What Is Keccak-256?
Learn what Keccak-256 is, how its sponge construction works, why rate and capacity matter, and why Ethereum keccak256 differs from SHA3-256.
Introduction
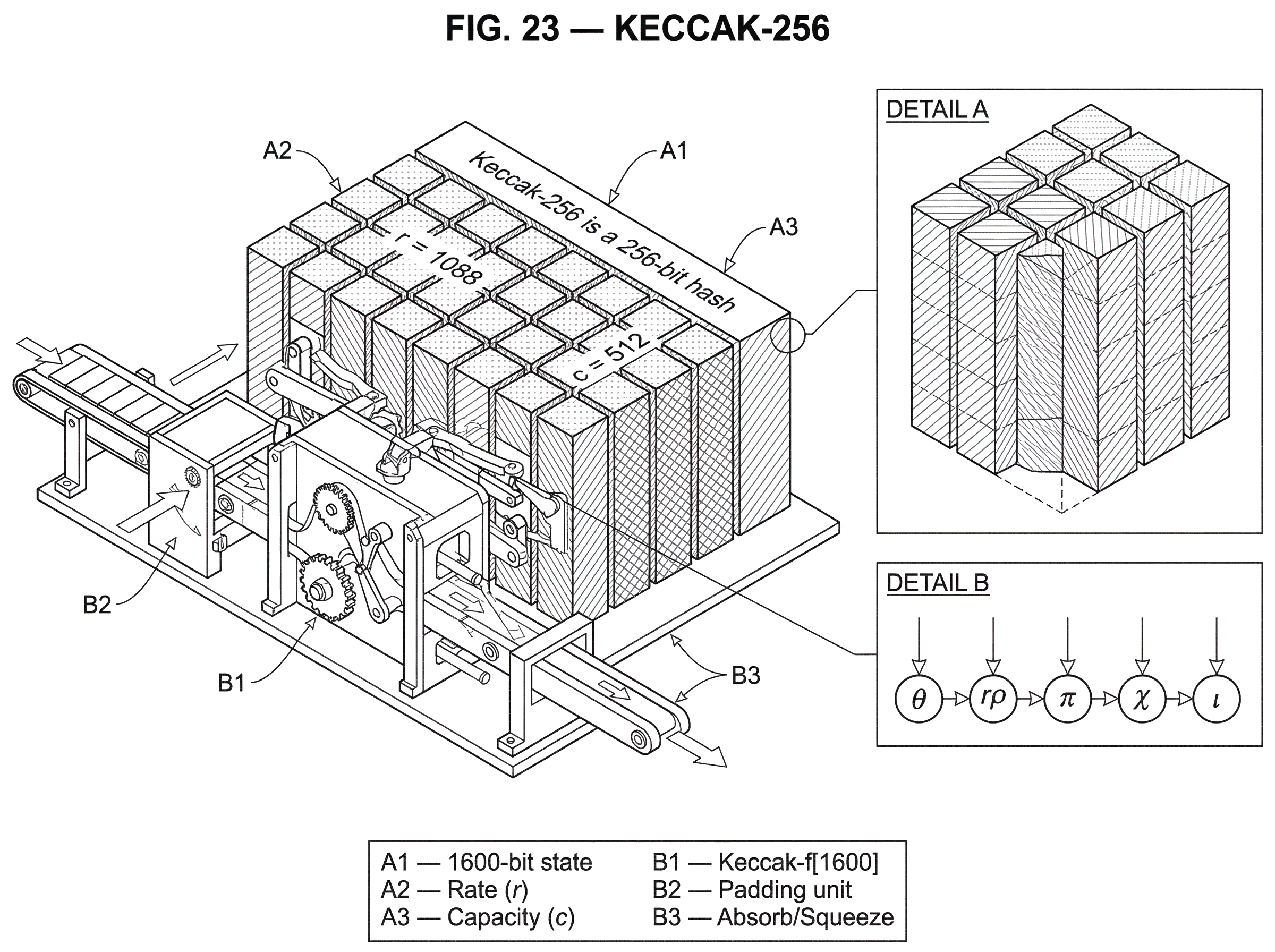
Keccak-256 is a 256-bit hash built from the Keccak sponge construction, and it matters because the same underlying design sits behind both the NIST SHA-3 family and the keccak256 function used across Ethereum tooling and protocols. That combination creates a persistent source of confusion: people often say “SHA-3” when they actually mean Ethereum’s older Keccak variant, even though the outputs are not the same.
