What Is Taproot?
Learn what Taproot is in Bitcoin, how key-path and script-path spending work, why Schnorr signatures matter, and what Taproot changes in practice.
Introduction
Taproot is Bitcoin’s SegWit v1 output design that lets an output be spent either by a single Schnorr signature or by revealing only the specific Script branch that was actually used. That sounds like an implementation detail, but it solves a deep mismatch in older Bitcoin outputs: before Taproot, complicated spending policies usually had to look complicated on-chain even when everyone cooperated and took the simplest path. Taproot changes that default. It makes cooperation cheap and private, while still preserving an escape hatch for more complex conditions.
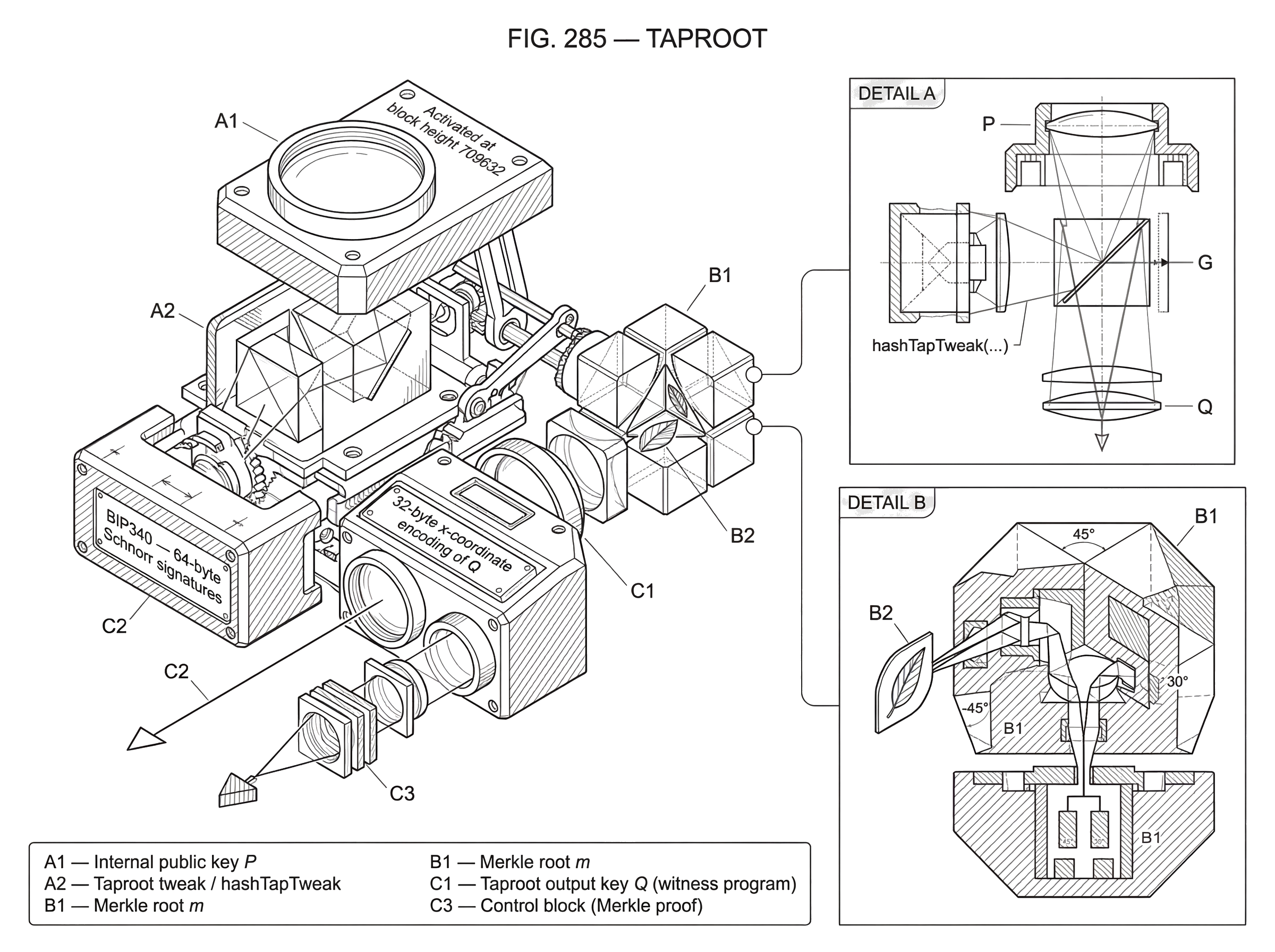
The key idea is simple enough to remember: commit to all your backup rules now, but reveal nothing except the path you actually use later. To make that work in Bitcoin’s UTXO model, Taproot combines three pieces that fit together tightly: Schnorr signatures from BIP340, a new output construction from BIP341, and new script rules called Tapscript from BIP342. If you understand how those three pieces cooperate, Taproot stops looking like a bag of cryptographic tricks and starts looking like a very clean redesign of what a Bitcoin output can be.
