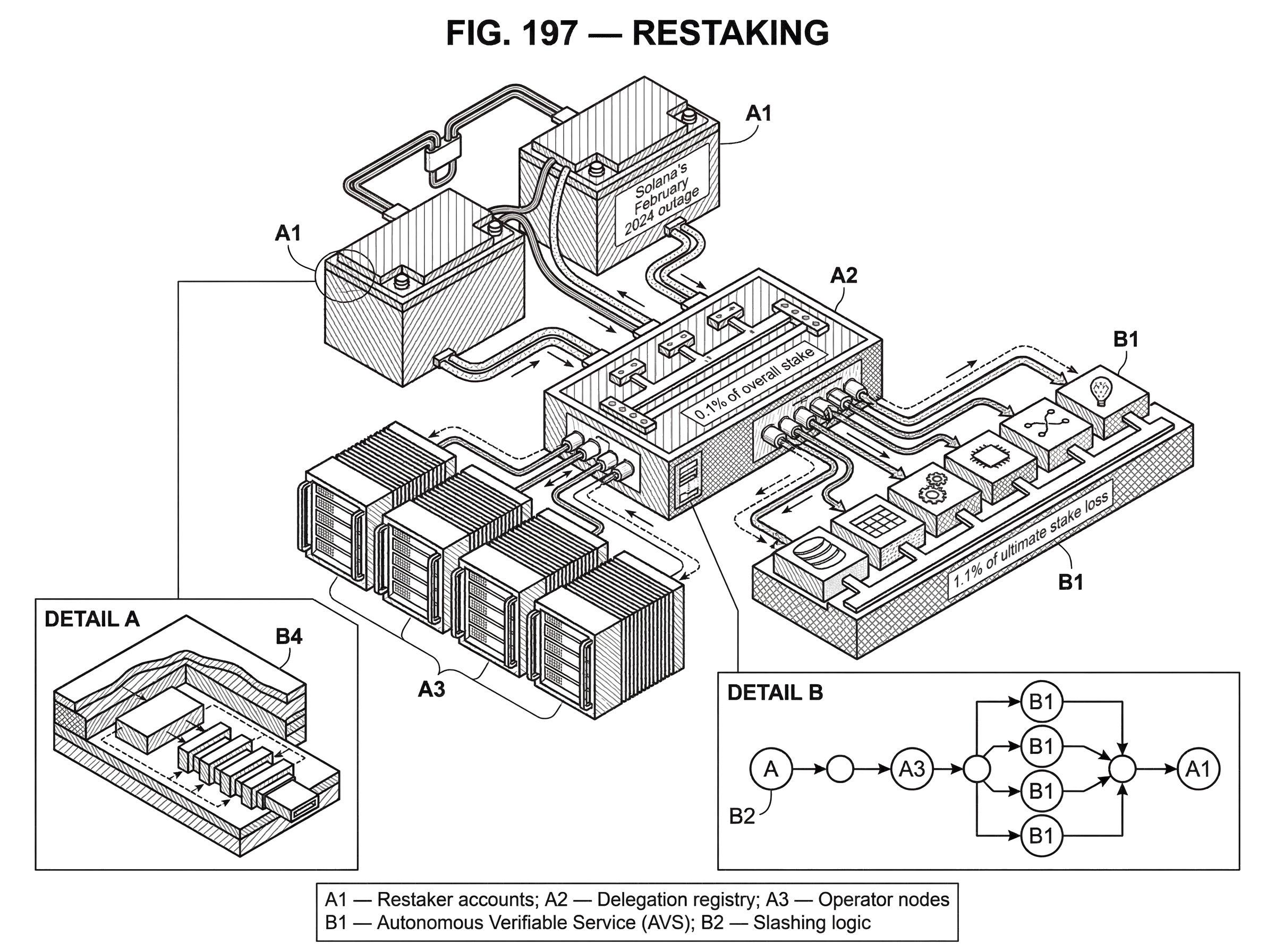
A prominent implementation is EigenLayer, which describes restaking as a primitive that lets app and service builders make verifiable commitments backed by staked assets. In its design, three roles matter: restakers, who provide slashable stake; operators, who run infrastructure and take on tasks; and Autonomous Verifiable Services, or AVSs, which consume that pooled economic security. EigenLayer supports multiple restaked asset types, including native ETH, liquid staking tokens, EIGEN, and some ERC-20-based strategies. That makes restaking broader than just "reuse your validator once more"; it is an attempt to build a market for shared cryptoeconomic security.