A hash function is supposed to feel simple from the outside. You give it bytes; it gives you a fixed-size digest. But cryptographic hashes are not just compression gadgets. They are designed so that tiny input changes scramble the output, so that finding two inputs with the same digest is hard, and so that working backward from a digest to a matching input is infeasible in practice. Keccak-256 solves that problem using a very different internal strategy from older designs such as SHA-256.
The key idea is that Keccak does not repeatedly compress message blocks with a dedicated compression function in the classic Merkle–Damgård style. Instead, it keeps a large internal state, mixes message blocks into only part of that state, and repeatedly applies a fixed permutation. That is the idea that makes the rest click.
Once you understand why Keccak separates the state into a rate and a capacity, most of the design choices become much easier to reason about.
- its security claims
- its performance tradeoffs
- the difference between Keccak-256 and SHA3-256
Why does Keccak reserve a hidden capacity instead of exposing the whole state?
| Choice | Throughput | Generic security | Best for |
|---|---|---|---|
| Large rate | Higher throughput | Lower security ceiling | Throughput-sensitive apps |
| Balanced (Keccak-256) | Good throughput | c = 512 → 128-bit birthday | Standard hash use |
| Large capacity | Lower throughput | Higher generic security | High-assurance systems |
If all you wanted were speed, you might let the whole internal state absorb input and emit output. Keccak deliberately does not do that. In a Keccak sponge instance, the state has r + c bits, where r is the rate and c is the capacity. During hashing, input blocks are XORed only into the r visible bits, and output is also taken only from those r bits. The remaining c bits stay hidden from direct input and output.
That hidden part is not wasted space. It is the main security lever. Intuitively, the rate is the part you expose for throughput, while the capacity is the part you reserve as a security buffer. If you increase r, you process more message bits per permutation call and run faster. But because the total state width is fixed for a given permutation, increasing r decreases c, and that weakens the generic security bound. So Keccak’s design is built around a clean tradeoff: speed comes from the rate; generic security comes from the capacity.
For the 1600-bit permutation used in standard large Keccak instances, Keccak-256 is typically the sponge instance with r = 1088 and c = 512. That means 1088 bits of the state are used for absorbing and squeezing, while 512 bits remain as the hidden reserve. The reason c = 512 matters is that generic sponge security is tied to c, not just to the digest length. In broad terms, collision resistance is bounded around 2^(c/2), and for a 256-bit digest that aligns naturally with the familiar 128-bit collision target.
This is already one place where readers often get tripped up. A 256-bit output does not automatically mean 256 bits of security against every attack. Different attack goals have different generic costs, and Keccak’s own security claims are framed in terms of the sponge’s capacity. The output length matters, but it is not the only thing that matters.
How does the Keccak sponge construction absorb input and produce output?
The name sponge is useful because it describes the mechanism fairly well. First the construction absorbs input block by block into the state. Then it squeezes output blocks back out. Between every absorb or squeeze step, the same internal permutation is applied to the full state.
Imagine starting with an all-zero state of r + c bits. Before absorption begins, the message is padded so that its length becomes a multiple of r. Keccak uses the pad10*1 rule, which means the padding starts with a 1 bit, ends with a 1 bit, and places as many 0 bits in between as needed to fill the final block. This simple rule matters for more than formatting. It makes the encoding injective in the way the sponge construction needs, so different messages do not accidentally become the same padded input stream.
