What is X25519?
Learn what X25519 is, how Curve25519 Diffie–Hellman works, why the Montgomery ladder matters, and where implementations can still fail.
Introduction
X25519 is a specific function for doing elliptic-curve Diffie–Hellman key exchange on Curve25519. That may sound like a narrow technical definition, but it solves a broad and very practical problem: how two parties can agree on a shared secret over an untrusted network without exposing that secret to observers, and in a way that implementations can perform safely and consistently.
The reason X25519 matters is not merely that it is fast. Cryptography often fails at the boundary between elegant math and messy software, where corner cases, invalid inputs, encoding mismatches, and timing leaks create vulnerabilities. X25519 was standardized in RFC 7748 with exactly that reality in mind. Its design aims to make the secure path the natural path: fixed-size byte strings, a simple scalar-multiplication interface, and a ladder-based computation pattern that is well suited to constant-time code.
This is why X25519 shows up so often in modern systems. TLS 1.3 includes x25519 as a named group for ephemeral key exchange. Noise-based protocols use it as a standard Diffie–Hellman primitive. WireGuard builds its handshake around Curve25519 ECDH. Cryptographic libraries from OpenSSL to libsodium expose it directly because it is not just a curve, but a highly interoperable operation on that curve.
The key idea to hold onto is simple: **X25519 is not “all of Elliptic Curve Cryptography on Curve25519.” It is a carefully defined function that takes a private scalar and a public u-coordinate, and returns another u-coordinate. ** Once that clicks, most of its surrounding design choices start to make sense.
Why was X25519 designed and what practical problems does it solve?
At the heart of Diffie–Hellman is an asymmetry that cryptographers try to exploit. It should be easy to combine your private secret with someone else’s public value to get a shared result, but hard for an eavesdropper to recover that result from the public values alone. On elliptic curves, that “combine” operation is scalar multiplication: take a point on the curve and multiply it by a secret integer.
In principle, many elliptic curves can do this. In practice, implementing elliptic-curve Diffie–Hellman has long been full of traps. Some APIs expose too much of the underlying geometry. Some require validating whether an input point is on the curve, in the correct subgroup, or encoded canonically. Some implementation strategies branch on secret-dependent bits and leak information through timing or cache behavior. Even when the mathematics is sound, software can become fragile.
X25519 addresses this by narrowing the interface. Instead of asking developers to manipulate full elliptic-curve points with signs, multiple coordinate systems, and special cases, it asks for just two byte strings: a 32-byte scalar and a 32-byte u-coordinate, both little-endian. The output is another 32-byte u-coordinate. That is the whole API surface at the cryptographic core.
This matters because simpler interfaces reduce both accidental misuse and implementation variance. RFC 7748 explicitly specifies how inputs are decoded, how non-canonical values are handled, how the scalar is “clamped,” and how the Montgomery ladder should perform the multiplication. These details are not incidental formatting rules. They are the mechanism by which independent implementations produce the same results and avoid many side-channel pitfalls.
Curve25519 vs X25519: what’s the difference and why does it matter?
A common source of confusion is the difference between Curve25519 and X25519. Curve25519 is the underlying elliptic curve, with field modulus 2^255 - 19 and Montgomery parameter A = 486662. X25519 is the standardized Diffie–Hellman function defined on the Montgomery form of that curve.
That distinction is worth keeping sharp. A curve is a mathematical object. X25519 is an algorithm plus encoding conventions plus input-handling rules that tell you exactly how to use that object for key agreement. Two systems can both “use Curve25519” and still fail to interoperate if they do not agree on the same coordinate representation, scalar decoding rules, or public-key format. X25519 is the specification layer that removes that ambiguity.
The base point for X25519 is the u-coordinate 9. If Alice chooses a private scalar a, her public key is X25519(a, 9). If Bob chooses a private scalar b, his public key is X25519(b, 9). Alice computes X25519(a, B) using Bob’s public value B; Bob computes X25519(b, A) using Alice’s public value A. Under the algebra of the curve, both arrive at the same shared result.
