What is Kamino?
Learn what Kamino is, how its Solana lending protocol works, how vaults and borrowing function, and why developers build on its APIs and SDKs.
Introduction
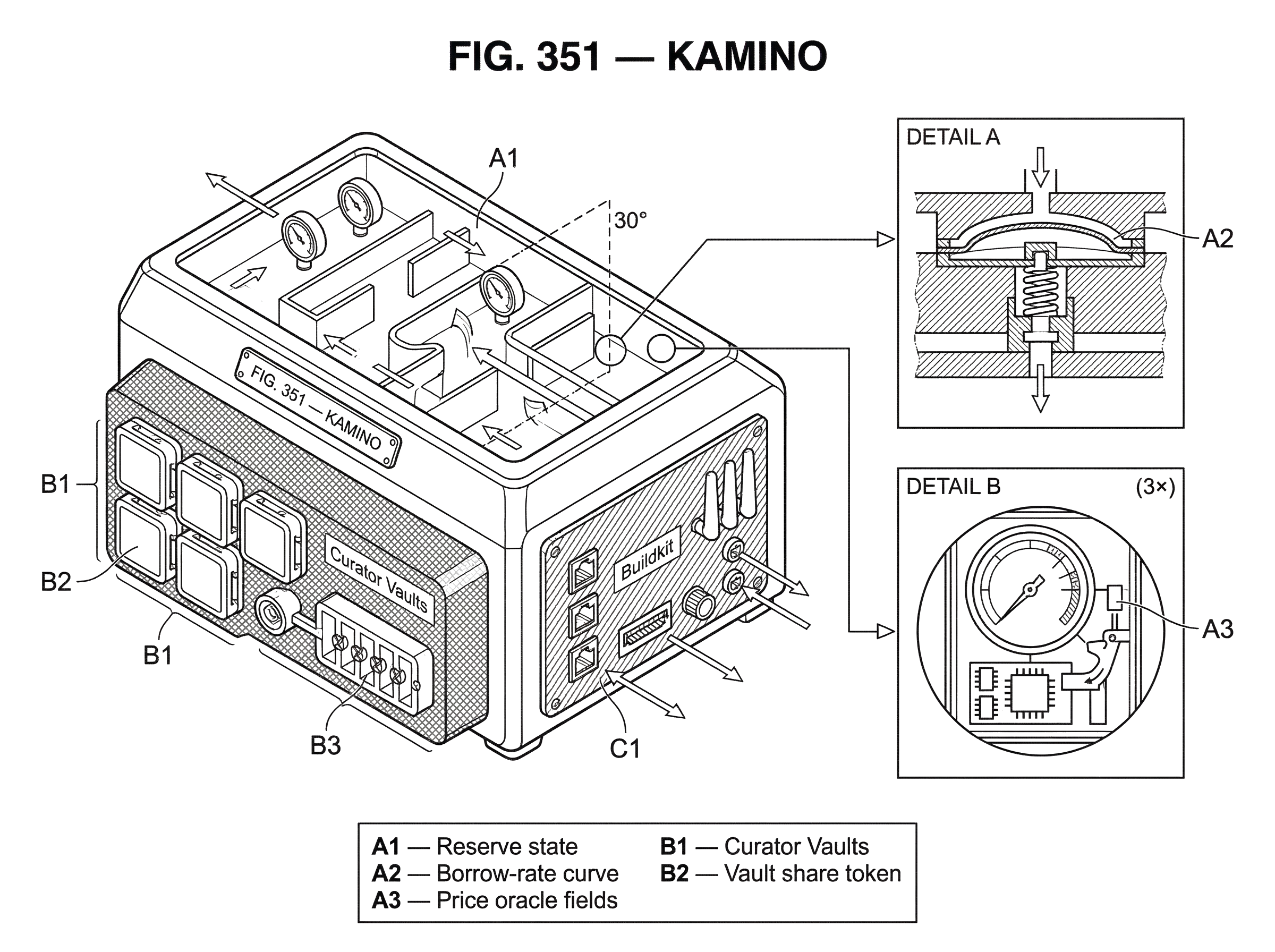
Kamino is a Solana-native DeFi protocol centered on lending, borrowing, and yield strategies, all presented as one connected product suite. That matters because in onchain finance, the hard part is often not a single action like “lend USDC” or “borrow SOL.” The hard part is stitching together markets, collateral rules, prices, and transaction flows into something people can actually use without losing track of risk. Kamino’s answer is to combine those pieces inside one system and one interface, while also exposing APIs and SDKs for builders who want to integrate the protocol directly.