To understand why this exists, it helps to start from the problem it is solving.
Why do new blockchain services have trouble getting credible security?
| Option | Deterrent strength | Startup cost | Liquidity | Best for |
|---|---|---|---|---|
| Reputation | Low deterrent | Low startup cost | Off-chain dependent | Small trusted services |
| Own token | Unproven market value | High startup cost | Thin liquidity initially | New token projects |
| Restaking | High if slashable | Low bootstrapping cost | Market-recognized collateral | Middleware and AVSs |
A new blockchain-adjacent service often needs some way to make users believe that misbehavior will be costly. Maybe it is a data availability service, a bridge verification network, an oracle system, a decentralized sequencer set, or some other coordination layer. If operators can lie with no meaningful penalty, users are being asked to trust infrastructure rather than verify it.
There are only a few basic ways to solve this. A service can rely on reputation and contracts in the real world. It can issue its own token and ask operators to stake it. Or it can try to borrow security from an already-established ecosystem. The second path is common, but it is hard. A new token starts with uncertain value, thin liquidity, and weak social legitimacy. Slashing a token that the market barely values is not much of a deterrent.
Restaking exists because established stake already has what new systems lack: credible economic weight. ETH that is already staked for Ethereum consensus, or a liquid staking position that ultimately traces back to that stake, has much deeper value and market recognition than the fresh token of a brand-new middleware project. So instead of every service separately building a validator set and a token economy, restaking tries to let them plug into an existing pool of slashable capital.
This is the compression point: restaking is not primarily about earning extra yield; it is about selling existing trust to additional consumers. The yield matters because it pays participants to take the extra risk. But mechanically and economically, the core idea is that a service wants access to a penalty-backed promise, and restakers are willing to rent out that promise.
What changes when you restake the same stake across multiple services?
| Model | Rule set | Capital efficiency | Failure correlation | Enforcement |
|---|---|---|---|---|
| Ordinary staking | Single network rules | Isolated per service | Low | Native slashing only |
| Restaking | Multiple opt-in rules | High reuse of stake | Higher shared exposure | Multi-AVS slashing |
The important invariant in ordinary staking is that stake backs a specific rule set. For Ethereum, that rule set is the protocol's consensus behavior. A validator signs blocks and attestations under Ethereum's conditions, and Ethereum's slashing logic penalizes certain violations.
Restaking changes that invariant from one stake, one rule set to one stake, several rule sets chosen by opt-in. The stake itself does not magically multiply. What multiplies is the number of commitments attached to it.
That distinction matters. People sometimes speak as if restaking creates "extra security" from nowhere. It does not. It reallocates the deterrent power of existing stake. If an operator with X dollars of slashable stake takes on tasks for five services, those five services are all depending, in different ways, on claims against the same X. The system becomes more capital-efficient because not every service needs its own isolated collateral base. But the shared dependency means the stake is now a common failure surface.
A useful analogy is a building used as collateral for several loans. The analogy explains reusability of collateral well: one asset can support more than one promise. But it fails in an important way. In finance, claims are usually contractual and adjudicated externally. In restaking, the aim is to make commitments enforceable by protocol rules or on-chain mechanisms, often through slashing. So the analogy helps with the balance-sheet intuition, but not with the precise enforcement machinery.
How does restaking work step-by-step?
Different protocols implement restaking differently, but the mechanism usually has the same shape.