Notice what is absent from this description: there is no need to serialize full affine points with both x and y, no explicit point-addition API, and no sign bit management for public keys. X25519 intentionally works with the Montgomery u-coordinate only. That narrower representation is one reason implementations can be simpler and less error-prone.
How does X25519 use the Montgomery ladder to compute scalar multiplication?
The computation inside X25519 is scalar multiplication on a Montgomery curve using the Montgomery ladder. The intuition is easier than the formulas might suggest.
Suppose your secret scalar is a string of bits. You could imagine processing those bits from most significant to least significant, updating a running pair of curve values at each step. One running value represents the current multiple of the input point; the other represents the next multiple. Each new scalar bit determines how those two values are transformed. The crucial feature is that the ladder performs the same pattern of field operations for every bit, regardless of whether the bit is 0 or 1. That regularity is what makes constant-time implementations easier.
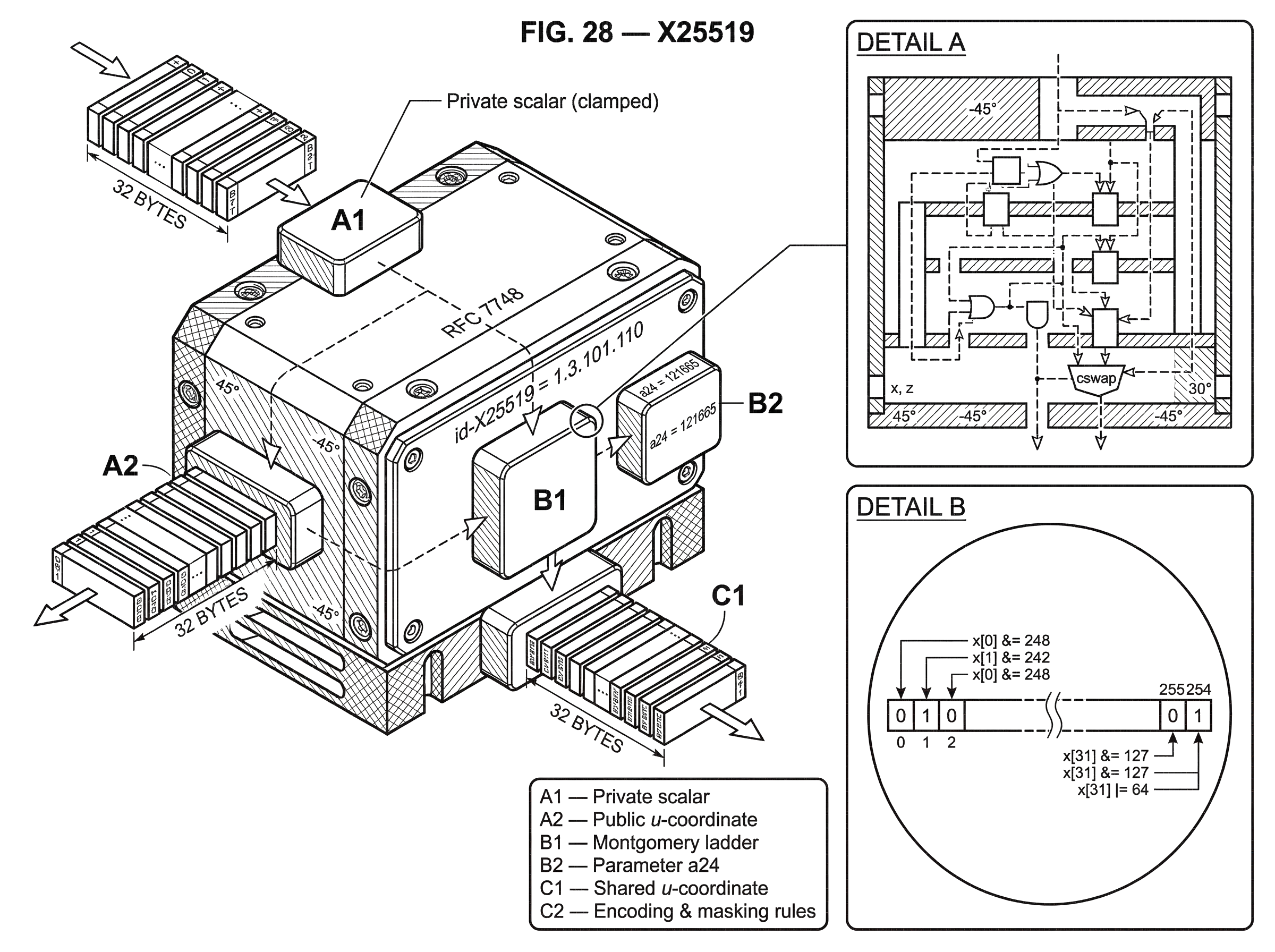
RFC 7748 specifies this algorithm with a constant-time conditional swap, often written as cswap, and a curve-specific constant a24 = 121665 for X25519. The ladder works in projective coordinates during the main loop, which avoids doing a costly field inversion at every step. Only at the end does the implementation convert back to an ordinary u-coordinate by multiplying by an inverse.
The point of this design is not elegance for its own sake. Here is the mechanism: if every secret-bit step uses the same instruction pattern and the same sequence of field operations, then a large class of timing leaks disappears. That does not make an implementation automatically safe (RFC 7748 is clear that memory access and arithmetic routines still must avoid secret-dependent leakage) but it gives implementers a much better starting point than generic elliptic-curve formulas often do.
An analogy can help here. X25519 is a bit like designing a road with guardrails so drivers are less likely to go off a cliff. The guardrails do not make accidents impossible; a careless driver can still crash. What they do is make the default path much safer. The analogy explains why X25519 is implementation-friendly, but it fails if taken too far, because real cryptographic side channels involve subtle interactions between code, compilers, CPUs, and memory systems, not just one obvious hazard.