What problem does Taproot solve in Bitcoin outputs?
Bitcoin outputs do two jobs at once. They lock coins to some spending condition, and they later force the spender to prove that condition was satisfied. In older designs, those two jobs were often entangled in a wasteful way. If you wanted a 2-of-3 multisig with a timelocked recovery clause, you usually had to publish a script structure that exposed more about your wallet policy than the chain really needed to know. Even if all signers cooperated and the “happy path” was just a normal payment, the transaction could still reveal that it came from a multisig or a more elaborate contract.
That creates three costs.
First, there is a Privacy cost. On-chain observers learn something about the wallet structure, fallback conditions, and sometimes even about paths that were not used. Second, there is an efficiency cost. Bigger scripts and witnesses consume more block space and therefore more fees. Third, there is a fungibility cost. If some coins visibly came from unusual policies while others came from plain single-key outputs, then not all spends look alike.
Taproot’s design starts from a different question: what should the chain learn in the best case, when all participants agree and can sign cooperatively? The answer is: ideally, almost nothing beyond “a valid spender authorized this.” If no dispute happened and no fallback branch was needed, there is little reason to reveal the whole policy tree.
How does a Taproot output support key-path and script-path spending?
| Spending path | On-chain reveal | Typical cost | Best for |
|---|---|---|---|
| Key path | only Schnorr signature | low witness size | cooperative single/multisig |
| Script path | script leaf + Merkle proof | higher witness size | fallbacks and complex policies |
A Taproot output has two spending paths.
The first is the key path. In that case, spending the output requires only a valid Schnorr signature for the output key. Nothing else needs to be revealed on-chain about any hidden scripts. If the participants arranged their policy so that the cooperative case can be represented by a single public key (including an aggregated multisig key) the spend looks like an ordinary single-signature spend.
The second is the script path. In that case, the spender reveals a specific script leaf, the inputs that satisfy that script, and a Merkle proof showing that this leaf was committed to by the output. Crucially, the spender reveals only the branch that was used, not the entire set of alternatives.
This is the compression point of Taproot: an output commits to both a public key and an optional tree of scripts, but the cooperative spend reveals only a signature, and the non-cooperative spend reveals only one script branch. The chain gets exactly the information it needs to validate the spend, and no more.
How is the Taproot output key (Q) constructed from P and a script Merkle root?
| Case | Internal key | Merkle root | Tweak input | On-chain Q |
|---|---|---|---|---|
| No script tree | P (x-only pubkey) | empty root | hash(bytes(P)) | Q = P + hash(P)·G |
| With script tree | P (x-only pubkey) | m (root of leaves) | hash(bytes(P) || m) | Q = P + hash(P||m)·G |
Now the mechanism.
Start with an internal public key P. This is a BIP340 x-only public key, meaning it is encoded as a 32-byte x-coordinate with an implied even y-coordinate convention. If you have no script conditions at all, you can still use Taproot by committing to an empty or unspendable script tree; the point is that every Taproot output starts from this internal key.