A staker begins with assets already committed to some staking or staking-adjacent system. They then opt into a restaking framework that records additional permissions and liabilities for those assets. In EigenLayer's architecture, restakers delegate to operators, and operators register to perform work for AVSs. The AVS is the service that wants security; the operator is the party actually doing the work; the restaker is the party whose capital is exposed if the operator misbehaves, depending on the delegation structure and protocol rules.
This division of roles is not cosmetic. It solves a real coordination problem. Many token holders want yield but do not want to run infrastructure. Many infrastructure operators can run services but do not own enough capital to self-secure everything they do. Many AVSs need security but do not want to bootstrap a fresh validator economy. Restaking links these three needs into one market.
A concrete example makes this easier to see. Imagine a data service that wants to promise users that it will honestly publish and serve data. It creates an AVS-style service definition with tasks operators must perform and with penalties if they do not. An operator signs up to run that service. But the operator's promise only matters if someone can economically punish failure. So restakers delegate stake to that operator. Now the operator can say, in effect: if I violate this service's rules, stake tied to me can be penalized. The service has acquired a deterrent-backed guarantee without minting an entirely new security token.
In EigenLayer, this design is meant to be permissionless and supports multiple asset forms. The contract repository describes support for native ETH, liquid staking tokens, EIGEN, and ERC-20 strategies. For standard ERC-20s, strategies can be deployed and whitelisted through a StrategyFactory, with deployed strategies using a beacon proxy pattern. That tells you something important about the protocol's ambition: restaking is being treated as an extensible settlement and security layer, not just as a one-off ETH feature.
The operational path depends on the asset type. For native ETH restaking, users may need special withdrawal routing. In the Ethereum-validator path described by Blockdaemon's guide, a validator's withdrawal credentials must point to an EigenPod address for that collateral to become restakable within EigenLayer's system. And because Ethereum validator withdrawal credentials cannot be changed after the fact, already-staked validators may need to exit and be re-staked with the proper withdrawal setup. That is a good example of where the mechanism is fundamental but the implementation is chain-specific: the need to control slashable collateral is fundamental; the EigenPod withdrawal-credential flow is one implementation detail tied to Ethereum's validator design.
Once capital is restaked, delegation becomes the next key step. Blockdaemon's guide notes that delegation to an operator is typically done once per wallet address, after which additional collateral in that address can follow the same operator choice. That captures a broader truth about restaking: the capital side and the operational side are separable but linked. The staker selects exposure; the operator performs work; the AVS defines what counts as success or slashable failure.
What real services and use-cases use restaking today?
The services that benefit most from restaking are the ones that need credible penalties for incorrect behavior but do not want to become full sovereign blockchains. A bridge verifier, an oracle committee, a data availability layer, a coprocessor, or a verifiable compute network all fit this pattern. They need operators to do work honestly, and they need a way to make dishonesty expensive.
That is why EigenCloud's product framing is revealing even though it is high-level. It presents EigenLayer as the trust layer where users stake ETH and EIGEN to secure cloud-style services, and it markets restaking-backed products such as verifiable compute and provable AI inference. The details of each service differ, but the shared mechanism is the same: developers want a verifiable claim whose credibility comes not just from cryptography, but from cryptography plus slashable stake.
This also shows where restaking sits relative to pure cryptographic verification. Some tasks can be checked entirely by math, with no economic assumptions beyond liveness. Others are only partially verifiable, expensive to verify on-chain, or depend on off-chain actions. In those cases, restaking fills the gap by making operators post economically meaningful guarantees. It is not replacing cryptography; it is complementing it where cryptography alone does not finish the job.
The pattern is not confined to Ethereum. MilkyWay, in a different ecosystem, described an opt-in restaking layer aimed at giving service developers a shared security pool while letting stakers pursue boosted yields. Its language (consolidating trust and security into one flexible pool of assets) is basically the same architectural move in another setting. Even though MilkyWay has announced a wind-down, it still illustrates the cross-chain generality of the concept: restaking is an architecture for pooled, reusable economic security, not an Ethereum-only slogan.