Why does X25519 require specific byte encodings and scalar clamping?
| Value | Length | Endian | Decode rule | Accept non-canonical |
|---|---|---|---|---|
| Private scalar | 32 bytes | Little-endian | Clamp bits before decode | Not applicable |
| Public u-coordinate | 32 bytes | Little-endian | Mask MSB of final byte | Reduce modulo p |
| Shared output | 32 bytes | Little-endian | Return u-coordinate | Already reduced |
Much of X25519’s practical value comes from very exact byte-level rules.
Public inputs and outputs are 32-byte arrays interpreted in little-endian form. When receiving an input u-coordinate for X25519, implementations must mask the most significant bit of the final byte. They must also accept non-canonical inputs and reduce them modulo the field prime instead of rejecting them. This is an interoperability choice, but also a behavioral one: it reduces the chance that implementations can be fingerprinted or distinguished by how strictly they parse inputs.
Private scalars are also derived from 32 bytes, but not by simply interpreting those bytes as an integer. Before decoding, X25519 applies clamping: it clears the three least significant bits of the first byte, clears the most significant bit of the last byte, and sets the second most significant bit of the last byte. Only then is the result decoded as a little-endian integer.
Why do this? The short answer is that clamping forces the scalar into a form with useful structural properties for this curve and this ladder-based computation. In particular, it makes the scalar a multiple of the cofactor-related power of two that the construction expects, while fixing its size range so implementations work with a predictable bit length. This is partly about group structure and partly about implementation discipline.
A reader might reasonably wonder whether this is merely convention. It is not. If different implementations interpreted raw secret bytes differently, they would derive different public keys and different shared secrets from the same nominal key material. The clamping rule is part of the definition of X25519, not a local optimization.
How does a complete X25519 Diffie–Hellman exchange look in practice?
