What is Key Sharding?
Learn what key sharding is, how threshold secret sharing works, and why wallets use shards for recovery, custody, and MPC signing.
Introduction
Key sharding is the practice of splitting wallet control across multiple cryptographic shares so that no single place, person, or device holds the whole private key. That sounds like a small engineering tweak, but it changes the wallet’s basic failure mode. A traditional wallet asks one thing to do two jobs at once: the same secret must be easy enough for you to use, yet impossible for anyone else to steal. Key sharding exists because that is often a bad trade.
If a wallet depends on one seed phrase, one file, one hardware device, or one backend signer, then both loss and theft become concentrated problems. Lose that one thing and recovery may be impossible. Expose that one thing and the attacker may gain full control. Key sharding tries to separate those risks. It replaces single possession with a threshold: perhaps any 2 of 3 shares can recover a wallet, or any 3 of 5 participants can approve a signature, while fewer than that cannot.
The important idea is not merely “cut the key into pieces.” Ordinary splitting is easy and often insecure. If you tear a secret into three literal chunks, each chunk may reveal part of it, and all chunks may be required. Key sharding, in the cryptographic sense, is designed so that some minimum number of shares is enough, and anything below that threshold reveals nothing useful about the secret. That is why the concept sits at the foundation of modern recovery systems, institutional custody, and many MPC wallets.
Why do wallets split private keys into shards?
A private key gives a wallet its authority. Whoever can use that key can usually move funds or authorize actions. The simplest architecture is therefore also the most dangerous: store one secret somewhere safe and use it when needed. This works until “somewhere safe” turns out to mean a phone that can be lost, a seed phrase that can be copied, a laptop that can be malware-infected, or an employee account that becomes a single point of compromise.
Here is the mechanism behind the risk. A single secret creates binary security. Either the secret is available, in which case one compromise can be catastrophic, or it is unavailable, in which case the rightful owner may be locked out. There is no graceful degradation. Key sharding introduces a different invariant: control survives some failures and resists some compromises at the same time, as long as both stay below the threshold. In Shamir’s original framing, a (k, n) threshold scheme can tolerate losing up to k - 1 shares while still allowing recovery with k shares, and it can tolerate exposure of up to k - 1 shares without revealing the secret.
That trade is why key sharding appears in very different settings. A family wallet may want resilience against a lost device. A startup treasury may want no single executive able to act alone. A custodian may want signing authority spread across independent machines and teams. A consumer wallet may want recovery that feels more like ordinary account recovery than memorizing one irreversible phrase. These use cases look different on the surface, but the underlying question is the same: how do you avoid making one secret the entire story?
How does key sharding work in wallets?
At its core, key sharding means turning one secret into multiple shares governed by a threshold rule. Suppose a wallet uses a 2-of-3 scheme. Three shares are created, and any two are enough to reconstruct or exercise control over the wallet. A single share, by itself, should not let anyone derive the key.
This is usually built from secret sharing, especially Shamir’s Secret Sharing. Shamir formalized the threshold property precisely: in a (k, n) scheme, any k or more shares make the secret easy to compute, while any k - 1 or fewer shares leave the secret completely undetermined. The striking part is the second half. Properly constructed shares are not “partial keys” in the intuitive sense. They are not fragments that each reveal a little. They are structured so that below the threshold, an attacker learns nothing about the underlying secret.
That distinction is worth pausing on because it is where many smart readers initially misfire. A shard is not necessarily like a shard of glass from a broken window. In well-designed secret sharing, a share is better understood as a constraint on a hidden object. One constraint is not enough. A threshold number of constraints is enough to determine the object uniquely. That is the mathematical shape of the construction.
In wallet systems, “key sharding” sometimes refers narrowly to backup and recovery, where the secret can later be reconstructed from shares. In other contexts it refers more broadly to distributed key control, where shares participate in signing without ever reconstructing the full private key in one place. The first is classic secret sharing. The second is what threshold-signature and MPC wallets aim to do. The two ideas are adjacent but not identical.