How do restaking rewards compensate for added slashing risk?
If restaking adds obligations, why would anyone opt in? The short answer is that rewards compensate participants for taking on additional slashing exposure and opportunity cost.
This is where people can misunderstand the economics. Restaking rewards are not free surplus appearing from nowhere. They are payments from services or protocols that want to buy security, plus sometimes programmatic token incentives designed to bootstrap participation. Those rewards exist because some other party values the service enough to pay for stronger guarantees.
EigenLayer's governance discussions make this visible. The proposal for Programmatic Incentives v2 describes an updated on-chain rewards engine for restaked security, including allocations to ETH stakers and operators, to EIGEN stakers and operators, and to ecosystem growth. Whatever one thinks of the exact percentages, the underlying logic is straightforward: if the protocol wants more security supplied to the network of services, it increases compensation to those providing that security.
That also explains a central open question in restaking economics: how much security should a service buy? Research on incentivized restaking frames the problem in exactly those terms. If a service pays too little, honest operators may not find the risk worthwhile, or attackers may find corruption profitable. If it pays too much, the system wastes resources over-securing low-value tasks. The hard part is that the right amount depends on operator behavior, attacker incentives, and the way risks interact across services.
What are the systemic and correlated risks of restaking?
| Risk source | Mechanism | Main consequence | Mitigation |
|---|---|---|---|
| More slashing rules | More punishable behaviors | Higher slashing probability | Clear AVS slashing rules |
| Operator concentration | Shared stacks and clients | Simultaneous service failures | Operator and client diversity |
| Capital correlation | One stake backs many promises | Cascade economic loss | Overcollateralization buffers |
| Exit constraints | Extended escrow and unbonding | Locked capital during incidents | Transparent exit windows |
The intuitive risk in restaking is “more slashing conditions means more ways to lose money.” That is true, but it is still too shallow. The deeper issue is correlation.
When the same operators, software stacks, and capital pools secure many services at once, failures stop being isolated. A bug, misconfiguration, or attack in one place can propagate economically into others. The literature on robust restaking networks studies exactly this issue: validator reuse across multiple services can create cascades, and the network's robustness depends on the buffer between attack costs and attack profits. In plain language, the system is safer when attacking remains meaningfully more expensive than whatever an attacker could gain.
One result from that work gives a useful intuition. Under assumptions where attack costs exceed attack profits by 10%, a sudden loss of 0.1% of overall stake cannot amplify into more than 1.1% of ultimate stake loss in the worst case. You should not treat that as a universal promise (it depends on the model's assumptions) but it shows what researchers are trying to quantify: when shared stake creates a network of dependencies, how bad can contagion get?
That concern is not merely theoretical. Even outside explicit restaking systems, staking incidents show how operator and software failures can create correlated loss. Lido's post-mortem on the Launchnodes slashing incident described how non-optimal failover procedures led multiple validator client instances to use a single Web3signer without slashing protection, causing double votes and attester slashings for 20 validators. The immediate penalties were limited and the operator compensated the protocol, but the lesson is broader: when infrastructure is reused or mirrored across systems, a single operational mistake can produce slashable behavior quickly.
Solana's February 2024 outage shows a different but related pattern. There, a software bug in validator execution logic and very high version concentration caused the network to halt finalization for about five hours. It was not a restaking event, but it demonstrates how common software exposure can turn one implementation bug into a system-wide failure. Restaking can amplify the importance of this kind of concentration because the same operators and stacks may be carrying obligations to many services simultaneously.
So the key risk is not just “there are more rules.” It is that the same capital is now attached to a graph of shared technical and economic dependencies.
Which implementation details in restaking protocols affect safety the most?
Because restaking sounds conceptually simple, it is easy to overlook how much safety depends on low-level contract and operations design.