Consider Alice and Bob using X25519 for a fresh key exchange in a protocol like TLS 1.3 or Noise. Alice begins by generating 32 random bytes. Those bytes are not used directly as the scalar; she clamps them according to RFC 7748, treating the result as her secret scalar a. She then computes her public value A = X25519(a, 9), where 9 is the standard base-point u-coordinate, and sends the 32-byte result to Bob.
Bob does the same on his side. He generates 32 random bytes, clamps them into a scalar b, computes B = X25519(b, 9), and sends B back to Alice. At this stage, an eavesdropper can see A and B, because they are public handshake values.
Now the symmetry of Diffie–Hellman appears. Alice combines her private scalar with Bob’s public value and computes K = X25519(a, B). Bob computes K = X25519(b, A). The two results are equal because both are, algebraically, the same shared curve point reached by scalar multiplication in opposite orders. Neither side had to send K on the wire.
But an important practical detail comes next: protocols usually do not use the raw X25519 output directly as an encryption key. Instead, they feed it into a key-derivation function, often together with transcript information and the public keys. This matters because higher-level protocols need domain separation, key confirmation, and resistance to subtle equivalence issues. RFC 7748 warns that equivalent public keys can exist, and recommends including public keys in the KDF context.
That last step is where “X25519 the primitive” becomes “secure key establishment in a full protocol.” X25519 gives you shared secret material. The protocol turns that material into the exact keys and guarantees the application needs.
What is the cofactor problem in X25519 and why can the shared secret be all zeros?
X25519 is widely used because it is robust, but it is not magic. One of the most important subtleties is that Curve25519 has cofactor 8. That means the full group structure is not a single large prime-order group; there is a small subgroup sitting alongside the large one.
The practical consequence is that some malicious or specially chosen public inputs can cause the X25519 computation to land in a small-order result. In the extreme case, the shared output can become the all-zero 32-byte string. RFC 7748 says implementations may check for this all-zero shared value and abort. That wording is careful: the check is allowed and often useful, but not universally required at the primitive level.
Why is this a real issue? Because if a protocol treats every 32-byte X25519 output as equally good secret material, then small-order inputs can sometimes collapse the shared-secret space and enable active attacks. The exact consequences depend on the protocol around X25519. Some protocol designs are naturally resilient because they mix the output with authenticated transcript context or reject impossible states elsewhere. Others are more exposed.
This is one place where neighboring constructions become relevant. Ristretto, for example, exists precisely to build a prime-order group abstraction on top of cofactor-8 curves like Curve25519. That is useful in protocols (especially zero-knowledge and group-based constructions) where cofactor complications are awkward or dangerous. X25519 does not try to erase the cofactor; it gives a very specific, interoperable DH function despite it.
Real incidents show why these details matter. Vulnerability reports have documented failures around weak-order-point handling in Curve25519-based exchanges, where missing checks allowed man-in-the-middle manipulation of shared keys in higher-level systems. That does not mean X25519 itself is broken. It means the boundary between primitive behavior and protocol assumptions must be understood clearly.
Why is X25519 the default choice in modern protocols and libraries?
X25519 became a default choice because several desirable properties reinforce each other.
First, it is specified in a way that strongly encourages interoperable implementations. RFC 7748 nails down the byte encoding, the scalar decoding, and the ladder behavior. RFC 8410 then gives X25519 a standard object identifier, id-X25519 = 1.3.101.110, and defines how keys appear in PKIX and ASN.1 structures. This is what lets certificates, PEM files, PKCS#8 private keys, and SubjectPublicKeyInfo public keys refer unambiguously to X25519 keys.
Second, major protocols adopted it in the places where modern systems most need efficient ephemeral Diffie–Hellman. TLS 1.3 lists x25519 as a supported named group and uses the key_share extension to carry its public values. Noise defines a 25519 Diffie–Hellman function with 32-byte public keys and 32-byte outputs. WireGuard uses Curve25519 for ECDH inside its Noise-based handshake, and identifies peers by 32-byte Curve25519 public keys.