If you do have script conditions, arrange them as leaves of a Merkle tree. Each leaf commits to a script and a leaf version, and the tree has a Merkle root m. Instead of putting P directly on-chain, Taproot tweaks it into a new public key Q. Informally, the rule is:
Q = P + hashTapTweak(bytes(P) || m) * G
Here G is the secp256k1 generator point, and hashTapTweak(...) is a tagged hash defined by the Taproot spec. The important intuition is not the elliptic-curve algebra itself, but what the tweak accomplishes: the on-chain key Q commits to both the internal key and the script tree. Anyone who later sees a script-path spend can recompute the tweak from the revealed internal key and Merkle root and verify that the script really was committed to when the output was created.
The witness program of a Taproot output is just the 32-byte x-coordinate encoding of Q. On-chain, that is all you see at creation time: a SegWit version 1 output with a 32-byte program.
Why does Taproot require Schnorr signatures instead of ECDSA?
Taproot depends on Schnorr signatures, and not merely because Schnorr is “newer” than ECDSA. The important property is structural.
BIP340 standardizes 64-byte Schnorr signatures over secp256k1 and uses x-only 32-byte public keys. That already makes Taproot’s encoding cleaner and more regular. But the deeper reason is that Schnorr signatures interact well with key aggregation. Multiple participants can combine public keys into a single aggregate key and, with an appropriate multisignature protocol such as MuSig2, produce a signature that verifies exactly like an ordinary single-party Schnorr signature.
That means a cooperative multisig under Taproot can use the key path and appear on-chain as a simple single-key spend. The privacy improvement comes from the chain seeing the result (one public key, one signature) rather than the organizational structure behind it.
There is also a subtle security reason BIP340 was designed the way it was. Its challenge hash includes the public key, a design often called key prefixing. That matters because Taproot relies on tweaking keys. Without protection against related-key attacks, key derivations of the Taproot sort could create dangerous signature malleability or conversion problems. BIP340’s signing equation was chosen to make such tweaks safe in the intended model.
And there is a practical node-level benefit: BIP340’s Schnorr variant supports batch verification. Nodes validating many signatures may be able to verify them more efficiently in aggregate, reducing CPU cost for blocks full of Taproot signatures.
What does a cooperative Taproot spend look like versus a fallback script spend?
Imagine a company treasury controlled by three officers. Under the ordinary operating policy, any two of the three should approve a payment. But there is also a recovery rule: if the company loses access to two keys, a cold backup key can spend the funds alone after a long timelock.
Before Taproot, the company might place this whole policy into a script-based output. When spending, the chain would often learn that the coins came from a multisig policy, and depending on the construction, might also learn more of the policy structure than was necessary.
With Taproot, the company can set up a cooperative aggregated key for the normal path and place the recovery rule in a hidden script leaf. On-chain, the output just looks like a 32-byte Taproot key. Months later, suppose two officers cooperate normally. They run a Schnorr multisignature protocol off-chain, produce one valid signature for the tweaked output key, and spend through the key path. The blockchain does not learn that there were three officers, that the normal policy was 2-of-3, or that a recovery clause existed.
Now consider the bad case. Two keys are unavailable, so the company must use the cold backup after the timelock expires. In that spend, they reveal the specific recovery script, the witness data satisfying it, the internal key, and a control block containing the Merkle path. Observers now learn that this particular branch existed and was used. But they still do not learn what other branches may have existed elsewhere in the tree.
This is the pattern Taproot was built for: hide complexity when cooperation succeeds; reveal only the minimum branch when cooperation fails.
What changes does Tapscript introduce to script-path spending and opcodes?
| Area | Legacy Script | Tapscript | Practical effect |
|---|---|---|---|
| Signature type | ECDSA signatures | Schnorr (BIP340) | supports key aggregation, batch verify |
| Multisig primitive | OPCHECKMULTISIG | OPCHECKSIGADD | batch-friendly threshold logic |
| Resource limits | global script/opcode caps | per-script sigops budget | cost tied to witness size |
| Upgrade hooks | no reserved success opcodes | OPSUCCESSx and annex | future soft-fork extensibility |
Taproot’s script path is not just “old Script inside a Merkle tree.” BIP342 defines Tapscript, which changes how script-path validation works.