The Consensys Diligence audit of EigenLayer's contracts is helpful here. It highlights issues like multi-contract reentrancy risk across strategy and manager flows, domain-separator handling for signatures, tradeoffs in share accounting, and withdrawal-flow design. None of these are side notes. Restaking systems move collateral through several linked contracts while tracking shares, delegations, queued withdrawals, and slashability. If accounting becomes inconsistent, the protocol can misstate who owns what, who is exposed to what, or when funds are actually available.
One particularly instructive example from the audit is the use of a minimum nonzero total shares threshold in StrategyBase to mitigate ERC-4626-style inflation or donation attacks. The benefit is clear: it helps defend against manipulations of the share exchange rate. But the tradeoff is that extremely small positions can become effectively non-withdrawable. This is a good example of a general truth in protocol design: security fixes often convert one failure mode into a more bounded but still real usability cost.
Operational details matter too. The Blockdaemon guide notes that withdrawal and unbonding timing can depend on AVS parameters, and that there is an escrow period on EigenLayer mainnet before full withdrawal. That means restaking changes not just risk but also liquidity. Your capital is not simply “staked twice”; it is subject to another layer of exit conditions.
And multichain support introduces another subtlety. EigenLayer's contract documentation says AVSs register on a source chain and that stake can be transported to supported destination chains such as Base. But it also notes that Base and Base Sepolia do not support standard core protocol functions like restaking and slashing; they only support verification of tasks backed by stake that lives on Ethereum mainnet or Sepolia. That distinction matters because “available on another chain” does not necessarily mean “the whole restaking lifecycle happens there.” Sometimes verification is remote while slashable security remains anchored elsewhere.
Is restaking the same as financial rehypothecation?
A useful neighboring idea is rehypothecation in finance: reusing collateral that already backs one obligation to support another. Restaking has the same core economic pattern. Capital gets reused, efficiency rises, and hidden interdependence grows.
But there is an important difference in what is being optimized. In classic rehypothecation, the goal is usually balance-sheet efficiency and liquidity creation inside financial intermediaries. In restaking, the explicit goal is to create on-chain, penalty-backed security guarantees for digital services. So the structural risk is similar, but the design target is different.
That difference also explains why restaking has attracted interest from infrastructure builders rather than only yield farmers. Builders are not just looking for leverage; they are looking for a credible way to make promises to users without bootstrapping an entirely new sovereign validator economy.
How does threshold signing compare with restaking for building shared trust?
Restaking often secures services that sit between pure code and operational reality, and those services frequently rely on distributed trust mechanisms such as multi-party computation or threshold signing. A concrete example is Cube Exchange's 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize settlement.
That is not itself a restaking protocol, but it helps clarify what restaking-backed services are often trying to secure. A threshold signing system can reduce single-key risk by distributing control, but users still need confidence that the parties running the system will follow the rules, stay online, and not collude or fail operationally. Restaking offers one way to attach economic penalties to those promises. In that sense, threshold cryptography handles how control is distributed, while restaking can help handle how misbehavior is made costly.
What key assumptions would make restaking fail?
Restaking depends on a few assumptions, and the concept weakens quickly when they fail.
The first assumption is that slashing conditions are credible and enforceable. If a service cannot clearly specify what counts as slashable misconduct, or cannot actually execute penalties when misconduct happens, then the promised security is mostly rhetorical.
The second is that the value at risk is genuinely meaningful relative to the value an attacker could gain. If a bridge secures billions while only a much smaller amount of stake is realistically punishable for failure, the deterrent may be inadequate. The formal literature expresses this as attack cost versus attack profit. The words differ, but the core issue is basic: if cheating pays more than getting caught costs, the security story is weak.
The third is that participants understand correlated exposure. A restaker may think they are earning multiple income streams from the same capital. Economically, that is true. But they are also underwriting multiple operational systems, multiple software stacks, and multiple rule sets. If those exposures are opaque, restaking can look safer than it is.