At a high level, Kamino does two jobs at once. For end users, it offers lending markets where you can supply assets, borrow against collateral, and use more advanced strategies such as leveraged yield loops. For protocol operators and developers, it provides vault infrastructure and integration tools so they can build their own products on top of those same lending rails. The useful way to think about Kamino is not just as an app, but as a lending engine with a user interface on top and programmable surfaces around it.
What problem does Kamino solve in Solana DeFi?
A lending protocol exists to match two needs that naturally fit together. Some users want their assets to sit somewhere productive and earn yield. Other users want liquidity now and are willing to pay interest for it, as long as they can borrow against collateral they already hold. In a pooled lending market, suppliers make capital available, borrowers draw from that pool, and the protocol enforces the rules that keep the system solvent.
Kamino’s distinctive move is to make this pooled model do more than plain supply-and-borrow. Its public product overview describes a suite spanning Lending, Liquidity, and Leverage, and its API exposes separate surfaces for earn vaults, borrow markets, swap routes, user holdings, and transaction building. In practice, that means Kamino is designed for a reader who may start with a simple goal (earn on idle SOL or USDC, for example) but may also want to move into more structured strategies without leaving the same ecosystem.
This is why the protocol emphasizes analytics and position detail in its interface. Once lending, collateral, and leverage are combined, usability is not cosmetic. It is part of the safety mechanism. A user needs to see what they supplied, what they borrowed, how their position is changing, and where risk sits.
How does Kamino's lending engine work on Solana?
The core onchain unit in Kamino lending is the reserve. A reserve is the state for a specific asset market: it tracks available liquidity, borrowed amounts, prices, fee accumulators, collateral accounting, configuration, and a withdrawal queue. If you strip away the interface, this is the engine room. Suppliers add liquidity to reserves. Borrowers take liquidity out, provided they have enough acceptable collateral and remain within the protocol’s borrowing constraints.
The interest mechanism is dynamic rather than fixed. The reserve computes a current borrow rate from utilization, meaning how much of the pool is already borrowed relative to what is available. That utilization is fed into a configured borrow-rate curve, and interest accrues over time as the reserve is refreshed. The idea is straightforward: when a pool is heavily used, borrowing should become more expensive, which discourages additional borrowing and encourages more supply. When a pool has plenty of idle liquidity, rates can be lower.
That design matters because it keeps the pool responsive without an operator manually repricing every market. The invariant Kamino is trying to preserve is simple to state even if the code is not: the protocol must always know how much value is in a reserve, how much has been lent out, and whether borrowers still have enough collateral to support their debt.
A user-facing example makes this concrete. Suppose someone deposits USDC into Kamino. At the protocol level, the reserve checks that the amount is nonzero and that the reserve’s configured deposit limit is not exceeded. If the deposit is accepted, the pool’s available liquidity rises. Another user who has posted collateral can then borrow from that reserve, but only if the reserve and the user’s obligation state are fresh, borrowing is enabled, prices are current enough, liquidity is available, and the resulting debt does not violate market limits. What looks like a simple “Borrow” button in the app is therefore the visible end of several solvency checks.
Why does Kamino require fresh prices and account state for lending actions?
A subtle but important part of Kamino’s design is that many actions depend on fresh state, especially fresh prices. The lending code checks whether reserves and obligations are stale, and it can reject actions if updates have not occurred in the current slot or if price data is too old relative to configured thresholds. This is not a side detail. In an overcollateralized lending protocol, old prices can make a safe-looking borrow or withdrawal unsafe.
So here is the mechanism: reserves are refreshed, interest is accrued, and market price fields are updated. Only then can later steps such as borrowing, repaying, or withdrawing rely on the numbers in storage. The consequence is that some operations may fail when market data or account state is stale. For users, that can feel like friction. For the protocol, it is one of the guards that prevents solvency decisions from being made on outdated information.
This is also where a smart reader might misunderstand the phrase “transparent analytics.” Analytics help you understand a position, but they do not replace the protocol’s actual enforcement logic. Kamino’s safety model lives in its state updates, utilization-based rates, collateral checks, borrow limits, and liquidation rules.