Most importantly, signature opcodes in Tapscript use Schnorr verification per BIP340 and a signature message scheme based on BIP341. The legacy OP_CHECKMULTISIG and OP_CHECKMULTISIGVERIFY opcodes are disabled. In their place, Tapscript introduces OP_CHECKSIGADD, which lets scripts express multisignature policies in a way that is friendlier to batch verification.
This shift matters because old CHECKMULTISIG carried historical quirks and inefficiencies. Tapscript moves toward smaller, more regular primitives. Instead of a special-purpose multisig opcode with awkward semantics, script authors can build threshold conditions by accumulating successful signature checks with OP_CHECKSIGADD and then comparing the total against a threshold.
Tapscript also changes resource accounting. The old fixed limits such as the 10,000-byte script-size rule and 201 non-push-opcode rule no longer apply in the same way. Instead, Tapscript uses a per-script sigops budget tied to witness size: the budget is 50 + witness_size, and each executed signature opcode with a non-empty signature consumes 50 units. This changes the way cost and denial-of-service resistance are balanced. The design ties the computational burden of signature checking more directly to the amount of witness data the spender is already paying to include.
There are also upgrade hooks. Certain opcodes are designated OP_SUCCESSx: if encountered, validation succeeds immediately under current rules. That sounds strange, but the purpose is to reserve room for future soft-fork upgrades. The caveat is important: using such opcodes before future meanings are defined is unsafe and can lead to fund loss.
How did Taproot redesign signature hashing (SigMsg and SIGHASH_DEFAULT)?
Taproot is not only about output structure. It also changes what signatures commit to.
BIP341 defines a new common signature message, often called SigMsg, and a new tagged-hash-based signature hashing algorithm. One important improvement is that Taproot signatures commit to the amount and scriptPubKey of spent outputs. This fixes a long-standing problem for offline signers and Hardware Wallet, which previously could not safely verify all relevant transaction details without extra trust in the host.
There is also a new default hash type, SIGHASH_DEFAULT, which avoids wasting a byte in the common case. More broadly, the hashing scheme was designed to remove unnecessary duplication and organize commitments more cleanly.
This part is less visible to ordinary users, but it is central for wallet engineering. Taproot did not merely hide scripts better; it also cleaned up the rules for what exactly a signature authorizes.
How are wallets and users using Taproot in practice?
The most direct use is single-signature P2TR outputs. Even without script branches, wallets may prefer Taproot because it provides a modern output type with Schnorr signatures and a clean upgrade path. The input-side spend cost for single-sig Taproot can be lower than older designs, though output and ecosystem tradeoffs still matter for wallet adoption.
The more transformative use is multisig that does not look like multisig. Using Schnorr-based aggregation protocols, an n-party wallet can publish one key and, in the cooperative case, produce one signature. That reduces on-chain footprint and improves privacy. The chain sees a valid authorization, not the internal voting rule.
Taproot also matters for more advanced protocols because Schnorr signatures support constructions such as adaptor signatures, which are useful for Point Time Locked Contracts and related designs. Those ideas are especially important in Lightning-style protocols, where reducing linkability and on-chain footprint can have outsized effects.
And then there is a use Taproot did not primarily set out to optimize: data-carrying witness usage, including inscriptions. Taproot’s witness structure and script-path flexibility made some forms of on-chain data embedding easier or cheaper to express. That is not the same thing as Taproot being “for inscriptions,” but in practice Taproot-era witness space became part of how such protocols were built. This has led to significant debate over relay policy, resource costs, and what Bitcoin nodes should treat as acceptable transaction forms.
What privacy and efficiency improvements does Taproot provide; and what are its limits?
Taproot improves privacy, but only in a conditional sense.
If users spend through the key path, and if their wallet uses aggregation correctly, then a complex policy can be indistinguishable on-chain from a simple single-key spend. That is a real privacy gain. But it is not magic anonymity. Wallet fingerprints, amount patterns, address reuse, timing, change heuristics, and off-chain coordination leaks can still reveal a great deal. Taproot reduces one important source of information leakage (script structure) but it does not erase the rest of transaction analysis.