How does Shamir's Secret Sharing create a k-of-n threshold?
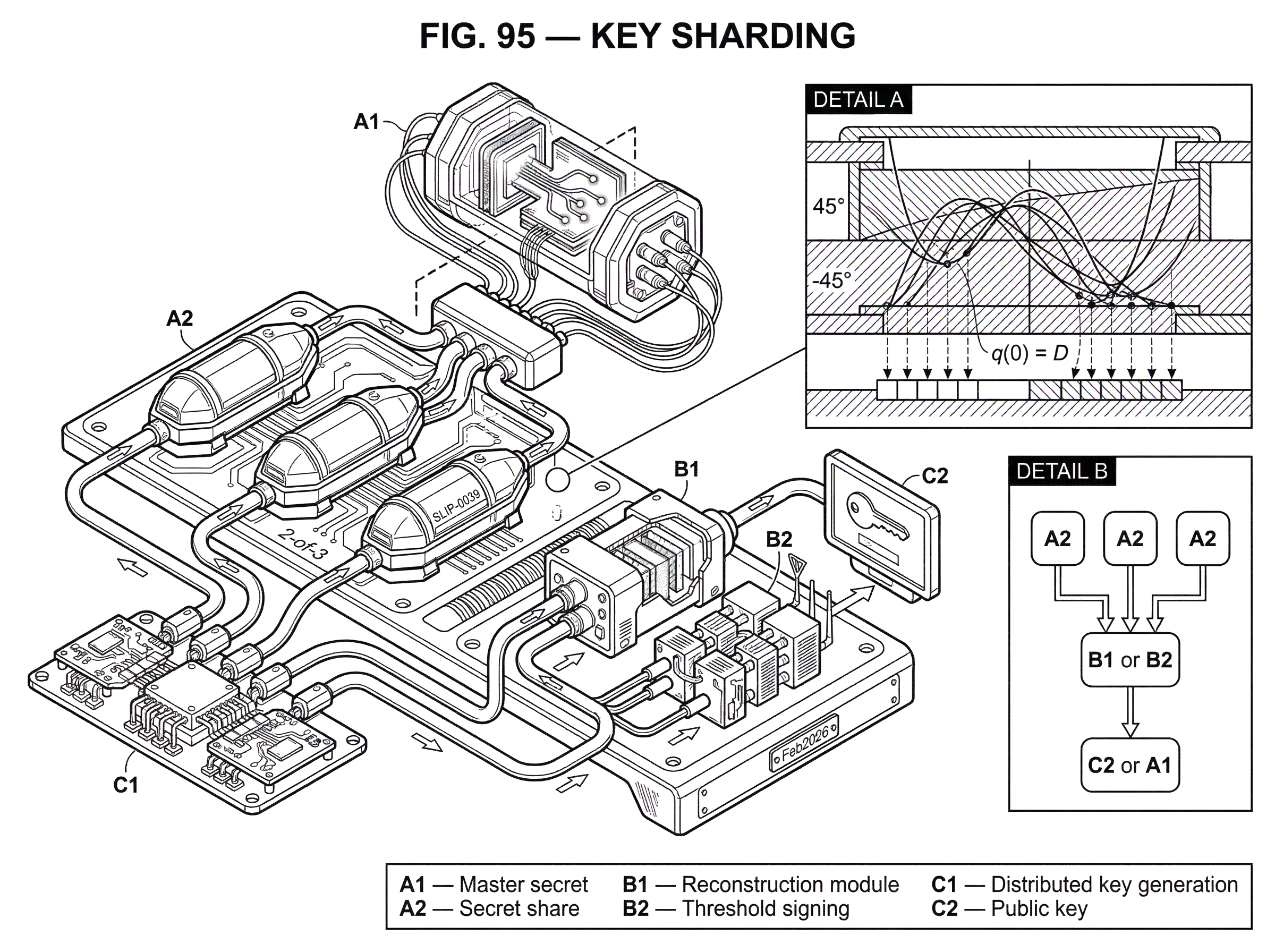
The reason Shamir’s construction matters is that it gives a clean way to enforce a threshold. The key idea comes from a simple fact about polynomials: a polynomial of degree k - 1 is uniquely determined by k points with distinct x values. If you know only k - 1 points, there are still many possible polynomials that could fit them.