How do collateral, borrowing, and liquidation work on Kamino?
| Position state | Trigger | Liquidation allowed | Liquidator incentive | User options |
|---|---|---|---|---|
| Healthy | Collateral > required LTV | No | None | Deposit, borrow, normal ops |
| Constrained | Tighter LTV or caps hit | Maybe limited | Reduced bonus caps | Reduce borrow or add collateral |
| Liquidatable | Threshold breached or other reason | Yes (per rules & caps) | Bonus within reserve caps | Forced sale or partial liquidation |
Kamino borrowing is overcollateralized. You do not borrow because the protocol trusts you; you borrow because you have deposited assets whose value, under the protocol’s rules, supports the debt. That distinction is fundamental. The system is not underwriting identity or cash flow. It is continuously comparing collateral value against debt value.
Withdrawals and new borrows therefore interact with the same core constraint: after the action, the position must still remain healthy enough under the allowed loan-to-value logic. If a user already has borrows outstanding, withdrawals require stricter freshness checks and can be limited by the maximum value that can safely leave the account. If assumptions change (for example, collateral falls in price, borrowed assets rise in price, or a reserve hits utilization or borrow caps) the room to maneuver shrinks immediately.
If a position crosses the protocol’s thresholds, liquidation becomes the repair mechanism. Kamino’s liquidation code computes how much debt can be liquidated, what bonus a liquidator may earn, how much collateral can be seized, and what fee the protocol takes from the liquidation bonus. The broad logic is familiar from other overcollateralized lending systems: when a borrower’s position becomes too risky, outside actors are incentivized to repay part of that debt in exchange for discounted collateral. That is not punishment in the moral sense; it is how the system restores solvency.
Kamino’s implementation adds nuance here. Liquidation triggers can come from more than a simple LTV breach, and the amount that can be liquidated depends on the liquidation reason and configured caps. Bonus rates are also bounded by reserve and market settings. The practical point for users is that risk is not binary. A position can move from healthy, to constrained, to liquidatable through a chain of state-dependent rules.
What are Kamino Curator Vaults and what trade-offs do depositors face?
| Option | Who decides | Control | Fees | Best for | Primary risk |
|---|---|---|---|---|---|
| Direct reserve deposit | User | Full user control | Lower base protocol fees | Users wanting simple yield | Manual reserve selection risk |
| Curator vault deposit | Curator | Delegated allocation | Vault management fees plus protocol | Passive depositors seeking strategy | Curator allocation and parameter risk |
| Create a vault (operator) | Operator/curator | Custom strategy & params | Earns fees from vault users | Teams offering branded yield | Operational and governance risk |
What makes Kamino more than a standard lending frontend is its vault layer. The developer docs describe Curator Vaults that let operators launch custom lending vaults with a single deposit token, route depositor assets across lending reserves, issue share tokens representing depositor positions, and configure allocation weights, caps, risk parameters, and fee structures.
This solves a different problem from ordinary lending. A basic lending market asks each user to choose where to deposit and how to manage exposure. A vault asks a curator to make those allocation decisions at the product level, so depositors can buy into a strategy rather than manually manage every reserve. The vault then distributes assets across reserves according to its configured strategy and issues shares so each depositor owns a proportional claim on the vault.
That design is especially useful for teams that want a branded or opinionated yield product without building a lending protocol from scratch. It is also useful for depositors who prefer delegated strategy design over direct reserve selection. The trade-off is equally clear: when you deposit into a vault, you are no longer choosing only Kamino’s base lending risk. You are also choosing the curator’s allocation logic, parameter choices, and fee model.
Who can build on Kamino and what APIs and SDKs are available?
| API surface | Purpose | Signing required | Common uses | Best for |
|---|---|---|---|---|
| Read-only endpoints | Market & historical data | No | Portfolio tracking, analytics | Dashboards and trackers |
| Unsigned txn endpoints | Build transactions server-side | Yes (client must sign) | Borrow/repay/withdraw flows | Wallet integrations and UI |
| TypeScript SDK / Buildkit | Convenience and helpers | Depends on flow | Programmatic vault ops, tx building | Product integrations and automation |
Kamino is built not only for traders and depositors, but also for developers. Its docs present Buildkit, open REST APIs, and a TypeScript SDK for onchain reads, historical metrics, transaction building, and advanced vault operations. The API surface includes earn vault data, lending market data, user positions, rewards, swap routes, and unsigned transaction endpoints.
That combination reveals who Kamino is for on the integration side. Portfolio apps can read user holdings and rewards. Trading or treasury tools can fetch market data and build borrowing or repay transactions. Protocol operators can create vault products that sit on top of Kamino’s lending rails. In other words, Kamino is designed to be embedded.