Taproot also improves efficiency, but again conditionally. It saves space especially when many possible branches exist but only one needs to be revealed, or when multisig can be aggregated into a single key-path spend. If users fall back to script-path spends frequently, or if they do not use key aggregation, some of the savings disappear.
And Taproot improves extensibility. Tapscript’s cleaner opcode semantics, leaf versioning, annex reservation, and OP_SUCCESSx design all create room for future soft forks. But extensibility is not the same as immediate capability. The annex, for example, is reserved for future extensions and the specification explicitly warns users not to include it until defined by another soft fork.
What are Taproot’s main assumptions and failure modes (nonce handling, tree construction)?
The biggest operational assumption is correct nonce handling in Schnorr signing, especially in multisignature protocols. BIP340 strongly warns that reused or predictable nonces can leak private keys. In MuSig-style signing this is even more delicate: reuse of a partial nonce can compromise not just a single key but, in some deployment patterns, much more. Taproot’s cryptography is elegant, but it is unforgiving if implementations mishandle nonce generation.
Another assumption is that wallet software constructs the tree and tweaks correctly. The control block in script-path spends must prove the committed branch exactly, and Merkle path depth is bounded. Implementers also need to respect details like x-only key conventions and tagged hashing. These are not optional formatting choices; they are consensus-critical rules.
There are also implementation-level risks that are not flaws in the abstract design. Post-activation research identified a Taproot-related denial-of-service issue in Bitcoin Core’s sighash implementation where repeated SIGHASH_SINGLE output hashing could create heavy validation costs until caching was added. That was an implementation vulnerability, not a consensus break, but it is a useful reminder: protocol design and software engineering are different layers, and both matter.
Some controversy around Taproot has also come from policy rather than consensus. Witness scripts have been used to bypass older assumptions about datacarriersize policy, enabling inscription-style data embedding. Whether that counts as a “bug,” a policy gap, or simply an allowed use of witness space is disputed. What is clear is that Taproot changed the practical landscape of what could be expressed in witness data and what relay policy needed to consider.
How does Taproot fit into the Bitcoin stack (SegWit, Schnorr, Miniscript)?
Taproot depends directly on SegWit and Schnorr signatures.
It depends on SegWit because Taproot outputs are SegWit version 1 outputs. Without SegWit’s separation of witness data from the transaction ID and its witness program structure, Taproot would not fit cleanly into Bitcoin’s transaction model. It depends on Schnorr because key-path spending, x-only keys, and aggregation-friendly signatures all come from BIP340’s design choices.
It also connects naturally to Miniscript and descriptor-based wallet tooling. Taproot’s script tree can become complicated to reason about if built manually. Tools that can analyze spending policies, compile them into scripts, and describe them in machine-readable descriptors make Taproot much more practical for real wallets and services.
How was Taproot activated and what compatibility issues should users and wallets consider?
Taproot was deployed on Bitcoin mainnet and activated at block height 709632. As a soft fork, older nodes continue to operate, but non-upgraded nodes do not fully validate Taproot rules and may treat SegWit v1 outputs as anyone-can-spend. In other words, backward compatibility in the narrow consensus sense does not mean old software provides full security. Upgrading matters.
Taproot addresses use bech32m, not the original bech32 checksum used for SegWit v0 outputs. That sounds minor, but wallet software must handle the distinction correctly. Taproot adoption therefore required not just consensus changes in nodes, but coordinated updates across address handling, hardware signers, wallet descriptors, fee estimation, and signing logic.
Conclusion
Taproot is best understood as a new answer to a basic Bitcoin question: how can an output commit to rich spending conditions without forcing the blockchain to see all of that richness every time it is spent? Its answer is elegant. Put the cooperative case behind a Schnorr key, put the fallback cases behind a Merkle tree, and bind them together with a key tweak.
The result is a Bitcoin output that is more private in the common case, more efficient for many advanced policies, and cleaner to extend in the future. The memorable version is this: Taproot makes Bitcoin reveal complexity only when complexity is actually needed.
How do you get practical exposure to Bitcoin after learning Taproot?