Shamir turns that fact into a secret-sharing scheme. Treat the secret as a number D. Choose a prime p larger than both D and the number of shares n, and do all arithmetic modulo p. Then choose a random polynomial q(x) of degree k - 1 whose constant term is the secret. In other words, q(0) = D. The remaining coefficients are chosen uniformly at random. Each share is then one point on the polynomial, such as (1, q(1)), (2, q(2)), and so on up to (n, q(n)).
Here is why this works. If you later collect any k shares, you have k points on the polynomial. Because the polynomial has degree k - 1, those k points determine it uniquely, and once you know the polynomial you can evaluate it at 0 to recover D, the secret. But if you only have k - 1 shares, there are many degree-k - 1 polynomials that pass through those points, each with a different constant term. Since the unknown coefficients were chosen uniformly at random, the secret remains information-theoretically hidden.
That last phrase matters. In the ideal Shamir model, secrecy up to the threshold does not depend on an attacker lacking computing power. It is not merely “hard” to compute the secret from too few shares. Rather, the shares do not contain enough information to determine it at all. That is a stronger statement than ordinary encryption usually gives.
A small example makes the mechanism easier to feel. Imagine you want a 2-of-3 split. Degree k - 1 now means degree 1, so the hidden polynomial is just a line. The secret is the line’s value at x = 0. You choose a random slope and produce three points on that line. Any two shares reveal the whole line, and therefore the intercept, which is the secret. But one share alone is just one point. Infinitely many lines pass through a single point in ordinary arithmetic; in the finite-field version used here, many candidate lines still remain. So one share gives no information about which intercept is correct.
The formal machinery may sound abstract, but the wallet-level consequence is concrete: each share can be the size of the original secret, and threshold recovery is built into the math rather than improvised operationally.
Why do some wallets encrypt the seed before splitting it into shares (for example SLIP‑0039)?
| Issue addressed | Raw Shamir (split only) | Encrypt then split (e.g., SLIP-0039) |
|---|---|---|
| Partial-leak resilience | Vulnerable to partial leaks | Leaked shares less useful due to encryption |
| User entry errors | No user-friendly error checks | Includes KDF and integrity checks |
| Checksum and integrity | Generally absent | Reed–Solomon checksum detects entry mistakes |
| Human-friendly encoding | Raw binary shares | Mnemonic word encoding for humans |
| Organizational policies | Flat threshold only | Supports groups, nested thresholds, passphrases |
A raw secret-sharing scheme protects against having too few complete shares. But wallet implementations have to deal with a messier world: users miscopy words, partial data may leak, formats need checksums, and people may want passphrase protection layered on top. That is why many wallet standards do not simply apply Shamir’s scheme to the master secret directly.
SLIP-0039 is a good example. It standardizes a Shamir-based mnemonic format for backing up HD wallets and is intended largely as a replacement for BIP-39-style single-seed backups. Its design first encrypts the master secret into an encrypted master secret, then applies secret sharing to that encrypted value. The reason is practical. The specification explicitly notes concern about scenarios where partial information about shares leaks, and it adds encryption and integrity checks to make those leaks less useful and recovery more robust.
Mechanically, SLIP-0039 packages shares into mnemonic word sequences. It also uses a checksum based on Reed–Solomon coding to catch entry mistakes. That is an operational point, but it has conceptual importance: key sharding in wallets is never just the threshold math. It is also the encoding, error detection, recovery ergonomics, and compatibility layer that determines whether the scheme is usable by actual humans.