Now take the padded message and split it into r-bit blocks. For each block, XOR that block into the first r bits of the state and then apply the permutation. Once all blocks have been absorbed, the hash output is read from the first r bits of the state. If you need more output than one block gives, you emit those r bits, apply the permutation again, emit another r bits, and continue. That is why Keccak naturally supports extendable-output functions such as SHAKE: squeezing more output is built into the construction.
A fixed-length hash like Keccak-256 simply truncates that potentially unbounded output stream to 256 bits. So the internal process is not “compute a 256-bit state and stop.” It is “run a sponge that could keep producing bits, then take the first 256 of them.” That distinction becomes important when you compare fixed-output hashes with XOFs and when you reason about why suffix bits are used for domain separation.
A worked example makes this less abstract. Suppose you want to hash a short byte string. Keccak first appends any required suffix bits for the chosen function instance, then applies pad10*1 so the resulting bitstring fits neatly into r-bit chunks. Because the message is short, maybe it occupies only one chunk. That chunk is XORed into the visible r-bit part of the zero state. Then the full 1600-bit state is permuted. At that point, the state contains a thoroughly mixed image of the message, but only part of that state is ever exposed. The hash is then taken from the first 256 output bits produced by the squeeze phase. What makes the construction secure is not that the message touched every bit directly, but that the permutation keeps diffusing what entered the rate across the whole state, including the hidden capacity.
What is Keccak-f[1600] and how does its permutation operate?
Under the sponge sits a family of permutations called Keccak-f. The standard widths are 25, 50, 100, 200, 400, 800, 1600 bits. In practice, the important one for Keccak-256 is Keccak-f[1600]. This width was chosen so one permutation could support all the main instances while mapping efficiently onto 64-bit CPUs.
The 1600-bit state is organized as a 5 × 5 array of lanes. Since 1600 = 25 × 64, each lane is 64 bits wide. This arrangement is not cosmetic. The round function is built around operations that mix bits within lanes, across rows, and across columns, so the grid gives the permutation a regular structure that implementations can exploit.
Each round applies five named steps: theta, rho, pi, chi, and iota. It helps to think of them by what they accomplish rather than by memorizing the names. One step mixes information across columns so that each bit becomes influenced by a broader neighborhood. Another rotates bits within lanes so patterns do not stay aligned. Another rearranges lane positions so local influence gets transported elsewhere. The nonlinear step combines nearby bits in a way that prevents the whole permutation from being described as a simple linear system. The final step injects a round constant so the permutation does not preserve dangerous symmetries.
For Keccak-f[1600], there are 24 rounds. The Keccak designers describe this as a conservative choice with a substantial safety margin. That is a different lever from capacity. Capacity governs generic sponge security; round count governs how much confidence you have that the permutation itself resists structural attacks. Keeping those levers conceptually separate is useful. If someone says “Keccak has 24 rounds,” that is not the same kind of claim as “Keccak-256 has capacity 512.” One speaks to the permutation’s internal robustness; the other speaks to the sponge instance’s generic security level.
What exactly does ‘Keccak-256’ mean in practice (Ethereum vs. SHA3-256)?
| Name | Suffix bits | r / c | Compatible with |
|---|---|---|---|
| SHA3-256 (NIST) | 01 | r=1088 / c=512 | FIPS 202 implementations |
| Keccak-256 (Ethereum/plain) | Different contest padding | r=1088 / c=512 | Ethereum tooling (keccak256) |
At this point, the most important naming distinction can be made precisely.
In the Keccak family, a function instance is defined by its sponge parameters and any suffix bits used to separate domains. NIST standardized a subset of the family in FIPS 202 as SHA3-224, SHA3-256, SHA3-384, SHA3-512, SHAKE128, and SHAKE256. For SHA3-256, NIST specifies KECCAK[512] with the message suffixed by the two-bit string 01, then truncated to 256 output bits. The capacity is 512, so the rate is 1600 - 512 = 1088.