Get exposure by trading or holding BTC and, if you want on-chain Taproot benefits, by sending BTC to a P2TR (bech32m) address. On Cube Exchange you can fund your account, trade the BTC spot market for immediate exposure, or use the withdrawal flow to hold funds on-chain in Taproot (P2TR) outputs that use Schnorr signatures.
- Deposit fiat or crypto into your Cube account using the fiat on‑ramp or a direct USDC/BTC transfer.
- Open the BTC/USD or BTC/USDC market on Cube and place a market order for immediate exposure or a limit order for price control.
- To hold on‑chain with Taproot, withdraw BTC from Cube and paste a P2TR (bech32m) receiving address into the withdrawal form.
- Review the Network Fees and confirmation target (Taproot spends use Schnorr signatures and often have smaller witness size), then confirm the withdrawal or trade.
Frequently Asked Questions
A Taproot output encodes a single on‑chain public key Q that is a tweak of an internal x-only key P and (optionally) a Merkle root of script leaves; in the cooperative case spenders produce a single Schnorr signature for Q and reveal nothing about any hidden scripts. This is achieved by computing Q = P + hashTapTweak(bytes(P)||m) * G and using Q’s 32‑byte x‑coordinate as the witness program, so the chain only sees an ordinary-seeming single-key spend when the key path is used.
When the script path is used the spender reveals only the specific script leaf that was executed, the witness data satisfying that leaf, and a control block containing the Merkle proof (and internal key) proving that leaf was committed to by the output; other branches in the tree remain hidden. Observers therefore learn that this particular branch existed and was used, but not what other branches may have been in the tree.
Taproot depends on BIP340 Schnorr because Schnorr provides compact 64‑byte signatures, x‑only 32‑byte public keys, and - critically - structural properties that enable secure key aggregation so cooperative multisigs look like single-key spends; BIP340’s design (including key prefixing) also protects the tweak-based constructions Taproot uses and enables node benefits like batch verification. These properties are the core reasons Taproot chose Schnorr over legacy ECDSA.
Implementers must ensure correct, fresh, unpredictable nonces for Schnorr signing because nonce reuse or predictable nonces can leak private keys; this risk is especially acute in multisignature protocols (e.g., MuSig/MuSig2) where partial-nonce reuse can compromise more than one key. BIP340 explicitly warns about nonce handling and recommends auxiliary randomness or protected synthetic nonces to mitigate nonce‑exfiltration attacks.
Until wallets and nodes upgrade, non‑upgraded clients will not fully validate SegWit version 1 outputs: older nodes may treat P2TR (Taproot) witness programs as anyone‑can‑spend, so relying parties and users are advised to upgrade their software to get full validation and security assurances. Taproot activated at block 709632, but practical safety requires ecosystem software (wallets, hardware signers) to also support the new address format and signing rules.
The annex is a reserved witness field for future extensions and users SHOULD NOT include an annex in transactions until its meaning is defined by a subsequent soft fork, because using it today can lead to permanent loss of funds. In short: do not include an annex until the protocol specifies its semantics.
Taproot’s Merkle proof (control block) path length is deliberately bounded - BIP‑341 limits path length to 128 - so trees that would require deeper paths should omit those leaves; this bound is part of the spec’s safety limits on tree construction. Implementations must respect this limit when building tap trees to ensure spent control blocks are valid and representable.
Taproot reduces script-structure leakage and on‑chain footprint in the common cooperative case, but it does not eliminate other privacy or fungibility leaks: address reuse, amounts, timing, change heuristics, wallet fingerprints, and off‑chain coordination can still reveal information. Likewise, efficiency gains depend on using the key path and aggregation; frequent fallback to script-path spends or lack of aggregation will reduce those savings.
Tapscript disables legacy CHECKMULTISIG opcodes and introduces OP_CHECKSIGADD for building threshold checks; it also changes sigop/resource accounting to a per-script budget of 50 + witness_size where each executed signature opcode with a non‑empty signature consumes 50 units. These changes aim to replace awkward legacy multisig semantics with a smaller, more regular set of primitives and to tie computational cost more directly to witness data size.
Related reading