SLIP-0039 also shows that thresholds need not be flat. It supports a two-level structure: first split the encrypted master secret across groups, then split each group share among members. That allows policies such as “any 2 of 3 groups, where within group A any 2 of 3 members suffice, but within group B all 2 members are required.” The deeper lesson is that sharding can express organizational structure, not just redundancy.
Should I use shards for recovery or for threshold signing (MPC)?
| Property | Reconstruction-based recovery | Distributed signing (MPC / TSS) |
|---|---|---|
| Key reconstituted? | Yes, shares combined | No, key never reconstituted |
| Normal operation | Reconstruct only when needed | Participants cooperate every signing |
| Attack surface | Risk during reconstruction events | Protocol, messaging, implementation risk |
| Recovery frequency | Infrequent but expected | Requires live availability for signing |
| Best for | Personal backups and offline recovery | Institutional custody and privacy-preserving signing |
There are two related but importantly different ways to use key sharding in wallets.
The first is reconstruction-based recovery. Shares are stored in different places, and when needed, enough shares are gathered to reconstruct the secret key or seed. This is conceptually closest to backups. A person might keep one share on a phone, another in a safe, and a third with a trusted relative, needing any two to recover the wallet after device loss.
The second is distributed signing. Here the goal is to avoid reconstructing the full private key at all. Instead, each participant holds a key share and cooperates in a threshold-signature or MPC protocol so that the final signature is valid, but the full private key never exists in one place during generation, storage, or signing. This is the design used in many modern MPC wallets and institutional systems.
That difference is easy to miss because both involve “shares.” But the operational security picture changes sharply. In a recovery scheme, reconstruction is a normal and expected event. In a threshold-signing system, reconstruction is precisely what the architecture tries to avoid. If you hear a vendor say key shards “never combine,” they are usually talking about the second model.
The connection between the two is Distributed Key Generation, or DKG. If a system simply generates a full key centrally and then splits it, there was a moment when someone or something saw the whole key. DKG removes that trusted dealer. The participants jointly generate shares and the corresponding public key so that no single participant ever learns the full private key. That is why DKG is a foundational neighbor of key sharding: it is the setup ceremony that makes distributed control trustless rather than merely redistributed after the fact.
What does key sharding look like in consumer and institutional wallets?
A concrete consumer example helps. Torus describes a 2-of-3 design in which one share lives on the user’s device, one is managed through a login service and distributed among node operators, and one is a recovery share held by the user. The wallet can be recovered with any two shares. The service never holds enough on its own to reconstruct the key, which is why the system is described as non-custodial even though a service participates.
The mechanism here is not interesting because it is exotic; it is interesting because it changes user experience. A user can log in through a familiar account flow, while the underlying wallet key is still protected by a threshold arrangement. In other words, key sharding is doing identity and recovery work, not only cryptographic ceremony. But the assumptions are now distributed across storage media and organizations. If the device share is poorly protected, or the recovery share is weakly stored, the threshold’s theoretical elegance may not survive contact with reality.
Institutional systems take the same idea in a different direction. Fireblocks, for example, describes MPC-based key sharding where key material is generated and stored as shares that never combine, with shares deployed across customer infrastructure, enclaves, HSM environments, or service-operated components. The pattern is broader than one company: distribute authority across machines, teams, and approval paths so that compromising one server or one admin is not enough to move funds.
This is not chain-specific. A threshold signature over ECDSA can produce an ordinary ECDSA signature, which means a blockchain verifier need not know whether one signer or a threshold protocol produced it. Libraries such as tss-lib implement threshold ECDSA and EdDSA with dealerless key generation, signing, and resharing. That makes the concept relevant anywhere those signature schemes matter, whether the wallet is used around Bitcoin-style keys, Ethereum accounts, or other ecosystems that rely on the same underlying signature families.