That should sound close to Keccak-256 (and it is close) but it is not identical to the variant used in Ethereum. Ethereum’s protocol specification explicitly says it uses the original Keccak contest submission version, often called plain Keccak, rather than the final NIST SHA-3 specification. The difference is not the permutation width or the 24 rounds. The crucial difference is the padding and domain-separation convention, namely the suffix bits appended before the sponge padding is finalized.
This is why keccak256("abc") in Ethereum-oriented libraries does not match SHA3-256("abc") from a FIPS 202 implementation. The internal machinery is largely the same, but the instance definition is not. The functions live in different domains, by design. Domain separation is not a bug or an implementation quirk. It is a deliberate way to ensure that standardized hash functions and XOFs built on the same primitive do not accidentally collide as “the same function with a different name.”
So when developers casually use “sha3” to mean Ethereum’s keccak256, they are usually naming the family or the competition-era algorithm, not the FIPS 202 standardized function. That shortcut has caused years of interoperability mistakes.
How do suffix bits and domain separation change Keccak function instances?
It can seem odd that appending a couple of bits changes the identity of the function so fundamentally. But from the sponge’s point of view, the input is exactly what you feed it. If two named functions append different suffixes, they are different functions even if they share the same permutation and the same rate/capacity pair.
The reason this is valuable is simple: many tools want several cryptographic functions from one underlying primitive. A fixed-length hash, an extendable-output function, and a customizable XOF should not all map the same raw message to related outputs by accident. Suffixes give each function its own namespace. FIPS 202 uses this to distinguish the SHA-3 hashes from SHAKE, and related standards such as SP 800-185 build further customizable functions on top of the same core idea.
This also explains a common misunderstanding in blockchain development. If a library says it implements “SHA-3” but it is meant for Ethereum compatibility, that wording is dangerously incomplete. Compatibility depends on the exact instance, including suffix handling. The safest mental model is: Keccak-f is the shared engine; named hash functions are specific ways of feeding and reading that engine.
What security guarantees does the Keccak sponge provide and what limits apply?
Keccak’s designers describe their security argument as a flat sponge claim. The rough idea is that if the permutation has no exploitable structural weakness, then the sponge behaves like a random oracle up to an advantage term driven mainly by the capacity. The standout term in the design documents scales like N^2 / 2^(c+1) for N calls or processed blocks in the distinguishing bound. You do not need the exact formula for ordinary use, but the consequence is important: capacity is the parameter that caps generic attack resistance.
For a fixed-output hash with c = 512, that gives the familiar picture. Collision attacks are generically limited around 2^(256) work in the state-based bound but effectively around 2^(128) because collisions on a 256-bit digest already obey the birthday bound. Preimage resistance is then associated with the 256-bit output length, while the sponge construction’s own generic ceiling remains tied to capacity. This is why NIST’s SHA3-256 uses c = 512: it aligns the sponge parameters with the desired security goals for a 256-bit digest.
The design documents also emphasize a subtle point for variable-output Keccak instances. More output bits do not magically raise security above the capacity-based ceiling. If an instance has capacity 576, then its claimed ceiling is 2^(288), even if you ask it for 512 output bits. That matters when people treat “more digest bits” as automatically equivalent to “more security.” In sponge constructions, that is only true up to the limit imposed by capacity.
There is also an important boundary between theory and engineering. The sponge security claim assumes the permutation behaves as intended; essentially, that no practical structural distinguisher turns into a real attack on the deployed construction. Researchers have studied reduced-round and structural properties of Keccak-f, and the Keccak team has addressed such analyses directly. The current practical status is that these do not amount to a break of Keccak-256 as used in standards or major protocols, but this is exactly the kind of distinction careful cryptography needs: a structural observation about a permutation is not automatically an attack on the hash function built from it.
Keccak-256 vs SHA-256: how do their internal designs differ?