There is an important architectural detail here: some API resources are for data and analytics, while transaction-building resources are for constructing unsigned transactions. That means integrators still need to handle signing and submission on the client side. Kamino is supplying protocol-specific building blocks, not abstracting away wallet control.
What is Kamino's security posture and what operational constraints should users expect?
Kamino presents itself as secure and publicly maintains an audits repository with multiple audit and formal-verification reports across components, including lending. There is also a public Immunefi bug-bounty program. Those are meaningful signals that the team invests in external review, but they should be understood precisely. An audit is not a guarantee, and the existence of reports does not by itself tell you the status of every issue or the exact production code version covered unless you inspect the underlying documents.
The more useful constraint to remember is mechanical rather than rhetorical. Kamino’s lending system can reject actions because reserves are stale, prices are stale, deposit or borrow caps are hit, utilization is too high, borrowing is disabled, or the requested action would violate collateral safety. Those are not edge cases around the product. They are part of what the product is.
Conclusion
Kamino is best understood as a Solana lending engine with a layered product strategy. At the base are pooled reserves with utilization-based rates, collateral checks, freshness requirements, and liquidation rules. On top are vaults, leverage strategies, analytics, APIs, and SDKs that make those reserves usable by both end users and other teams.
If you remember one thing, remember this: Kamino’s value is not just that you can lend or borrow there. It is that the protocol turns lending markets into reusable infrastructure; for individuals managing positions, and for builders creating products on top of Solana’s DeFi stack.
How do you evaluate a DeFi lending or collateral market before using it or buying related tokens?
Before using a lending market or buying related tokens, run a focused protocol-risk checklist: read audits and bounty reports, verify oracle freshness and reserve constraints, assess liquidation mechanics and curator or vault exposure, and confirm token liquidity. After that research, use Cube Exchange to act on your decision by funding your account and placing an order for the token you want to hold.
- Read the protocol docs and public audits: open the audits repo and Immunefi page, note which contract versions were reviewed, and record any open or recently fixed findings.
- Check on-chain health signals: query reserve utilization, price-oracle age, deposit/borrow caps, and recent liquidation events via a block explorer or on-chain analytics tool; note any stale-price thresholds or queued-withdrawal mechanics.
- Measure token market depth and execution risk: review DEX/book liquidity, 24h volume, and estimated slippage for your intended trade size; prefer a limit order when depth is thin.
- Fund Cube Exchange and execute with control: deposit fiat or supported crypto, open the token market, place a limit order (or a market order if immediate execution is required), set a max slippage, then submit.
Frequently Asked Questions
Kamino computes the current borrow rate from reserve utilization using a configured borrow-rate curve; interest accrues when the reserve is refreshed, so higher utilization raises borrowing costs and lower utilization lowers them.
Many lending actions require fresh reserve, obligation, and price state; if accounts or prices are stale (not refreshed in the current slot or older than the configured thresholds) the protocol will reject borrows, withdrawals, or related operations to avoid making solvency decisions on outdated data.
Curator Vaults let an operator create a single-deposit-token product that routes depositor funds across Kamino reserves according to configurable allocation weights, caps, risk parameters, and fees, and issue share tokens representing pro rata claims; the trade-off is that depositors delegate allocation and curator risk choices rather than selecting individual reserves themselves.
Kamino’s API surface includes transaction-building endpoints that return unsigned transactions; integrators must perform client-side signing and submission because the API does not itself sign or submit transactions.
Liquidations are not a single binary check: triggers can come from multiple reasons beyond a simple LTV breach, and the liquidatable amount, bonus, and allowed seizure are calculated based on the liquidation reason, reserve/market caps, and configured parameters, so positions can move through constrained states before becoming liquidatable.
Kamino publishes audit and formal-verification reports in a public audits repository and runs an Immunefi bug-bounty program; however, audits and bounties are signals, not guarantees - you need to inspect individual reports for scope, the exact contracts/versions covered, and remediation status.
Kamino targets developers building portfolio apps, trading or treasury tools, and protocol operators who want to launch vault products; tooling includes Buildkit, open REST APIs, and a TypeScript SDK for on‑chain reads, historical metrics, transaction building, and advanced vault operations.
On‑chain constraints that can block otherwise-valid operations include reserve-level deposit and borrow limits, utilization thresholds, disabled-borrow flags, stale-state or price-age checks, and queued-withdrawal mechanics (withdraw_ticket/withdraw_queue) that enforce later processing of some withdrawals.
Related reading