Threshold signatures vs. multisig: what's the difference?
| Aspect | Multisig | Threshold signatures |
|---|---|---|
| On-chain visibility | Multiple public keys visible | Single public key visible |
| Signature format | Multiple signatures or script | Single standard signature |
| Privacy | Signing set often observable | Signer set usually hidden |
| Policy enforcement | Enforced by the chain | Enforced by off-chain protocol |
| Main downside | Chain complexity and linkage | Protocol complexity and implementation risk |
Key sharding is often compared with multisig because both distribute control. But they do so at different layers.
Multisig usually means the blockchain itself sees multiple keys and enforces a policy on-chain or in the transaction format. A 2-of-3 multisig account visibly has three public keys and a rule requiring two signatures. Threshold signatures, by contrast, usually produce a single ordinary signature under a single public key, even though multiple parties cooperated to create it. The chain sees the end result, not the internal ceremony.
That creates different consequences. Threshold signing can preserve signer privacy because outside observers may not learn which subset participated. It can also be more compatible where chains or wallet infrastructure expect a standard signature format. But this convenience comes at the cost of off-chain protocol complexity. The security now depends not only on the blockchain’s validation rules but also on the correctness of the cryptographic protocol, the messaging layer, proof systems, and implementation details.
So when people say key sharding is “better than multisig,” that is too blunt. A better statement is this: threshold systems move policy enforcement from the chain into cryptographic protocol execution, which can improve privacy and compatibility, but shifts more trust into implementation correctness.
What security assumptions does key sharding depend on, and how can it fail?
The clean threshold story depends on assumptions that are often hidden in product descriptions. The first assumption is independence of compromise. If all shares are stored under one cloud account, one admin domain, one malware-exposed laptop fleet, or one vendor backend, then multiple “shares” may collapse into one practical point of failure. A threshold only helps if the shares fail independently enough that crossing the threshold is materially harder than compromising one system.
The second assumption is correct share generation and distribution. Shamir’s original paper does not solve the dealer problem. Someone must generate the shares honestly, or the system must use DKG so no single dealer is trusted. If a malicious generator biases the setup or keeps a copy of the secret, the threshold guarantee may be weaker than it appears.
The third assumption is lifecycle discipline. Shares can be refreshed and participants can be changed, but revocation in the real world is not magical. If an employee leaves or a device is lost, the old share is only truly gone if it is actually inaccessible. Shamir noted that shares can be changed without changing the underlying secret by choosing a new polynomial with the same constant term, but enforcement against adversarial retention is an operational challenge, not a mathematical one.
Then there is the hardest category: implementation vulnerability. Modern threshold ECDSA and MPC systems are much more complex than plain secret sharing. Research has shown practical key-extraction attacks against real MPC wallet implementations, including attacks that exploited malformed Paillier keys, flawed or missing zero-knowledge proofs, unsafe handling of signature failures, and subtle proof-encoding mistakes. In some cases, a single malicious party and surprisingly few signing sessions were enough to recover the full private key.
This does not mean key sharding is a bad idea. It means the security boundary has moved. The wallet is no longer only protecting a secret at rest; it is protecting an interactive protocol. That protocol needs audited implementations, careful parameter choices, secure transport, correct proof verification, and sometimes hardware isolation. A threshold scheme can remove the single-key failure mode while introducing protocol-level failure modes if implemented badly.
What trade-offs does key sharding introduce for users and organizations?
It is tempting to frame key sharding as simply “more secure.” The more accurate description is that it reallocates risk.
It usually improves resilience against single events. One lost device need not mean permanent loss. One compromised server need not mean immediate theft. One employee need not be able to act alone. That is real and important.
But it can also increase coordination burden. More shares mean more storage locations, more recovery procedures, more chances for user confusion, and more need for documentation. The SoK on Web3 recovery makes the point clearly: share-based designs often improve availability relative to relying on one high-entropy mnemonic, but weak or centralized storage of many users’ shares can create systemic risk. If a service stores one share for everyone and that service is breached, the threshold margin for many users may be reduced at once.