Keccak-256 and SHA-256 solve the same external problem (map arbitrary input to a fixed-size digest with strong one-way and collision-resistant properties) but their internal logic differs sharply.
SHA-256 is built from the Merkle–Damgård pattern with a dedicated compression function and a narrow chaining value. Keccak uses a sponge construction over a large permutation state with an explicit rate/capacity split. The consequence is not just aesthetic. Sponge constructions naturally support variable-length output, straightforward domain separation, and a tunable security/performance tradeoff through r and c. In contrast, classic Merkle–Damgård designs are more naturally framed as fixed-output iterated compression.
That does not make one universally “better” in every engineering context. It means the underlying abstraction is different. Keccak’s design gives you a family of related primitives from one core mechanism. This is why the same foundation supports SHA3-256, SHAKE256, cSHAKE, KMAC, and more. The function is not merely “a hash with 256 bits out.” It is a configurable sponge built on a common permutation.
Where is Keccak-256 actually used in blockchains and software?
The most famous practical use is Ethereum. The protocol uses plain Keccak-256 for block header fields, state roots, transaction-related trie roots, storage-key mapping, and account code hashes. Solidity exposes this directly as keccak256(bytes), and function selectors are derived by taking the first four bytes of keccak256 over the function signature string. If you compute a selector with FIPS SHA3-256 instead, you get the wrong answer.
A concrete example helps. The selector for a function such as transfer(address,uint256) is defined as the first four bytes of keccak256(bytes("transfer(address,uint256)")). Those four bytes are then placed at the front of calldata so the EVM can dispatch to the correct function body. Nothing about this mechanism is “approximately Keccak.” It depends on exact byte-level agreement. A different suffix convention yields a different 32-byte digest, which yields a different selector, which means the call no longer names the same function.
Ethereum’s use is not the only place Keccak-256 appears. Solana exposes a sol_keccak256 syscall so programs can compute a Keccak-256 hash inside the runtime. That does not make Keccak the chain’s universal consensus hash in the way it is woven through Ethereum state, but it shows the primitive is useful beyond one ecosystem. More broadly, any EVM-compatible environment inherits the need for Ethereum-compatible Keccak behavior if it wants byte-for-byte compatibility with contracts, selectors, receipts, and state-related encodings.
This is the practical rule worth remembering: when interoperability matters, the exact variant matters more than the family name.
What implementation risks and real-world vulnerabilities affect Keccak deployments?
| Risk | Cause | Effect | Mitigation |
|---|---|---|---|
| Integer overflow | 32-bit counter wrap | Memory corruption and RCE | Bounds checks and 64-bit counters |
| Wrong padding variant | Using contest vs NIST padding | Incompatible digests | Use instance's exact suffix/padding |
| Packed ABI misuse | abi.encodePacked ambiguity | Hash collisions | Use explicit, unambiguous encoding |
The cryptographic design and the implementation are separate risk layers. A correct algorithm can still be embedded in unsafe code.
That is not hypothetical for Keccak-family software. A published vulnerability analysis described a serious buffer-overflow issue in certain final-round Keccak and XKCP-derived implementations, triggered by a sequence of calls involving very large inputs and integer overflow in absorb logic. The important lesson is not that Keccak was broken. The analysis explicitly distinguishes the implementation flaw from the SHA-3 standard itself. The lesson is that sponge-based APIs, especially incremental Init–Update–Final interfaces, need careful bounds handling and testing for edge-case message lengths.
This is also why the XKCP codebase matters. It is the Keccak team’s main open-source implementation package, with portable and optimized variants split between high-level constructions and low-level state/permutation code. For implementers, that separation is useful because the construction logic can stay simple and auditable while the permutation layer gets hand-tuned for SIMD or specific architectures.
Key takeaway: what to remember about Keccak-256 and its variants
Keccak-256 is best understood not as “just another 256-bit hash,” but as a specific sponge instance built on the Keccak-f permutation, where security and performance are controlled by the split between exposed rate and hidden capacity. That is why it can serve as both a practical hash and the basis for a wider family of standardized functions.