Third, the implementation ecosystem is mature. OpenSSL exposes X25519 via EVP_PKEY for key generation and derivation, with RFC 8410-compatible formats. Rust libraries such as x25519-dalek provide both low-level RFC 7748-style APIs and higher-level abstractions for ephemeral and static Diffie–Hellman. Libsodium makes X25519 easy to use directly and also exposes conversion functions between Ed25519 and Curve25519 key material for developers who need that bridge.
These are not separate stories. Standardization, protocol adoption, and library support feed each other. A primitive becomes common not just because its mathematics is good, but because engineers can carry it across files, certificates, APIs, and network handshakes without ambiguity.
Can X25519 be used for signatures or reused with Ed25519 keys?
| Aspect | Purpose | Public key derivation | Interoperability | Key reuse recommendation |
|---|---|---|---|---|
| Ed25519 | Digital signatures | Edwards point from seed | Signature-focused ecosystem | Prefer distinct keys |
| X25519 | Diffie–Hellman key agreement | Montgomery u-coordinate from scalar | ECDH/KEM; TLS/Noise/WireGuard | Conversion possible but use caution |
Another confusion point is the relationship between X25519 and Ed25519. They are closely related in the sense that both are built around the same underlying curve family, but they are used for different jobs and have different public-key derivation procedures.
X25519 is for Diffie–Hellman key agreement. Ed25519 is for digital signatures. RFC 8410 is explicit that the procedure for deriving a public key from a private key differs between Diffie–Hellman and Edwards signatures, so the same public key cannot simply be reused for both roles. Even when the underlying seed material is related, the public representations and operations are different.
Some libraries support conversion between Ed25519 and X25519 keys. Libsodium, for example, provides APIs to convert Ed25519 public and secret keys to X25519 form. That is useful in constrained systems that want one root identity to support both signatures and authenticated encryption. But the same documentation also recommends using distinct keys where possible, because signing keys are often long-term while key-exchange keys are better when ephemeral.
There is research showing that certain carefully constructed X25519-based KEMs can be jointly secure with Ed25519 even when the same key pair is reused, under specific assumptions and KDF constructions. That is a narrower statement than “key reuse is always fine.” The safe takeaway is: conversion and reuse are possible in some designs, but they are protocol choices that need justification, not defaults to reach for casually.
What implementation and protocol mistakes still put X25519 security at risk?
| Failure | Cause | Impact | Mitigation |
|---|---|---|---|
| Weak randomness | Non-crypto RNG or poor seed | Private key brute-force | Use CSPRNG and rotate keys |
| Skipping KDF/context | Using raw DH output directly | Ambiguity or malleability | Apply KDF with public keys and transcript |
| Missing small-order checks | Accepting twist or weak inputs | All-zero shared secret; MITM | Check for all-zero or use Ristretto |
| Side-channel leakage | Secret-dependent branches or memory | Secret leakage via timing/cache | Constant-time arithmetic and cswap |
X25519 was designed to remove many common mistakes, but some failure modes remain entirely outside the curve formulas.
The most basic is bad randomness. If your private scalar comes from a weak random number generator, the strength of elliptic-curve Diffie–Hellman is irrelevant. A documented SSH.NET vulnerability used System.Random to generate the client’s private key in an X25519 exchange, making the secret seed brute-forceable for an eavesdropper. That kind of bug is a reminder that key exchange is only as strong as key generation.
Another failure mode is assuming the raw shared secret is the final answer. In sound protocol designs, the X25519 output is only one input to a KDF that mixes in context such as public keys, transcript hashes, or other handshake material. Skipping that step can create ambiguity or expose malleability that the surrounding protocol should have eliminated.
A third is confusing primitive-level permissiveness with protocol-level safety. RFC 7748 tells implementations to accept non-canonical inputs and defines behavior on a broad set of public values, including values from the twist. That is useful for interoperability and for exception-free computation. But if your application needs stronger validation properties, those belong at the protocol layer, not in wishful thinking about the primitive.