So the central question is not “is sharding secure?” but rather which failures are you trying to survive, and which new dependencies are you willing to accept? A 2-of-3 personal backup design, a 3-of-5 executive approval scheme, and a dealerless MPC signing cluster answer that question in very different ways.
Conclusion
Key sharding is the idea that wallet control should depend on a threshold of shares, not on one secret sitting in one place. Its mathematical core comes from threshold secret sharing, especially Shamir’s construction, where any sufficient number of shares can recover the secret and anything below that threshold reveals nothing. In modern wallets, that idea extends beyond backup into threshold signing and MPC, where the full private key may never exist in one place at all.
The part to remember tomorrow is simple: key sharding does not make secrets disappear; it changes the shape of trust and failure. Done well, it replaces a brittle single point of loss or compromise with a system that can survive some mistakes and some attacks. Done badly, it can turn one obvious risk into several subtle ones. That is why the mechanism matters as much as the slogan.
How do you secure your crypto setup before trading?
Secure your crypto setup by using threshold key sharding and independent recovery shares before you trade. On Cube Exchange, use the non‑custodial MPC workflow to split signing authority into shares so a threshold (not one secret) controls funds while you keep operational control.
- Create a non‑custodial MPC key on Cube and pick a threshold policy (example: 2‑of‑3 for personal recovery or 3‑of‑5 for treasury approvals).
- Export or record each recovery shard to separate, independent locations; for example a hardware wallet, an encrypted offline USB in a safe, and a trusted custodian or separate device.
- Protect exported shards: encrypt with a strong passphrase or use a SLIP‑0039 mnemonic layer before storing any offline copy.
- Test recovery and signing: perform a simulated k‑of‑n recovery and broadcast a small signed transaction to confirm you can reconstruct access and submit valid signatures.
- Fund your Cube account and execute a small trade to confirm end‑to‑end signing, network confirmation, and that your shard-based recovery works in practice.
Frequently Asked Questions
Shamir’s scheme encodes the secret as the constant term of a random polynomial of degree k−1 and gives each share as a point on that polynomial; any k points uniquely determine the polynomial (so you can recover the secret) while k−1 or fewer points are consistent with many possible polynomials and therefore reveal nothing about the secret (information‑theoretic secrecy).
Reconstruction‑based recovery collects enough shares to rebuild the private key or seed in one place (a backup model), whereas distributed signing/MPC keeps shares separate and runs a protocol that outputs a valid signature without ever assembling the full private key in one location.
Key sharding only helps if shares fail independently; if multiple shares are stored under the same cloud account, admin domain, or poorly protected device, those 'separate' shares can collapse into a single point of compromise and defeat the threshold guarantee.
The dealer problem is the risk that whoever creates and splits the secret could keep a copy or bias the setup; it’s addressed by dealerless Distributed Key Generation (DKG) and verifiable secret sharing protocols so no single party ever learns the full private key during setup.
Wallet standards like SLIP‑0039 first encrypt the master secret and add integrity/checksum data before applying secret sharing to reduce risks from partial leaks, to provide human‑friendly mnemonics and error detection, and to make actual backups more robust in practice.
No - multisig exposes multiple public keys and on‑chain policy, while threshold signatures produce a single ordinary signature under one public key even though many parties cooperated; that gives better privacy and compatibility but shifts enforcement off‑chain into complex cryptographic protocols.
Yes; real‑world attacks have shown that implementation flaws (for example malformed Paillier keys, missing or incorrect zero‑knowledge proofs, and unsafe handling of protocol failures) can enable extraction of the private key even from MPC/threshold deployments.
Mathematically you can resharing or refresh Shamir shares without changing the underlying secret, but in practice revocation is an operational problem: ensuring a departed participant cannot retain a usable copy requires procedures and controls beyond the math and the paper does not solve enforcement for you.
Sharding can make recovery more available and reduce single‑device loss, but it increases coordination, storage locations, and user complexity; designers must trade off which failures they want the system to survive versus the new dependencies they accept.
Related reading