And the naming caveat is not incidental: Ethereum’s keccak256 is the original Keccak variant, not the same function as FIPS 202 SHA3-256. If you remember that the shared engine is the permutation, while the named function is defined by its parameters and suffixes, most of the confusion around Keccak-256 disappears.
What should you check before using Keccak-256 for transfers or contract calls?
Before you rely on Keccak-256 for deposits, signatures, or contract calls, confirm which Keccak variant the destination expects (Ethereum's plain Keccak vs. NIST SHA3-256) because a mismatch changes selectors, checksums, and digests. Use Cube Exchange to fund an account, run a small, verifiable test transaction, and only then move larger amounts.
- Fund your Cube account with fiat or a supported crypto transfer.
- Verify the destination chain and token contract on Cube; check the protocol docs or ABI to confirm it expects Ethereum plain Keccak (contest submission) rather than FIPS SHA3-256.
- Compute any required hashes locally and compare bytes: for function selectors, confirm the first 4 bytes of keccak256(signature) match the contract ABI; for addresses, verify the EIP-55 checksum derived by keccak256.
- Send a small test transfer through Cube and confirm the exact on-chain receipt and contract behavior before executing the full trade or withdrawal.
Frequently Asked Questions
They use the same Keccak-f permutation and the same 1600-bit width in practice, but they differ in padding/suffix/domain-separation: Ethereum uses the original Keccak contest submission (often called plain Keccak) while NIST’s SHA3-256 is the Keccak sponge with a specific two-bit suffix and FIPS 202 conventions, so keccak256("abc") in Ethereum does not equal SHA3-256("abc").
Keccak splits its state into an exposed rate r and a hidden capacity c so you can trade throughput for generic security: a larger rate processes more message bits per permutation (faster), while the capacity is the security buffer that primarily governs the generic resistance bounds.
No - a 256-bit digest does not automatically give 256 bits of security for every goal; generic sponge security is capped by the capacity c (e.g., with c = 512 the collision-bound scales like about 2^(c/2) and practical collision effort for a 256-bit digest is constrained by the birthday bound around 2^128).
Because the sponge treats the input bit-for-bit, appending different suffix bits or using different padding yields different functions; suffixes are deliberate domain separators so a fixed-length hash, an XOF, and other modes built from the same permutation do not collide or interfere.
The 24 rounds of Keccak-f[1600] are a conservative parameter to strengthen the permutation against structural attacks; round count is about the permutation's internal robustness and is a different security lever than capacity, which governs the sponge-level generic bounds.
The sponge can produce an unbounded output stream by repeated squeezing, and a fixed-length hash like Keccak-256 is simply the first 256 bits of that stream, whereas XOFs use the same mechanism but continue squeezing to produce more output on demand.
Practical vulnerabilities have occurred in implementations (not the design), for example a published integer-overflow/buffer-overflow bug in some XKCP-derived code triggered by very large Update calls (~4 GiB) and tracked as CVE‑2022‑37454, illustrating that incremental sponge APIs need careful bounds checking.
If you need byte-for-byte compatibility with Ethereum contracts, selectors, or state roots, you must use Ethereum’s plain Keccak variant (the contest submission) rather than FIPS SHA-3, because selectors are computed from exact keccak256 bytes and a different suffix yields different selectors.
No; asking a sponge for more output bits does not raise the construction’s generic security ceiling beyond what the capacity imposes - for example, an instance with c = 576 has a capacity-based ceiling around 2^288 even if you request 512 output bits.
They differ in architecture: SHA-256 is a Merkle–Damgård/iterated-compression design with a narrow chaining value, while Keccak is a sponge over a large permutation with an explicit rate/capacity split, which makes Keccak naturally support XOFs, domain separation, and a tunable speed/security tradeoff.
Related reading