The fourth is governance and implementation discipline. Restaking protocols are not static. Reward schedules change, new strategies are whitelisted, operators come and go, and destination-chain support can differ from source-chain support. If governance expands collateral types or incentives faster than it can assess the resulting risk, the protocol may accumulate fragility faster than participants notice.
Conclusion
Restaking is the reuse of slashable stake to secure additional services beyond the base network it was originally securing. Its appeal comes from capital efficiency: new services do not have to build security from zero if they can tap into existing stake. Its danger comes from the same place: once the same capital backs many promises, failures can become shared.
The shortest way to remember it is this: restaking turns stake into a market for reusable trust. That can make decentralized services much easier to launch and much harder to attack. But it only works as advertised if the extra promises are clearly defined, credibly slashable, and priced for the risks they add.
How do you build a crypto position over time or earn on it?
Build a position over time by funding your account regularly and using recurring buys or controlled orders to dollar-cost-average into the assets you want. Use Cube Exchange to fund your account and execute recurring or one-off buys, then separately evaluate staking, liquid-staking, or lending options (and their risks) if you want to pursue yield.
- Fund your Cube account with fiat (ACH, card) or a crypto transfer to the deposit address.
- Create a recurring buy (weekly or monthly) or schedule limit orders for the spot pair (e.g., ETH/USD) to dollar-cost-average.
- Choose order types: use limit orders for price control or market orders for immediate execution; set order size and frequency to match your target allocation.
- After you accumulate a base position, research yield options (staking, liquid staking, lending) and, if you proceed, move only the portion you intend to lock after checking withdrawal timing and slashing rules.
Frequently Asked Questions
Restaking reuses assets already locked for base-layer staking to back additional, opt-in rule sets for other services, whereas ordinary staking ties stake to a single protocol consensus rule set; restaking therefore multiplies commitments on the same capital rather than creating new capital-backed security.
A typical restaking stack splits three roles: restakers who provide slashable capital, operators who run the infrastructure and perform service tasks, and AVSs (autonomous verifiable services) that define tasks and slashable rules - this division lets capital providers earn yield without running nodes while operators acquire economic backing to make on-chain promises.
EigenLayer and related implementations support multiple asset forms including native ETH, liquid staking tokens, the protocol token (EIGEN), and some ERC‑20-based strategies, with ERC‑20 strategies deployed and whitelisted via a StrategyFactory pattern.
Restaking raises systemic risk by creating correlations: the same slashable capital, operators, and software stacks can back many services so a bug, misconfiguration, or attack can produce simultaneous failures across services rather than isolated losses.
You often cannot simply repoint an existing Ethereum validator to restake; because validator withdrawal credentials are immutable after deposit, many setups require exiting and re‑staking with withdrawal credentials (e.g., to an EigenPod) so the collateral becomes restakable.
Restaking rewards come from services buying security (fees or protocol-paid incentives) plus programmatic token emissions meant to bootstrap participation; they compensate participants for additional slashing exposure and are not free surplus.
Implementation-level risks - buggy contract accounting, multi-contract reentrancy, signature domain handling, and withdrawal/escrow flow design - matter greatly because they change who is exposed and when funds are available; audits (e.g., ConsenSys Diligence) highlight these concrete contract-level failure modes.
Restaking resembles rehypothecation economically because the same collateral supports multiple promises, but it differs in goal and enforcement: restaking aims to create on‑chain, slashable guarantees for digital services rather than balance‑sheet liquidity inside financial intermediaries.
Formal work on restaking cascades gives usable bounds: for example, under a model where attack costs exceed profits by 10%, a sudden 0.1% stake loss cannot amplify to more than a 1.1% ultimate loss in the worst case, but such bounds rely on model assumptions and are not universal guarantees.
Regulatory guidance is unsettled: a recent SEC staff statement distinguished custodial staking (which should avoid rehypothecation) and expressly excluded constructs like liquid staking and restaking from its safe examples, but that statement is a non‑binding staff view and legal treatment will depend on specific facts.
Related reading