Finally, “constant-time-friendly” does not mean “automatically constant-time.” The ladder structure helps, but developers still need side-channel-safe field arithmetic, careful compiler interactions, and secret-independent control flow and memory access. Cryptographic engineering is full of designs that were secure on paper and leaky in machine code.
Conclusion
X25519 is the standardized Curve25519 Diffie–Hellman function: 32-byte inputs, 32-byte outputs, Montgomery-ladder scalar multiplication, and precise encoding rules designed for safe interoperability. Its importance comes from a rare combination of good mathematics and good engineering constraints.
If you remember one thing, remember this: X25519 exists not just to do elliptic-curve Diffie–Hellman, but to do it in a form that real systems can implement consistently, efficiently, and with fewer sharp edges. That is why it became a foundation stone of modern secure protocols.
What should you understand about X25519 before trading or transferring crypto?
Understand the key operational and protocol assumptions behind X25519 before moving funds or integrating a wallet. On Cube Exchange, you can still perform normal deposits and transfers, but follow cryptographic checks so the recipient, protocol, and keys match the expectations X25519 requires.
- Confirm the recipient or protocol expects a 32-byte X25519 public key (u-coordinate) and the correct network.
- Verify the protocol or wallet you’re interacting with derives session keys from the X25519 output using a KDF and documents how it handles the all-zero shared secret.
- Ensure your key material was generated or imported with a secure RNG and a vetted library (OpenSSL, libsodium, or x25519-dalek); confirm clamping is applied per RFC 7748.
- Fund your Cube account via fiat on‑ramp or supported crypto transfer.
- Open Cube’s transfer flow, paste the recipient’s 32-byte public key, double-check the network/encoding and fee, then submit the transfer.
Frequently Asked Questions
Curve25519 is the underlying elliptic curve (the mathematical object); X25519 is the standardized Diffie–Hellman function on that curve - an algorithm plus exact byte encodings, scalar-decoding (clamping), and input-handling rules specified so independent implementations interoperate.
Clamping deterministically clears and sets specific bits of the 32-byte secret seed so the decoded scalar has the structural properties the ladder and group arithmetic expect (a predictable bit-length and alignment with the cofactor-related power of two); it is part of X25519’s definition, not an optional optimization.
No - protocols should not use the raw 32-byte X25519 output directly as a final key; instead they feed it into a KDF (typically including transcript and public-key context) to provide domain separation, key confirmation, and to avoid ambiguities that can lead to attacks.
Because Curve25519 has cofactor 8, certain malicious or small-order public inputs can cause the shared DH result to collapse to a small-order value - in the extreme the 32-byte all-zero string; RFC 7748 permits implementations to check for an all-zero shared value and abort, and whether you must reject such cases depends on the protocol’s higher-level protections.
X25519’s Montgomery-ladder design reduces secret-dependent branching and makes constant-time implementations easier, but it does not remove the need for careful side‑channel engineering - field arithmetic, memory access patterns, compiler behavior, and platform caches still require attention to avoid leaks.
You can convert between Ed25519 and X25519 key formats in many libraries, but reusing the same key pair for both signing and key-exchange is discouraged in practice; conversion is supported and some research shows limited safe scenarios, but key reuse is a protocol decision that needs explicit justification.
RFC 7748 intentionally requires accepting non‑canonical public inputs (reducing them modulo the field prime and masking the top bit) to maximize interoperability and avoid parsing-induced fingerprinting; refusing non‑canonical inputs or signaling errors can create implementation variance and interoperability problems.
RFC 8446 lists x25519 among the named groups TLS 1.3 uses, but the specification does not make a single named group mandatory for all implementations; support for x25519 is widespread in TLS 1.3 deployments but the RFC leaves choices about which groups an implementation must offer to implementors.
RFC 8410 assigns X25519 an OID (id‑X25519) and requires that AlgorithmIdentifier parameters be absent when encoding keys in PKIX structures; some legacy systems incorrectly expect parameters, which can cause interoperability problems that need compatibility handling.
Related reading